Fuerboos (Virus Removal Guide) - Free Instructions
Fuerboos Removal Guide
What is Fuerboos?
Fuerboos is a malicious trojan virus that might steal your banking details and login data, although might also be a false positive
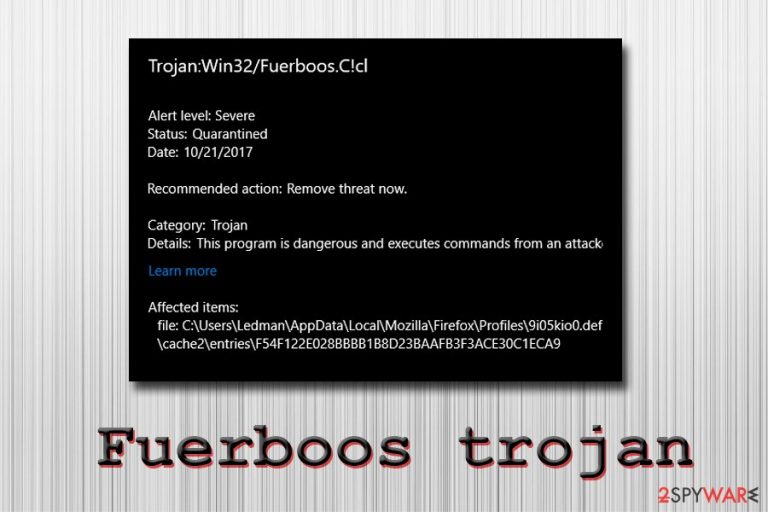
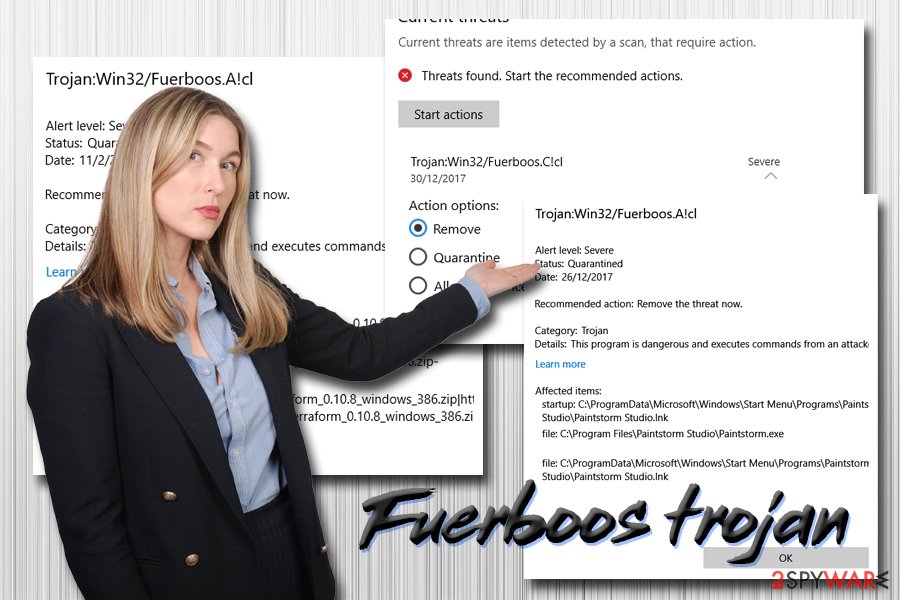
Fuerboos trojan is a generic name used by Windows Defender's machine learning technology to describe malware that has not been encountered before. The detection can indicate the infection of ransomware, a backdoor, botnet, banking trojan, or a crypto miner. Depending on the type of infection, these malicious programs might have different goals, including money extortion, sensitive information harvesting, spying, proliferating another malware, etc.
Nevertheless, because Trojan:Win32/Fuerboos is a heuristic detection, it can also indicate a false positive, as it happens with similar detections, such as Win32/Heri, IDP.Generic, and many others. Users said that legitimate tools like ArangoDB[1], WinZip, as well as Blizzard's video game Diablo II.[2]
| Name | Fuerboos |
| Also known as | Trojan:Win32/Fuerboos.C!cl |
| Type | Trojan, malware |
| Infiltration | Malicious executables, software cracks, spam emails, torrent sites, exploits, etc. |
| Symptoms | Varies depending on the malware type |
| Risk factors | Stolen bank account information and other sensitive details, infiltration of other malware, loss of personal files, etc. |
| Termination | Delete the infection with anti-malware software |
| Recovery | Scan your device with FortectIntego for best results |
While it is possible to be a false positive, it is necessary to find out whether or not the detection of Fuerboos trojan poses any threat to your computer first. The best way to do that is by scanning your device with another anti-malware tool and even confirming with the developers of the program in question. Nevertheless, if the infection is real, it is vital to remove Fuerboos virus as soon as possible.
Fuerboos false positive is detected due to the operation patterns of certain applications. For example, many newly-created apps establish a new Windows service that tracks the incoming requests in the combination of the rare binary – the trait of the newest releases.
If Fuerboos trojan infection is not a false positive, however, you might be facing serious consequences, as threat actors might:
- steal money directly from your bank account by remotely controlling your computer;
- execute arbitrary code and upload other malware on your device;
- include you in a botnet operation;
- lock up your files and demand ransom for the decryption tool;
- steal your sensitive information and sell it on the Dark Web;
- secretly mine cryptocurrency by abusing your system resources, increasing electricity bills, slowing down the operation of the PC and deteriorating the hardware, etc.
Unfortunately, but Trojan:Win32/Fuerboos symptoms are not consistent, as it depends on the infection type:[3]
Symptoms of infection vary from threat to threat. In general, threat activity can result in unusual system behaviors, including unexpected opening of windows, unusual network connections identified by your firewall, and decreased system performance.
Fuerboos removal should only be performed if you are sure that the detection is genuine. You can use Windows Defender or other security software to terminate the malicious activity on your machine. Once you delete the virus, you should scan your device with FortectIntego to restore all the affected system files for a swift recovery.
Avoid malware by being attentive online
There are many ways to get infected with malware while browsing the internet. While many methods include users initiating the infection themselves, some, more sophisticated malware distribution methods require no user interaction at all. For example, drive-by downloads, exploit kits, software vulnerabilities, and other techniques can inject malicious code without users initiating it. However, in most cases, infections occur due to negligence from the user part.
To avoid malware infections, follow these tips from security experts:[4]
- Install reputable anti-malware software with real-time scanning feature;
- Make sure Windows and the installed apps are patched with the latest security updates;
- Treat every email with attachments and/or hyperlinks as a potential threat – scan them with tools like Virus Total;
- Do not download/execute cracks or pirated software;
- Use ad-blockers on sites that are considered to be high-risk (porn, torrent, gambling, etc.);
- Enable two-factor authentication for your important accounts and use password managers;
- Backup your files on an external drive or a virtual storage.
Remove Fuerboos of if it is not a false positive
Before you remove Fuerboos virus from your computer, you need to make sure that it is not a false positive. The easiest way to do so is by downloading and installing alternative anti-malware software, such as SpyHunter 5Combo Cleaner or Malwarebytes. All you have to do is download the security application, install it, and run a full system scan. If any of the AV engines detect the infection as well, it is a high chance that it is not a false positive. If the virus is tampering with the anti-malware application, enter Safe Mode with Networking – we explain how below.
Nevertheless, because heuristic detection deals with brand new and never discovered threats, the best way to find out whether the program in question is malicious is by contacting its developers or flag it up on official anti-virus provider forums.
Once you are sure it is malware, you should proceed with Fuerboos removal as soon as possible to avoid such consequences as identity theft, money loss, or personal data leak.
Getting rid of Fuerboos. Follow these steps
Manual removal using Safe Mode
To remove Trojan:Win32/Fuerboos safely, enter Safe Mode with Networking as explained below:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Fuerboos and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting trojans
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Windows 10 - Installer recognized as trojan (Win32/Fuerboos.A!cl) by Defender #4170. GotHub. Official technical support.
- ^ Trojan:Win32/Fuerboos.C!cl. Blizzard Entertainment. Official forums.
- ^ Trojan:Win32/Fuerboos.C!cl. Microsoft. Microsoft Security Intelligence.
- ^ Novirus. Novirus. UK's cybersecurity team.
