Windowsdetector.com ads (Free Instructions)
Windowsdetector.com ads Removal Guide
What is Windowsdetector.com ads?
Windowsdetector.com misleadingly tells people their systems might be infected

When you use your address bar to type in the URL of the webpage you want to visit, the outcome is always what you expect it to be. However, when using the search engine, the top results do not always match what you expect due to ads that could be shown at the very top; likewise, less secure websites might include links to places that you might not expect.
Windowsdetector.com is a scam site that you might encounter in the latter scenario when you click links on websites that are less protected, e.g., torrents, gambling, illegal video streaming, etc. Once users arrive at it, they are usually surprised by unexpected warning messages and alerts – this is one of the more commonly-used social engineering[1] tactics that help online scams be successful.
According to the message, users have visited an illegal website, and the PC is at risk of being infected. Then they are offered to click the “Scan” button, which is meant to work as an antivirus scan, and check the system. If they proceed, they are then told that their systems are infected and that they need to remove these infections with an alleged security app.
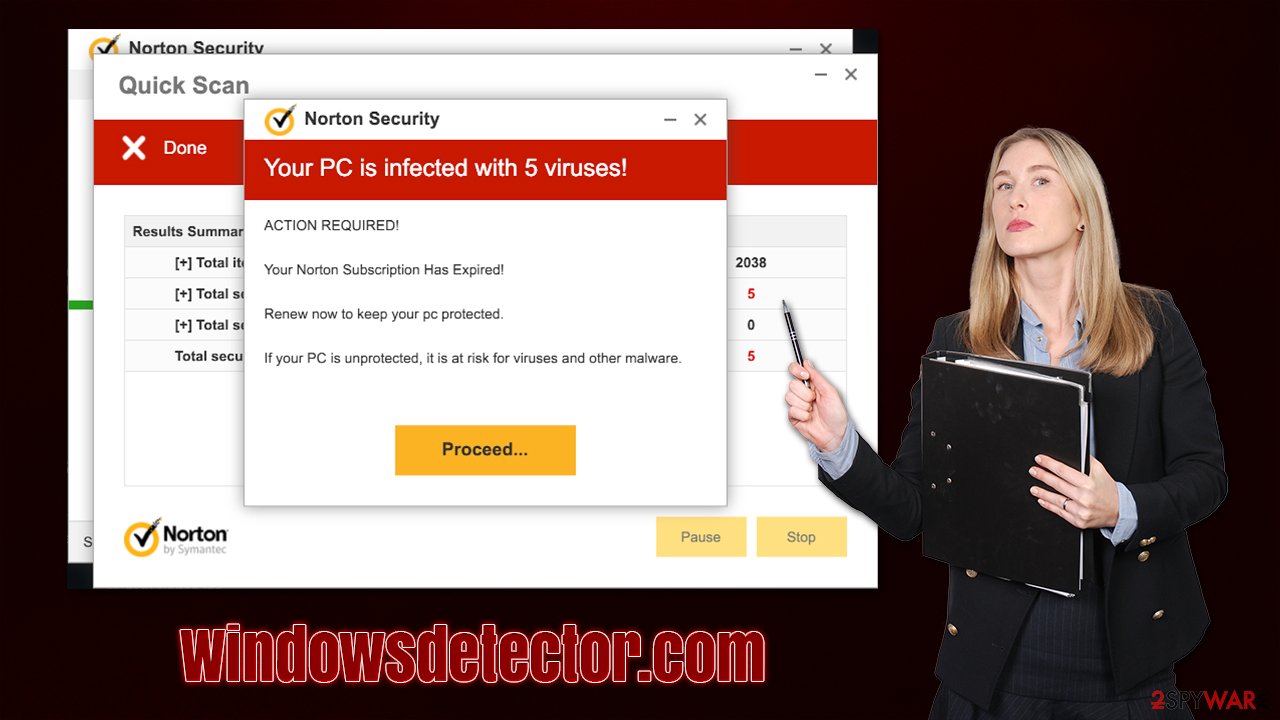
Do not listen to Windowsdetector.com alerts as they are all fake, even if it looks like it is coming from a legitimate provider such as Norton. The goal here is to make people unsure about their system status regarding security and download the offered application. Offered software can be anything, even malware, so please do not install anything you are suggested.
In addition to the fake alerts, the website also asks users to enable notifications, which should be avoided. Those who click the “Allow” button within the prompt might start receiving push notifications from it at any time, and the contents would be less than desirable. Scams, fake messages, misleading statements, and much more. If you have been affected by this issue, you will find the solution at the bottom of this article.
| Name | Windowsdetector.com |
|---|---|
| Type | Scam, redirect, adware |
| Distribution | Software bundles, third-party websites, ads |
| Symptoms | Redirects to suspicious websites that accommodate commercial or scam content; fake messages that offer to download malicious software; ads plague every visited website; unknown extension or program installed on the system |
| risks | Installation of other potentially unwanted software or malware, personal information disclosure to cybercriminals, financial losses due to scams, etc. |
| removal | You should not interact with the contents shown by a scam website and instead, check your system for adware or malware infections with SpyHunter 5Combo Cleaner security software |
| Additional tips | You should remove caches and other web data after the elimination of PUPs to prevent data tracking with the FortectIntego repair and maintenance tool. You can also repair damaged system components with it |
There have been plenty of fake websites that are trying to impersonate popular security vendors such as Norton or McAfee – Mydesktopdefence.com, Bluelight-mc2.club, and Redlight-mc2.club are just a few examples why have already been discussed in our articles. Scammers use logos and other attributes that are meant to be familiar to visitors.
When using well-known company names, crooks ensure that some people would not recognize the deception and believe whatever is said to them. Windowsdetector.com starts by briefly showing a message about the alleged potential danger:
Security Alert
You've visited illegal infected website
You visited unsafe site with illegal content
Your PC is at risk of being infected by viruses
To continue browsing safely – perform and antivirus scan
Under this premise, users are already being frightened about the consequences of visiting “illegal websites.” The page then automatically loads a fake scan that would remind that one of the security software. However, the loading bars and “detections” are all fake, and users are finally shown the following:
Your PC is infected with 5 viruses!
ACTION REQUIRED
Your McAfee Subscription Has Expired!
Renew now to keep your PC protected.
If your PC is unprotected, it is at risk for viruses and other malware.
Then visitors are asked to download and install an alleged security tool that would remove the infections. Without a doubt, this step would result in computer infection, as it is not Norton or McAfee that users would install but some potentially unwanted program or even malware.
If you have been tricked by the Windowsdetector.com scam, you should immediately check your system for infections. Likewise, in case you have allowed notifications accidentally, we will provide instructions on how to remove them as well.
1. Find and remove adware from your device
Knowing more about scam techniques and tricks that scammers use to trick people online is a very important part of staying secure online. However, another aspect is to make sure that the system is not affected by adware,[2] as it is more likely to cause users to encounter unwanted or even dangerous material online.
In other words, those who are exposed to pop-ups, deals, offers, in-text links, and other commercial content while browsing the web are likely to be affected by it. Additionally, those who have been tricked by the scam and installed the offered “removal software” are affected by the same or even worse problem.
Since adware comes in a variety of shapes, the severity and the impact on the system differ. First of all, we recommend scanning the device with SpyHunter 5Combo Cleaner, Malwarebytes, or another powerful security tool. Then, you can check your browsers for unwanted extensions – you can find them in the small section to the right of the URL bar or by accessing browser settings.
Next, you should check whether there are apps installed on the system level:
Windows
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

Mac
While moving apps into Trash is how you delete most normal applications, adware tends to create additional files for persistence. Thus, you should look for .plist and other files that could be related to the virus. If you are not sure, skip this step entirely.
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
Once you have removed unwanted browser extensions, programs, and malware from your device, you should also clean your web browsers carefully. Cookies[3] are often used to track users' online behavior so that ads could be more targeted. This and other data is commonly shared or sold to other parties, which can't guarantee its security. Thus, after PUP removal, you should delete web data and other leftover files from your browsers. This job can be done much easier with software like FortectIntego, which can also fix any damage that could have been caused to your system files while the malware was active.
Google Chrome
- Click the Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

2. Get rid of Windowsdetector.com push notifications
If you have enabled push notifications from the site, you might start receiving annoying pop-ups on your desktop from time to time. Malicious websites tend to abuse this feature a lot as long as users accept the offer, so you might be spammed with notifications constantly.
You should never click on links that these pop-ups show and never believe what they say. Instead, you should use the instructions below to eliminate the unwanted activity. Note that if you come across similar issues with different websites, you can use this guide to remove push notifications from those as well.
Google Chrome
- Open Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.

Google Chrome (Android)
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).

Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.

MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.

Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.

How to prevent from getting adware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Social Engineering. Imperva. Data and application protection.
- ^ Lucian Constantin. What is adware? How it works and how to protect against it. CSOonline. CSO offers the latest information and best practices on business continuity and data protection.
- ^ HTTP cookie. Wikipedia. The free encyclopedia.
