Cyberpunk 2077 virus (Virus Removal Guide) - Free Instructions
Cyberpunk 2077 virus Removal Guide
What is Cyberpunk 2077 virus?
Cyberpunk 2077 virus – a fake version of a popular video game that installs Raccoon malware on a Windows computer

Cyberpunk 2077 virus is a term used to describe malware that is hiding behind one of the most anticipated video game titles of the year. Users download the virus when they visit insecure third-party torrent, crack, or warez websites that offer the pirated version of the game. While the original cost reaches as much as $59.99, users who want to avoid payments resort to cracked versions of the game. This, unfortunately, often does not end well, as players end up infecting their PCs with malware.
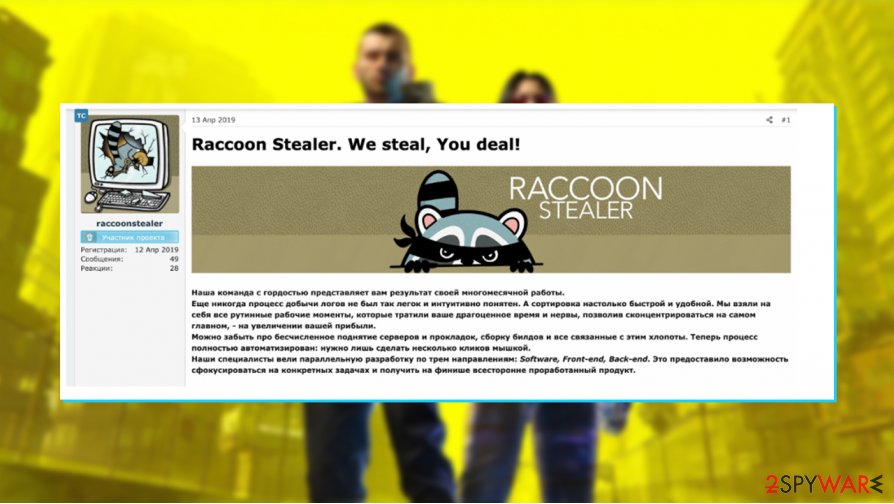
While many malicious programs can hide behind Cyberpunk 2077 virus, researchers have found that threat actors tend to hide info-stealing Trojan known as Raccoon. Once installed, malware is capable of stealing login credentials, financial details, as well as other sensitive user data. Creators of the strain operate a Malware-as-a-Service,[1] which allows various actors to access the fully-functional info-stealer, providing regular bug fixes and feature updates.
| Name | Cyberpunk 2077 virus |
| Type | Malware, info-stealer |
| Related malware | Raccoon Trojan released in April 2019; operated via the MaaS (Malware-as-a-Service) scheme |
| Distribution | Users install the Trojan when attempting to download a cracked version of the popular video game known as Cyberpunk 2077 from torrent, crack, warez, and similar sites |
| Symptoms | Info-stealing malware usually operates in the background without emitting any symptoms, although some users might experience system crashes, errors, or other uncommon issues |
| Dangers | identity theft, installation of other malware, banking and other account compromise, financial losses, etc. |
| Elimination | The only way to uninstall the virus from the system is by using robust anti-malware software such as SpyHunter 5Combo Cleaner |
| System fix | In case your system is experiencing various stability issues post-removal, we recommend using FortectIntego to fix damaged Windows system files and settings automatically |
Cyberpunk 2077 is an Action Role-Playing Game (RPG) released by polish developer CD Projekt Red. Almost eight years in development, intense marketing campaigns brought this title to the very top – almost 8 million preorders were made, and the global game's release managed to crash Steam and Gog functions due to overload.
Such intense attention did not bypass cybercriminals, of course, as it is not uncommon for them to abuse the latest trends and titles that are highly consumed. Previously to Cyberpunk 2077 virus, bad actors also released fake mobile games for Fortnite or Valorant, which, once installed, would steal sensitive user data or allow the attackers to take full control over the infected computer.
Cyberpunk 2077 virus on mobile was also recently discovered. According to Kaspersky security researcher Tatyana Shishkova,[2] Android malware is spread via a fake Google Play website. It allows the attackers to encrypt all personal files, appending .coderCrypt extension to them, later asking for $500 for data return.
Thousands of websites spread pirated programs, a large amount of which are video games. Users need to install it and then apply the so-called crack, which would bypass the regular registration processes and allow playing the game for free. Without a doubt, such practice is illegal, although up to this day, millions of clicks are made each day when trying to download pirated software.
The worst part is that most security applications would flag malicious code within the cracks or installers, but users choose to ignore these warnings. Here's one of the samples that are detected as follows by various security vendors, according to Virus Total:[3]
- Trojan.GenericKD.45092211
- Win32.Trojan-Stealer.Raccoon.B5RA2F
- Win32.Outbreak
- Trojan.MalPack.GS
- BehavesLike.Win32.Trojan.hc, etc.
Raccoon Trojan is MaaS malware that is relatively cheap on the underground forums ($75/week or $200/month),[4] so many malicious actors are using and spreading it around the web via various methods. As evident, this time, criminals are using fake websites and torrents to spread it around. Despite being inexpensive, the Trojan is rich in its performance and capabilities, making it one of the most popular malware of such type.
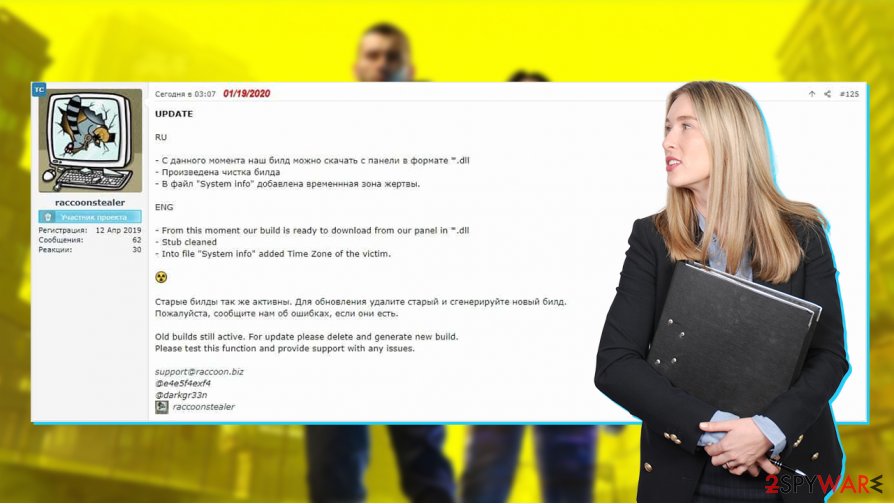
Once installed, the malware behind the fake version of Cyberpunk 2077 connects to a remote Command & Control server controlled by the attackers. For the setup, several commands are used:[4]
The malware generates an ID for the machine from MachineGuid, which is a quite common ID (query this registry keyHKLM\SOFTWARE\Microsoft\Cryptography for the value MachineGuid) and from the current username (calling to GetUserNameA).
It creates the next machine profile bot_id=%machineGUID%_%username%&config_id=%configID%&data=null and encoded the string as base64.
What’s left is to send the machine profile to the C&C. It connects the encoded base64 string to params= and sends a POST request with params=%base64MachineProfile% as the content of the request.
It is then used to transfer all the stolen information and also would allow cybercriminals to enforce a set of malicious commands. For example, it could allow the infiltration of other malicious software that would further compromise the computer, all without victims having a clue about it.
Once installed, Raccoon targets most Chromium-based browsers, including Google Chrome or Opera, and is also capable of stealing data from Mozilla Firefox. Mozilla-based email client Thunderbird is also affected, so all the content of written messages, cryptocurrency wallets, usernames and passwords, technical device information, etc., are harvested and sent over to a remote C2 server.
Cybercriminals can abuse this data in various ways. For example, they might sell it to other actors that would use the information for fraud or phishing. Without a doubt, nobody wants to end up with stolen sensitive information like that.
Thus, if you attempted to download a fake version of the game, you should immediately take action to perform a full Cyberpunk 2077 virus removal with the help of powerful security apps – we recommend using SpyHunter 5Combo Cleaner or Malwarebytes. Since malware can affect various computer functions and settings, many users might suffer from stability issues after the malware is eliminated.
If you experience lag, crashes, errors, and other issues after you remove Cyberpunk 2077 virus from your system, we recommend trying FortectIntego repair software that would be able to fix various underlying issues within the Windows environment and ensure that it is at its best condition. It is important to note that game crashes, lag, and other issues might not necessarily be related to malware (some technical issues with the game might be fixed). However, it is very important to make sure that it is not the case to avoid the severe ramifications of the infection.
Stick to the original version of the game and avoid torrents
Torrent sites such as Pirate Bay attract millions of users regularly. This makes torrent and similar sites a perfect ground for cyberattacks, and criminals are constantly abusing the popularity of such high-risk websites, all while being extremely successful. For example, one of the most widespread ransomware strains known as Djvu is distributed via software cracks and pirated program installers and is hugely successful at doing that. Latest malware samples, such as Omfl or Booa, can infiltrate your machine easily and encrypt all data, later asking for a ransom in Bitcoin for a decryption tool.
That being said, as much as security researchers warn users about dangers that lurk on the torrent and similar sites, the malware remains successful in infecting thousands daily. Therefore, you should not give in to temptation and attempt downloading pirated programs not only because it's illegal and causes financial losses to creators but also because it can result in malware infection. Instead, you should look for an alternative for the game or simply buy it on official platforms such as Steam, GOG, or Epic Games Store.
You must never ignore warnings from your security software, as this is one of the main reasons why so many people get infected via software cracks. These tools are usually flagged by anti-virus programs regardless if they actually carry malicious code within them (this happens due to the fundamental feature of the tool, which includes breaking the code of another software).
Remove Cyberpunk 2077 virus from your system
The cybercrime theme is very prevalent within the actual game. While you dive in deep, don't forget that if you used an illegal installer, your computer might be compromised by Raccoon malware. Therefore, you should immediately take action to remove Cyberpunk 2077 virus from your computer as soon as possible.
While malware elimination is possible without employing automated tools, it is not recommended for regular computer users. Malicious programs perform a massive amount of changes within the system, drop malicious files, and alter presets to ensure that malware operates without any difficulties. Therefore, you should employ SpyHunter 5Combo Cleaner, Malwarebytes, or another reputable anti-malware for Cyberpunk 2077 virus removal. Sometimes, malware might interfere with your security software – we advising using Safe Mode with Networking in such a case (we explain how below).
Since malware is hiding behind the fake game version of the game is an info-stealer, you should clean your machine with security software, use FortectIntego to repair possibly damaged system files, and then change all your passwords on all your accounts. It is also recommended to follow the online banking history to ensure no funds are being leaked.
Getting rid of Cyberpunk 2077 virus. Follow these steps
Manual removal using Safe Mode
If malware is tampering with your anti-virus software, you can access Safe Mode with Network to bypass malware functions easier:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Cyberpunk 2077 and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting malware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Wylie Wong. New Malware-as-a-Service Threat Targets Android Phones. Security Intelligence. Security research blog.
- ^ Tatyana Shishkova. New Android #Ransomware disguised as #Cyberpunk2077 game. Twitter. Social media.
- ^ da0863c8100f03955cdc4f964d9931c1921e46cc1b9318aebc88dff4cfad4906. Virus Total. File and URL analysis.
- ^ Ben Cohen. Raccoon: The Story of a Typical Infostealer. CyberArk. Cybersecurity research blog.
