WhiteRose ransomware (Virus Removal Instructions) - May 2018 update
WhiteRose virus Removal Guide
What is WhiteRose ransomware?
WhiteRose ransomware is a dangerous program using AES cryptography to encrypt target files
WhiteRose ransomware is a crypto-virus that uses AES encryption algorithm[1] to lock target files and make them inaccessible. To mark these files, it appends [random text]_ENCRYPTED_BY.WHITEROSE file extension and drops a ransom note named HOW-the TO-the RECOVERY-files.txt. This txt document includes the picture of rose and data recovery instructions claiming that the victim has to pay a ransom to recover his/hers locked files. Ransomware is very similar and is believed to belong to the same group of hackers as Zenis ransomware and BlackRuby, so there is no legitimate decrypter for WhiteRose ransomware.
| Summary | |
|---|---|
| Name | WhiteRose |
| Type | Ransomware |
| Danger level | High. Makes system changes and encrypts files |
| Encryption method | AES |
| Appended file extension | [random text]_ENCRYPTED_BY.WHITEROSE |
| The name of ransom note | HOW-the TO-the RECOVERY-files.txt |
| Official decryptor | No. However, some security experts offer file decryption (paid and free) |
| To get rid of ransomware, install FortectIntego and run a full system scan | |
WhiteRose virus typically infiltrates users machines in deceptive ways – via phishing emails or malicious websites. As soon as ransomware's code is executed, it scans the machine and looks for files to encrypt. It will lock up a variety of different files, including .7zip, .dat, .mp3, .doc, .xml, .txt, .pdf and many others. However, the malware will skip files in the following locations: Windows, Program Files, Microsoft and Recycle Bin.
Soon after the encryption is complete, the virus will modify names of infected files. For example, the file, which before infection used to be called picture.jpg will be turned into r4lK6pWmzqYe_ENCRYPTED_BY.WHITEROSE. Once the targeted files are locked, the ransom note is dropped into every encrypted data folder.
We must admit that the ransom note of WhiteRose ransomware stands out among thousands of other messages provided by cybercriminals. The hacker wrote a whole story of himself, expressed his passion for writing and willingness to plant a garden of white roses and give gifts to people all over the world. Indeed, this gift is a ransomware virus.
I think of days and write at night : the story, poem, code, exploit or the accumulation of the number of white roses sold and I say to myself that the wealth is having different friends of different races, languages, habits and religions, Not only being in a fairly stylish garden with full of original white roses.
Today, I think deeply about the decision that has involved my mind for several weeks. A decision to freedom and at the worth of unity, intimacy, joy and love and is the decision to release white roses and to give gifts to all peoples of the world.
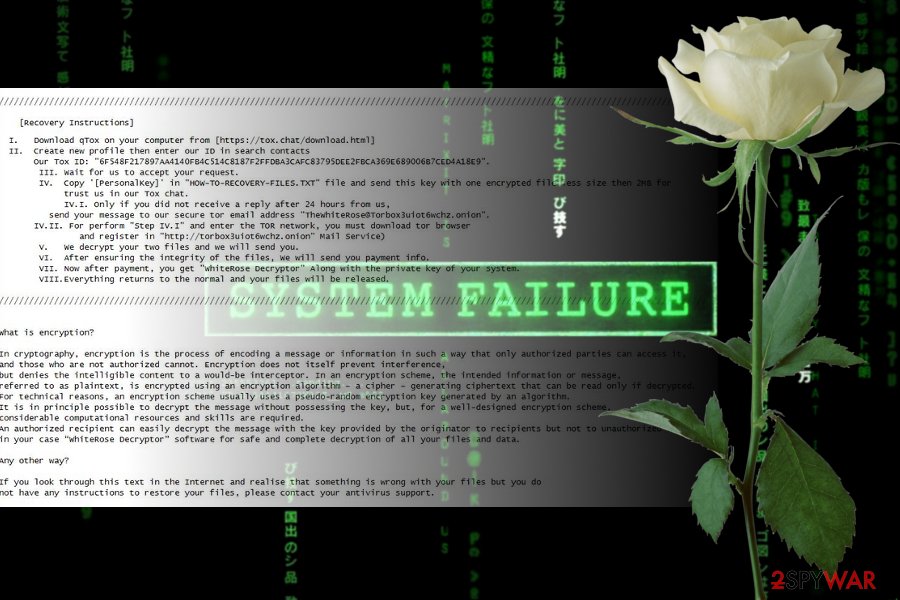
Never mind the fact that hacker is poetic – victims of ransomware still are asked to pay a ransom in order to get back access to their files. A developer of WhiteRose virus informs that people have to send their unique ID number provided in the TXT file and one of the encrypted files via Tox.[2] However, if victims to do not receive an answer within 24 hours, they have to send the same content to the WhiteRose@Torbox3uiot6wchz.onion.

Users are asked to provide personal ID and include two personal files. According to cybercrooks, this action is required to prove victims that decryption is possible.Then, cybercriminals should respond and inform the user about the size of the payment. As soon as the ransom is paid, victims should receive a WhiteRose Decryptor and a private decryption key.
Finally, the virus will delete shadow volume copies (an automated backup system in Windows), disable Startup Repair function and erase event logs.[3] Soon after that, WhiteRose finishes its malicious process by deleting itself from the system entirely.
Ransomware viruses are used for illegal money-making activities. Therefore, as soon as criminals receive the money, they might disappear and leave you with a bigger money loss. Hence, it’s recommended to remove WhiteRose ransomware from the computer and look up for alternative recovery solutions.
WhiteRose ransomware removal has to be performed with reputable anti-malware software. This malicious program can install countless malicious files and affect critical system files. Hence, manual termination might be dangerous for the computer. You might accidentally delete or corrupt important files.
The virus might also modify Windows registry or create new entries in order to boot with system startup and perform malicious activities. Hence, it’s important to fix all these changes to make the system safe and properly working.
For this reason, we recommend using FortectIntego for cleaning malware and fixing its damage because this program has a double functionality. As soon as it deleted the virus, it restores and repairs registry entries and other system-related problems.
Security specialists from virukset.fi[4] remind that WhiteRose virus removal does not bring back encrypted files. You will need to use backups for full recovery. Alternatively, you can contact security expert Michael Gillespie[5] for free file decryption. Also, you can also try asking Dr.Web for help; however, the service is paid.
If none of the mentioned file decryption methods suit you, you can try alternative third-party software. You will find all descriptions and download links below this post.
Dissemination methods of the file-encrypting malware
It’s unknown how this specific ransomware is spread and installed on Windows computers. However, specialists note that these type of cyber threats spread using similar methods, such as:
- malicious spam email attachments;[6]
- fake software updates;
- bogus security software or illegal programs;
- exploit kits;
- malvertising;
- drive-by downloads;
- insecure RDP services.
Thus, it is not enough to install anti-virus program to avoid ransomware attacks. Of course, it’s an important security measure, but you have to remember that any program can protect you 100%. You have to follow general security tips: avoid downloading questionable software, clicking suspicious ads and keeping software updated.
Remove White Rose ransomware virus
WhiteRose removal can only be performed by using professional security software (we suggest using robust tools like FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes. Ransomware viruses are complicated and cannot be exterminated manually, unless you are an IT professional. Thus, don't even try it, or you might damage system files and damage the machine further.
However, if you experienced some problems and cannot remove WhiteRose because malware blocks security programs, follow the steps below. Our specialists are willing to help you to disable the virus and run automatic elimination.
As soon as you get rid of WhiteRose virus, you can start data recovery procedure. If you attempt to reclaim your files before virus elimination, all the data will be encrypted once again.
Getting rid of WhiteRose virus. Follow these steps
Manual removal using Safe Mode
To disable the virus and run automatic removal, follow this guide:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove WhiteRose using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of WhiteRose. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove WhiteRose from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by WhiteRose, you can use several methods to restore them:
Try Data Recovery Pro to restore .WHITEROSE files
This tool might help to recover corrupted files. However, we cannot promise full recovery; it's not an official decryptor.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by WhiteRose ransomware;
- Restore them.
Try Windows Previous Versions feature
If System Restore was enabled before ransomware attack and you need to get back only a few files, follow these steps:
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Try ShadowExplorer
If malware did not delete ShadowVolume copies, this tool might help you with data recovery:
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
WhiteRose decryption
The official decryptor for this crypto-virus is not available yet. However, you can contact Michael Gillespie or Dr.Web for help, as these security experts are capable of decrypting files affected by WhiteRose.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from WhiteRose and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Advaced Encryption Standard. Wikipedia. The free encyclopedia.
- ^ The Tox Project. Tox client. Tox client project.
- ^ Event Log. Technopedia. Site that explains technology.
- ^ Virukset. Virukset. Finnish cyber security news.
- ^ Michael Gillespie. @demonslay335. Twitter. Social network.
- ^ Ransomware Is the Most Popular Malicious Email Attachment in Q2 2017. The Merkle. News website.







