Locks ransomware (Virus Removal Instructions) - Free Guide
Locks virus Removal Guide
What is Locks ransomware?
Locks ransomware – malware that encrypts files and then asks for $1,500 ransom for its retrieval
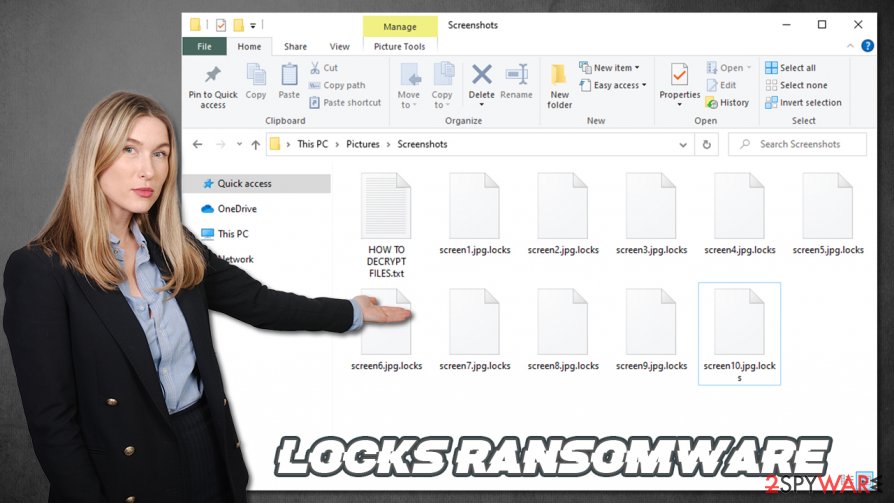
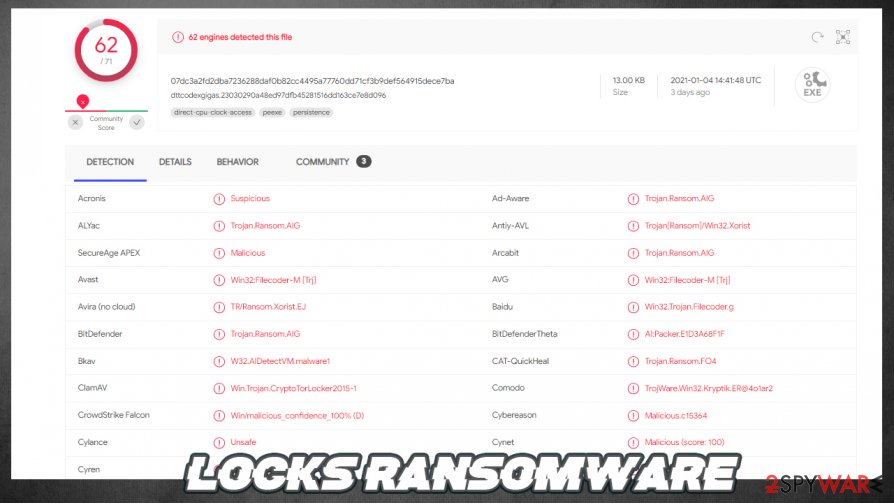
Locks ransomware is a new version of the Xorist ransomware family. It encrypts all personal data on an infected computer, renames it by appending all original filenames with a .locks extension, and creates two types of ransom notes which contain the same message.
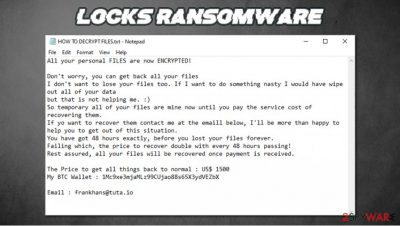
Within these notes (a pop-up window titled “Error” and text file HOW TO DECRYPT FILES.txt), developers of Locks virus state their demands, the main of which is to pay $1,500 in cryptocurrency Bitcoin for a decryption key that would allegedly decipher the encrypted data.
If the ransom isn't forwarded to their wallet crypto-wallet (1Mc9xe3mjaMLz99CUjao88s65X3ydVEZbX.) within 48 hours, the amount will be doubled every two days. The threat actors are urging the victims to contact them through a provided email address – frankhans@tuta.io.
| name | Locks ransomware |
|---|---|
| type | Ransomware, file-locking virus |
| Family | Xorist |
| Appended file extension | .locks |
| Ransom note | Text file HOW TO DECRYPT FILES.txt and a pop-up window. Both bearing identical messages. |
| Ransom amount | The original price is $1500. If the ransom isn't paid within 48 hours, it doubles. |
| Criminal contact details | frankhans@tuta.io |
| Criminal Crypto-wallet | 1Mc9xe3mjaMLz99CUjao88s65X3ydVEZbX |
| Virus removal | This, and any other kind of malware, should be eliminated with anti-malware software to ensure it's done properly |
| system repair | We highly recommend performing a system repair with the FortectIntego system tune-up tool, having in mind that cryptoviruses usually mess up Windows Registry and other core files and settings |
Ransomware is on the rise, and cybersecurity experts predict that damages caused by this type of malware could increase to $20 billion this year.[1] We've already spotted some new variations of ransomware this year, including Atek, Ziggy, Qlkm, 2021, and many more.
Developers of Locks ransomware, and cybercriminals, in general, should never be trusted as they are criminals for a reason. The transferred ransom only encourages them to increase their attacks and develop more sophisticated crypto-malware that are harder to detect. All in all, these are the most probable scenarios after a victim meets the demands of the assailants:
- Threat actors disappear, and no decryption tool is sent.
- The decryption tool doesn't work.
- Criminals ask for more money.
- Instead of the promised tool, additional malware is sent.
Other ways of regaining access to your data are possible. You just have to not panic and not make any rash decisions. The only right thing to do is to remove Locks ransomware from the infected machine as soon as possible.
It would be best if you did that with anti-malware software that would automatically locate, isolate, and eliminate the virus with all of its components. If there's no anti-malware software installed on the device, we recommend downloading reliable tools such as SpyHunter 5Combo Cleaner or Malwarebytes and letting them do the work.
In some cases, cryptovirus alter Windows Registry, host files, and other key system settings and files to establish persistence and prolong their unwelcomed stay by disabling anti-malware tools. In that case, Locks ransomware removal might be done in Safe Mode with Networking (see a detailed guide on that at the bottom of this article) if the virus tampers with the security software's functionality.
When the ransomware-type infection is removed from your device, it's time to take care of those corrupted system settings. The best results are achieved when system repair tools such as the FortectIntego software is used to scan the whole system and let it do the rest.
Message from the creators of Locks file virus in the ransom note states:
All your personal FILES are now ENCRYPTED!
Don't worry, you can get back all your files
I don't want to lose your files too. If I want to do something nasty I would have wipe out all of your data
but that is not helping me. 🙂
So temporary all of your files are mine now until you pay the service cost of recovering them.
If yo want to recover them contact me at the emaill below, I'll be more than happy to help you to get out of this situation.
You have got 48 hours exactly, before you lost your files forever.
Failing which, the price to recover double with every 48 hours passing!
Rest assured, all your files will be recovered once payment is received.The Price to get all things back to normal : US$ 1500
My BTC Wallet : 1Mc9xe3mjaMLz99CUjao88s65X3ydVEZbXEmail : frankhans@tuta.io
Spam emails – still one of the most popular ways for cybercriminals to deliver their creations
Cybercriminals have many weapons when we're talking about malware delivery options – Remote Desktop Protocol attacks, drive-by downloads,[2] file-sharing platforms, etc. But our research shows that one of the most popular techniques used by the threat actors is spam emails.
They send out tens of thousands of these emails all over the world during so-called spam campaigns. These letters usually urge the users to either click on a hyperlink that opens a malicious site where the virus can be downloaded without even pushing anything or download an infected attachment that contains the virus payload file.
If either of these options is taken, and the virus bypasses anti-malware software filters, then some sort of malware infection is guaranteed. We're here to help, so use this short list of guidelines to determine whether the email is sent from a legitimate source or cybercriminals:
- Companies usually don't make grammatical mistakes.
- Email sender's domain must exactly match the one of a company.
- Companies don't push their clients into visiting their sites or opening unsolicited attachments.
- Legitimate companies don't request sensitive information to be sent via email.
- Companies know their clients' names, so they address you directly, instead of “Dear member”, “Dear Client”, etc.
Detailed Locks ransomware removal guide
More and more people suffer from ransomware attacks every day. Computer users should upgrade their cybersecurity level by acquiring professional, trustworthy anti-malware software such as SpyHunter 5Combo Cleaner or Malwarebytes to watch their backs whenever they're connected to the internet.
If you were unlucky enough and got your device infected by Locks ransomware – all is not lost. Other family members have already been deciphered, meaning that their encrypted files are easily decryptable with free software available on the Emisoft webpage.
If you've tried their decryption software but it didn't work – there's still hope. The good guys are constantly working on helping ransomware victims by creating decryption tools for various cryptoviruses. Before Locks ransomware removal, export all encrypted data to offline storage, and check back on us as we update our readers with the latest news.
Once that's done, you're ready to remove Locks ransomware from your machine. Launch anti-malware software and perform a full system scan. Let the application to find, isolate, and eliminate the virus. When it's finished, experts[3] recommend performing a system repair with the powerful FortectIntego system tune-up tool to restore all corrupted system files and settings.
Getting rid of Locks virus. Follow these steps
Manual removal using Safe Mode
If the infection can't be eliminated in normal Windows mode, then try doing it in Safe Mode with Networking/GI]
[GI=method-2]If restore points weren't deleted or encrypted, then the infection could be removed with System Restore
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Locks from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Locks, you can use several methods to restore them:
Using third-party apps, such as Data Recovery Pro to restore .locks extension files
These kinds of apps might help to recover encrypted files.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Locks ransomware;
- Restore them.
File recovery with Windows Previous Version feature
Windows Previous Version feature might be a helpful tool when trying to restore .locks extension files.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Shadow Explorer uses Shadow Volume Copies to recover data
If these copies are undamaged and weren't removed, then Shadow Explorer might recover some data from them.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No decryption tool is currently available
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Locks and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Steve Morgan. Global Ransomware Damage Costs Predicted To Reach $20 Billion (USD) By 2021. Cybersecurityventures. Cybersecurity news.
- ^ Drive-by download. Wikipedia. The free encyclopedia.
- ^ Losvirus. Losvirus. Spyware and security news.














