This update requires an action (Removal Instructions) - updated Nov 2019
This update requires an action Removal Guide
What is This update requires an action?
This update requires an action is a fake alert seeking to infect Mac users with Potentially unwanted programs
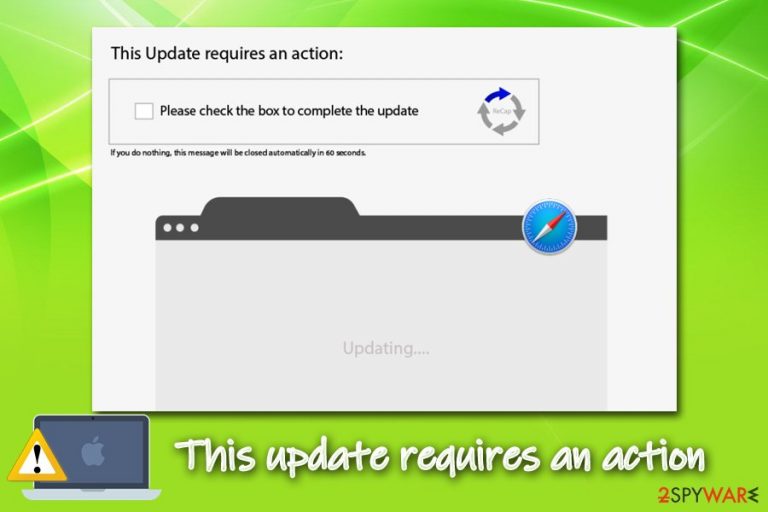
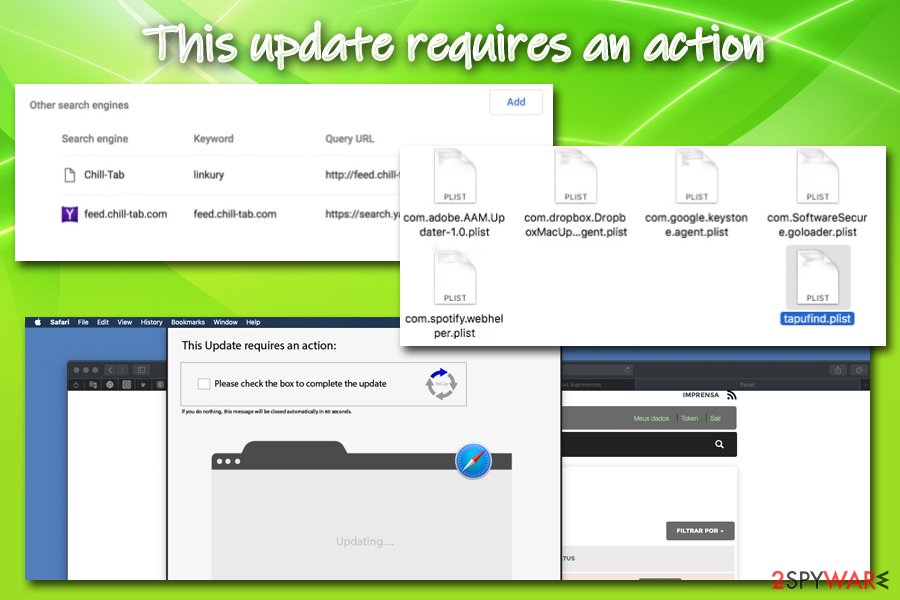
“This update requires an action” is a fraudulent pop-up message targeting Mac users. It typically appears on the Safari browser and claims that an update is mandatory for the system. It typically keeps reappearing and interrupting the user's activity on the system. The message is related to adware which drops numerous executable files on the computer, Users/Shared folder. If not ignored, it can lead to the infiltration of Chill Tab, Tapufind, and other PUPs.[1]
While in some cases users might encounter This update requires an action pop-up when visiting an insecure website, in most of the cases, persistent pups indicate that Mac is already infected with adware. Therefore, the fake notification can be removed by fixing the web browser by resetting it. However, to ensure that no PUPs have been installed yet, run a full system scan with the security software.
| Name | This update requires an action |
|---|---|
| Type | Mac malware |
| Sub-type | Adware/PUP |
| Targeted systems | The unwanted notification is targeting MacOS |
| Targeted browsers | Mostly, Safari is affected by this PUP, but we cannot exempt the possibility that it might occur on other web browsers such as Chrome, Firefox, etc. |
| Potential danger | Users might install other potentially unwanted software or even malware on their devices, disclose personal information to cybercriminals, etc. |
| Distribution | In most of the cases, users infect their Macs with adware or malware when they agree to install applications from third-party sources (especially those that host cracked software) or when they get tricked by fake updates or other bogus alerts |
| Removal | The best way to get rid of all unwanted components is to use anti-virus software. Nevertheless, it is also possible to eliminate the PUP manually as per our instructions below. Once you are done, eliminate virus damage by using FortectIntego |
It is yet not clear which application installed on macOS is causing the particular This update requires an action alert, but users should definitely not ignore it. The infection might become nastier tas the installation of apps without permission is a typical sign of more severe parasites, such as Trojans or RATs.
This update requires an action pop-up claims the following:
This Update requires an action:
Please check the box to complete the update
If you do nothing, this message will be closed automatically in 60 seconds.
As evident, the claims posted on the message are entirely fake, and the pop-up does not shut itself down within 60 seconds. In fact, users have reported that the issue becomes extremely persistent, and it is only possible to shut down This update requires action after opening Activity Monitor and killing the process of the browser.
This update requires an action is a bogus Mac security alert that might also ask you to contact fake tech support. If you receive any kind of offer for cleaning/securing/investigating your computer system, do not take it as you might put yourself in significant danger. If you have been experiencing any system problems recently, better reach out to a reliable Mac expert.
This update requires an action Mac virus might bring other suspicious activities to your computer as it is usual for an ad-supported application. The main goal of adware developers is to push their apps for income purposes. Usually, these people gather revenue from clicks that are made on their pop-up notifications or by sharing collected browsing data with other parties.

The pay-per-click technique is the most popular method used for collecting money between adware developers. This variant works within every click that is made on the ads provided. However, be careful as “This update requires an action” as it might push some bogus offers straight to your computer system and try to convince you to purchase useless products.
Do not take any deals or offers that come from This update requires action as you will only face unnecessary financial losses. Additionally, do not type in any surveys and questionnaires that might come from this suspicious app as you might be urged to enter personal information that might get exposed all over the Internet in the upcoming future.
The second monetization method from promoting This update requires an action virus is gathering information about your browsing activities. Adware programs often plant tracking cookies[2] or beacons for spying on your online activities. Later on, the collected data might be passed on to other parties or used for creating targeted ads.[3] Adware authors usually harvest the following information (which sometimes might be personal):
- IP address;
- Computer technical data and installed apps;
- Visited websites;
- Links clicked;
- Bookmarks added;
- Geo-location;
- Search queries, etc.
We suggest using FortectIntego to scan the entire computer system for suspicious entries added to your computer system. Once you find all of the questionable content that has been hiding on your machine, you can remove This update requires an action properly. Also, check the end of the article where you will find manual removal guidelines for this PUP.[4]
Learn about necessary precautionary steps towards PUP prevention
Specialists from NoVirus.uk[5] claim that if you take online safety steps seriously, you have a great chance of avoiding secret infiltration of adware programs, browser hijackers, plug-ins, and other bogus content. Here are the places where you are likely to meet potentially suspicious applications, and that should always be avoided:
- Free software packages. Be aware of sources that offer free downloads of particular software as they do not fit the needed security requirements. Also, avoid installing cracked products as they might carry bogus/potentially malicious payload.
- Third-party services. If you are a frequent visitor of online-dating, gambling, gaming, and similar websites, note that there is a risk of getting a PUP secretly installed on your computer system through bogus links and adverts.
In order to secure your incoming downloads, you should opt for the Custom/Advanced installation mode and avoid Quick/Recommended configuration as here your downloads will be completed automatically and you will not have the chance of deselecting all rogue products that you do not want to see on your machine.
In addition, you should think about automatic protection also. Securing your computer system with a reliable anti-malware program is necessary if you want to protect your machine at a higher level. Make sure that you choose an expert-tested piece of software and keep it regularly updated whenever new updates are released.
The termination process of This update requires an action infection
There are two ways which will help you to remove This update requires an action from your computer system and web browser. You can employ reputable anti-malware products for completing this process. The software will carry out the entire process in a few minutes of time and ensure that all infection sources are permanently cleaned.
However, if you think of yourself as an experienced computer user, you can perform the This update requires an action removal process with the help of our manual instructions. We have provided detailed steps at the end of this article that will you to erase all bogus products from macOS and infected browser apps. Before proceeding with this method, however, you should check the following folders for suspicious entries and eliminate them:
- /Library/LaunchAgents
- /Library/Application Support
- /Library/LaunchDaemons
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of This update requires an action. Follow these steps
Delete from macOS
Eliminate the adware program from your Mac OS X computer system by following the below-provided instructing lines:
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Mozilla Firefox (FF)
You can clean Mozilla Firefox from questionable products and reverse unwanted changes with the help of these guidelines:
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
Google Chrome can be reversed back to its previous state if you follow our below-given instructing steps:
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
Remove all bogus extensions and plug-ins from your Safari web browser. Use these instructions for help:
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of This update requires an action registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ "This update requires an action" Safari, Mac OS, Mojave. Reddit. Apple help.
- ^ Tracking Cookie. Techopedia. Tech terms and definitions.
- ^ Targeted advertising. Wikipedia. The free encyclopedia.
- ^ Margaret Rouse. PUP (potentially unwanted program). Search Security. Tech Target.
- ^ NoVirus.uk. NoVirus. Security and spyware news articles.
