AssistiveTask mac virus (Free Guide)
AssistiveTask mac virus Removal Guide
What is AssistiveTask mac virus?
AssistiveTask is an adware-type virus that sneakily targets Mac systems
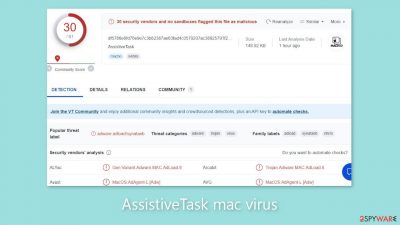
AssistiveTask, an Adload malware family member, is malicious software designed specifically for Mac operating systems. This virus has adware and hijacking capabilities, resulting in the appearance of bothersome elements such as pop-ups, banners, redirects, and changes to browser settings. This behavior not only irritates users, but it also poses significant risks.
The truth is that, contrary to popular belief, Mac systems are vulnerable to malware attacks. Malicious developers are constantly devising new ways to circumvent Apple's security system, XProtect,[1] and Adload is no exception. Surprisingly, they achieved this by purposefully omitting any discernible patterns in their code. We have previously discussed various versions of this virus, including ChannelLegion, UpgradeControl, and SharedKey.
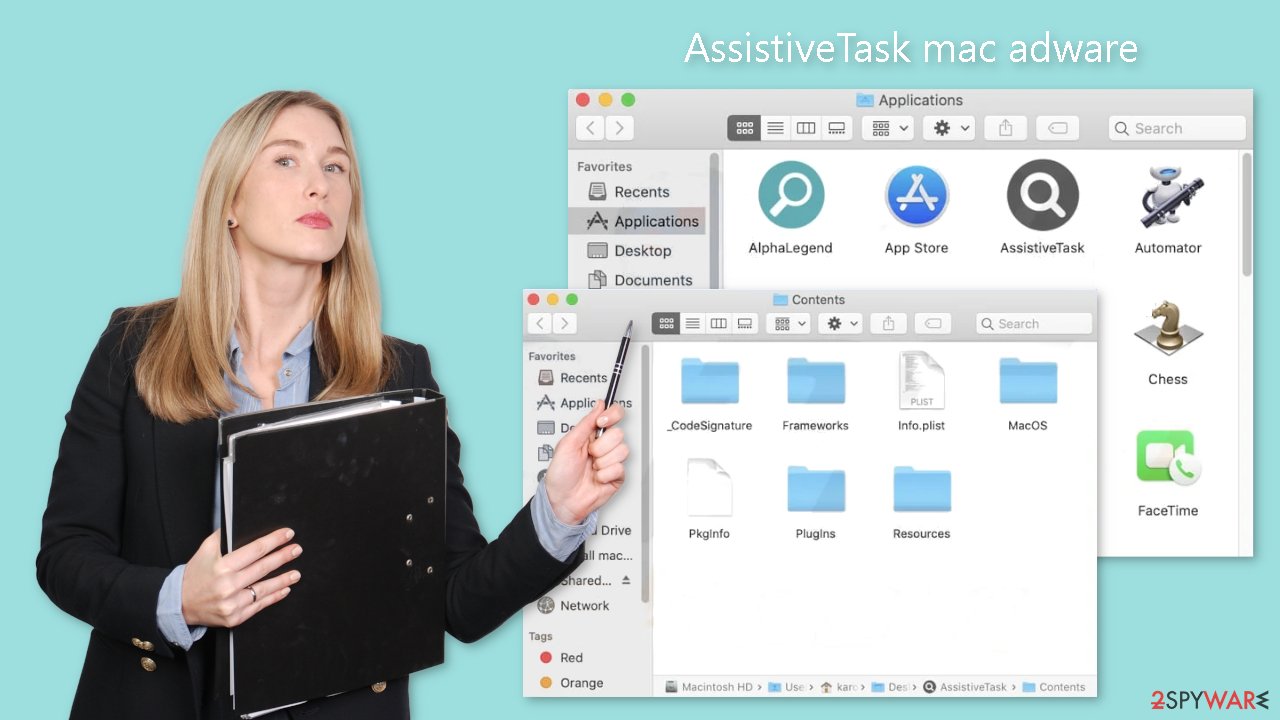
These versions have one thing in common: an icon of a magnifying glass enclosed within a green or teal-colored circle. If you find this icon in your “Applications” folder, it is almost certainly the source of your constant redirection to questionable websites and bombardment with advertisements. Adload is more aggressive than typical adware designed for Windows systems because it can install other potentially unwanted programs (PUPs)[2] and malware on Mac devices without the users' knowledge.
| NAME | AssistiveTask |
| TYPE | Adware, browser hijacker, mac virus |
| MALWARE FAMILY | Adload |
| SYMPTOMS | Changed homepage, new tab address, and search engine; redirects to shady websites; an increase of commercial content; decrease in performance |
| DISTRIBUTION | Fake software updates, deceptive ads, torrent websites |
| DANGERS | Altered search results can lead to dangerous websites; pop-up ads might be promoting scams; the virus can install other PUPs or even malware without the users' knowledge |
| ELIMINATION | Eliminating an adload virus manually can be quite complicated if you do not have experience. The easiest and most effective is to open a professional security tool and scan your system to delete every related file |
| FURTHER STEPS | FortectIntego should be used to completely wipe out any data left and fix the remaining damage |
The particular danger posed by this Mac virus is that most users become aware of its presence only after it has begun to carry out its malicious activities. Through a deceptive technique, this malware is capable of collecting user data and stealing the administrator password. It generates a prompt that is identical to a genuine system prompt, tricking users into entering their administrator password.
Once this malicious program has obtained the necessary information, it can cause significant damage to your system. It can launch malicious scripts and secretly install additional malware without your knowledge. If left undetected, this infection can lead to the presence of various intruders within your machine, including spyware, adware, hijackers, and crypto miners.
Furthermore, the average user will find it difficult to completely remove Adload from their machine. The virus disperses its files throughout the system, making it difficult to locate each file. This highlights the significance of using professional security tools. A device without antivirus software is analogous to a house without a door. It is clear that Apple's native security system is falling behind, forcing users to employ additional security measures to effectively protect themselves.
Adload distribution methods
Users are frequently infected with viruses such as Adload as a result of their careless web browsing. Because users believe that Apple devices are immune to infection, they browse carelessly, clicking on random links and visiting suspicious websites. Fraudsters use fake Flash Player installations as one of their primary methods of infecting people.
The scam works by informing users that their Flash Player is out of date and that they must update to the most recent version in order to access certain content. Many people do not hesitate to click the “install” button. However, Flash Player no longer exists, having been phased out in 2020 and replaced by HTML5.[3]
Unfortunately, many users are still unaware of this fact, endangering their systems. If you come across a website urging you to install a new Flash Player, it is almost certainly a scam. Another popular way to obtain AssistiveTask is to download “cracked” software from torrent websites.
These platforms operate illegally and in violation of regulations. There are no organizations that examine the listed programs to ensure their safety. As a result, peer-to-peer file-sharing platforms have become a haven for potentially unwanted applications (PUAs) and malware. Regardless of the potential cost, it is best to obtain software from official web stores and developer websites to protect yourself.
The programs available on reputable online marketplaces have been thoroughly reviewed. Investing in secure software helps keep your system safe from intruders in the long run, potentially saving you money on costly repairs. Always conduct extensive research before installing anything from random websites. Examine reviews and look for press releases. A lack of search results for rogue applications is frequently encountered, which should raise a red flag.
Removal of AssistiveTask Mac virus
Manual removal of the virus is not recommended unless you have a thorough understanding of the required actions and the specific files that must be deleted. Some of these files may end in .plist, which is a standard settings file used by macOS applications. These files, also known as “properties files,” contain program configuration settings and properties. Furthermore, the virus employs multiple persistence techniques and scatters files throughout the system, making removal of browser extensions and applications associated with it difficult.
We recommend using professional anti-malware tools such as SpyHunter 5Combo Cleaner or Malwarebytes to ensure peace of mind and effective removal. These tools are intended to detect and remove unwanted programs, including viruses. Furthermore, because it is unknown whether the virus installed any additional malicious programs, using these tools is the safest way to ensure the system is thoroughly cleaned.
If you still want to try and delete it manually, proceed with these steps:
- Open Applications folder
- Select Utilities
- Double-click Activity Monitor
- Here, look for suspicious processes related to adware and use Force Quit command to shut them down
- Go back to the Applications folder
- Find AssistiveTask in the list and move it to Trash.
If you are unable to shut down the related processes or can't move the app to Trash, you should look for malicious profiles and login items:
- Go to Preferences and select Accounts
- Click Login items and delete everything suspicious
- Next, pick System Preferences > Users & Groups
- Find Profiles and remove unwanted profiles from the list.
There are likely to be more .plist files hiding in the following locations – delete them all:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
![Uninstall from Mac 2 Uninstall from Mac 2]()
The manual elimination process might not always result in full virus removal. Therefore, we still strongly suggest you perform a scan with security software.
Remove the extension
AssistiveTask also installs a browser extension that performs a variety of unwanted tasks. It may collect sensitive data and send it to tracking servers. The user's IP address, username, macOS version, browser versions, computer ID, items in the “Applications” folder, and a list of agents, daemons, and system configuration profiles may all be exposed.
It is critical to remove the browser add-on as soon as you have removed the dangerous files from your system. You can also use FortectIntego to delete cookies and cache automatically. This tool will also repair any damaged files and system errors, resulting in improved machine performance.
If you prefer to handle the removal process yourself, below are instructions specifically for Google Chrome and Mozilla Firefox, located at the end of this article:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
Cookies and website data:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
The simplest and quickest solution to this is completely resetting Safari:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.
![Reset Safari Reset Safari]()
Getting rid of AssistiveTask mac virus. Follow these steps
Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Protecting against malware in macOS. Apple. Support Page.
- ^ Potentially Unwanted Application. TrendMicro. Cyber Definitions.
- ^ HTML5. Wikipedia, the free encyclopedia.











