CryptoWall 3.0 virus (Easy Removal Guide) - 2021 update
CryptoWall 3.0 virus Removal Guide
What is CryptoWall 3.0 virus?
CryptoWall 3.0: the main features of the famous ransomware spin-off
CryptoWall 3.0 virus is a dangerous ransomware [1] which can easily lead you to lots of trouble. This threat has no problem blocking your files, blackmailing you and feels no shame leaving its victims penny-less [2]. If you want to avoid such issues, you should try your best when preventing CryptoWall 3.0 and previous its versions, such as Cryptowall, Cryptolocker, CTB Locker, etc from infecting your PC. Otherwise, you can be left without your important documents, photos, video files and similar data. In this article you will learn all about how this virus works, how it infiltrates computers and, finally, how can an infected user remove CryptoWall 3.0 from the computer without inflicting more damage.
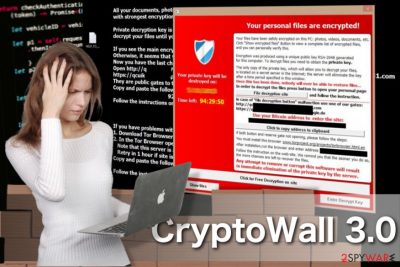
If any of the previously mentioned viruses infiltrate the system, they typically start by scanning and encrypting the predetermined files. It is now known that CryptoWall 3.0 virus is specifically looking for these file extensions: 3fr, accdb, ai, arw, bay, cdr, cer, cr2, crt, crw, dbf, dcr, der, dng, doc, docm, docx, dwg, dxf, dxg, eps, erf, indd, jpe, jpg, kdc, mdb, mdf, mef, mrw, nef, nrw, odb, odm, odp, ods, odt, orf, p12, p7b, p7c, pdd, pef, pem, pfx, ppt, pptm, pptx, psd, pst, ptx, r3d, raf, raw, rtf, rw2, rwl, srf, srw, wb2, wpd, wps, xlk, xls, xlsb, xlsm, xlsx, etc. After finding these files, the virus encrypts their content with the help of AES CBC 256-bit encryption algorithm [3]. This means that the only way to decrypt each of the encrypted files is to get a decryption key. After it's done encrypting, Cryptowall displays a full-screen warning message instructing the victim about possible data recovery options. Typically, the extortionists ask to download and install Tor web browser, launch it and then visit an indicated website. Here, the victim is asked to pay a ransom of $500. After failing to do so within 7 days, the hackers threaten to increase the sum to $1000. However, we want to encourage you NOT to pay the fine. There is no guarantee that after pushing you into paying a ransom, CryptoWall owners will send you the decryption key.
At the moment of writing, ransomware-type programs are a serious threat for all PC users. Luckily, there are also lots of developers who began designing specific tools that could help the affected PC users. If this parasite has just appeared on your desktop, you should run a full system scan with FortectIntego and remove CryptoWall 3.0 from your computer for good.
Preventing CryptoWall 3.0 infiltration. Is it possible?
If you want to avoid ransomware such as CryptoWall 3.0, you must take active steps to prevent it. First of all, make sure you have a reputable anti-spyware installed on your computer. Also, try to keep it up-to-date to have an ability to see what malware is trying to get inside your PC system. Also, make sure you stay away from misleading email messages. If an email looks suspicious [4], it is full of typos or grammar mistakes, or if you don't recognize the sender, simply ignore it. You can try to contact the person who is responsible for this mail and double check him/her. Otherwise, you may be tricked into clicking on a malicious link or downloading an infected email attachment. If CryptoWall 3.0 enters the system, it takes only a few minutes until it checks it, blocks the files and starts demanding ransom. If you think that you are infected with CryptoWall 3.0 ransomware, scroll to the end of the article and perform the required actions.
Frequently Asked Questions (FAQ)
Question. I got infected with CryptoWall 3.0 ransomware last week. It seems that all my drivers except C have been affected. Is there anything else I can do instead paying the ransom to get my files back?
Answer. The worst thing that you can do is to pay the ransom. Doing so is equal to giving away your money straight to online scammers. Moreover, you can disclose your credit card details and other personal information that is related to your bank account. Thus, instead of paying the ransom, remove CryptoWall 3.0 from your PC and use a data recovery tool for encrypting your personal files. For that, you can rely on a guide, which is given down below.
Question. A couple of days ago Cryptowall virus infected my computer. Fortunately, it seems that it has affected only one folder in my hard drive and, luckily, it does not contain any important data. Of course, I'm not going to pay the ransom for criminals; however, I wonder if it's enough to remove the infected folder to get rid of this threat?
Answer. NO. Ransomware is very deceiving and very cleverly designed computer infections that can hide in computer's memory for a long time and then attack unexpectedly. Removal of the folder with encrypted files will not help you at all. In contrast, you may lose more important data, such as photos, documents, music, videos, etc. Thus, the only hundred percent reliable data protection solution is a full CryptoWall 3.0 removal. Recently, 2-spyware security experts prepared a helpful guide that should help you with the removal of Cryptowall 3.0. You can find it down below.
Question. How can I decrypt my files after Cryptowall infiltration? My whole drive has been encrypted. I made a backup on a separate drive, but it is also infected. Is there a way to decrypt my files without experiencing any damage?
Answer. The most important thing that you have to remember is NOT to pay the ransom that you are demanded to pay. This way you risk disclosing credit card details to online scammers. Besides, we doubt if the key that you will get after making the payment will help you in decrypting your data. Therefore, as soon as this ransomware affects your machine, scan it with a reputable anti-spyware and try to recover data using a R-Studio, Photorec or another data recovery software. All details are given below.
Question. Yesterday I got attacked by CryptoWall 3.0. I've found the file named help_decrypt.png .txt .html in every folder and removed it. Besides, I did remove it from the registry. Nevertheless, file types, such as .xls .pdf, .doc, etc. cannot be opened. What's the problem? It's the first time I'm dealing with the ransomware, but I'm not going to pay a dollar for those frauds. Please, advice!
Answer. Manual CryptoWall 3.0. ransomware removal is not possible. The only way to get rid of this infection is a full system scan using a reputable and updated (!) anti-spyware. If you want to delete CryptoWall 3.0. virus from your computer once and for all, you should use once of the programs that are mentioned below.
Question. Please provide me with a hand on getting my money and files back! I paid for these bastards $500 and received a fake key, which did nothing at all with encrypted files. Is there any way to refund my money? And what about files? Are they lost permanently? Any help appreciated!
Answer. Such scenario is the most common. That's why we urge people NOT to pay the ransom. Unfortunately, it's not very likely that you will get your money back. You can try to contact the bank and ask it to cancel the payment. However, this will certainly not work if you made the payment via Tor web browser. Speaking about encrypted data, we have better news. Before starting the recovery, make sure that you remove CryptoWall 3.0 virus from the system with a reliable anti-spyware (the list of recommended programs is provided below). After that, install a reliable data recovery tool and try to decrypt your files. You can find a full Cryptowall 3.0 removal guide down below.
Free your computer from CryptoWall 3.0
If you are looking at a message which claims that your files have been encrypted and that you must pay certain amount of money to decrypt them, there is no denying that you are infected with ransomware and have to take action immediately. Don't try to remove CryptoWall 3.0 virus by yourself! Minor mistakes during the virus elimination can have disastrous consequences and your computer may be corrupted beyond repair. Thus, it is best to perform the elimination automatically, using professional antivirus software. If you want to restore the access to your files, you should try using backups or, if you don't have them, try following manual recovery guidelines below this article.
We highly recommend thinking about the prevention of such infections like Cryptowall. Besides, don't forget to think about the immunity of your files and backup [5]. For that, you can use USB external hard drives, CDs, DVDs, or simply rely on online backups, such as Google Drive, Dropbox, Flickr and other solutions. More information about backups can be found in this post: Why do I need backup and what options do I have for that?
Getting rid of CryptoWall 3.0 virus. Follow these steps
Manual removal using Safe Mode
CryptoWall 3.0 is not a lightweight infection, so it may not be eliminated from the computer that easily. CryptoWall may block your antivirus and prevent it from properly scanning the system. To get you antivirus running again follow the instructions below:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove CryptoWall 3.0 using System Restore
In some cases, CryptoWall 3.0 may give in an abandon your computer easily, in other instances, the malware may be more difficult to remove. To help achieve a smoother elimination, we have prepared the guidelines below. When you are done with the indicated steps, run the scan of your system again.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of CryptoWall 3.0. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove CryptoWall 3.0 from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by CryptoWall 3.0, you can use several methods to restore them:
CryptoWall 3.0 recovery using Data Recovery Pro
Data Recovery Pro is often used to recover files that have been accidentally deleted or corrupted. Nevertheless, it works well with data recovery after ransomware infiltration, too. Here is how you use this tool:
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by CryptoWall 3.0 ransomware;
- Restore them.
Rolling back files encrypted by CryptoWall 3.0 with the help of Windows Previous Versions feature
Windows Previous Versions feature may help recover some of the CryptoWall 3.0 virus affected files. You will have to pick which files you want to roll back yourself:
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Download ShadowExplorer to recover data encrypted by CryptoWall 3.0
With ShadowExplorer you can help your files only if their Volume Shadow Copies are not deleted by the virus. To test that complete these steps:
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
CryptoWall 3.0 decrypter
Unfortunately, CryptoWall 3.0 decrypter is currently unavailable. Please check back with us later.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from CryptoWall 3.0 and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Ransomware. Definition, prevention and removal. KasperskyLab. Kaspersky antivirus blog.
- ^ David Strom. The secret keys to Cryptowall’s success. SecurityIntelligence. Analysis & Insight on Information Security.
- ^ Advanced encryption standard. Wikipedia. The free encyclopedia.
- ^ Brien Posey. 10 tips for spotting a phishing email. TechRepublic. News, Tips, and Advice for Technology Professionals.
- ^ Maria Korolov. Will your backups protect you against ransomware?. CSOonline. Security news, features and analysis about prevention, protection and business innovation..





















