ChannelLegion Mac virus (Free Guide)
ChannelLegion Mac virus Removal Guide
What is ChannelLegion Mac virus?
ChannelLegion is Mac malware that can damage your security online
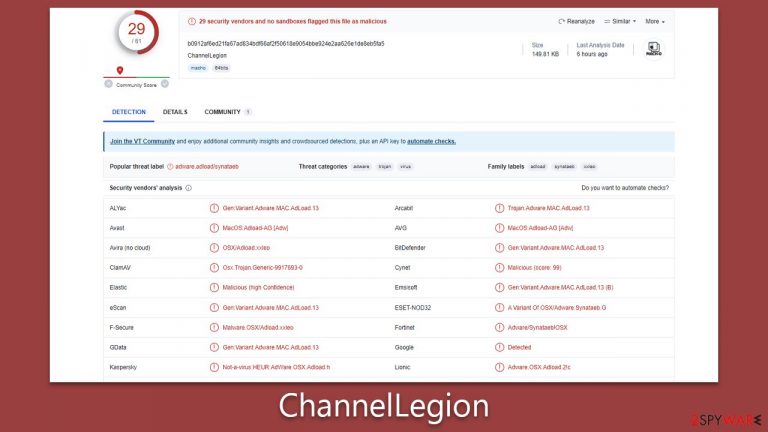
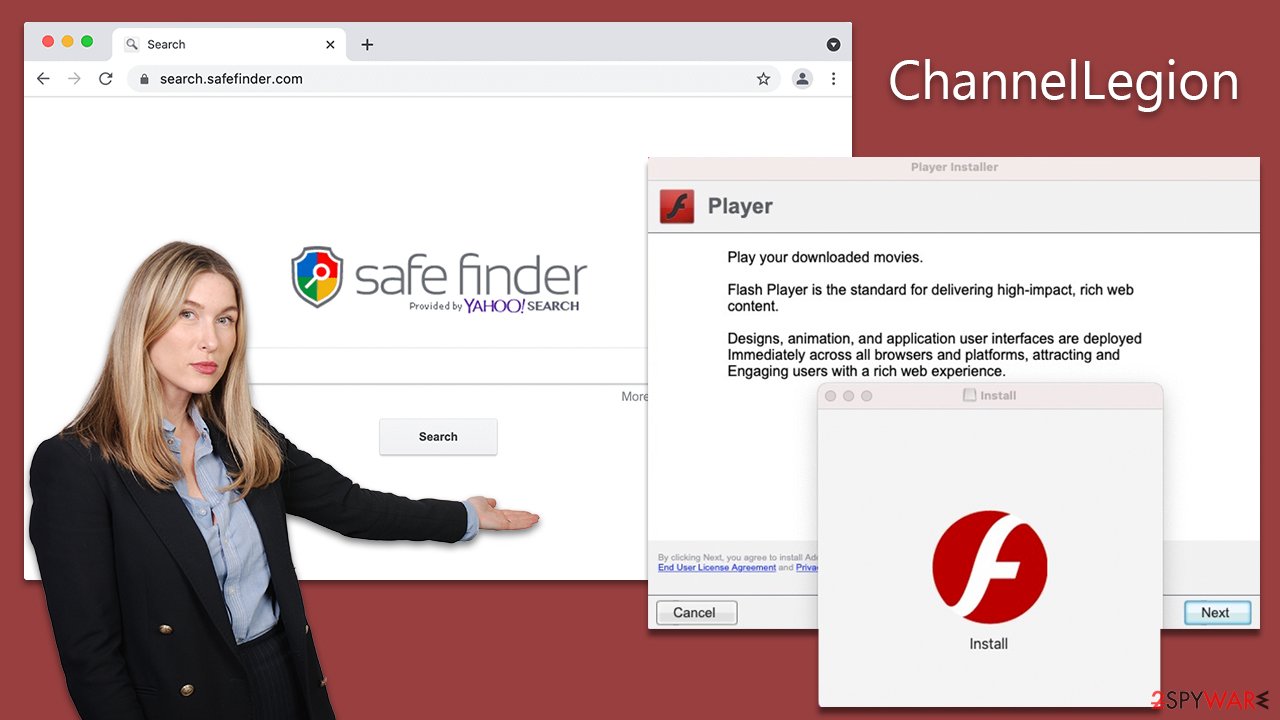
ChannelLegion, a derivative of the well-documented Adload malware family, has emerged as a substantial threat to the cybersecurity landscape. This malicious software proliferates primarily through counterfeit Flash Player updates and unauthorized software installers or cracks. Its dual-component structure, which includes an extension and a primary application, contributes to its resilience against removal attempts and allows for the possibility of further iterations to be installed.
The potential for data compromise is a significant concern associated with the ChannelLegion virus. The installed extension can clandestinely harvest sensitive data, creating considerable privacy and security risks for users. Furthermore, the ability of ChannelLegion to alter browser configurations, enabling it to divert internet traffic via a Man-in-The-Middle proxy, significantly expands its eavesdropping capabilities.
An additional distinguishing feature of ChannelLegion is its proficiency in circumventing in-built defenses, thereby compromising systems that are otherwise considered secure. For individuals impacted by this malware, detailed removal instructions for this malware are provided below.
| Name | ChannelLegion |
| Type | Mac virus, adware, browser hijacker |
| Malware family | Adload |
| Distribution | Third-party websites distributing pirated software, software bundles, fake Flash Player updates |
| Symptoms | Installs a new extension and application on the system; changes homepage and new tab of the browser; inserts ads and malicious links; tracks sensitive user data via extension |
| Removal | The easiest way to get rid of Mac malware is by doing a full system scan with SpyHunter 5Combo Cleaner security software. If you'd rather remove it manually, see the guide below |
| System optimization | After you terminate the infection with all its associated components, we recommend you also scan your device with FortectIntego to clean your browsers and other leftover files from the virus |
Mac malware and Adload
There was a time when the general public believed that Mac devices were immune to cyber threats, their architecture ostensibly resistant to the variety of malware that plagued other systems. However, the evolution of the cybersecurity landscape and the increased sophistication of cybercriminals have unequivocally debunked this myth. In recent years, Mac devices have increasingly been targeted, succumbing to a variety of digital threats.
A key player in this landscape is Adload, a prolific malware family from which ChannelLegion is derived. Since its initial discovery in 2017, Adload has been prolific, releasing countless variants such as UpgradeControl, SharedKey, CommonHandler, among others. These strains, despite minor differences among them, generally retain the same operational and distribution methods.
A key identifier of an Adload infection is the recurring use of a magnifying glass icon for both the primary application and associated browser extension, a feature consistent across its variations.
While ChannelLegion is technically classified as adware, it's important to note that its impact extends far beyond mere advertisement displays. Its largely detrimental functionalities align more with traditional malware, thus making it, and by extension, the Adload family, a significant threat to Mac users. It exemplifies the increasing complexity and potency of threats facing modern Mac systems, highlighting the need for stringent security measures.
Malware removal explained
The removal of ChannelLegion, much like Adload's other variants, poses challenges due to the virus's ability to run with elevated system privileges. It not only deposits harmful files but also establishes new profiles and login items. Assisted by AppleScript, the virus has the capability to circumvent detection by security mechanisms such as XProtect and Gatekeeper. Removing the core files of the main application or extension does not guarantee a resolution, as they may easily resurface.
To ensure a thorough removal, using anti-malware software such as SpyHunter 5Combo Cleaner or Malwarebytes is recommended. These tools can efficiently identify and eliminate malicious files, including persistent components. Regular updates to these software solutions are necessary to keep up with evolving threats. This approach offers the best chance of successfully eliminating ChannelLegion from your Mac and securing the system against future infiltrations.
However, if you opt for a manual removal process, we provide detailed instructions below. Bear in mind that remnants of the virus left on the system could enable its return. Initiating the manual process should begin with accessing the Activity Monitor to terminate any processes associated with ChannelLegion. After that, efforts can be made to remove the primary application.
Additionally, system optimization and browser cache cleaning are integral for a comprehensive clean-up process. FortectIntego is an effective tool for this purpose, ensuring any lingering traces of the virus are purged. Despite the availability of manual instructions, it's worth noting that an automated approach using dedicated software is generally more reliable, hence highly recommended.
- Open Applications folder
- Select Utilities
- Double-click Activity Monitor
- Here, look for suspicious processes and use the Force Quit command to shut them down
- Go back to the Applications folder
- Find the malicious entry and place it in Trash.

Deleting unwanted profiles and Login Items is necessary when trying to eliminate malware from a Mac.
- Go to Preferences and pick Accounts
- Click Login items and delete everything suspicious
- Next, pick System Preferences > Users & Groups
- Find Profiles and remove unwanted profiles from the list.
The PLIST files are small config files, also known as the “Properly list.” They hold various user settings and hold information about certain applications. To remove the virus, you have to find the related PLIST files and delete them.
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and delete all the related .plist files.

Checking your browser and removing the extension component
The ChannelLegion extension plays a pivotal role in the functioning of the virus. It orchestrates significant alterations to essential browser settings such as the homepage, new tab address, and search provider. This manipulation allows the delivery of a continuous flow of intrusive ads to the user. More alarmingly, with this extension, the malware can access and amass all data entered into the browser, which could include sensitive information such as account passwords and credit card details.
For those who opted for the automatic removal method, the extension should already have been eradicated, hence posing no further concern. However, if you chose the manual route, it's essential to verify the successful deletion of the extension as follows:
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

After ensuring the removal of the extension, it is crucial to clear your browser's caches, including Safari or any other browser in use. Cache memory often retains data from previously visited websites, which could potentially harbor remnants of the malware. Equally important is the deletion of cookies, which are frequently utilized for tracking user activities and can be manipulated by malicious software.
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Finally, you may have noticed that the virus' browser extension has returned, or you were not able to eliminate it in the first place. If that's the case for you, you should opt for a full browser reset.
Safari
- Click Safari > Preferences…
- Go to the Advanced tab.
- Tick the Show Develop menu in the menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

Google Chrome
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
