CrescentCore (virus) - Improved Instructions
CrescentCore Removal Guide
What is CrescentCore?
CrescentCore is the malware that can significantly damage the machine and evade detection

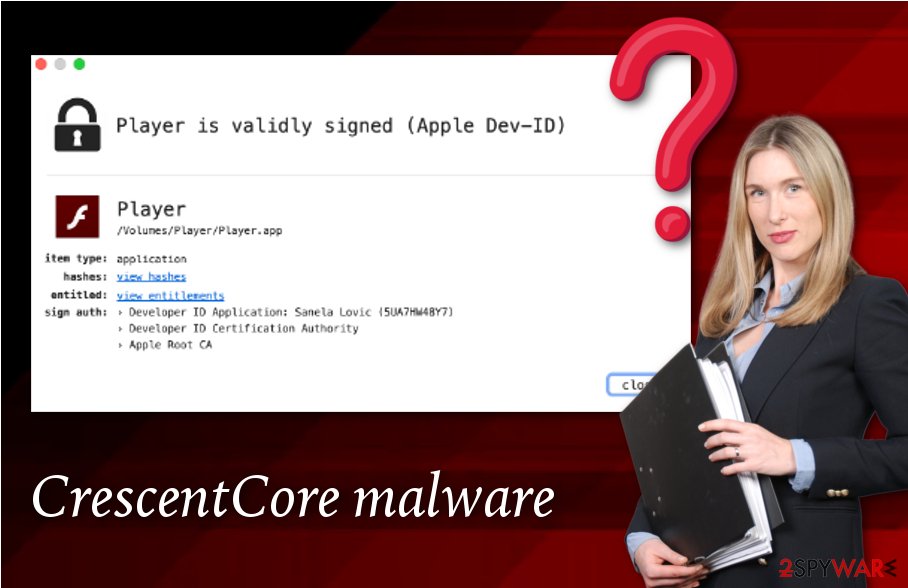
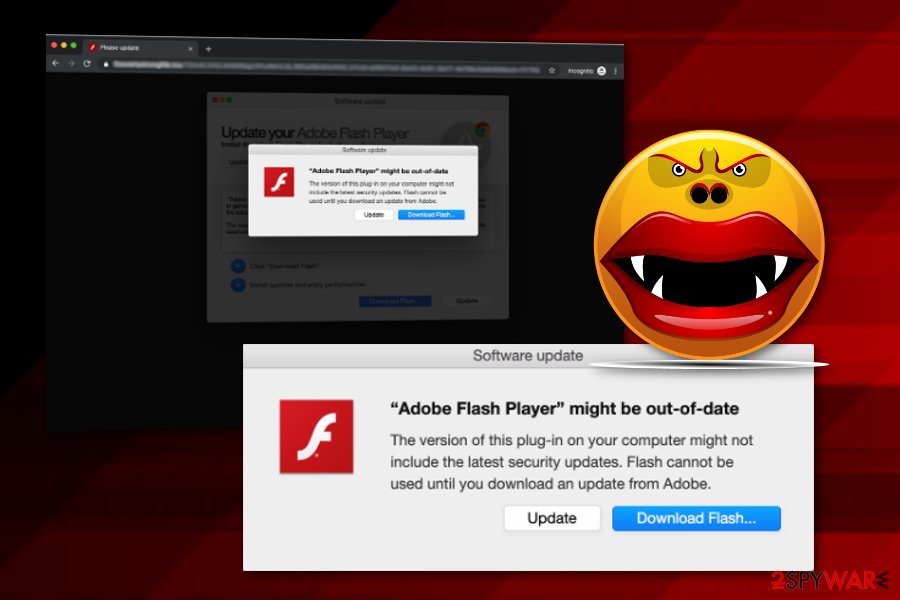
CrescentCore, also known as OSX/CrescentCore is a Trojan horse designed to infect Mac computers by avoiding antivirus detection. This dangerous threat is capable of secretly hiding inside a .dmg disk image and pretends to be a fake update of the Adobe Flash Player tool.[1] First discovered by Intego, the particular virus appears to be a highly advanced threat that can avoid being spotted even by highly experienced specialists. Nevertheless, this type of malware aims to inject other programs into the system if the infected OS is not activated on a virtual machine and if no third-party security tools are enabled.
| Name | CrescentCore, OSX/CrescentCore |
|---|---|
| Type | Trojan horse/Mac malware |
| Appears as | Fake Adobe Flash Player update |
| Target | Mac systems that are not running on virtual machines and have no strong security |
| Related objects | LaunchAgent |
| Distribution | Malicious websites, infected hyperlinks, fake Adobe Flash Player updates |
| Removal | Use anti-malware tools to perform a full system scan and find malware |
| System repair | In addition to virus removal, you should take care of the virus damage to, so run FortectIntego to fix possible |
The infection process of any Mac malware, similar to OSX/Shlayer, begins when the victim clicks on the disk image icon and enters the fake Flash Player application. However, the threat takes some certain precautionary measures and identifies if it is not a virtual machine that it is running on. If not, malicious activities successfully continue.
Such a precaution step is taken by CrescentCore to ensure that the cybercriminals do not damage their own systems during the infective period. Nevertheless, the Trojan virus needs to ensure that no antivirus protection is running on the infected system and if the malware finds out that it is working on a virtual machine or there is anti-malware on the system, it immediately stops the infections process and deletes itself from the computer/laptop.
If you are a Mac user who has always been concerned about automatic system protection, we can congratulate you as OSX.CrescentCore should not appear on your computer. However, if your machine lacks the required security, the risk of getting infected with this Trojan horse might not be that small as you expect it to be.
If CrescentCore finds all conditions satisfying, it continues malicious actions by installing another component known as LaunchAgent.[2] Talking about what it does after such installation, cybersecurity researchers do not have one true answer. However, the Trojan horse might relate in the injection of suspicious security tools such as Advanced Mac Cleaner, Mac Tonic, Mac Mechanic, Auto Mac Speedup, and similar.
Besides, security experts think that the new malware strain might be capable of injecting a malicious “helper object” (e.g. extension) into the Safari web browser application. This type of activity can lead anywhere. CrescentCore and LaunchAgent might start spying on your personal information or credentials for misusing them in the future.
If you have discovered this notorious malware on your Mac computer system, you should be careful with it and opt for malware removal right away. Note that trojan infections might relate to high CPU work, injection of other malicious programs, corruption of software or files, collection of personal data/credentials.[3]
You should not try to remove CrescentCore by yourself as manual activities might relate to more damage than you think it could. Our suggestion would be to scan the entire system with a strong antivirus program such as SpyHunter 5Combo Cleaner, Malwarebytes to identify all malware strains. Once you find their directories, clean these locations with reputable software entirely.
Malicious pieces can spread around with the help of deceptive content and other threats
Security experts from NoVirus.uk[4] claim that dangerous infections often choose unprotected sources to be placed in. These pages are easy to enter and due to the lack of protection they provide, potential victims are also very easy to catch here. If you like entering third-party video-watching, gambling, adult-themed, or piracy[5] websites, you have a big risk of ending with notorious malware on your computer system.
The second way of distributing notorious viruses is by using fake Adobe Flash Player updates. Messages which claim that updates are needed for the Player app often appear to be very legitimate-looking and aim to trick a big number of users. However, we want to warn users not to fall for such tricks, especially, if they are using Google Chrome. This browser updates its in-built Player automatically and no manual updates are ever needed.
Malware might also be pushed through email spam campaigns and come injected into normally-looking attachments which are the main carriers of the malicious payload. Be aware of messages that include numerous grammar mistakes, come from an unrecognizable sender. All attachments (even legitimate-looking ones) need to be put under a scan of anti-malware software for full identification.
Elimination of the CrescentCore virus
CrescentCore removal process is not a thing you should postpone or not pay attention to. Most important, DO NOT try to get rid of this malware by yourself if you lack skills in this field. However, if you believe that you are a well-experienced user and have found some signs of infection on your computer, what you can do by yourself is disabling malicious processes if some are found in your Mac machine:
- Go to Launchpad and type in “Activity Monitor”.
- Open the application and go to the Processes tab.
- Find all suspicious processes and press the X button to quit them.
Once you have done this, you can also search for malicious strings related to the malware in your Mac login items. If you have found some, you can delete them with the help of these guiding steps:
- Locate the Apple menu and continue with System Preferences.
- Press on the Users & Groups sector.
- Ensure that your username is picked in the left side.
- After that, find all suspicious login components in the Login Items tab.
- Use the minus (-) sign to eliminate them.
However, our suggestion would still be to use reputable anti-malware programs such as FortectIntego, SpyHunter 5Combo Cleaner, Malwarebytes for detecting all components related to this Trojan virus. Furthermore, if you choose a trustworthy repair tool, you will be able to remove CrescentCore from all directories of your machine, reverse all suspicious modifications, and optimize the enter system. Also, you can keep the antivirus protection on your computer/laptop for future safety purposes.
How to prevent from getting mac viruses
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Lindsey O'Donell. Mac Malware Pushed via Google Search Results, Masquerades as Flash Installer. Threat Post. Relevant technology news.
- ^ Roger Fingas. Latest Mac malware in the wild evades security software, researchers. Apple Insider. Security Articles.
- ^ What Trojan Horse Virus Do?. Comodo. Creating Trust Online.
- ^ NoVirus.uk. NoVirus.uk. Spyware news articles.
- ^ Definition of 'Piracy'. The Economic Times.
