.anonimus.mr@yahoo.com virus (Virus Removal Guide) - Recovery Instructions Included
.anonimus.mr@yahoo.com virus Removal Guide
What is .anonimus.mr@yahoo.com virus?
.Anonimus.mr@yahoo.com virus is a crypto malware that originates from Animus actors

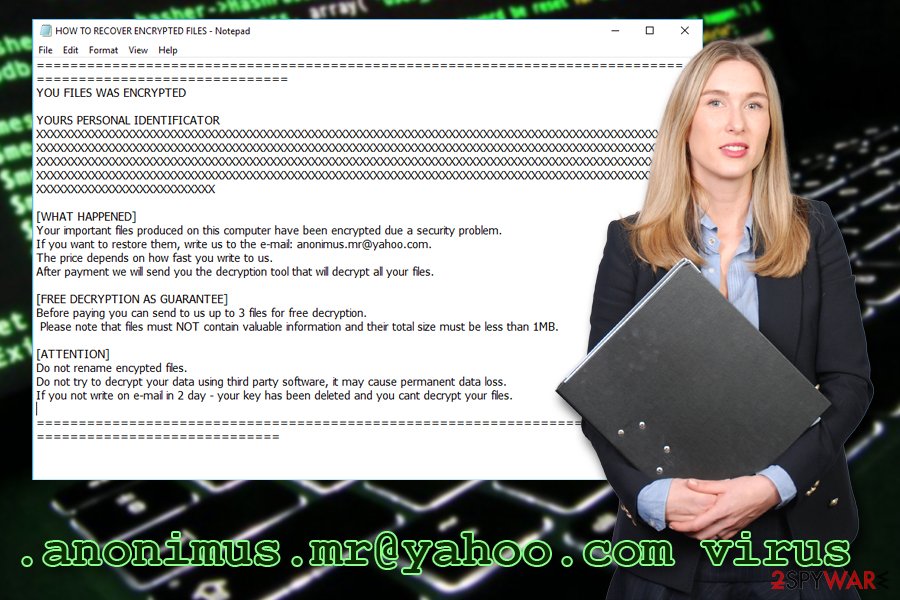
.Anonimus.mr@yahoo.com virus is a new threat that appeared early August 2018. According to researchers, authors of Animus switched over to using Scarab ransomware code. Extortionists use AES[1] military-grade encryption algorithm to lock up personal data, which makes files unusable and appends the .anonimus.mr@yahoo.com extension to each of the affected files. Unfortunately, only hackers have access to the decryption tool, and victims need to pay ransom in cryptocurrency (typically Bitcoin) for it. All the information about the virus ransomware can be found in a ransom note called HOW TO RECOVER ENCRYPTED FILES.TXT which is placed into each of the compromised files' folder.
| Summary | |
| Name | .anonimus.mr@yahoo.com virus |
| Type | Ransomware |
| Related ransomware | Animus ransomware |
| A variant of | Scarab ransomware |
| Cipher used | AES |
| Ransom note | HOW TO RECOVER ENCYPTED FILES.TXT |
| Contact email | anonimus.mr@yahoo.com |
| Decryption | Backups or third-party apps only, no official decryptors created yet |
| Elimination | Use reputable security software like FortectIntego or Malwarebytes |
AnimusLocker ransomware was quickly deciphered by malware hunters and became ineffective in a short period of time. Thus, researchers believe that due to the inability to fix flaws in its own code, hackers resorted to using more sophisticated one – Scarab. Although files of the several variants of the latter can be recovered using official decryptors, the experts still did manage to crack .anonimus.mr@yahoo.com virus' code yet.
The .Anonimus.mr@yahoo.com virus enters machines in deceptive ways, but devices that are unprotected by security software are especially vulnerable. Therefore, malware researchers[2] recommend having powerful security software installed at all times. We highly recommend either FortectIntego or Malwarebytes.
.Anonimus.mr@yahoo.com ransomware makes several changes to the infected device:
- Modifies Windows Registry.[3] This allows the virus to be launched with every Windows boot.
- Deletes Shadow Volume Copies. This is the automatic Windows backup system.
- Modifies all personal files by adding .anonimus.mr@yahoo.com file extension.
Several different files can be affected, including .doc, .pdf, .html, .dat, .zip, .jpg, .mp3 and similar. For example, picture.jpg is turned into picture.jpg..anonimus.mr@yahoo.com. Soon after locking the data, the crypto-virus uploads the ransom note on victims' computer that states the following:
YOU FILES WAS ENCRYPTED
YOURS PERSONAL IDENTIFICATOR
XXX [redacted]
[WHAT HAPPENED] Your important files produced on this computer have been encrypted due a security problem. If you want to restore them, write us to the e-mail: anonimus.mr@yahoo.com. The price depends on how fast you write to us. After payment we will send you the decryption tool that will decrypt all your files.
[FREE DECRYPTION AS GUARANTEE] Before paying you can send to us up to 3 files for free decryption. Please note that files must NOT contain valuable information and their total size must be less than 1MB.
[ATTENTION] Do not rename encypted files. Do not try to decrypt your data using third party software, it may cause permanent data loss. If you not write on e-mail in 2 day – your key has been deleted and you cant decrypt your files.
Hackers offer victims the “free” decryption service to prove that they can decode data. Please do not contact these people and remove .anonimus.mr@yahoo.com virus from your computer instead. Regardless of what they say, you might not get any files back, as they might simply ignore you.
As soon as you perform full .anonimus.mr@yahoo.com removal, you can try to recover your data. Unfortunately, the only safe way to decrypt files is by using backups. If you do not possess one, you can try to use third-party software, although chances of recovery are pretty low.
Do not open spam emails casually – ransomware can be hidden inside
Spam emails have been around as long as the online advertisement was active – since the early 90s. While most of the spam emails that enter your inbox are most likely harmless, several phishing emails can end up there as well. The worst part is that some phishing emails are so well engineered that it is quite hard to recognize whether or not the message is legitimate or fake.
It is true that many genuine emails might end up in the Spam folder. Therefore, you do not have to eliminate all of them straight away. Nevertheless, be sure to pay attention and learn to recognize fake emails. Check for grammar and/or spelling mistakes, questionable formatting, the referral (Dear Customer, Dear User and similar) and especially the “From” address, as is the best giveaway when it comes to phishing emails. If you notice anything suspicious, remove the email without thinking and never open attachments or click on links inside.
Additionally, security researchers recommend avoiding suspicious file-sharing, porn, and similar sites and installing reputable security software. Finally, updating backups regularly is a must.
Eliminate .anonimus.mr@yahoo.com virus and then proceed with file recovery
Like we already mentioned, you should not proceed with file recovery before you remove the .anonimus.mr@yahoo.com virus from your computer entirely. While it is possible to get rid of the malware manually, it is not recommended, as several changes made to the system makes it very difficult.
Therefore, we recommend downloading and installing FortectIntego or Malwarebytes for a full .anonimus.mr@yahoo.com virus removal. Be aware that malware might block security software. In such case, enter Safe Mode with Networking and start the scan from there.
Only when the .anonimus.mr@yahoo.com elimination is completed, you can proceed with file decryption. Either get them back from a backup or use third-party software. For the latter, check the instructions below.
Getting rid of .anonimus.mr@yahoo.com virus. Follow these steps
Manual removal using Safe Mode
To remove .anonimus.mr@yahoo.com virus safely, enter Safe Mode with Networking:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove .anonimus.mr@yahoo.com using System Restore
You can also disable the virus by using System Restore:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of .anonimus.mr@yahoo.com. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove .anonimus.mr@yahoo.com from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.Although there is no official decryptor released yet, we do not recommend contacting cybercriminals. They might simply ignore you and never send you the key. Thus, you would be left with neither your files or money. If you have no backup, try one of the methods below.
If your files are encrypted by .anonimus.mr@yahoo.com, you can use several methods to restore them:
Data Recovery Pro might help you
Data Recovery Pro is an application designed to recover damaged or accidentally deleted files. In some cases, however, it does help to get back the data that was encrypted by ransomware.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by .anonimus.mr@yahoo.com ransomware;
- Restore them.
Windows Previous Versions Feature could help you to recover separate files
This method only works if you had System Restore function enabled before the cyberattack occurred.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Try ShadowExplorer
ShadowExplorer will help you if the virus failed to delete Shadow Volume Copies.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No official decryptor is available yet
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from .anonimus.mr@yahoo.com and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Margaret Rouse. Advanced Encryption Standard (AES). SearchSecurity. Knowledge base of security industry.
- ^ OdstranitVirus. OdstranitVirus. Cybersecurity news and articles.
- ^ Structure of the Registry. Microsoft. Docs.







