“Oops your files have been encrypted” ransomware / virus (Removal Guide) - updated Sep 2018
“Oops your files have been encrypted” virus Removal Guide
What is “Oops your files have been encrypted” ransomware virus?
“Oops your files have been encrypted” is a threat that executes ransomware virus on the system

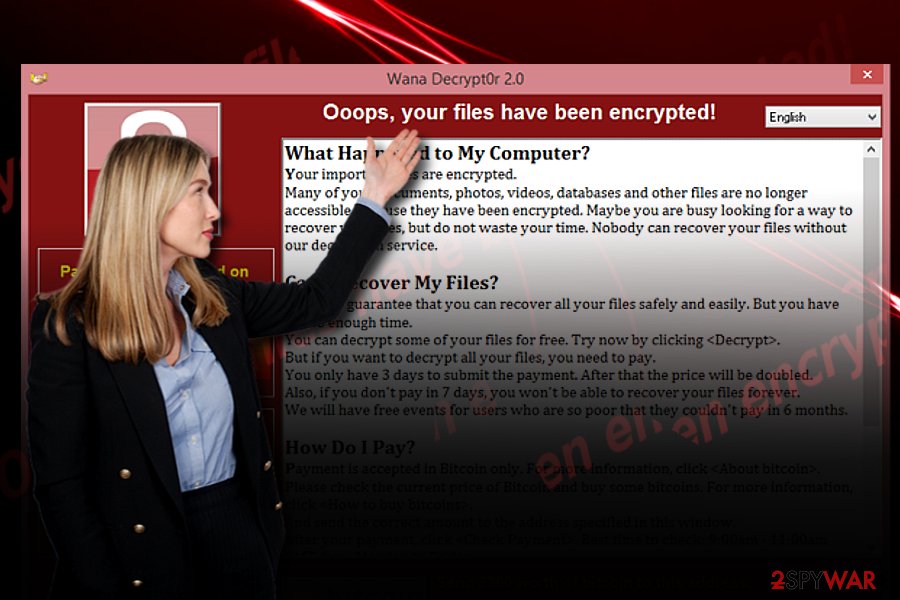
“Oops your files have been encrypted” virus is an alternative name given to an infamous cyber threat called WannaCry virus and other ransomware. This innocent string of words now brings a sense of fear to anyone who has been infected with WCrypt, Wana Crypt0r, WNCRY file extension virus or any other cryptovirus, or at least read one of the numerous articles written about such threats.[1] The “Oops your files have been encrypted” phrase is the first thing that people see when infected with this vicious parasite. However, the biggest issue is the loss of data which is typically encrypted by ransomware. The latest news is showing that the threat has just been updated – at the moment it is attacking servers and domains. The virus is causing an HTML window appearing with the “Ooops, your website have been encrypted!” slogan as a greeting. In this note, hackers are claiming that to unlock encrypted website you need to contact them via spamrslt@inbox.ru.
| Name | “Oops your files have been encrypted” |
|---|---|
| ALternative name | “Ooops, your website have been encrypted!” |
| Contact email | spamrslt@inbox.ru or spm.lifethuggest@hotmail.com |
| Type | Ransomware |
| Association | WannaCry |
| File extensions | .wncry; .wcry |
| Ransom note | @Please_Read_Me@.txt |
| Distribution | Exploits CVE-2017-0144 and permits the access to SMB protocol |
| Ransom amount | 300 USD |
| Elimination | Download and use FortectIntego for fixing the damage |
The phrase “Oops your files have been encrypted” has been actively used by ransomware developers who started using it in their own malicious creations. For instance, the new Petya virus version, which is trying to repeat the success of WCry by employing the Eternal Blue exploit kit, is also showing the same message.
“Oops your files have been encrypted” virus has been known worldwide since 2017, when it all started it has done a lot of things. The newest information about this ransom demanding threat is the ability to attack servers and leave their owners completely disabled.
It is known that this new “Ooops, your website have been encrypted!” ransomware and the previous version spreads the payload via Server Message Block protocol. At the moment, it appears that various domains, sites, and servers have been hacked by this virus. When the payment wallet address (1EwzEjNVtFezGQS5L555r4szP86GJ4n5DR) is googled, the results show a list of sites that are locked by this ransomware.
The short message displayed by ransomware provides these details:
- The wallet address;
- The ransom amount of 0.08BTC;
- Contact email address (spamrslt@inbox.ru or spm.lifethuggest@hotmail.com)
Origins of the WannaCry virus
On May 12th, cybersecurity specialists globally have been summoned for an emergency – the ransomware under the name of WannaCry has paralyzed the activities of the National Health Center, hacked Deutsche Bahn transportation system and Hitachi company and multiple others.[2]
Both, corporations and individual users, did not escape the menace of this malware. It was said to have affected approximately 200 000 devices in 150 countries. The success of this malware lies in the leaked information about EternalBlue vulnerability found in Windows OS based systems.
Users or companies which have been using older Windows version fell into the well-devised trap of the hackers. Personal files have been encoded and marked with .wncry or .wcry file extensions.
Luckily, the rampage of the malware was terminated by a security specialist Marcus Hutchins, who bought unregistered domain associated with the virus. Furthermore, further analysis revealed that the malware might be linked to a notorious group of hackers “Lazarus.” [3]
IT specialists are still convinced that it is too early to lay down arms as the threat may strike again. There have been already several subsequent versions[4]. If you have been affected by this malware, remove “Oops your files have been encrypted” virus. FortectIntego or Malwarebytes speeds up the process.
Unlike the majority of Windows OS-based ransomware viruses which spread via spam emails, this malware succeeded in wreaking chaos by exploiting EternalBlue exploit, technically known as CVE-2017-0144. It permits access to SMB (Server Message Block) protocol. Such an exploit has been developed by the US national Security Agency.
This cyber weapon has been kept in secret until the group of hackers known as Shadow Brokers stole it. Corresponding to it, Microsoft issued an update in March, but as the situation revealed a significant number of corporations and users did not apply the update.
Therefore, such mistake granted “Oops your files have been encrypted” malware freedom to wreak havoc. After it invades systems, further on, it behaves like an ordinary virus: encrypts files, launches its @Please_Read_Me@.txt guide with instructions, demands 300 USD in ransom and sets a 7-day period for users to pay. After the expiration, the files are said to be deleted.
Thanks to the malware researcher, the virus has been terminated. Unfortunately, further forecasts are not positive: recently previously emerged UIWIX virus has been gaining power in China.[5] The hackers seem to have eliminated the flaw which let the termination of the virus.
UIWIX virus does not have a “kill switch” and targets outdated systems as well. Unfortunately, this data leak also inspired others hackers to join the ransomware market. Adylkuzz virus is known as another virus which exploited the same vulnerability and is expected to rise in the future[6]. Thus, before we proceed to “Oops your files have been encrypted” removal section, get acquainted with its prevention options.
Malware prevention measures
This malware confirms that having professional anti-malware tools is not sufficient in battling crypto-malware threats. Therefore your participation is of high importance in the prevention of “Oops your files have been encrypted” infiltration. To stay at least a little safer, you should follow some basic rules:
- Install Windows OS updates right after they are issues.
- Keep system applications up-to-date.
- Avoid opening email attachments without confirming the identity of a sender, restrain from visiting websites which are crammed with ads do not get tempted to click on fishy links on similar domains.
It has been observed that early versions of WannaCry spread via spam messages, so these prevention tips are applicable. These tips will help you limit the risk of “Oops your files have been encrypted” hijack.
Ways to delete “Oops your files have been encrypted” virus
Despite how menacing this virus may be, remove “Oops your files have been encrypted” virus as soon as you notice its marks of activity on the computer. For the successful elimination, you may use malware removal tools such as FortectIntego or Malwarebytes. Only when “Oops your files have been encrypted” removal is completed, you may start thinking about data recovery procedure. On the final note, we encourage you to remain rational and vigilant and avoid diverting to panic or inadequate precautions methods.
Getting rid of “Oops your files have been encrypted” virus. Follow these steps
Manual removal using Safe Mode
Safe Mode should grant you access to the computer. Later on, you should be able to eliminate “Oops your files have been encrypted” virus.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove “Oops your files have been encrypted” using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of “Oops your files have been encrypted”. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove “Oops your files have been encrypted” from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by “Oops your files have been encrypted”, you can use several methods to restore them:
Data Recovery Pro method
This is one of the few methods to decrypt files. Since the application is designed for recovering files after a system crash, there is no 100% guarantee that you will succeed in recovering files.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by “Oops your files have been encrypted” ransomware;
- Restore them.
”Oops your files have been encrypted” Decrypter
On torrent sites, “Oops your files have been encrypted” decryption tools may appear. However, note that it might be only corrupted tools released by the hackers themselves. You may need to wait until IT specialists release such program for free.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from “Oops your files have been encrypted” and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Olivia Morelli. How to survive WannaCry attack?. 2-spyware. remove adware, spyware.
- ^ Some University of Montreal computers hit with WannaCry virus. The Globe and Mail. World news.
- ^ Elizabeth Weise and Jon Swartz. Why a shadowy hacking crime group called Lazarus may have launched a mass ransomware attack. USAToday. News and commenatry.
- ^ Timothy B. Le. The WannaCry ransomware attack was temporarily halted. But it’s not over yet.. Vox., Understand the News.
- ^ Ians. China warns of new ransomware-like virus UIWIX. The Economic Times. Business News, Personal Finance, Security News.
- ^ Jake Doevan . Adylkuzz crypto-miner exploited EternalBlue and DoublePulsar weeks before WannaCry. 2-spyware. remove adware, spyware.







