Amazon virus. 7 latest versions listed (2021 removal guide)
Amazon virus Removal Guide
What is Amazon virus?
Amazon virus is a form of fake alerts spreading malware right after being clicked

Amazon virus is a term used to describe scams that spread as fake messages on social media, dangerous sites, or malicious emails. The set of phishing messages[1] usually offer attractive and expensive prizes (such as Amazon gift card, iPhone, PlayStation or Samsung Galaxy phone) or try to convince users that they need to update their banking information on Amazon spoofing account.
As evident, these alerts are fake, and those who unintentionally install Amazon virus on their device might end up with potentially unwanted programs or malware. Additionally, many scams are trying to harvest personal information from users, such as name, email, address, or other data. Nevertheless, in most cases, victims are persuaded to disclose their banking details, which consequently end up in cybercriminals' hands.
If you installed any type of software suggested in these scams or extracted an attachment in an email pretending to be from Amazon, you should scan your device with anti-malware software and remove Amazon virus from your device immediately.
| Name | Amazon virus |
|---|---|
| Type | Scam, potentially unwanted program |
| Versions | Amazon Gift Card scams, Amazon Reward scams, supposedly useful Amazon apps, etc. |
| Caused by | Adware. Used to hijack web browsers and modify their settings |
| Main functionality | Interrupts victims with pop-up ads claiming that they need to enter their personal details to claim prizes, offers free software |
| Main dangers | By entering your personal information, you can be involved into identity theft and similar crimes. Besides, there is a high risk of getting infected with malware |
| Repair | To get rid of virus damage, use FortectIntego. |
In the beginning, let’s make it clear that Amazon virus is not related to the legitimate Amazon company in any way. You can visit its online store and spend your money on purchasing its goods without any fear.
However, if you happen to run into a simple offer telling you that you need to enter your personal details to receive a $1000 gift card from this company, you should stay away from it and double-check your computer with reputable anti-spyware software.
The very first infections related to Amazon scams installed a Trojan on victims' machine
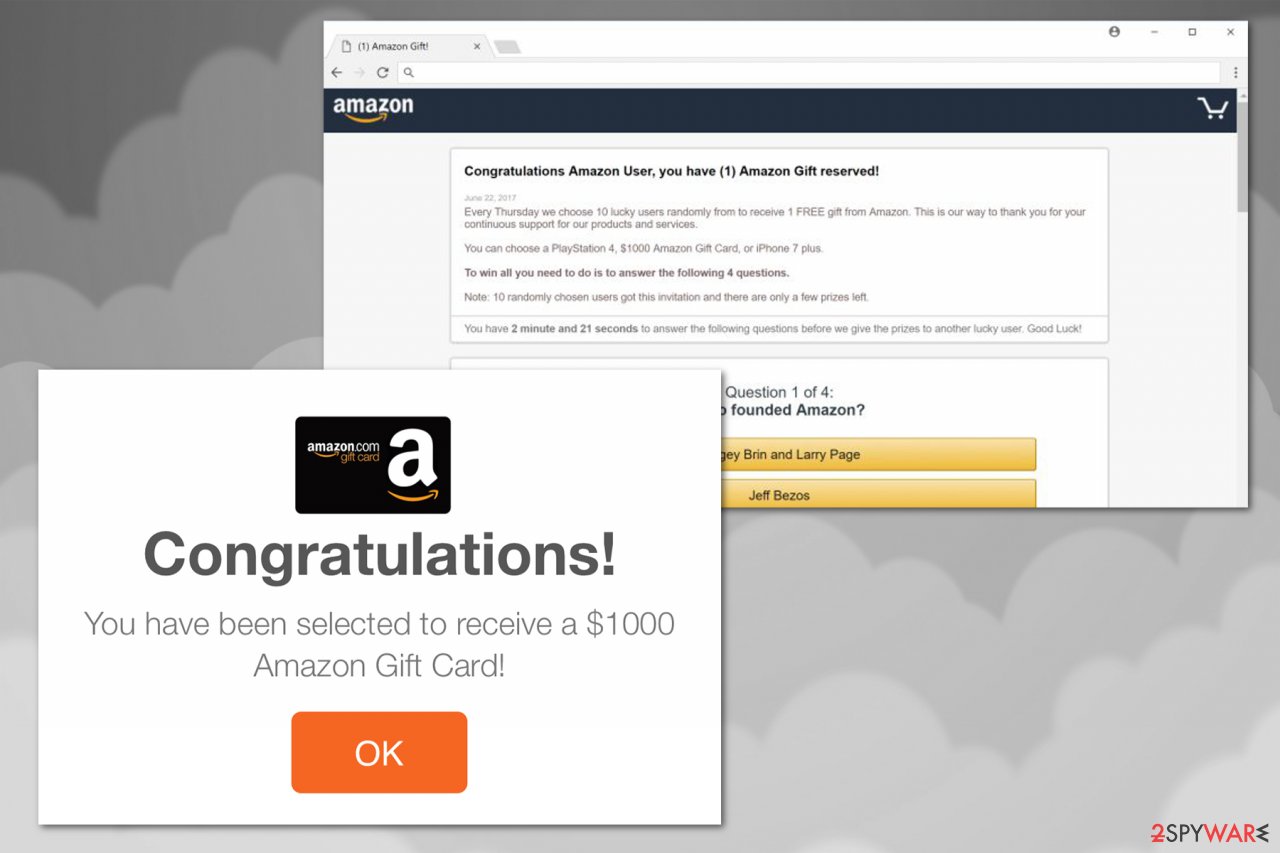
Amazon virus was first noticed in the form of a Trojan horse[2] in 2012. Since then, cybersecurity experts have been monitoring this malware as its initial versions were found almost seven years ago.[3] Recently, cybercriminals started using various scams claiming that victims should enter their personal details to get free prizes. One such example comes from “Congratulations Amazon User” scam:
Congratulations Amazon User, you have (1) Amazon Gift reserved!
Every Thursday we choose 10 lucky users randomly from to receive 1 FREE gift from Amazon. This is our way to thank you for your continuous support for our products and services.
You can choose a PlayStation 4, $1000 Amazon Gift Card, or iPhone 7 plus.
To win all you need to do is to answer the following 4 questions.
Note: 10 randomly chosen users got this invitation and there are only a few prizes left.
You have 1 minute and 24 seconds to answer the following questions before we give the prizes to another lucky user. Good Luck!
Typically, crooks are trying to convince users by using social engineering and offering gifts, as well as creating a sense of urgency due to the given timer. However, those who see Amazon virus fake alerts should be able to recognize them in the future and not get deceived.
Additionally, Amazon has set up a support page that informs users about the latest scams and offers them to report spoofed emails or spam to remove Amazon virus from the system. Therefore, users can always find the newest information regarding Amazon scams.
Nevertheless, scammers have been successfully exploiting the name of Amazon company to collect people's personal information, such as their logins, passwords, and similar data through fake emails.[4] Unfortunately, that's not the only expectation of Amazon email virus.
Some serious Amazon virus infections could:
- Download and install additional malware on the system;
- Inset ads into all sites that you visit;
- Record keystrokes and take screenshots;
- Steal banking information and other sensitive data;
- Include the device into a botnet.[5]
Nevertheless, if you see consistent Amazon scams, as well as constant redirects to suspicious sites, the culprit is a potentially unwanted program, such as adware. While it is a lesser infection than malware, it should not be underestimated as it can create havoc on your machine over time.
To carry out Amazon virus removal on your computer, you should run a full system scan with updated anti-spyware. This is the easiest way to spot potentially unwanted programs that have been installed on your system behind your back. For this purpose, we recommend using FortectIntego which can not only find malicious entries on your computer but also fix the outcomes of this virus, e.g., reinstall missing system components and damaged files.
The list of all Amazon scams
Since the beginning of its operation, Amazon virus has been actively related to scams and phishing emails used to mislead victims into thinking that they need to take care of their purchases, enter their details to receive free gifts and prizes, etc. Amazon scam can also inform its victim that he/she needs to print the postal label with the tracking number to get the parcel or to print the invoice that can be found in e-mail's attachment. Of course, you should NEVER do that because this attachment is a malicious file. Below we provide a few examples of currently active scams related to the company:
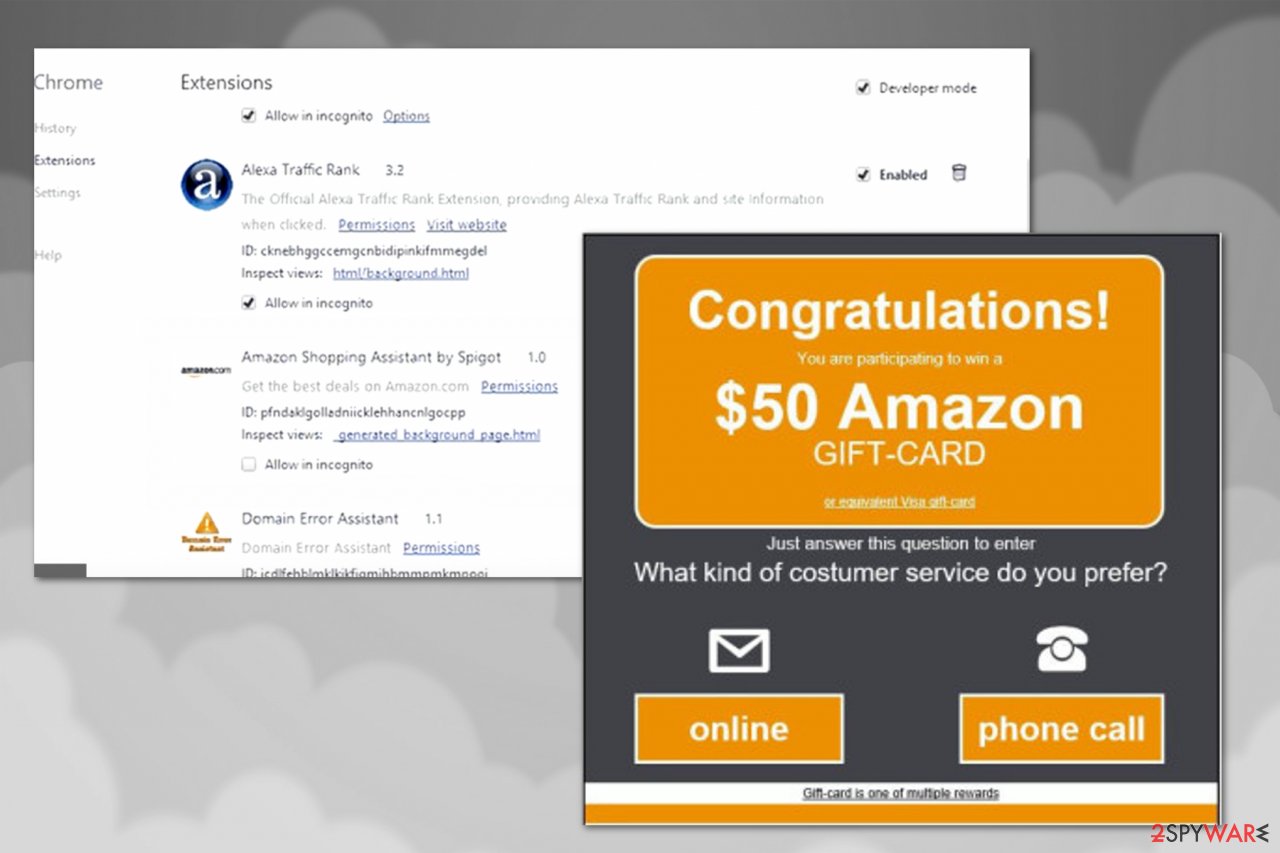
Amazon Assistant virus
Amazon Assistant virus is a potentially unwanted program which has been actively promoted via bundling. Typically, it is presented as a useful add-on that is supposed to help customers of Amazon find the best deals, sales and promotions. However, the main issue related to this “shopping helper” is its ability to spy on its visitors.
Typically, it collects information related to your browsing activities, location and computer. Technically, this app is not malicious, but there is no need to rely on its offers as the most of them are fabricated. You should definitely double check prices and similar information displayed by Amazon Assistant.
Congratulations Amazon User
Congratulations Amazon User is one of the most persistent scams spreading on the Internet since last year. This bogus Amazon alert is mostly displayed on iPhone, iPad, and Android operating systems but, undoubtedly, it has also been bothering Windows users as well. Its spam campaigns are used to trick users into thinking that they are about to win one of these “Amazon gifts” – PlayStation 4, $1000 Amazon Gift Card, or iPhone 7 plus. Unfortunately, after claiming these prizes, you can not only receive more spam in your email, but can also receive suspicious calls opening the malware-laden programs.
Amazon Gift Card scam
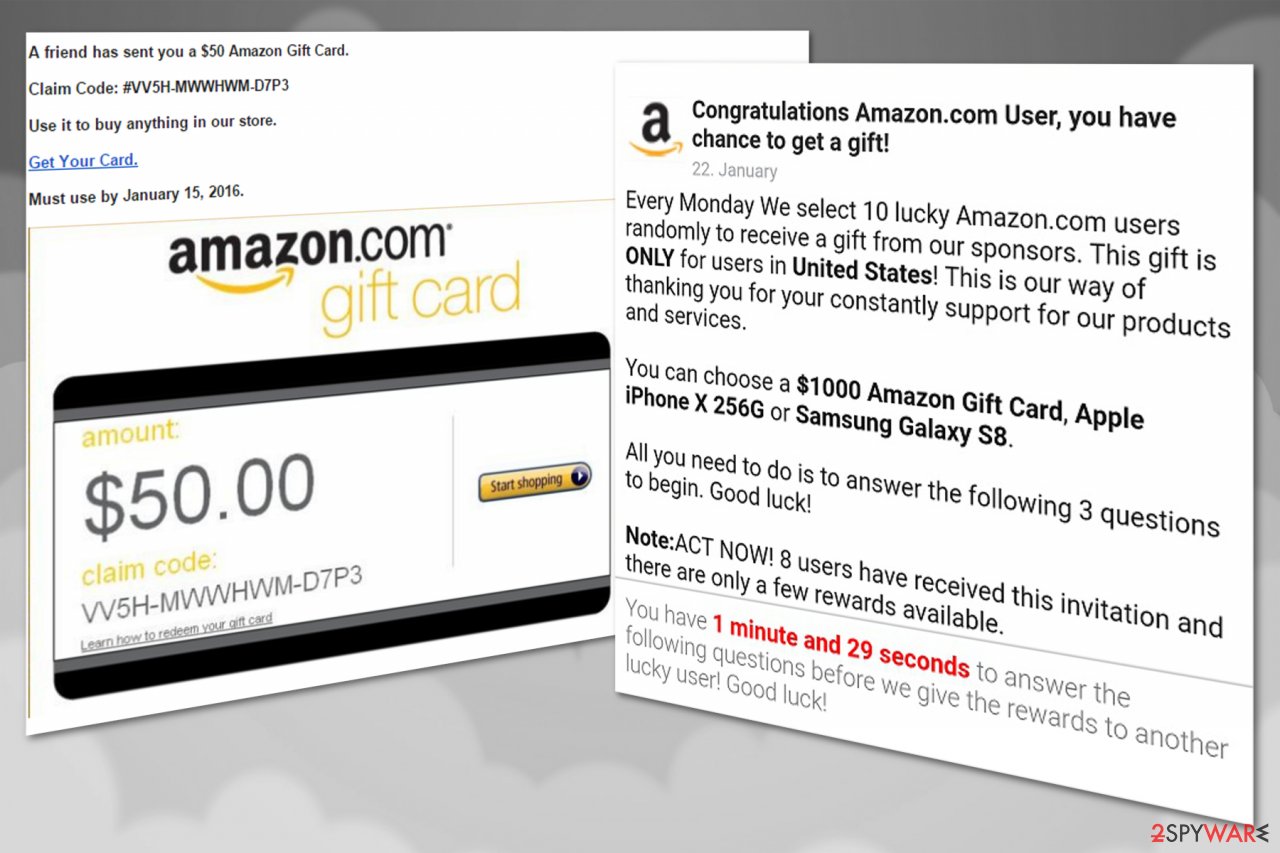
Amazon Gift Card scam is a scam related to this giant company. It seeks to convince its victims that he or she is about to get a $1,000 prize for answering several questions to the questionnaire. Typically, the pop-up comes from coupon2342341.com or similar domain name and interrupts you while you are browsing the web. First two questions displayed by this scam are as simple as you can imagine.
For example, you can be asked who is the president of the United States or who launched Amazon company. Beware that after catching your attention, scammers move on to personal information which can be later sold on the black market to cybercriminals.
Amazon Rewards Event
Amazon Rewards Event is yet another Amazon scam that has been actively used to mislead users into thinking that their loyalty to Amazon has paid off. The fake popup, which typically shows up out of nowhere, claims that the victim can receive a prize just for shopping.
However, just like any other scam, it requires entering some personal information “to claim the prize”. Typically, victims are asked to reveal their full name, home address, telephone number, and similar data. However, some scammers have been setting aggressive campaigns used to swindle financial data and personally identifiable information.
$1000 Amazon Gift Card is reserved for you
$1000 Amazon Gift Card is reserved for you has mostly been seen on Mac OS X computers. However, the same prize can easily be offered for those who are using Windows OS or even Android. According to the latest reports, this type of Amazon scam has already deceived hundreds of victims.
Of course, scammers do not send them any presents and just collect these personal details for their own needs. Beware that they can easily sell them to third parties who can misuse them for their malicious deeds.
Amazon Membership Rewards
Amazon Membership Rewards is yet another scam that refers to a type of scam designed to swindle sensitive information from Amazon shoppers and take over their bank accounts. The sequence of the attack is simple. First, victims receive an email telling about a reward related to their shopping online or is interrupted by a similar pop-up while browsing on the web.
The victim is then asked to click a link or popup and visit the “official” Amazon page which is in reality is fake. All data entered on this bogus website is revealed to scammers and can be used to break into your Amazon account and even your bank.
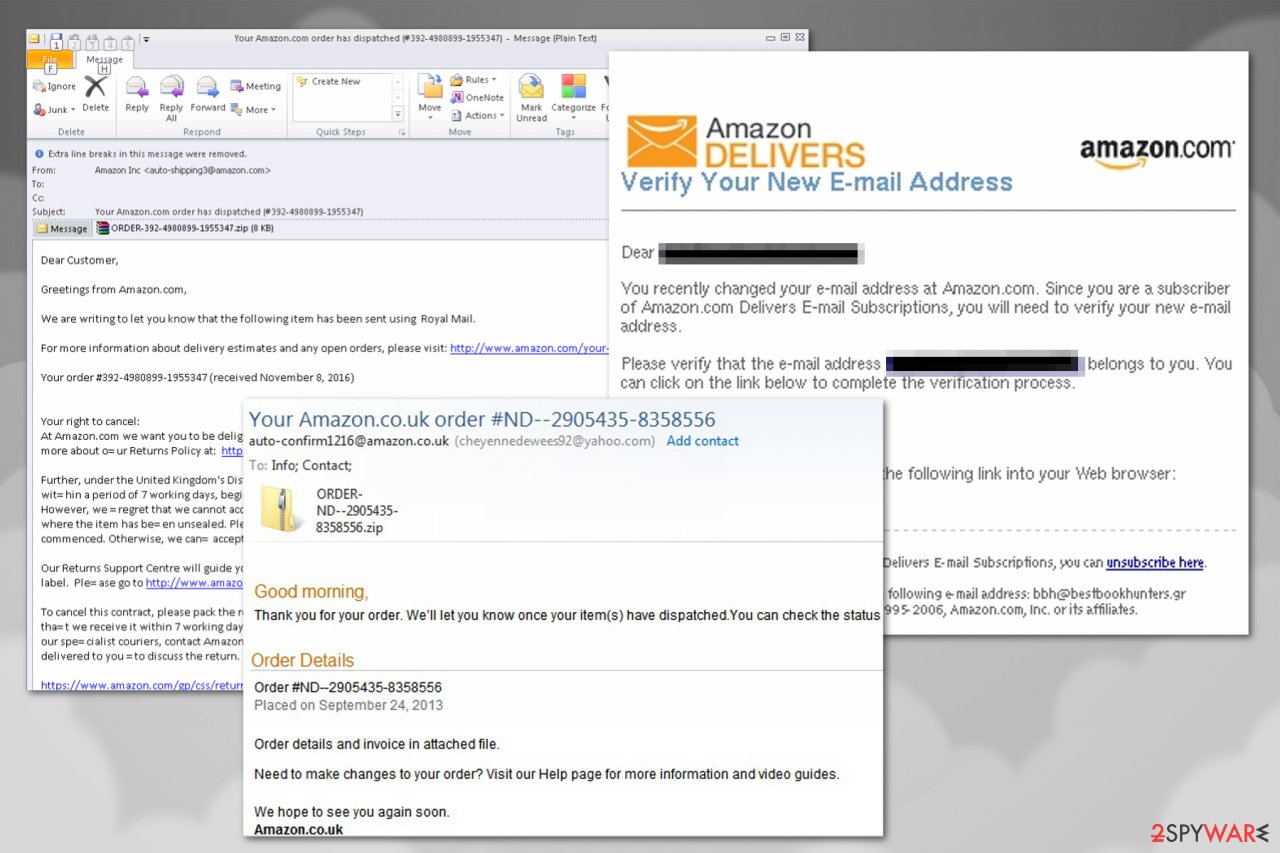
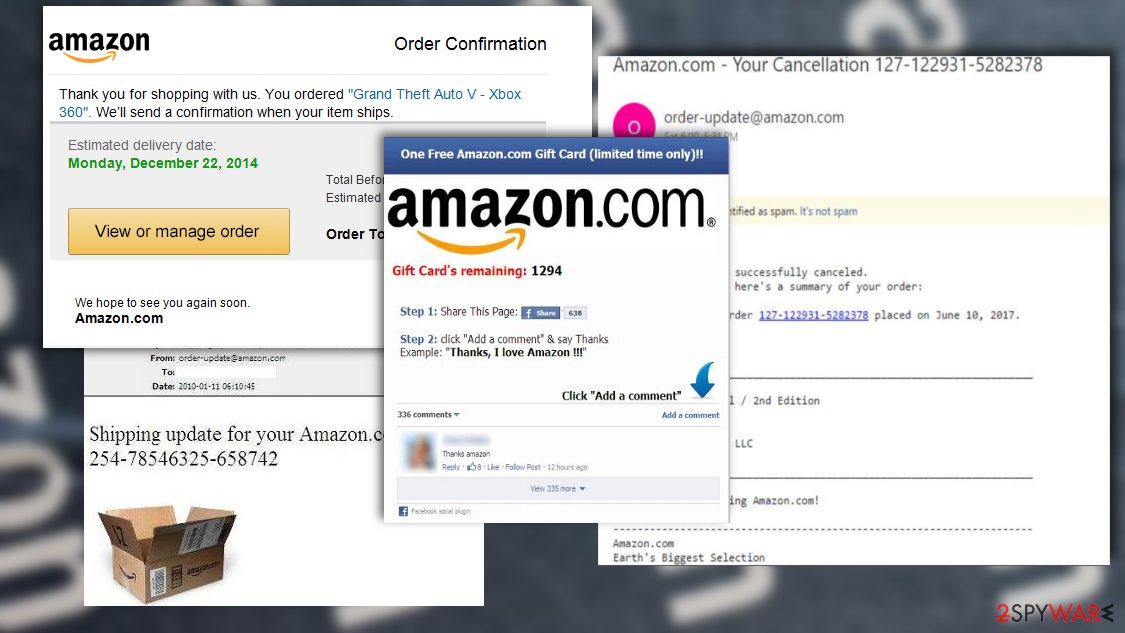
Amazon order confirmation scam
Amazon order confirmation scam is a cleverly compiled scam email that uses subject lines like “Your Amazon.com order, “Amazon order details,” or “Your order 162-2672000-0034071 has shipped.” As evident, crooks are trying to impersonate legitimate emails from Amazon, and are doing an excellent job to make the fake email believable.
Many people are using Amazon on a daily basis, so there is a high chance of it landing in an inbox of a user who is actually expecting an order from Amazon. This Amazon virus scam incorporates a malicious attachment, usually by the name “Order Details.” Once opened, the .doc. file requires shoppers to enable macro function – one of the main signs of malicious activities.
If granted, PowerShell commands[6] ensure the download and execution of Emotet banking trojan – this modular malware is capable of stealing personal information and uploading it on C&C server controlled by hackers, and also installing additional malware payloads.
You need to recognize Amazon virus to protect your data
Typically, deceptive emails or pop-up ads look like important notifications from Amazon company. However, there are several traits that they all contain. To remain safe and prevent the loss of your personal data, you should remember these basic rules:
- If you are actively using Amazon e-shop, pay attention to whether the products or services described in the received emails are related to your activity on the site.[7] If they are not – most likely, you are at the risk of getting scammed;
- Check the trustworthiness of the sender before opening ANY email and, especially, before clicking on the received link;
- Avoid downloading attachments if they were sent to you by senders that you don't even know;
- Do NOT enter your personal information to receive an invented gift card. You are recommended to contact Amazon before revealing personal details about yourself.
Pop-up ads are typically caused by adware on your computer
As we have already mentioned, all these hoaxes rely on misleading emails and pop-up ads that are used to help this them noticed. The main reason why misleading ads are bothering you is adware which can infiltrate your computer in a bundle with other programs.
Please, make sure you forget about installing freeware without checking what additional programs it has. For that, you should always opt for Custom or Advanced installation mode and deselect pre-checked check marks that agree with the installation of browser add-ons, extensions and plugins. Typically, these suspicious app claim that they can improve your searches on the web. However, all what they do is interrupting users while they are browsing on the web.
If you think that one of these programs is already hiding on your computer, there is a great danger that your machine is now infected with Amazon virus. If kept inside the system, it may easily record your keyboard clicks[8] and steal banking data or other personal information. In order to avoid identity theft, you have to remove Amazon virus ASAP.
Uninstalling Amazon virus might be tricky
Amazon virus has numerous different versions that may infect multiple parts of your computer's system. Therefore, uninstalling this cyber threat might get not only tricky or confusing but also impossible. Be aware that this malicious program might target your sensitive data, credentials or even help infiltrate ransomware. For this reason, automatic elimination is the best option.
If you think that your PC is infected with this virus or similar malware, you must scan your PC with an updated anti-spyware and delete malicious files from it. Amazon virus removal requires extreme care. Thus, make sure that the security software, is reliable, robust, and easy-to-use if you want to get rid of this cyber threat quickly without further damage.
To ensure the removal goes smoothly we highly recommended using reputable programs that would be able to clean your device. In case you do not have the ability to remove Amazon automatically, you can also delete the Trojan yourself. Follow the instructions below and complete all the indicated steps.
Although, keep in mind that trying to uninstall Amazon virus manually is challenging due to the complexity and diversity of the malware. Its components might be hidden in different locations all across your computer while deleting them all is a must. If you do not feel confident enough, please stick to the automatic elimination method.
Furthermore, in case you have been victimized by Amazon scam and provided your personal information for someone who wasn't allowed to get it, we suggest changing your banking information and taking other preventative steps to protect your sensitive data.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Amazon virus. Follow these steps
Manual removal using Safe Mode
To decontaminate the Trojan and carry out its removal properly, run your system in Safe Mode. We explain how to enter this mode below:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Amazon using System Restore
As we have already mentioned, Amazon virus may try to block your antivirus from scanning the system. In such a case, follow the steps below:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Amazon. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Amazon from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.In case you have opened a malicious and phishing email and opened the malicious file attached to it, your files probably got encrypted. If this happened, you shouldn't be able to open them now and most likely their filenames were modified, too. If this applies to you, you will need to find out what kind of malware has compromised your system. We highly recommend you to follow instructions provided in Method 1 and scan the system with anti-malware program. This way, you will find out what kind of virus infected your PC. Some ransomware viruses are weak and there are free decryption tools that you can use; however, if you manage to open an email sent by professional ransomware constructors, your files might not be recoverable. You can use data backups to restore them, or one of the techniques given below:
If your files are encrypted by Amazon, you can use several methods to restore them:
Data Recovery Pro
If you opened a malicious email from Amazon scammer and you cannot open your files anymore, try running Data Recovery Pro tool. This way, you can find recoverable files and restore them. Although this utility cannot decrypt files, it can help you restore a part of them.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Amazon ransomware;
- Restore them.
Windows Previous Versions
If you created a system restore point at some time in the past, you can try to restore your records using these steps. Remember that this method helps to recover individual files only.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Amazon registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting malware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Josh Fruhlinger. What is phishing? How this cyber attack works and how to prevent it. CSO. Security news, features and analysis about prevention.
- ^ What is a Trojan virus? - Definition. Kaspersky labs. Kaspersky Personal & Family Security Software.
- ^ Amazon email spoofing – virus alert!. NetworksPlusco.South Jersey IT and Web Services.
- ^ Zack Whittaker. Google let scammers post a perfectly spoofed Amazon ad in its search results. ZDnet. Technology News, Analysis, Comments and Product Reviews for IT Professionals.
- ^ Chris Hoffman. What Is a Botnet?. How-to Geek. Site that explains technology.
- ^ PowerShell. Microsoft. Windows IT Pro Center.
- ^ About identifying whether an E-mail is from Amazon. Amazon. Online Shopping for Electronics, Apparel, Computers, Books, DVDs & more.
- ^ Keystroke logging. Wikipedia. The free encyclopedia.





















