Internalnetworkpc.com ads (fake) - Free Guide
Internalnetworkpc.com ads Removal Guide
What is Internalnetworkpc.com ads?
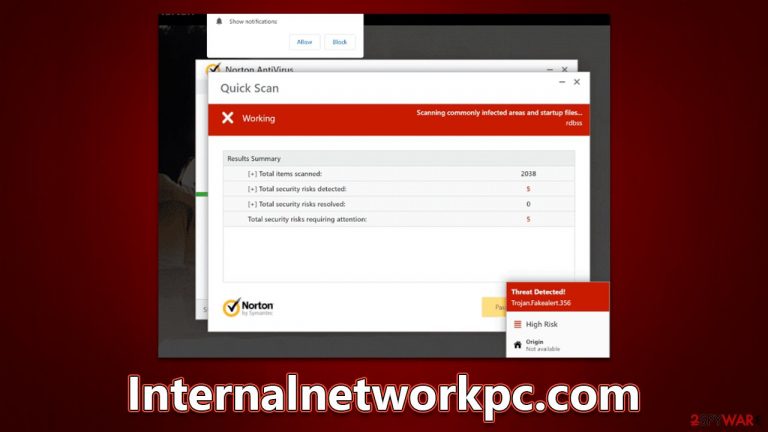
Internalnetworkpc.com is a scam website that asks you to enable push notifications and makes you download software
Internalnetworkpc.com is one of many websites that attempts to dupe users into clicking on affiliated links and purchasing the software by imitating a well-known security vendor. You could encounter this malicious page at any time while browsing the web using Chrome, Safari, Edge, Firefox, or any other web browser. You'll most likely be redirected here after clicking on a bad link from another site – torrent sites, illegal video streaming sites, and similar are likely culprits.
In some circumstances, adware might force users to see phishing[1] sites more often than not. If it's paired with an increased number of ads, this effect is amplified. Because removing the offending software could stop Personal-scan.com redirects for good, uninstalling unwanted programs should be your top priority.
| Name | Internalnetworkpc.com |
| Type | Scam, ads, redirect |
| Infiltration | Redirects from other websites, pop-up ads, potentially unwanted applications |
| Scam content | A message claims the subscription for security software has expired and needs to be immediately renewed to remove the allegedly found viruses. Also asks to enable push notifications |
| Dangers | Installation of PUPs or malware, sensitive information disclosure, financial losses |
| Removal | Interacting with the scam content is dangerous, as scammers may promote fake versions of antivirus software. Instead, use reputable tools for your system safety |
| Other tips | To make sure that third parties can no longer track your online activities, we suggest clearing browser caches and other leftover PUP files with FortectIntego |
Scammers employ names of well-known security companies
Cybercrime is immensely lucrative, and scam artists have found much success by manipulating people's fears and lack of understanding about how computer viruses spread. Numerous studies show that users fall victim to tech support scams and lose billions of dollars every year[2] because they cannot tell the difference between real threats and fake notifications or phone calls from scammers.
Social engineering ploys, like incorporating familiar names in cybersecurity, are nothing new. It gives people a sense of false security and builds trust, so they believe these scams are legitimate – Internalnetworkpc.com is one such example of this behavior. In fact, there are thousands of other websites that use identical scam techniques, including Erbi90s.click, Control-scanning.com, Protectwatcher.xyz, and many others. They use identical message even, which reads:
Your PC is infected with 5 viruses!
ACTION REQUIRED
Your McAfee Subscription Has Expired!
Renew now to keep your PC protected.
If your PC is unprotected, it is at risk for viruses and other malware.
This message is definitely fake, and all the virus infection claims are too. No website can tell if your system has a virus just by looking at it (unless malware is already installed), so any messages claiming that your computer is infected are automatically false – even if they look like they're from a legitimate source. The logos and UI elements in these messages can be very convincing, but they're easy to fabricate.

How to resolve the situation
It must be said that you should not interact with the scam page in any way – this includes clicking links and downloading software. If you do, you will likely be redirected to a McAfee download page; however, there is no guarantee that it will be legitimate. There is always a chance you will end up on a false/harmful version of the AV software.
By purchasing software from scammers and giving your money, you are inadvertently supporting their scam business. The best thing you can do is to immediately close the webpage and scan your device for any potential adware. If you have installed any promoted software from Internalnetworkpc.com or its links, follow the steps below as soon as possible.
1. Check the system for infections
We recommend using SpyHunter 5Combo Cleaner, Malwarebytes, or another reputable anti-malware software to check your system. Not only will it find any unwanted apps that might be causing you to encounter phishing websites, but it can also find hidden malware. If you want to try removing the adware yourself, start by checking programs installed on the system level:
Windows
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

Mac
While moving apps into Trash is how you delete most normal applications, adware tends to create additional files for persistence. Thus, you should look for .plist and other files that could be related to the virus. If you are not sure, skip this step entirely.
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
Browser extensions can also be used to perform adware-type activities. Therefore, you should also check your browser for suspicious add-ons and remove them immediately – you can achieve that by clicking the “Extensions” button next to the settings menu. If you aren't sure, simply leave this job for security software.
2. Get rid of push notifications
If you have enabled push notifications from Internalnetworkpc.com either intentionally or by accident, you might start seeing suspicious pop-ups that include various ads and links. These can represent inappropriate or misleading content and trick you into installing other potentially unwanted software or malware, disclose your personal information, or make you lose money for useless services. Thus, get rid of them as soon as possible.
Google Chrome
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.

Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.

MS Edge (Chromium):
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.

Safari:
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.

3. Take care of your privacy
Adware is known to gather various details once it gets installed on the device. For example, cookies[3] and other tracking items can be placed on your local folders and then be used to gather your search history, visited websites, link clicks, IP address, and much more. Therefore, we recommend you employ FortectIntego or use the manual guide below to remove these remnants from your device after you are sure that malware and adware are eliminated.
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content, and press Clear.

MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

How to prevent from getting adware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Phishing attacks. Imperva. Application and data security.
- ^ Audrey Conklin. Record $4.2 billion stolen through online scams in 2020: report. Fox Business. Fox News.
- ^ What are cookies? | Cookies definition. Cloudflare. The Web Performance & Security Company.
