Basicnetworkpc.com ads (scam) - Tutorial
Basicnetworkpc.com ads Removal Guide
What is Basicnetworkpc.com ads?
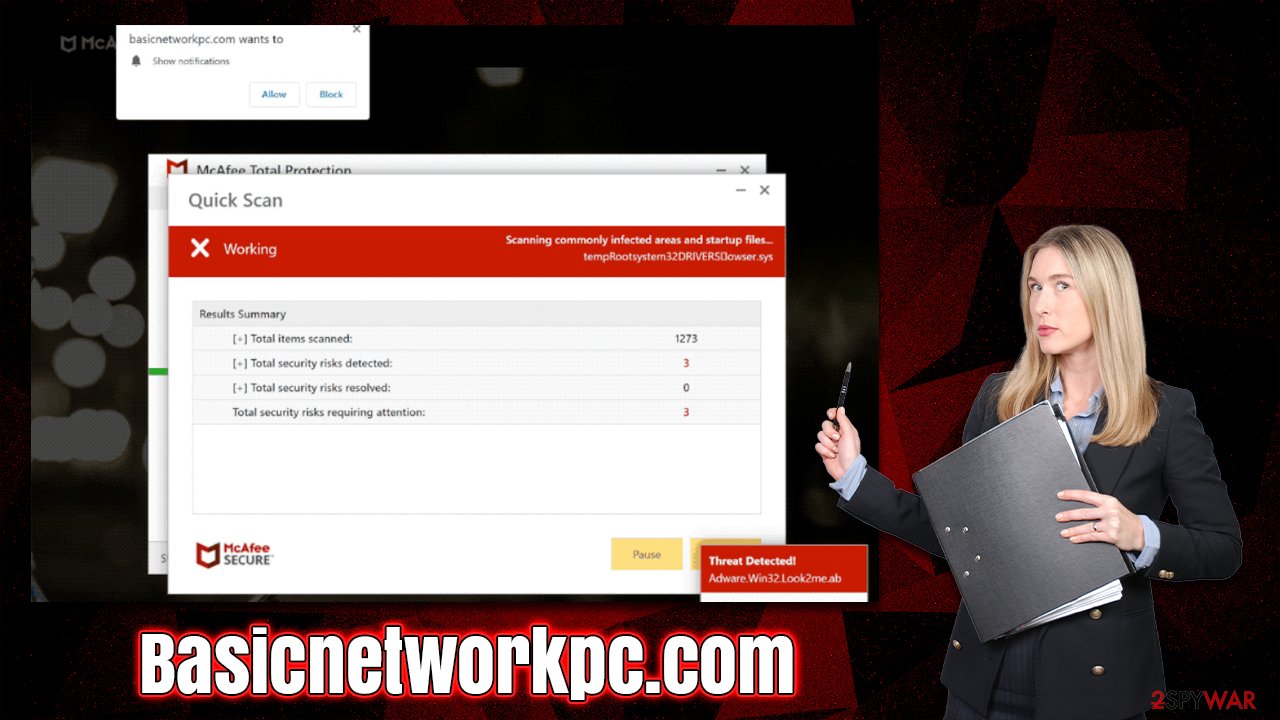
Basicnetworkpc.com attempts to convince people to purchase security software using scam techniques

Basicnetworkpc.com is just one of the sites that try to look like a credible security vendor in order to get people to click on its links and buy software from affiliates. People might come across this malicious page at any time while browsing online using Chrome, Safari, Edge, Firefox, or any other web browser. It's likely that users will be redirected here when they click on a bad link somewhere else – these can often be found on torrents, illegal video streaming sites, and similar websites.
Adware can often redirect users to phishing[1] sites, especially if this activity is accompanied by an increased number of advertisements. This is important to note, as removing the adware from your system could stop the Basicnetworkpc.com redirects for good. Also, if you have enabled push notifications from the site, you should access browser settings to stop them – we explain how to perform all these steps below.
| Name | Basicnetworkpc.com |
| Type | Scam, phishing, redirect, adware |
| Operation | A message claims the subscription for security software has expired and needs to be immediately renewed to remove the allegedly found viruses on the system |
| Distribution | Compromised websites, pop-up ads, potentially unwanted applications |
| Risks | Installation of PUPs or malware, sensitive information disclosure, financial losses |
| Removal | You should not interact with the contents shown by a scam website and check your device with legitimate security software to check for adware |
| Other tips | Third parties can use cookies to continue tracking your online activities, so we recommended clearing browser caches and other leftover files with FortectIntego |
Many internet scams are successful because they exploit people's fears. For example, users may receive a message informing them that their computer is infected with a virus. These messages can be convincing, especially if they appear to come from reputable sources such as Google, Microsoft, or Apple.
However, even if you don't know much about how malware works, there are some things you can do to protect yourself and avoid becoming the victim of fraud, and one of the main prevention measures is getting familiar with how these scams operate and what signs to look out for.
Misleading claims about computer security
When users first enter Basicnetworkpc.com, they're immediately greeted with a blue warning message that looks very similar to the Windows Blue Screen of Death.[2] Immediately after that, an alleged system scan begins – users can see the items being scanned, and pop-ups of supposedly malicious files also come up. One of the pop-up messages that come up claims that users have visited illegal websites:
Security Alert
You've visited illegal infected website
You have visited unsafe site with illegal content
Your PC is at risk of being infected by viruses
To continue browsing safely – perform an antivirus scan
Soon after, visitors are told that their systems have been infected with five viruses that need to be removed immediately – they are also suggested to use the “Proceed” button, which would link them to the purchase page of McAfee security.
While the software might be legitimate, the means for advertising it are not, hence proceeding with the purchase is not recommended. Besides, since McAfee itself has nothing to do with the Basicnetworkpc.com website or its contents, redirecting to fake pages where malicious links are hosted is also possible.
How to check for and remove adware or other malware from your system
If you're seeing more ads than usual or being redirected to strange websites, it's time to check your device for infections. Adware is a type of malicious software that forces users to see pop-ups, deals, and other advertisements while also collecting their data in the background. In some cases, it can even include personal details like addresses and credit card details, which would be a major privacy concern.
To eliminate the redirects to harmful phishing websites and annoying ads, you should scan your computer with a reliable anti-malware program, such as SpyHunter 5Combo Cleaner or Malwarebytes. Additionally, other active viruses might be present on your computer without you knowing it. As a result, security software is important in order to prevent any further damage that could occur.
Since adware commonly tracks an individual's internet activity, protecting your privacy is of utmost importance. We always recommend utilizing a FortectIntego cleanup utility to eliminate cookies[3] and other data that have been cached online. You can also follow the manual steps listed below:
Google Chrome
- Click the Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
![Clear browser data from Chroum Edge Clear browser data from Chroum Edge]()
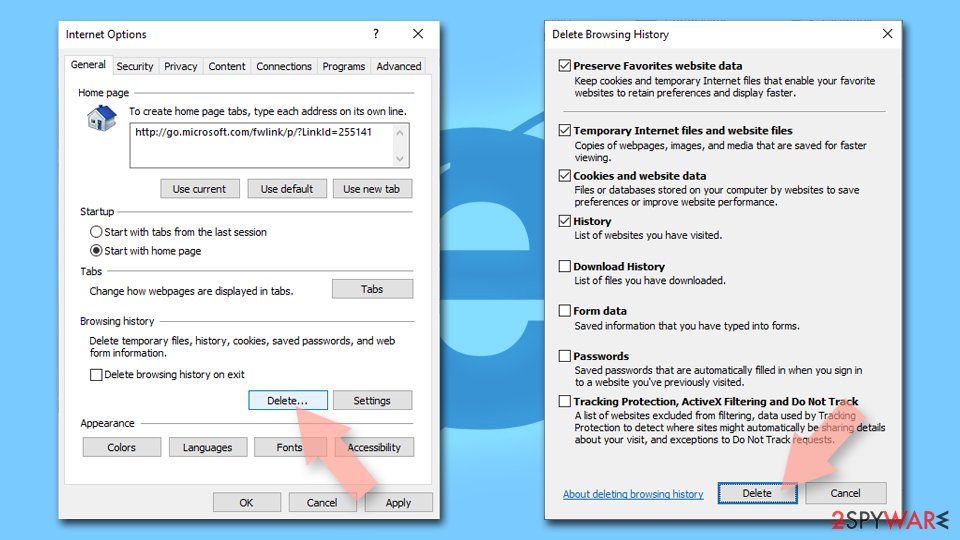
Internet Explorer
- Press on the Gear icon and select Internet Options.
- Under Browsing history, click Delete…
- Select relevant fields and press Delete.
![Clear temporary files from Internet Explorer Clear temporary files from Internet Explorer]()
Basicnetworkpc.com ads may also come via push notifications
Websites that show false information about users' computer status try to make money in as many ways as they can. For example, they want to sell software to users and ask them to enable push notifications when they first enter the site – it manifests as a prompt at the top of the page, below the URL bar.
If you accidentally click the “Allow” button, intrusive pop-ups will appear on your desktop and show material that is misleading and might even contain malicious links. Do not interact with these notifications, as it could jeopardize your safety. Instead, follow the instructions below to stop the ads:
Google Chrome
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.
![Stop notifications on Chrome PC 2 Stop notifications on Chrome PC 2]()
Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.
![Stop notifications on Mozilla Firefox 2 Stop notifications on Mozilla Firefox 2]()
Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.
![Stop notifications on Safari Stop notifications on Safari]()
MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.
![Stop notifications on Edge Chromium Stop notifications on Edge Chromium]()
Internet Explorer
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.
![Stop notifications on Internet Explorer Stop notifications on Internet Explorer]()
- Locate the web address in question under Allowed sites and pick Remove.
How to prevent from getting adware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Phishing attacks. Imperva. Application and data security.
- ^ Chris Hoffman. Everything You Need To Know About the Blue Screen of Death. How-to Geek. Site that explains technology.
- ^ Cookies and Web Beacons. NTT. NTT Communications.