Apple.com-fixing.live (Free Instructions) - Removal Guide
Apple.com-fixing.live Removal Guide
What is Apple.com-fixing.live?
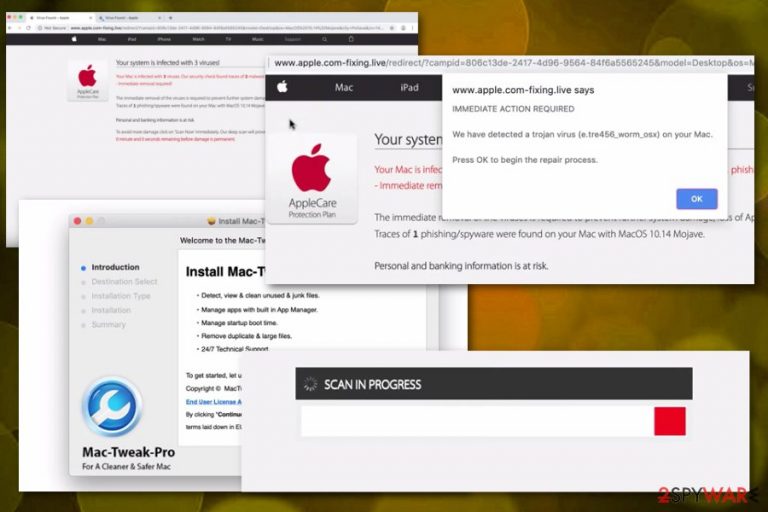
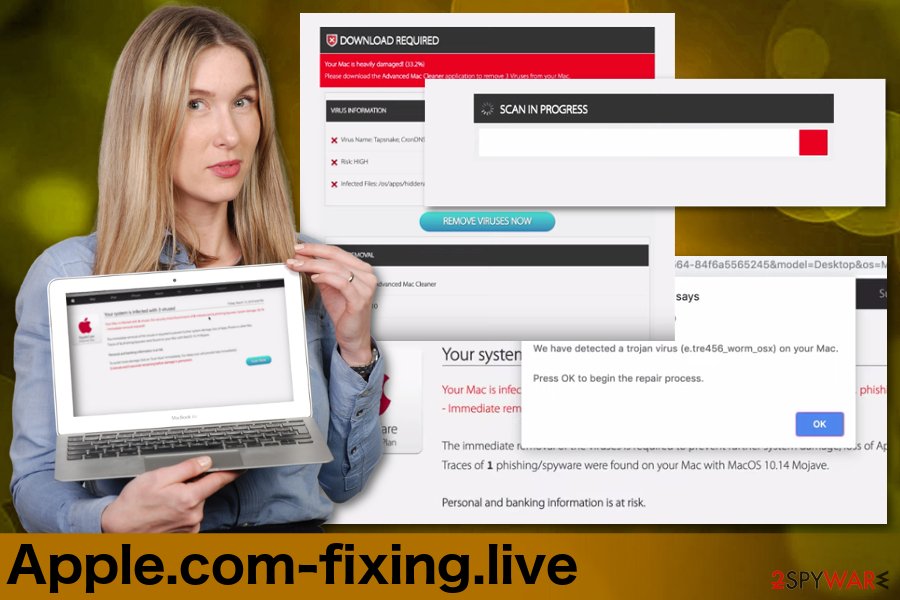
Apple.com-fixing.live is a MacOS targeting adware program that scares people into thinking their device is infected with trojans and other malware
| Name | Apple.com-fixing.live |
|---|---|
| Type | Adware |
| Purpose | Trick people into installing rogue software |
| Similar to | |
| Also installs | Mac-Tweak-Pro |
| Targeted system | Mac operating system |
| Distribution | Insecure websites, installations |
| Removal tips | Use an anti-malware tool and scan the system to remove Apple.com-fixing.live from the PC |
Apple.com-fixing.live virus is the program similar to many other Mac malware[2] variants that pose as an official Apple website. However, the message stating about the malware issue on your device is not a legitimate alert, and your device is not infected with three viruses or any other malware. The only intruder that is causing these pop-ups is adware which is designed to distribute other rogue tools.
When you get redirected to this website, Apple.com-fixing.live delivers a message and immediately offers to scan the device. When you choose to do so, the results may appear scarier because of all the Trojans, malware and other intruders indicated on the list.
Apple.com-fixing.live is designed to lure people into installing allegedly helpful tools with the purpose of fixing the issues and removing malicious programs. Unfortunately, these applications that get automatically installed cause more PUP-type behavior as such:
- constant redirects to commercial websites;
- pop-up windows with intrusive ads;
- questionable apps installed without your consent;
- the general slowness of the machine.
Various other PUPs like Apple.com-fixing.live offers and installs tools that give no value to your device. In particular, Mac Tweak Pro is one of many other fake tools promoted online that only show more falsified scan results and encourage people to purchase other versions or even buy the licensed version of the program.
You need to remove Apple.com-fixing.live as soon as possible and uninstall all software added without your consent because these programs only affect the registry entries and cannot remove actually dangerous programs or files. For this reason that adware causes additional installations, you need to get a professional anti-malware tool for the virus removal process.
Software like FortectIntego or any similar antivirus program can help with the Apple.com-fixing.live removal and improve the performance of your computer overall. Various researchers[3] advise cleaning the machine thoroughly using reputable tools so all those intruders can be eliminated.
Insecure online surfing may lead to additional PUP infiltrations
When you browse online every day and spend most of the time on the internet, paying enough attention to websites, you visit, and content you click on becomes a crucial thing. When you regularly click on commercial content and get redirects to suspicious sites you get exposed to possibly malicious content.
Often visiting questionable pages may lead to the installation of unwanted programs or infiltration of potentially unwanted programs like adware or browser hijackers. This can also be the issue when you willingly get software or applications from the internet.
Using less than reliable sources for your programs often mean that you get more than the program you wanted to get in the first place. However, this can be avoided because choosing Advanced or Custom options during the installation process give you the opportunity to see all the programs on the list and de-select unwanted ones.
A full system scan is required for Apple.com-fixing.live termination
To remove any program like adware, scareware, browser hijackers or this particular Apple.com-fixing.live virus there is a need for the proper tool. Antivirus programs can check your machine for any malicious intruders, outdated software or corrupted files.
Apple.com-fixing.live removal especially requires reliable anti-malware tools because this adware installs other programs to your computer without permission. A full system scan can indicate all possibly dangerous programs and delete them from your device.
There is no need for advanced knowledge of IT or computers. You can remove Apple.com-fixing.live automatically by using the correct program. However, you should also manually check your browser settings and delete suspicious extensions or add-ons that may be installed by the adware.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Apple.com-fixing.live. Follow these steps
Delete from macOS
Apple.com-fixing.live can affect more than the browser on your MacOS supporting device, so check the system thoroughly
-
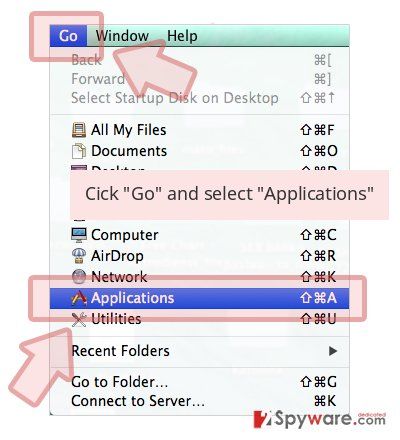
If you are using OS X, click Go button at the top left of the screen and select Applications.

-
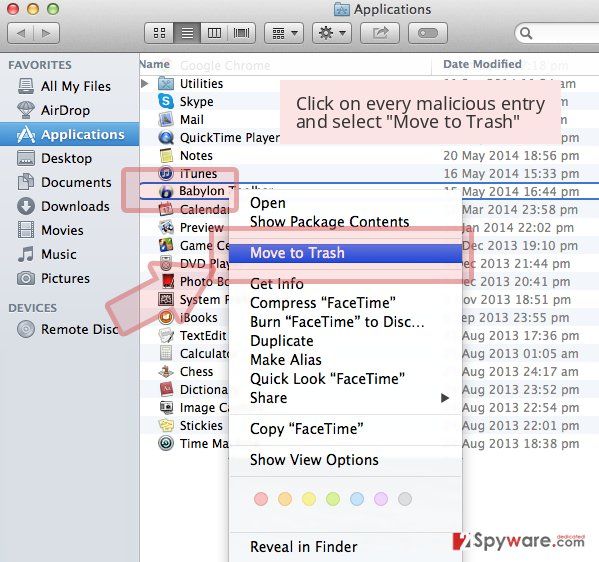
Wait until you see Applications folder and look for Apple.com-fixing.live or any other suspicious programs on it. Now right click on every of such entries and select Move to Trash.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select the unwanted extension and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Settings.
- Under Home, set your preferred homepage and new tab settings.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data and Temporary cached files and pages, then click Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
Google Chrome may include other Apple.com-fixing.live-related applications. Check for them and delete any suspicious programs
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all suspicious extensions related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
Make sure to clean the browser and eliminate all possibly dangerous apps or extensions
-
Remove dangerous extensions
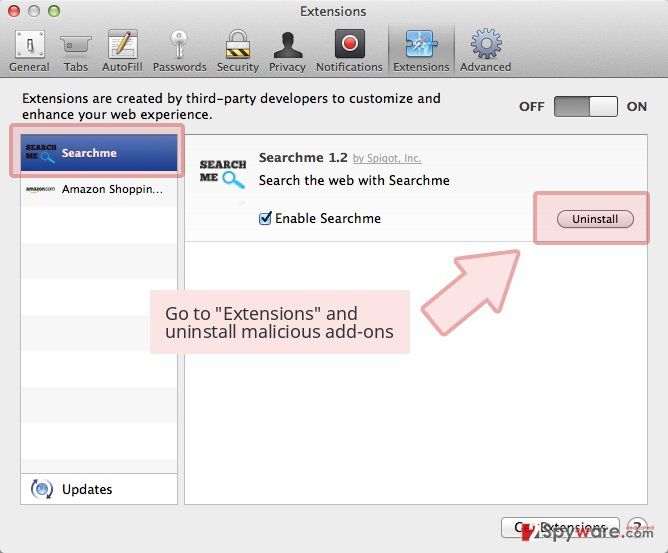
Open Safari web browser and click on Safari in menu at the top left of the screen. Once you do this, select Preferences.
-
Here, select Extensions and look for Apple.com-fixing.live or other suspicious entries. Click on the Uninstall button to get rid each of them.

-
Reset Safari
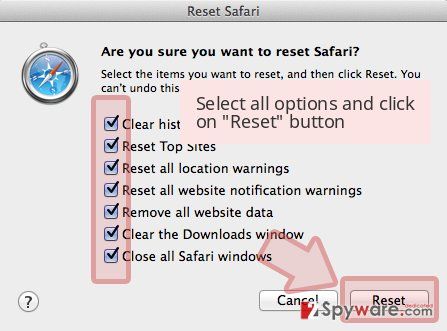
Open Safari browser and click on Safari in menu section at the top left of the screen. Here, select Reset Safari....
-
Now you will see a detailed dialog window filled with reset options. All of those options are usually checked, but you can specify which of them you want to reset. Click the Reset button to complete Apple.com-fixing.live removal process.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Apple.com-fixing.live registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting adware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Social engineering. Wikipedia. The free encyclopedia.
- ^ Jonny Evans. Warning as Mac malware exploits climb 270%. Computerworld. IT news, careers, business technology.
- ^ Lesvirus. Lesvirus. Spyware related news.