Smart.bytemarkup.xyz scam (Free Instructions)
Smart.bytemarkup.xyz scam Removal Guide
What is Smart.bytemarkup.xyz scam?
Smart.bytemarkup.xyz is a scam website that seeks to steal your personal information

If one enters the web address into a search bar or the URL bar, the result is always accurate and predictable. However, it goes quite a bit different when dealing with links on various (insecure) websites, as they could easily redirect users to Smart.bytemarkup.xyz or a similar malicious website.
Immediately upon website entry, users are presented with what seems to be a warning from a security application, although it is far from it. The message claims that the Windows PC needs to be cleaned after browsing the web, and it is recommended to remove the alleged junk files to free up some disk space. In reality, the message is misleading and its authors have some underlying motives behind it.
The main goal of the Smart.bytemarkup.xyz scam is to make users pay for fake security software, all while having them provide their personal details such as email, name, and phone number. We recommend not believing anything that the website pushes and instead ensuring that the computer is malware and adware-free with the steps we provide below. If you have engaged with the scam, we also provide steps to minimize the damage.
| Name | Smart.bytemarkup.xyz |
|---|---|
| Type | Scam, adware, redirect |
| Distribution | Software bundles, malicious redirects, ads |
| Symptoms | Redirects to suspicious websites that hold plenty of commercial or scam content; fake messages offer to download malicious software; ads plague every visited website; unknown extension or program installed on the system |
| risks | Installation of other potentially unwanted software or malware, personal information disclosure to cybercriminals, financial losses due to scams, etc. |
| removal | You should not interact with the contents shown by a scam website and instead, check your system for adware or malware infections with SpyHunter 5Combo Cleaner security software |
| Additional steps | Remove caches and other web data after the elimination of PUPs to prevent data tracking with the FortectIntego repair and maintenance app. You can also fix damaged system components with it |
How Smart.bytemarkup.xyz scam operates
Unfortunately, users who use the internet on a regular basis are bound to encounter malicious websites at some point. It is still worth employing security measures such as ad-blockers and security software, as these tools can significantly diminish the probability of such an unfortunate event happening.
That being said, those who visit high-risk websites more often are also more likely to encounter malicious websites during their browsing routines. What we are talking about are websites that distribute illegal software installers and cracks – it is a well-known fact that the poor security measures of such websites create a perfect environment for cybercriminals or do their malicious deeds.
Thus, insecure websites often host fake links that might reroute users to Smart.bytemarkup.xyz or a similar scam site (for example, Repairquickcompletelythefile.vip, Killsexkcell.com, or Finkeapp.com). The best thing to do is avoid websites that offer copyright material seemingly for free, as there is usually always a catch. In the worst-case scenario, malware could be installed without users taking any actions thanks to vulnerabilities[1] within the software on their machines.
Once users are redirected to the scam page, they are taken by surprise, as they are told that they need to clean their systems and protect them from Trojans and other malicious software. There is also a McAfee logo (a well-known security vendor) embedded within the message, which implies that it comes from the company. The truth is, the logo is faked and so is this website, there is nothing genuine about it.
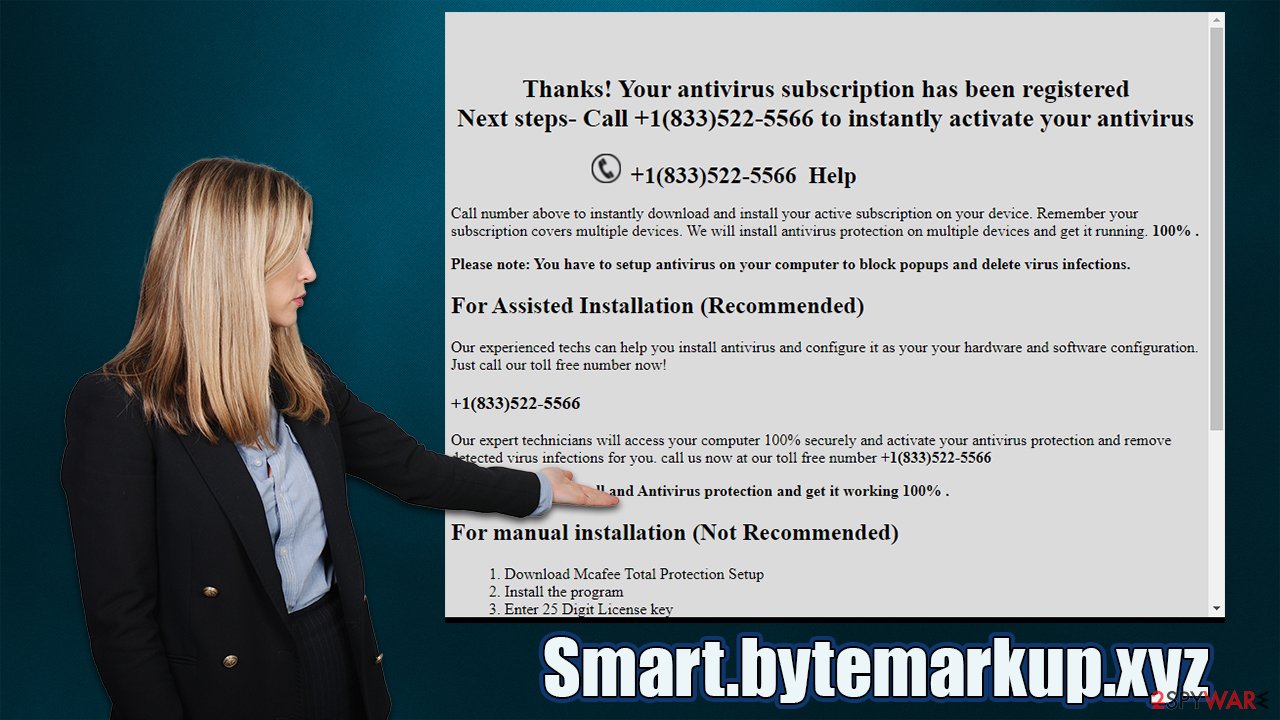
Those who proceed ar asked to enter their personal information and once they do, they receive the following message:
Thanks! Your antivirus subscription has been registered
Next steps- Call +1(833)522-5566 to instantly activate your antivirus
+1(833)522-5566 Help
Call number above to instantly download and install your active subscription on your device. Remember your subscription covers multiple devices. We will install antivirus protection on multiple devices and get it running. 100% .Please note: You have to setup antivirus on your computer to block popups and delete virus infections.
For Assisted Installation (Recommended)
Our experienced techs can help you install antivirus and configure it as your your hardware and software configuration. Just call our toll free number now!<…>
The rest of the message explains that manual steps of installing anti-malware software are apparently way too difficult and that alleged expert advice is needed. This is all false, as software installation is very straightforward – the installation instructions are provided within each step on the way (at least when it comes to legitimate software).
Those who called the provided number will be likely asked to allow a remote connection to their computer and then charged a lot of money for the alleged services. Likewise, the is no guarantee that the version of the alleged security software is legitimate and might in fact be malware in disguise.
Therefore, never trust anything that the website tells you, as these messages are all fake – crooks are trying to get your personal information and also make you pay for fake tech support services.[2]
Check your system for infections
While knowing how scams and phishing messages are operated by cybercriminals is a very important precautionary measure to avoid being a victim in the future, it is also vital to make sure that the computer you are using is free of malware and adware. Adware especially is known to divert users to websites that specialize in scams and fake messages.
Since adware is commonly distributed via software bundle packages downloaded from third-party websites, many might not be aware of their presence on the system. Some aggressive adware and most malware are invisible to regular computer users, as they don't have an active window. Therefore, the best way to check the system for most malicious programs is by scanning it with SpyHunter 5Combo Cleaner, Malwarebytes, or another powerful anti-malware.
The below steps can help you find and uninstall potentially unwanted programs that might show you intrusive ads or engage in other annoying behavior. If you can't find anything suspicious, skip this step.
Windows
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till the uninstallation process is complete and click OK.

Mac
While moving apps into Trash is how you delete most normal applications, adware tends to create additional files for persistence. Thus, you should look for .plist and other files that could be related to the virus. If you are not sure, skip this step entirely.
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
Once you have removed unwanted browser extensions, programs, and malware from your device, you should also clean your web browsers carefully. Cookies are often used to track users' online behavior so that ads could be more targeted. This and other data is commonly shared or sold to other parties, which can't guarantee its security.
Thus, after PUP removal, you should delete web data and other leftover files from your browsers. This job can be done much easier with software like FortectIntego, which can also fix any damage that could have been caused to your system files while the malware was active.
Google Chrome
- Click the Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Remediation steps
If you have been tricked by the scam in one way or another, the first thing you should do is not panic. What's done is done, and the best thing to do now is to think of how to diminish the consequences of these actions.
If you have provided your personal details that were asked by Smart.bytemarkup.xyz – email, name, and phone number, you should expect calls and emails that will try to scam you. This information can also be passed to other cybercriminals, and you might be exposed to a variety of phishing[3] attempts.
Therefore, you should always be careful when viewing new emails or receiving calls from unknown numbers. Be aware that if something sounds strange, do not give in to it, and remember that no technical support would call you unless you contacted it yourself first.
If you have spent money on useless software that was installed by crooks, make sure you uninstall it as soon as possible (use anti-malware software if needed) and then contact your bank. In some cases, transactions to scammers could get reverted.
How to prevent from getting adware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ What is a Software Vulnerability?. JFrog. Software Supply Chain.
- ^ Technical support scam. Wikipedia. The free encyclopedia.
- ^ Phishing attacks. Imperva. Application and data protection.
