Nineaidmon.live ads (scam) - Free Guide
Nineaidmon.live ads Removal Guide
What is Nineaidmon.live ads?
Nineaidmon.live is a suspicious website that spreads scams and attempts to gather personal user data

You might come across Nineaidmon.live completely by accident while browsing the web on your Google Chrome or another web browser, although adware[1] installed on your device might also cause redirects to it. There could be a variety of scams that the site could propagate, although all of them could be described as survey or lottery scams. The main goal of this page is to convince visitors that they are the lucky winners and that a free gift is awaiting them.
As soon as users get excited with the prospects of receiving an expensive item for free, scammers would reroute them through several other pages, ultimately asking them to provide personal information under various pretexts. It is also not uncommon for crooks to make people subscribe to various services, which would result in monthly or weekly payments directly from their bank accounts.
| Name | Nineaidmon.live |
| Type | Scam, phishing, redirect, adware |
| Operation | The scam attempts to trick users with fake surveys and giveaways (allegedly from Google), only to later ask for personal information or make people subscribe to useless services |
| Distribution | Redirects from other malicious websites, adware |
| Risks | Privacy issues due to various personal data disclosure, installation of malware or financial losses |
| Removal | We recommend checking the system for potentially dangerous software with the help of SpyHunter 5Combo Cleaner or Malwarebytes security software |
| Other tips | In order to stop third parties from tracking you, employ FortectIntego to clean your browser caches. If you provided your personal information, such as contact details, keep in mind that you may receive scam calls or spam emails trying to trick you again |
Ways people get tricked
Online fraud has been around for decades now, and the perpetrators usually get away with it because of how anonymous the internet can be. In fact, the resources needed to investigate these crimes are overwhelming, that's why only high-profile cybercriminal gangs are being investigated. In the meantime, millions of people are being scammed online thanks to websites such as Nineaidmon.live, and it's not the only one out there.
While the web page is not classified as malicious per se, the intentions of the people behind it are clear: to make people do something they otherwise wouldn't, which is the main principle of social engineering[2] schemes. For example, the site can commonly promote the “You've made the 9.68-billionth search” scam, which is presented as a message from a well-known tech giant Google. It says:
You've made the 9.68-billionth search!
Congratulations! You are the lucky winner!
Every 10 millionth search is reached worldwide, we will proclaim a winner to send out a thank-you gift.
Please select your lucky prize below and claim it by following the instruction.
According to the message, Google has selected you, the user, because you did the 9.68-billionth search. It is unclear why the number is 9.68, and it almost seems like crooks simply came up with it on the fly. Nonetheless, it is deemed to be some type of occasion, and that's allegedly what users are entitled to be rewarded for.
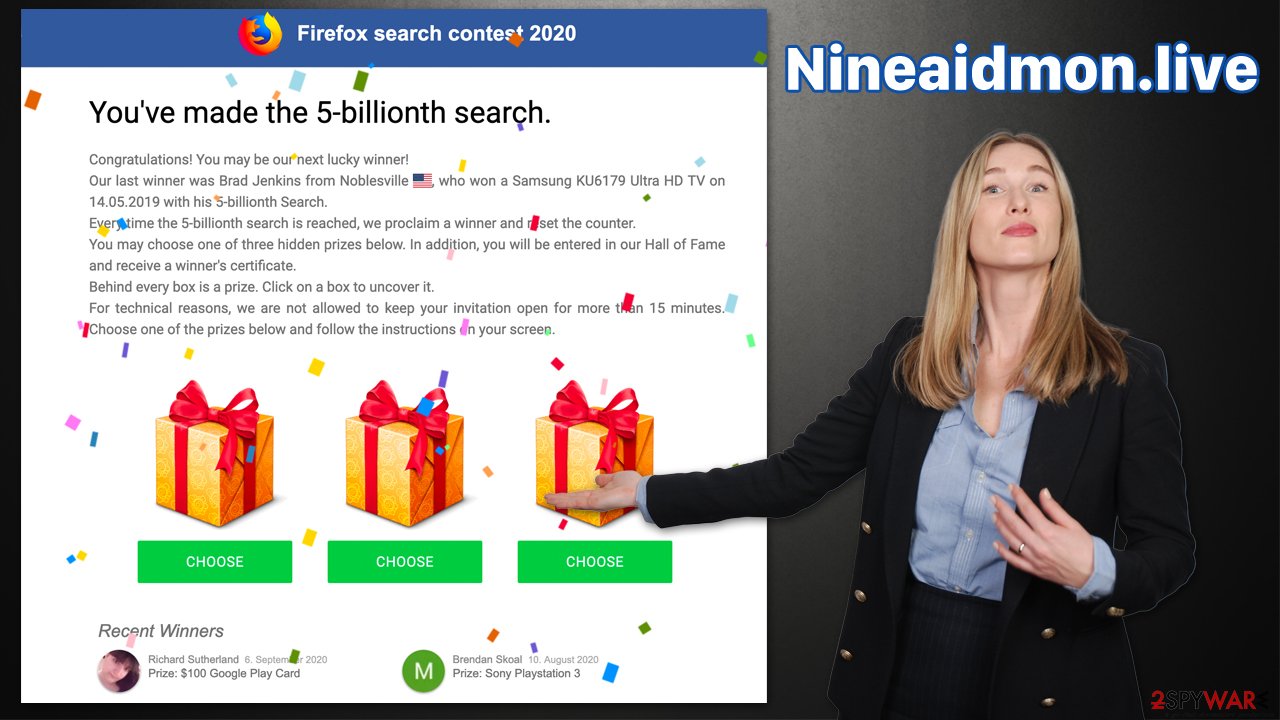
Upon entering Nineaidmon.live site and reading this message, users are then asked to pick one of the gift boxes, which usually returns a great result, such as a $1,000 Amazon gift card, the newest iPhone, PlayStation, or a TV. Excited, users may proceed through several other steps, ultimately landing on the last page where they would be asked to provide their contacts and other personal data.
In some cases, crooks even ask to give credit card details as proof of identity, which is absolutely bogus request. Such information can later be sold on underground forums to cybercriminals, which may result in financial losses for those affected. Likewise, subscriptions to suspicious services may result in the credit card being charged automatically in particular time intervals until the service is canceled.
Tips on how to avoid being scammed online
First of all, the easiest way to avoid being scammed online is to avoid accessing websites like Nineaidmon.live, Clickdark.xyz, Papcorwye.live, Watchadsfree.com, etc. For that, you need to make sure that you avoid the installation of adware and other potentially unwanted/malicious software and refrain from visiting high-risk websites.
Malicious software will rarely affect your system if you adhere to security measures, including running security software on your device at all times and not visiting websites that are known for their security issues (torrents, software cracks, illegal video streaming, and similar).
Besides this, it is inevitable that you may still run into various scam pages by accident, even without visiting risky sites. For example, even legitimate and high-profile websites could get hacked[3] unexpectedly, so visiting them could expose you to malicious ads or start redirecting you to scam sites.
Therefore, you should always pay close attention to what you are being shown – always question messages which claim you won something for allegedly no effort at all or if you are told that your system is infected with dangerous viruses. The biggest giveaway is the URL address of the site showing the scam; for example, Nineaidmon.live has nothing to do with Google.
Adware removal and remediation
Close the browser tab the next time you come across a scam message on the internet. Even if you don't detect any adware or other malware infection symptoms, it's still a good idea to double-check – especially if you previously visited insecure websites.
Begin by checking the installed applications and getting rid of anything that appears suspicious. If you just installed a new application and are seeing more advertising than usual, remove it right away. Don't worry if you're not completely sure; SpyHunter 5Combo Cleaner or Malwarebytes will always take care of any harmful programs automatically.
Windows
- Enter Control Panel into the Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till the uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
Mac
While moving apps into Trash is how you delete most normal applications, adware tends to create additional files for persistence. Thus, you should look for .plist and other files that could be related to the virus. If you are not sure, skip this step entirely.
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)
![Uninstall from Mac 1 Uninstall from Mac 1]()
To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
We recommend you check for unwanted extensions as well; you can do this by clicking the “Extensions” button, usually located at the top-right corner of your browser window, and removing all the suspicious add-ons. We recommend uninstalling everything if you aren't sure which app is causing issues.
Finally, you should also remove cookies and other web data to ensure that your online activity tracking no longer takes place. If you don't feel like doing this manually, you can always count on FortectIntego – a maintenance and repair utility that can clear your browsers and all the other junk from your system to improve stability. Likewise, it can correct errors and other issues commonly encountered after a malware attack. You also follow the instructions below for a manual solution.
Getting rid of Nineaidmon.live ads. Follow these steps
Remove from Google Chrome
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Remove from Microsoft Edge
Delete unwanted extensions from MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Clear cookies and other browser data:
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Restore new tab and homepage settings:
- Click the menu icon and choose Settings.
- Then find On startup section.
- Click Disable if you found any suspicious domain.
Reset MS Edge if the above steps did not work:
- Press on Ctrl + Shift + Esc to open Task Manager.
- Click on More details arrow at the bottom of the window.
- Select Details tab.
- Now scroll down and locate every entry with Microsoft Edge name in it. Right-click on each of them and select End Task to stop MS Edge from running.

If this solution failed to help you, you need to use an advanced Edge reset method. Note that you need to backup your data before proceeding.
- Find the following folder on your computer: C:\\Users\\%username%\\AppData\\Local\\Packages\\Microsoft.MicrosoftEdge_8wekyb3d8bbwe.
- Press Ctrl + A on your keyboard to select all folders.
- Right-click on them and pick Delete

- Now right-click on the Start button and pick Windows PowerShell (Admin).
- When the new window opens, copy and paste the following command, and then press Enter:
Get-AppXPackage -AllUsers -Name Microsoft.MicrosoftEdge | Foreach {Add-AppxPackage -DisableDevelopmentMode -Register “$($_.InstallLocation)\\AppXManifest.xml” -Verbose

Instructions for Chromium-based Edge
Delete extensions from MS Edge (Chromium):
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Clear cache and site data:
- Click on Menu and go to Settings.
- Select Privacy, search and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Reset Chromium-based MS Edge:
- Click on Menu and select Settings.
- On the left side, pick Reset settings.
- Select Restore settings to their default values.
- Confirm with Reset.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

How to prevent from getting adware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ What Is Adware?. Norton. Security research blog.
- ^ Will Kenton. Social Engineering. Investopedia. Financial market news.
- ^ Kristen Wright. How Do Websites Get Hacked?. iThemes. Essential WordPress Tools & Training.





















