Whats App – Missed Voice Message email scam (fake) - Free Guide
Whats App – Missed Voice Message email scam Removal Guide
What is Whats App – Missed Voice Message email scam?
Whats App – Missed Voice Message email scam was created to redirect users to shady sites
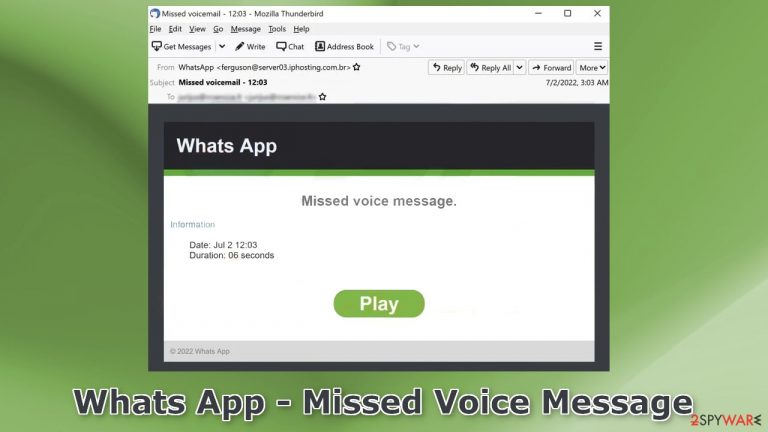
“Whats App – Missed Voice Message” is a fake email completely fabricated by crooks. It tries to convince users that they have a missed voice message on Whats App. People are prompted to click the “Play” button which can redirect users to dangerous pages. The full message reads as follows:
Whats App – Missed Voice Message email scam
Subject: Missed voicemail – 12:03
Whats App
Missed voice message.
Information
Date: Jul 2 12:03
Duration: 06 secondsPlay
© 2022 Whats App
The dangerous pages that users are redirected to can try to trick people into providing personal information which could result in monetary losses or even identity theft. Crooks could also try to make people mistakenly install PUPs (potentially unwanted programs),[1] or even malware which could damage the operating system.
| NAME | Whats App – Missed Voice Message |
| TYPE | Social engineering attack; email scam |
| SYMPTOMS | Users receive an email supposedly from Whats App that contains links leading to dangerous websites |
| DANGERS | People can end up on sites possessed by crooks that try to lure out personal information, trick users into downloading PUPs or even malware |
| ELIMINATION | If you opened an email with a malicious attachment scan your computer with anti-malware tools |
| FURTHER STEPS | Use FortectIntego to clear your browsers and get rid of any remaining damage |
One of the pages discovered to be promoted by the malicious email is an Amazon Loyalty Program Scam. It tries to convince people that they have a chance to win an Apple iPhone 13 Pro. To receive the gift, users are asked to enter their personal details, like name, phone number, email address, credit card details, etc.
The page uses geolocation information and inserts the users' country in the message to make it more believable. You can see the full message in the image below:
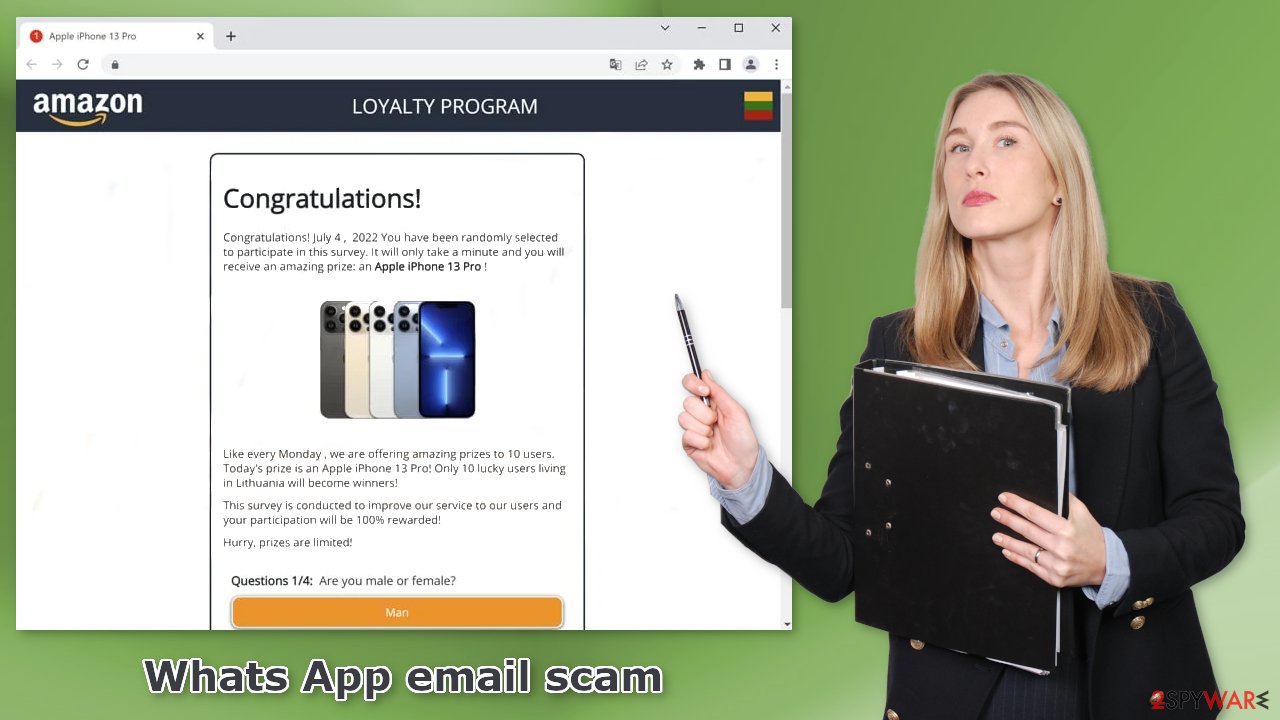
It is extremely important to think twice before entering your details on a random page. If it is too good to be true – it probably is. Be aware that fraudsters can use scare tactics and social engineering methods[2] to perform some kind of action.
Email scams in general
Most often, cybercriminals use email to try to deliver malware into victims' accounts via infected email attachments. These attachments can come in different types of files. Usually, the malicious code gets introduced by an executable file (.exe) that may have been in a zip folder, embedded within a Microsoft Office document’s macros,[3] or disguised as another attachment.
The emails are also often disguised as official and urgent letters from well-known companies and organizations. Crooks use the branding, logos, and trust that these companies have built over the years with their customers. If you think you were tricked by a deceptive message, there are some actions you should take to protect yourself.
What to do if I interacted with a malicious email?
The most important thing to do if you gave away your login details is to change your passwords as soon as possible. If you do it quickly, there may be a chance that cybercriminals will not have enough time to do any damage. If you think you entered your bank account information into an unsafe site – contact your bank and explain what happened. You may be able to cancel your card before fraudsters reach it.
If you think you opened a malicious email attachment, you should scan it with professional security tools because most likely – it got infected. In this guide, you will find instructions on how to act in case of malware infection and how to fix a damaged operating system.
Check your system for malware infections
If you suspect that you have opened an email with an infected attachment, you should take care of the threat. We recommend using SpyHunter 5Combo Cleaner or Malwarebytes security tools that will scan your machine, eliminate it, and prevent such infections in the future by giving you a warning before a malicious program can make any changes.
Crooks often disguise their malicious programs as “handy” tools so they would be more difficult to identify for the average user. People also often fail to eliminate all the related files and entries which could lead to the renewal of an infection. The program could have any name and icon, so this step is best performed by anti-malware tools.
However, if manual removal is what you prefer, we have instructions for Windows and Mac machines:
Windows 10/8:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

Windows 7/XP:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Mac:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Repair the damaged operating system
Performance, stability, and usability issues, to the point where a complete Windows reinstall is required, are expected after malware infection. These types of infections can alter the Windows registry database, damage vital bootup and other sections, delete or corrupt DLL files, etc. Once a system file is damaged by malware, antivirus software is not able to repair it.
This is why FortectIntego was developed. It can fix a lot of the damage caused by an infection like this. Blue Screen errors, freezes, registry errors, damaged DLLs, etc., can make your computer completely unusable. By using this maintenance tool, you could avoid Windows reinstallation.
- Download the application by clicking on the link above
- Click on the ReimageRepair.exe
- If User Account Control (UAC) shows up, select Yes
- Press Install and wait till the program finishes the installation process
- The analysis of your machine will begin immediately
- Once complete, check the results – they will be listed in the Summary
- You can now click on each of the issues and fix them manually
- If you see many problems that you find difficult to fix, we recommend you purchase the license and fix them automatically.

How to prevent from getting spam tools
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Chris Hoffman. PUPs Explained: What is a “Potentially Unwanted Program”?. Howtogeek. Technology Magazine.
- ^ Cynthia Gonzalez. Top 8 Social Engineering Techniques and How to Prevent Them [2022]. Exabeam. Information Security.
- ^ Chris Brook. WHAT IS MACRO MALWARE?. Digitalguardian. Data Protection.
