Kuus ransomware (Virus Removal Instructions) - Decryption Methods Included
Kuus virus Removal Guide
What is Kuus ransomware?
Kuus ransomware – a file locking virus that attempts to extort Bitcoin from innocent PC users
Kuus file-encrypting virus is ransomware that has resurfaced in the second half of July 2020. Detected by the well-known ransomware hunter Michael Gillespie[1], the ransomware has been proved to be the 241st variant of the STOP/Djvu ransomware family. Just like its predecessors, the malware takes advantage of software cracks, keygens, password unprotected RDPs, and other stealthy infiltration strategies.
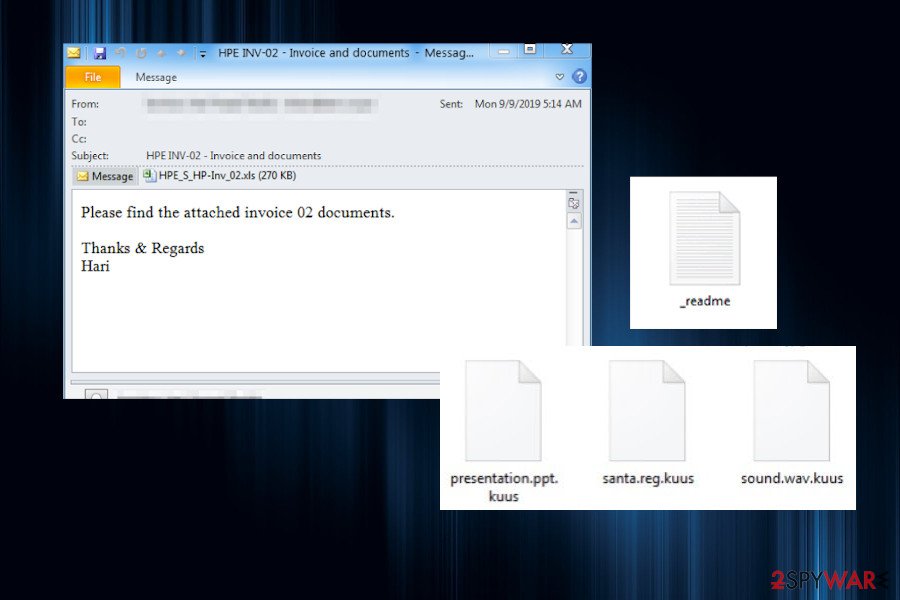
If the payload dropper is activated, the ransomware runs a bunch of malicious files, including , f6ff.tmp.exe, c7c6.tmp.exe, and 6AEC.tmp.exe. This group of files is responsible for damaging the system, running the AES-256 encryption algorithm, and taking control over all personal files stored on the infected machine. If successful, the operation ends up in a complete lock of personal data stored on the system. All pictures, documents, archives, etc. get .kuus file marker and cannot be opened any longer. Ransomware managers provide a sole problem solution – paying the ransom, which is $490 if paid within 72 hours or $980 if later.
| Name | Kuus |
| Type | Ransomware/file-encrypting virus |
| Family | STOP/Djvu |
| Version | 241st member of Djvu virus |
| Ransom note | _readme.txt |
| Criminal contacts | helpmanager@mail.ch, restoremanager@airmail.cc |
| File extension | .kuus file marker |
| Symptoms | Personal files can no longer be accessed. All of them have an unusual file extension attached. Alternatively, the machine runs slower than it used to before, high CPU usage can be noticed |
| Danger level | High. The ransomware can permanently delete personal files, cause money loss, or download other viruses to the system |
| Can files be decrypted? | .kuus file decryptor is not yet available. However, there are several alternatives that can be applied for unlocking some of the encrypted files |
| Removal | Before any attempts to regain access to the personal files, it's a must to remove the ransomware from the machine. For this purpose, use a trusted anti-virus program |
| Fix virus damage | Ransomware damage to the system is severe. The malware runs a multiplicity of commands via an elevated PowerShell aiming at Registry corruption, disability of system files, startup processes, and more. To fix suchlike damage, try using FortectIntego repair tool |
.kuus file virus is a ransomware that has been expected as a weekly Djvu ransomware family augmentation. Initially, it's difficult to forecast which variant will be prevailing, but the latest practice with Maas, Zida, Repl, Usam, and others show that the latest releases of this ransomware family are perspective.
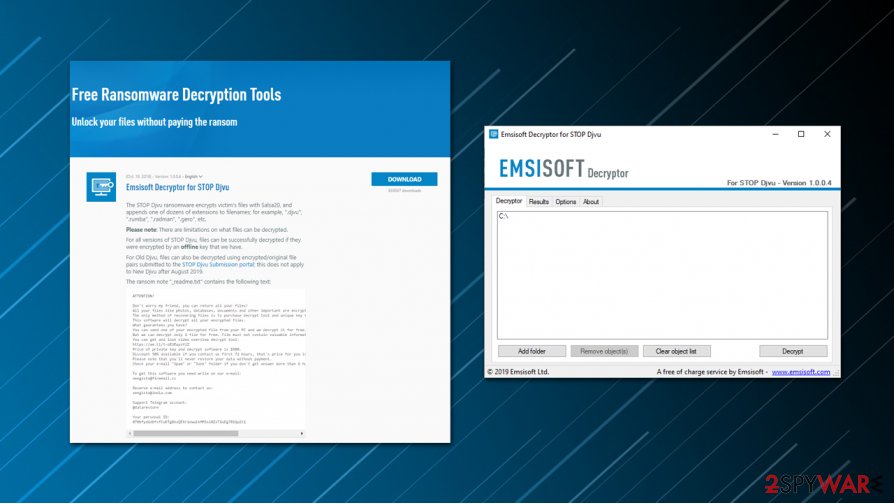
Djvu Ransomware virus remains one of the most active viruses since 2019 taking approximately 56% of the active file-encrypting ransomware market. Although variants released before 2019 August can be successfully decrypted using an official decryptor by Emsisoft, the latest variants cannot be cracked by the same decryptor because they are using online keys. In other words, all the keys provided to the victims are unique and generated in a secure manner, which is why there's no working decryptor for the new versions like the Kuus ransomware virus.
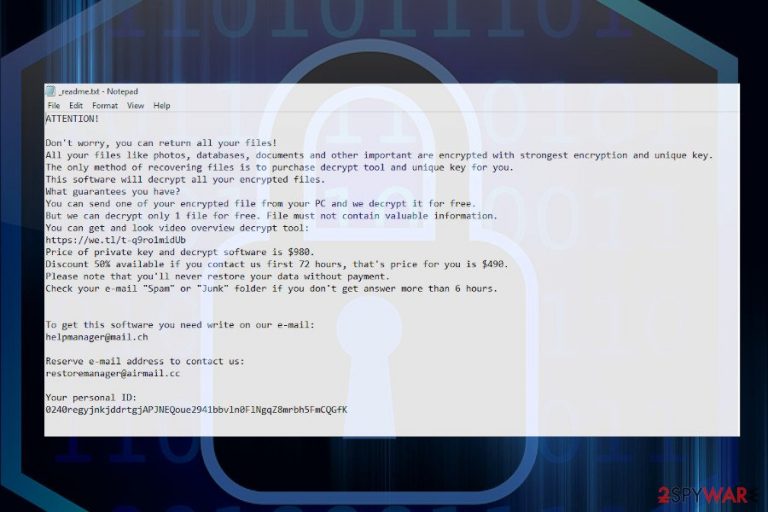
The installation of the ransomware is spotted by the owner of the infected machine because all files (except system files) are encrypted by .kuus extension. Compromised files lose their typical logos, i.e. instead of PDF file logo victim sees a blank logo. Apart from inaccessible files, the ransomware manifests its presence by creating a _readme.txt note on the desktop and many other non-system files. The note says:
ATTENTION!
Don’t worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-7YSRbcuaMa
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.To get this software you need write on our e-mail:
helpmanager@mail.chReserve e-mail address to contact us:
restoremanager@airmail.ccYour personal ID:
The ransomware sample has been uploaded to VirusTotal[2] scanner the day the virus has been released. Based on the results, Kuus removal can be successfully initiated by 47 AV programs out of 72 possible. Typically, the security tool warns the user about the presence of the following infection:
- Win32:CrypterX-gen [Trj] (AVG)
- Trojan.GenericKD.43514787 (BitDefender)
- Trojan.GenericKD.43514787 (B) (Emsisoft)
- W32/Ursnif.DA!tr (Fortinet)
- Trojan.MalPack.GS (Malwarebytes)
- TrojanSpy.Win32.EMOTET.USXVPGI20 (TrendMicro)
- A Variant Of Win32/Kryptik.HEYU (ESET-NOD32)
- Trojan.Win32.Chapak.equk (Kaspersky)
- Trojan:Win32/Glupteba.DSE!MTB (Microsoft), etc.
If the system states showing such and similar alerts, do not ignore them. Kuus ransomware removal should be performed immediately to minimize the system damage. Besides, the elimination is needed to start data decryption. However, since the ransomware may run malicious files to block AV tools, you may need to restart the system into Safe Mode with Networking.
As soon as you remove Kuus ransomware, you can pursue with the .kuus file decryption methods. If you have data backups, we recommend you to remove the virus ASAP and use the copies that you have. That's the best scenario possible. If, however, you don't have backups, there are several data recovery options.
A full guide on .kuus file recovery is provided at the end of this article. However, before that, make sure to remove the virus using a robust anti-virus and fix the damage that it initiated over the system with FortectIntego tool.
Kuus file virus can lock files on the connected external drives
The Kuus virus shows a tendency to widespread. Right after its detection, victims of this Djvu successor started reporting that the virus managed to lock files on the external drive. Although this fact is currently under investigation by experts, it's most likely that the external drive has been connected to the targeted machine.
The .kuus file recovery on the external drive is the same as on the PC or laptop. If you have a functional decryption key, all files can be decrypted. Otherwise, you can only test the alternative data recovery methods, which may help to return at least some of the locked documents.
Kuus virus files: limited recovery options
Ransomware, such as the Kuus file virus, is one of the most dangerous computer infections out there. Since it belongs to the Djvu family, it mainly targets home users rather than corporations and businesses. The developers rely on victims to pay a ransom as soon as they are aware that they cannot open or modify previously-accessible personal data. Since ransomware authors do not care about the wellbeing of their victims, they seek to infect as many people as possible.
The most common misconception about ransomware is that anti-malware software can remove .kuus file extension from the files, and allow users to use them once again. However, they couldn't be more wrong, as security software is not designed for that purpose. Anti-malware is there to free your system from the infection and eliminate the payload of ransomware (e.g., malicious files).
Therefore, do not expect to be able to open .kuus files after you eliminate the infection, as it will not work. Instead, you are left with a very limited set of options that could help you if you are not willing to pay the $490/$980 ransom to criminals.
In most cases, it cannot be decrypted. However, since .kuus files virus belongs to a malware family that is extensive and often scrutinized by various security researchers and AV companies, there are several methods that could help you.
Using Emsisoft's decryption tool
In case the Kuus file virus used an offline ID to lock your data, there is a chance that Emsisoft's decryptor for Djvu could help you. Note that this only works after one of the victims pays ransomware authors, regains a decryption key, and then shares it with Emsisoft security researchers. Therefore, it is important to retain encrypted files, even if there is no immediate solution upon infection.
Third-party recovery tools usage might bring some positive results
While data recovery applications work great when data is accidentally deleted or formatted, they are not as good when it comes to ransomware-encrypted files. In some situations, however, victims of cryptomalware might be able to restore at least some portion of encrypted data.
Utilizing built-in Windows resources
It is not surprising that Windows uses automated backup systems, which can be very useful in many situations. For the purpose, Microsoft employs a system called Shadow Volume Copies. Unfortunately, ransomware developers are well aware of this system and program malware to delete these volumes during the infection process. In case this step fails, users still have chances to recover .kuus files without many troubles.
STOP ransomware variants most successfully spread through software cracks
Ransomware virus is the prevailing virus type circulating on the Internet for the last couple of years. Hackers take advantage of inexperienced PC users who fall for various social engineering tricks and unconsciously download file-locking viruses. Unfortunately, the minority of PC users take care of the backups, so ending up with ransomware often pushes them to pay the demanded ransom.
The vast majority of ransomware attacks are initiated via cracked products, such as key generators that are available on torrenting websites, such as The Pirate Bay. Therefore, to protect yourself from virus attacks, do not visit such websites, and stop pirating in any form. Keep in mind that pirated software is the best target for hackers. In addition to cracks and other pirated content, experts from Dieviren.de[3] warn that criminals can spread ransomware via:
- Email spam attachments. Malicious executables are typically disguised under EXE, Word, PDF, and similar attachments.
- Malvertising. Malicious ads positioned on script-infected websites can run a payload dropper once clicked.
- Fake software updates. People are more and more educated in the technology field, so this method is losing success. Nevertheless, some users still fall for clicking on fake updates saying that some Windows software is out-of-date, Java Flash player or web browser needs updates. Such pop-ups occurring on random websites are fake and should never be trusted. Software updates can be downloaded from official sources only.
Eliminating Kuus ransomware and recovering the locked files
If you have become a target for hackers, the first thing that you have to do is to remove Kuus virus completely. This ransomware is dangerous due to a couple of reasons. First of all, it can permanently delete personal files. Second of all, it can run a secondary payload and download other cyber infections, such as Trojan or spyware. Thus, immediate removal is required.
To speed up Kuus removal, restart your machine into Safe Mode and launch a full system scan with a professional anti-virus program. Although you may detect some of the malicious virus files on the system, you are not very likely to be allowed to disable them. Thus, an automatic removal procedure is required with tools like SpyHunter 5Combo Cleaner or Malwarebytes.
When you successfully remove Kuus virus from Windows, you should check the machine for the damage. For this purpose, try using FortectIntego tool. In case it does not find any affected areas, you can proceed with the data recovery steps listed below.
Getting rid of Kuus virus. Follow these steps
Manual removal using Safe Mode
Do not fall for panic if you cannot run the AV scanner. Kuus virus may be running several processes to block security programs. To enable the software, restart the system into Safe Mode with Networking.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Kuus using System Restore
Previous Windows version might help when trying to deal with ransomware.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Kuus. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Kuus from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.As we have already explained, Kuus ransomware virus belongs to the next-gen Djvu versions, which uses unique online keys. Thus, the official decryptor is not available, at least not yet. Nevertheless, we do not recommend paying ransom for criminals. Instead of that, try third-party data recovery methods listed below.
If your files are encrypted by Kuus, you can use several methods to restore them:
Install and run a scan with Data Recovery Pro
Data Recovery Pro might help to retrieve some of the .kuus files.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Kuus ransomware;
- Restore them.
Use Windows Previous Versions feature for data restore
In case third-party software did not help you to retrieve personal files, try to regain access to them using the System Restore feature. (The feature must have been enabled before the attack).
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Use Shadow Explorer
Shadow Explorer is not likely to help in this case. The ransomware is set to run the command to delete Shadow Volume Copies. However, you can give this method a try in case the ransomware failed to run the command via the PowerShell successfully.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No official decryptor available.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Kuus and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Michael Gillespie. Twitter. Social networking platform.
- ^
analysis . VirusTotal. Free URL and virus scanner. - ^ SICHERHEIT- UND SPYWARE-NEUIGKEITEN. Dieviren. Virus and spyware news.







