Bitpaymer ransomware / virus (Removal Guide) - 2018 update
Bitpaymer virus Removal Guide
What is Bitpaymer ransomware virus?
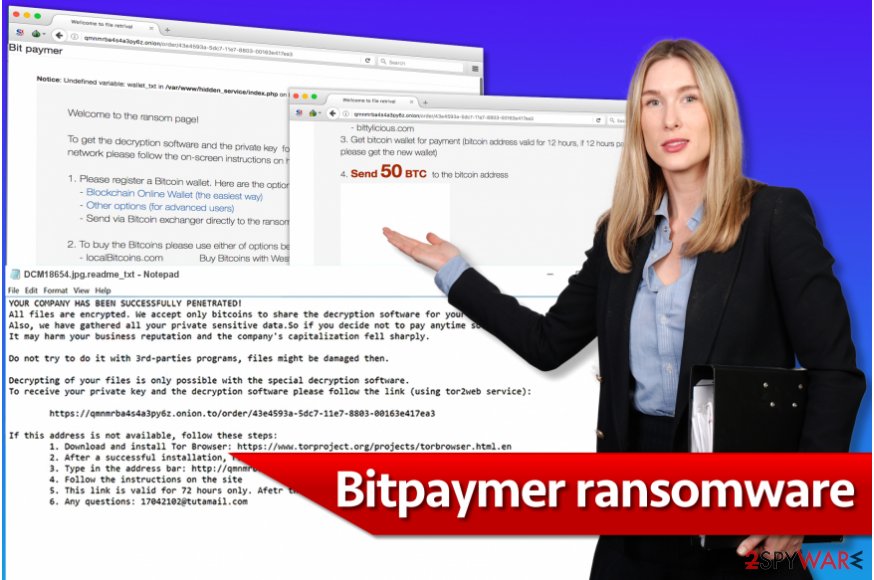
Bitpaymer ransomware is a file-encrypting virus which targets large scale organizations
BitPaymer ransomware is a crypto-malware which uses RC4 and RSA 1024 ciphers to encrypt information on the computers. Researchers have first discovered this file-encrypting virus in July 2017 operating under the name of FriedEx. Although, BitPaymer continues to attack computers in 2018 and even expanded its targets to large-scale organizations, like hospitals and government entities. The compromised data is marked with .locked file extension which remained the same even when the malware was updated. However, developers include different ransom notes and contact details with every new variant of BitPaymer.
| Summary | |
|---|---|
| Name | BitPaymer |
| Alternative name | FriedEx |
| Release date | 2017 |
| Type | Ransomware |
| Danger level | High. Makes system changes and encrypts files |
| Appended file extension | .locked |
| Cryptography | RC4 and RSA-1024-bit |
| Ransom note | readme_txt |
| Contact email address | ClaudiaBarnengham@protonmail.com, 1173022@protonmail.com, 15010050@tutamail.com |
| Targeted OS | Windows |
| Main targets | Hospitals and other organizations |
| Distribution | RDP attacks |
| To uninstall BitPaymer, install FortectIntego and run a full system scan | |
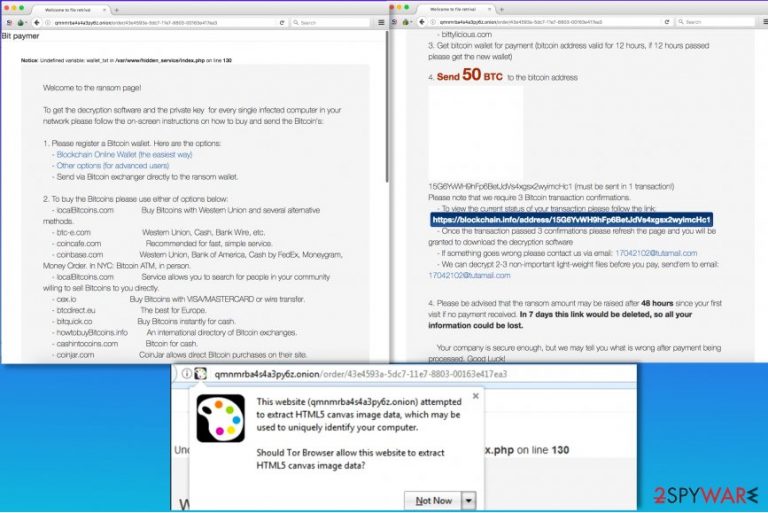
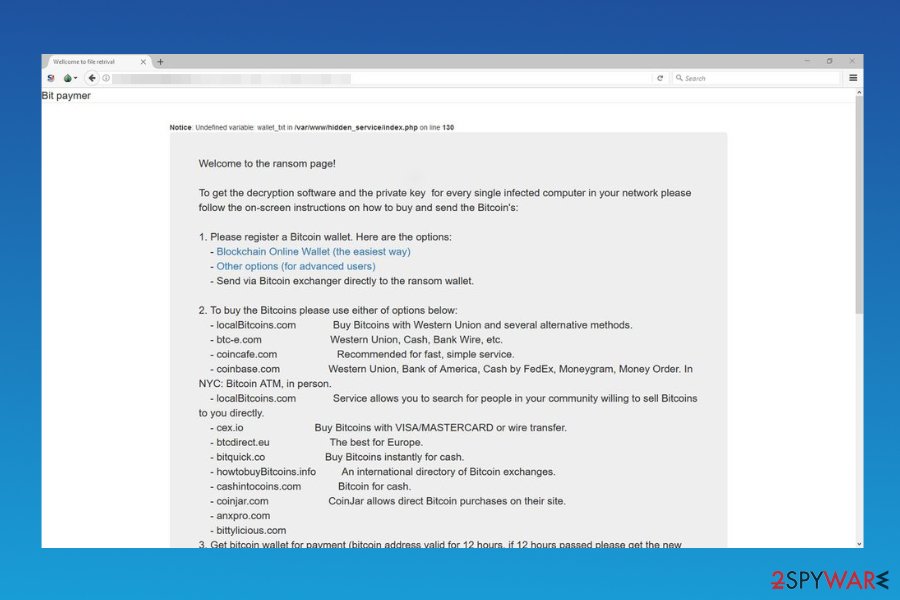
Bitpaymer virus has been created by the same group of hackers who are responsible for Dridex banking trojan. However, this time cyber criminals aimed at Scottish hospitals.[1] Fortunately, it did not manage to cause huge damage. However, it asked to pay 50 Bitcoins for data recovery.
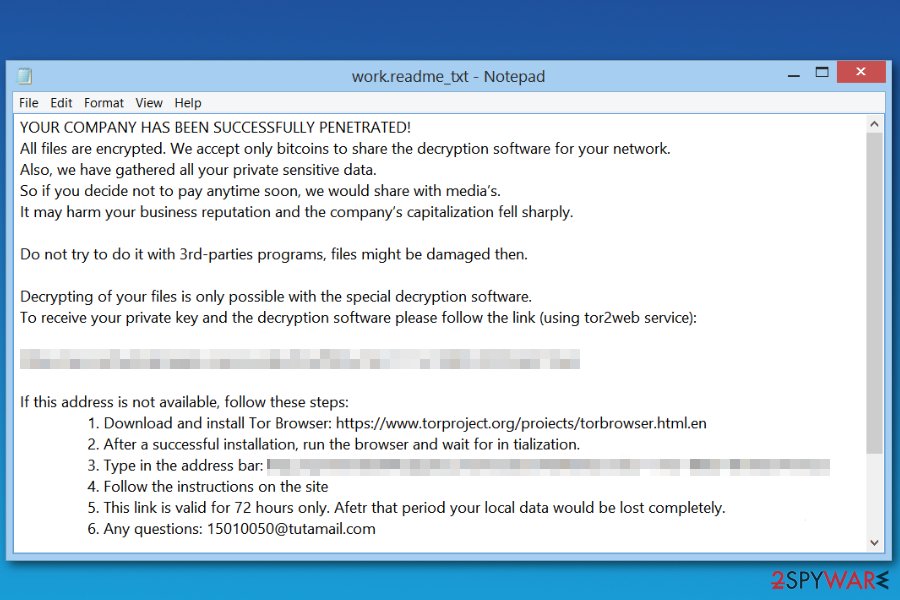
Bit Paymer has a unique feature and creates a unique ransom note for each encrypted file. The name of the ransom note consists of the original filename and .readme_txt extension. For example, a file called document.txt gets a ransom note called document.txt.readme_txt. The ransom note reveals that the victim has to pay a specified sum of money in order to restore encrypted files.
The virus has been updated a several times. However, nothing in ransomware's operation has been changed. The only major difference is used different Bitcoin wallet address (for ransom payments) and used contact email address. Currently, researchers detected three of them. However, there might be a bunch of different ones too:
- ClaudiaBarnengham@protonmail.com,
- 1173022@protonmail.com,
- 15010050@tutamail.com
The payment is only accepted in Bitcoins, which is the favorite cryptocurrency used in many illegal operations[2]. The payment system itself is legitimate; however, cyber criminals tend to use it to become anonymous and untrackable. But in a case of a ransomware attack[3], an immediate Bitpaymer removal is required to protect your PC from further malware attacks.
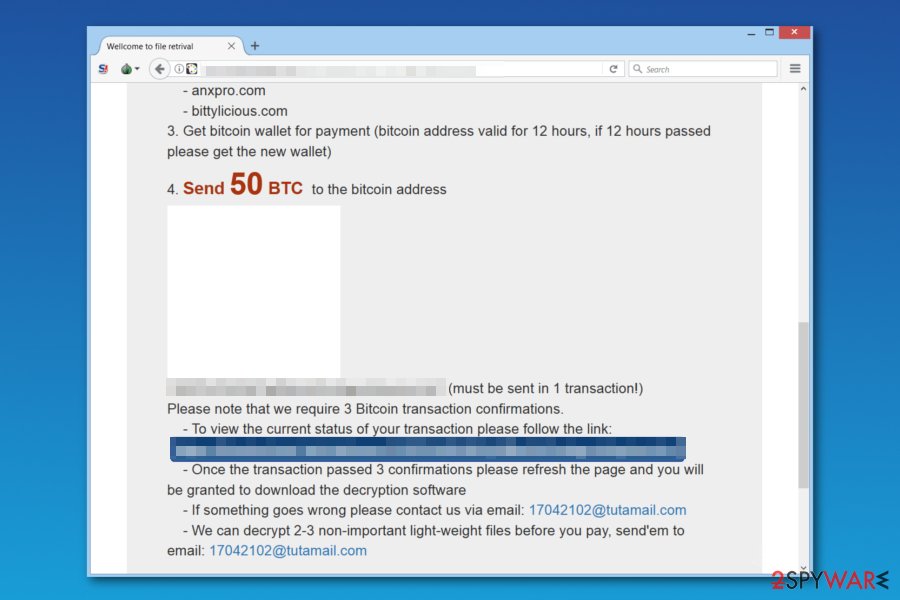
The Bitpaymer ransomware suggests installing Tor browser in order to access a particular ransom payment website. The payment website has no shame to ask the victim to pay 50 Bitcoins, which is an incredibly large sum of money – approximately 230,000 US dollars. We doubt that the Bitcoin wallet provided on that website will ever receive any payments from ransomware victims because such amount is simply unreasonable.
Speaking of alternative data recovery methods than paying the excessive ransom, there are some tools that you can try out. We have described possible data recovery techniques below this article. However, before taking any actions to recover your files, remove Bitpaymer virus first. To complete this task, we highly recommend using security programs such as FortectIntego that can eliminate spyware and malware from your PC.
If your files were encrypted by Bit Paymer, we hope that you had a data backup. It is the most efficient way of restoring files; however, not many ransomware victims have it. In case you’re reading this article because you want to find out more about the latest ransomware viruses, we strongly recommend you to create a data backup. For more security-related tips, visit NoVirus.uk site[4].
The PGA of America was possibly infected with Bitpaymer
Previously, the main targets of BitPaymer malware were hospitals and government entities. However, now the developers of this dangerous cyber threat decided to attack the PGA of America by hijacking the network. The staff identified the ransomware attack only on Tuesday morning when they started receiving ransom notes on each affected computer.
Just like SamSam ransomware, BitPaymer uses RDP Brute Force attacks to infect the network. After the attack, malware drops a ransom note where criminals inform about a penetrated network and ask to contact them via email:
Your network has been penetrated
All files on each host in the network have been encrypted with strong algorithm.
Backups were either encrypted or deleted or backup disks were formatted.
No free decryption software is available in the public.
Additionally, crooks threaten not to rename or move encrypted files. According to them, this may cause more damage and files might be lost forever. However, it’s just a psychological terror and attempts to gain more money from unsuspecting computer users.
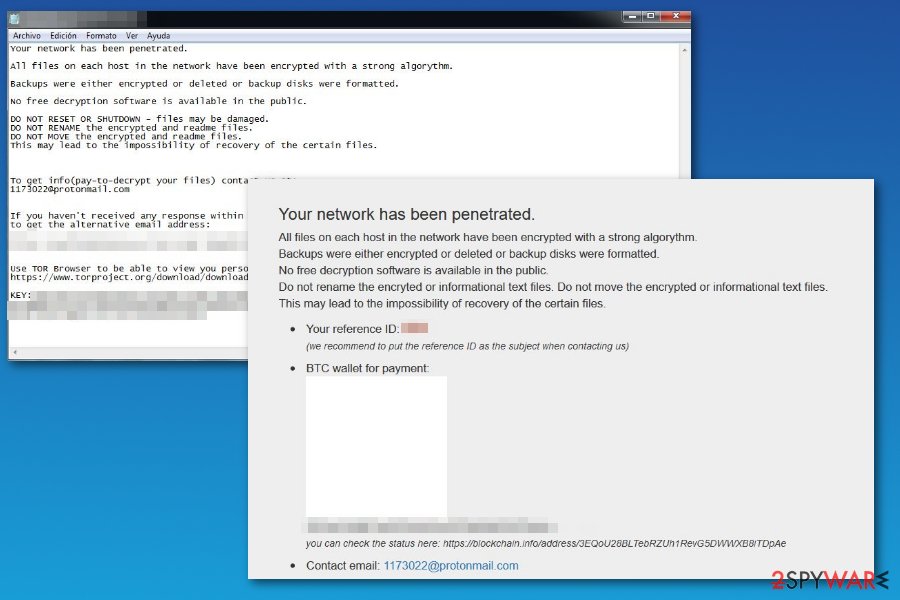
According to the research conducted in May, experts have identified other BitPaymer RDP attacks which left ClaudiaBarnengham@protonmail.com and 1173022@protonmail.com email addresses for contact purposes. However, other major changes were not noticed.
Similarities between BitPaymer and Dridex malware
Researchers at ESET[5] have introspected FriedEx virus and compared it to Dridex banking trojan. Surprisingly, experts discovered numerous similarities, starting from similar disguise techniques to identical malware packers and other indistinguishable features.
The analysis of malicious software codes allowed to confirm that both viruses are created by the same developers. It means that criminals are ambitious and willing to commit more cyber crimes. Instead of continuing updating banking trojan, they are also taking advantage of the most popular cyber crime – ransomware business.
Developers managed to create one of the most dangerous banking trojans. Thus, they are expected to update Bitpaymer and find new ways to make another hazardous crypto-malware soon.
Hospitals were one of the main targets of the crypto-malware
BitPaymer ransomware was undeniably active during the end of August. Researchers note that this file-encrypting virus managed to attack even three hospitals at National Health Service’s (NHS) Lanarkshire outpost. According to the sources, developers demanded to pay 53 Bitcoins (approximately 190 000 British Pounds at the current exchange rate) for BitPaymer decrypt software.
NHS Lanarkshire reported[6] about the issue and shared the news that hospitals’ security and IT systems were under control. Ransomware affected phone and staff rostering system mostly. Therefore, the attack disturbed hospitals’ work. They had to postpone surgeries and cancel people appointments.
It’s unknown how Bit Paymer launched the attack. It is suspected that malware may have launched RDP brute-force attack. Security experts continue investigating this issue.
The peculiarities of BitPaymer RDP attacks
Usually, ransomware spreads via spam emails, exploit kits, or with the help of Trojans. Although, BitPaymer ransomware uses RDP Brute Force attacks to infect large networks and extort money from organizations or companies. There are several tips to help you protect your computer or even business from ransomware attacks.
First of all, we highly recommend that you secure your computer with anti-malware software to ward off malicious software. Then, you should create a data backup. Create copies of the most important files and transfer them to an external data storage device, such as hard drive or USB. Keep it away from the computer and use when needed only.
Finally, we suggest keeping all of your programs up-to-date. In other words, whenever your computer suggests you to install an update to programs that you already have, agree to do it. You can also enable automatic updates and save yourself some time. Please remember that you should never decide to install software updates presented by suspicious Internet sites – these can land some spyware/malware programs on your PC.
Introduction to BitPaymer removal
Those who are infected with this sophisticated cyber threat should do not hesitate and take action immediately. The most convenient way to remove BitPaymer is running a full system scan with a professional security tool, like FortectIntego, SpyHunter 5Combo Cleaner, or Malwarebytes. Although, in some cases malware might block all antivirus programs. Thus, reboot your computer into Safe Mode with networking as shown below.
Do not try to perform a manual Bitpaymer removal. It can only be completed by experienced IT professionals that have experience in dealing with malware like ransomware. Attempts to uninstall ransomware can result in failure and cause you a lot of problems.
Getting rid of Bitpaymer virus. Follow these steps
Manual removal using Safe Mode
Delete the ransomware using the anti-spyware or anti-malware software. If you do not have it yet, install it after rebooting your PC into Safe Mode with Networking. This mode should always be used when dealing with malware – it helps to temporarily disable the virus and clean up the computer system efficiently.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Bitpaymer using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Bitpaymer. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Bitpaymer from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.Data backup clearly is the best tool when it comes to data recovery. If you haven't created it in the past, it will be quite hard to recover your files now. However, we suggest trying one of the provided methods to restore some of your files.
If your files are encrypted by Bitpaymer, you can use several methods to restore them:
Data Recovery Pro technique
Data Recovery Pro can help you to restore your files easily. Although it might not be able to break the encryption of Bitpaymer ransomware, it might successfully recover some of your files. This is how you should use this tool:
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Bitpaymer ransomware;
- Restore them.
ShadowExplorer software
Volume Shadow Copies are extremely useful because they can help to restore corrupted files. However, ransomware viruses tend to delete them. You can check if your PC still contains some Volume Shadow Copies by running a scan with ShadowExplorer.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Bitpaymer and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Richard Chirgwin. Lanarkshire NHS infection named as Bitpaymer variant. The Register. Sci/Tech News for the World.
- ^ Doug Pollack. Bitcoin's strategic place in ransomware. International Association of Privacy Professionals. News.
- ^ Global ransomware attack causes turmoil. BBC Technology News. Breaking News and Analysis on Computing, the Web, Blogs, Games and more.
- ^ Official website of NoVirus UK. NoVirus UK. Security News, Malware Removal Guides.
- ^ Michal Poslušný. FriedEx: BitPaymer ransomware the work of Dridex authors. WeLiveSecurity. News, views, and insight from the ESET security community.
- ^ NHS Lanarkshire's statement on Facebook. Facebook. The Social Network.







