Shopping Guide browser extension (Free Instructions)
Shopping Guide browser extension Removal Guide
What is Shopping Guide browser extension?
Shopping Guide is a potentially unwanted browser extension that might show you ads instead of discounts
Potentially unwanted applications are relatively common, although users are often not even aware that they have one of those installed on their systems. To be more precise, we are talking about the Shopping Guide extension, which is one of the prime examples of how deceptive adware apps operate while disguising themselves as something useful.
First and foremost, most people commonly install PUPs unintentionally due to their deceptive distribution methods. Software bundling, or product bundling, is among the most popular ones – that's where several applications are compiled into a standalone installer. If not paying attention to the installation steps, many might not notice that they were offered optional components and install them inadvertently.
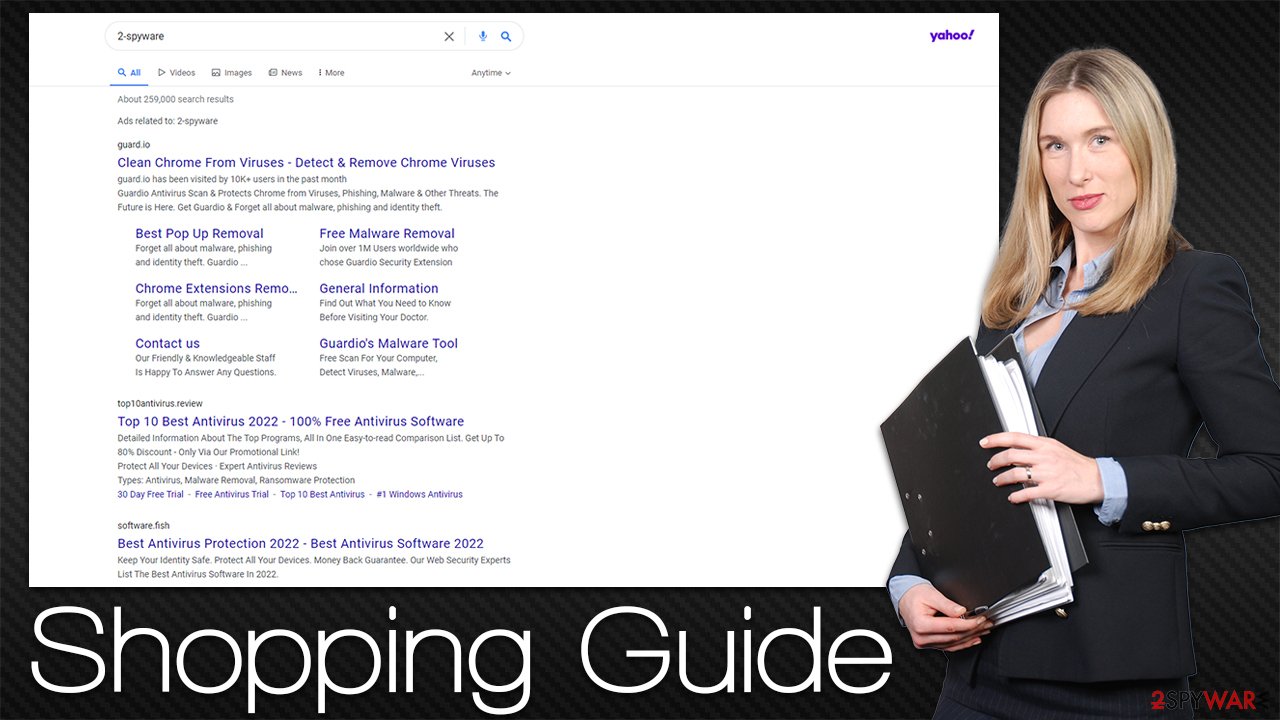
Alternatively, Shopping Guide adware might also be installed after users come across an ad for it – they might think that an app offering discounts and offers would be a great addition. However, it soon becomes clear that instead of helping users with shopping, the extension inserts its own ads on websites that users visit, which can be quite intrusive.
Another way adware earns money to its developers is by tracking user data and even sharing or selling to third parties. The information is mostly anonymous, although some details, such as the IP address[1] or device identifier, might be considered private in some jurisdictions or countries.
| Name | Shopping Guide |
| Type | Adware |
| Alleged function | Shopping discounts and deals |
| Distribution | Software bundles, third-party websites, misleading ads |
| Dangers | Installation of other potentially unwanted software or malware, personal data disclosure to third parties/cybercriminals, monetary losses due to fake offers |
| Uninstall | To get rid of adware, you can follow our removal guide below. If ads and other intrusive behavior do not stop, you should scan your computer with SpyHunter 5Combo Cleaner anti-malware and delete all threats automatically |
| Additional tips | You should delete web browser caches and other data from your browsers to protect your privacy and prevent information leaks. You can do that quicker with FortectIntego |
The fake offers
Coupons, discounts, and offers are words that greatly attract users in general. Who wouldn't want to shop online for much cheaper? However, shopping deals are not always as straightforward as they might initially seem, especially when it comes to browser extensions that offer this functionality, which initially seems like it's without downfalls. Not everything is that simple, though.
Adware and other potentially unwanted applications have been disguised as shopping apps for a long time – MyShopcoupon, Discount Dragon, and OfferssDirect are just a few examples of this scheme. Not only do they usually fail to provide effective discounts and offers, but they may also include advertisements that are completely unrelated or even dangerous. For example, adware is known to be the reason why users encounter phishing, scam, and similar dangerous websites.
Shopping Guide ads might be shown in various forms, for example, as sponsored search results at the top or as pop-ups, interstitial ads, auto-play videos, and similar. Without a doubt, the browsing experience might be very much ruined due to this and some people might not even be aware that it is the adware that is causing it.
Therefore, it is always important to ensure that powerful security software is running in the background to warn you about potentially dangerous applications. Additionally, you should always download freeware[2] apps with caution, as they commonly include optional components that are hidden within a standalone installer.
How to remove the unwanted Shopping Guide ads?
While some adware might cause difficulties when trying to remove it, extensions are usually not that difficult to get rid of. However, it is important to keep in mind that there might be other PUPs or even malware running in the background. Therefore, we recommend not only removing the main culprit for the ads but also checking other aspects of your device.
Step 1. Uninstall the browser extension
Browser extensions are really easy to eliminate under normal circumstances. The easiest way to do so is by checking the “Extensions” button close to the URL bar. Since not all apps show up that way, you might have to access the settings section of your browser – check out the instructions below if you need help with that.
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select the unwanted plugin and click Remove.

MS Edge
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

MS Edge (legacy)
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Step 2. Scan your system with anti-malware
Most adware apps come in the form of extensions nowadays – they are lightweight and hold enough functionality for the developers to receive the benefits of promotional links and other sponsored content. In this case, the surface of the operation is usually smaller than that of a program installed on the system level.
In the case of the latter, a PUP can affect all the browsers and show ads outside of them, resulting in aggressive forms of adverts known as pop-ups. Likewise, malware can make background connections to generate traffic in the background without users knowing anything about it.
Considering that adware and malware are distributed in rather deceptive ways, there could be additional unwanted or malicious applications installed on your device. Therefore, we strongly suggest you perform a full system scan with SpyHunter 5Combo Cleaner, Malwarebytes, or another powerful security software – it would ensure that all the malicious components are eliminated effectively.
Step 3. Clean your browsers to prevent data tracking
As soon as you remove the extension and other unwanted/malicious programs, you should also take care of your browser caches. Adware is known for its ability to track user data – IP addresses, cookies,[3] visited websites, clicked links, location, device identifiers, and much more. These details might later be shared with unknown third parties, which does not benefit users in any way – they might instead receive ads from unknown advertisers.
Therefore, you should either perform a scan with FortectIntego PC repair and maintenance utility to eliminate cookies and other web data to ensure the unwanted ad activity does not come back and you are no longer tracked by unknown advertisers. Alternatively, you can follow the instructions to get rid of browser caches manually (we also recommend repeating this process from time to time for better privacy and security).
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies, and other site data, as well as Cached images and files.
- Click Clear data.

Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content, and press Clear.

MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

MS Edge (legacy)
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

How to prevent from getting adware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ What is an IP Address – Definition and Explanation. Kaspersky. Resource Center.
- ^ Tim Fisher. What Is Freeware?. Lifewire. Tech News, Reviews, Help & How-Tos.
- ^ HTTP cookie. Wikipedia. The free encyclopedia.
