.WNCRY file extension virus (Decryption Steps Included)
.WNCRY virus Removal Guide
What is .WNCRY file extension virus?
.WNCRY virus can become the next most destructive crypto-malware
.WNCRY virus is an alternative name of ransomware, known as WannaCry, WanaCryptor, WanaCrypt0r and Wana Decrypt0r. The name comes after the .WNCRY file extension which is appended to the target files as soon as virus encrypts them. The news broke out about ransomware on May 12, after the Spanish telecommunications company called “Telefonica” reported encountering a cyber threat which demands money.[1] Soon afterward, several hospitals in the Great Britain reported about “Ooops, your files have been encrypted!” alert found on their computers' desktops. Japanese company ”Hitachi”, telecom of Portugal, Renault, FedEx, German train operator Deutsche Bahn AG are also among those that found @Please Read Me@.txt, @WanaDecryptor@.exe, and other files of WNCRY. The main targets are Windows OS users. At the moment, there are more than 230 000 infected computers and digital equipment. By the end of the week, more than 150 countries reported of encountering WNCRY virus. The popularity of this ransomware hides in the EternalBlue vulnerability, specifically, CVE-2017-0145, found in Windows OS devices.[2] The news about this flaw leaked together with the NSA plan to launch cyber attacks against Windows users. Thus, the malware targets all devices with this operating system starting from Windows XP[3]. However, leaked tool would certainly encourage the hackers to improve their malware and launch the second wave of the attack. Luckily, at the moment, you can battle the virus only automatically. Remove .WNCRY virus without hesitation. Updated versions of FortectIntego orMalwarebytes might come in handy.
Perhaps WNCRY ransomware-computer worm did not take place if not for the major leak of National Security Agency developed hack tool. Using Windows OS system vulnerability, named EternalBlue, NSA crafted a hack tool. The attack succeeds when a corrupted package is transmitted to one of SMBv1 servers. Nonetheless, it did not take too long for it to get stolen by Shadow Brokers[4]. Thus, this exploit became a goldmine. According to recent reports, the number of infected users is rapidly growing despite the reports about terminated attack. One of the key features of this menace is worm-like features, which enable the virus to infect all devices within the same network. The malware targets all countries without excluding any in particular[5].
Furthermore, the malware is known to use a “mutex” – mutual exclusion object. This element enables several programs or commands to share the same source. Thus, this feature enables the virus to function properly even in offline mode and infect other devices detectable in the same network. It has been observed that the malware employs Global\\MsWinZonesCacheCounterMutexA0 mutex[6]. At the same time, this feature grants the ransomware to detect whether the company is not infected with the virus to avoid disturbance among several versions of the same threat. After the encryption process is finished, it launches the program called WannaCryDecrypter and starts counting down the time. Observing the tendency of similar hackers, subsequent versions of the former threat might be expected in the future. In order to attempt and complete .WNCRY virus removal, it is crucial to know how it spreads. 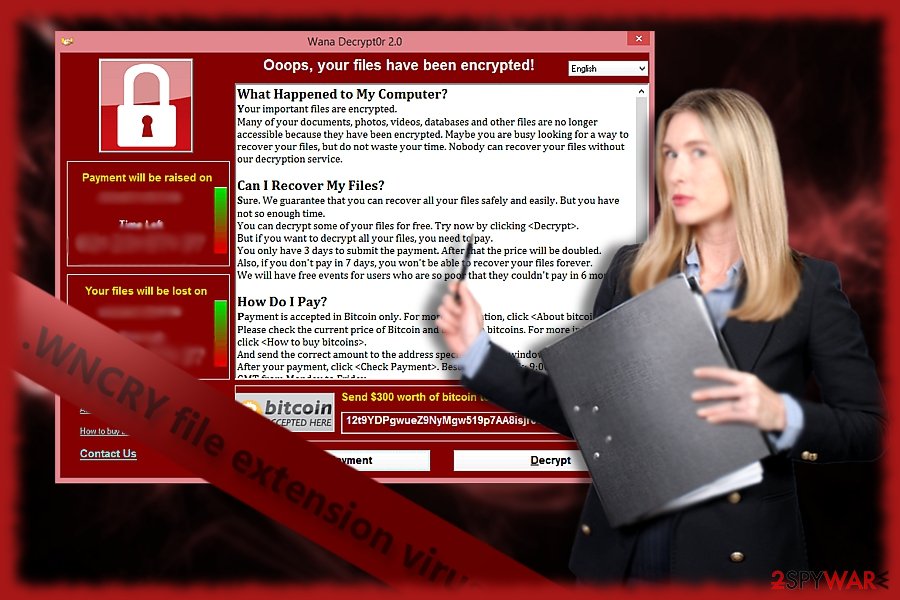
The peculiar distribution campaign of the malware
In comparison with the crypto-malware which is distributed via corrupted spam emails, WNCRY virus is on a new level. In the former case, the malware has few chances to infiltrate computers if users simply ignore the email with embedded macro settings or infected attached file. However, in this case, the malware exploits a vulnerability in Windows OS operating systems which creates a backdoor. Therefore, the malware enters through this flaw and paralyzes the PC by encrypting files. Likewise, the infiltration process is complete. Later on, victims are demanded to pay 300 USD in exchange for their affected data. Needless to say, the chances that you will receive the files even after remitting the payment are low. Since the malware has managed to corrupt thousands of the computers worldwide, the decryption process simply might be interrupted due to the challenge to manage such number of infected users. Certainly, WNCRY file virus cyber campaign is monitored by a wide network of botnets. This fact sparks that perhaps developers of Cerber or Locky “shared” knowledge and joined forces to multiply the scale of the assault. Since the malware possesses a huge potential, a series of SMB exploit kits are suspected to come in handy in further development stages of this malware. At the moment, the viable way to escape this WCRY is to update the operating system to fix the flaw.
.WNCRY virus elimination guide
If you delay installing Microsoft updates right after they are issued, no anti-virus will help you escape this cyber menace. Check your update history to see whether all updates are successfully installed. In addition, create backup copies in order to avoid devastating outcomes when encountering malware. In case, the virus already occupied your device, launch the PC into Safe Mode and run a computer security application to remove .WNCRY virus. If you are not sure how to do it, follow the instructions below. Note that only after WNCRY removal is completed, you may attempt data recovery. While there is no official decryption tool released yet, be careful not to install the one offered by the hackers.
Getting rid of .WNCRY virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove .WNCRY using System Restore
You may opt for the second method to regain access to the computer.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of .WNCRY. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove .WNCRY from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by .WNCRY, you can use several methods to restore them:
Data Recovery Pro
Regarding the complexity of this threat, this program may not decrypt all files affected by WNCRY virus, but it is still worth a try.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by .WNCRY ransomware;
- Restore them.
The benefits of ShadowExpplorer
Since the malware is still under analysis, there are high chances that it deletes shadow volume copies. In order not to pay the ransom, you may try this method as well. However, in this case time is crucial.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from .WNCRY and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Nicole Perlroth and David E. Sanger. Hackers Hit Dozens of Countries Exploiting Stolen N.S.A. Tool. The New York Times.
- ^ msft-mmpc. WannaCrypt ransomware worm targets out-of-date systems. Microsoft. Windows Security News.
- ^ Thomas Fox-Brewster. Microsoft Just Took A Swipe At NSA Over The WannaCry Ransomware Nightma. Fortune. Entertainment, Security, Politics, Finance.
- ^ WannaCry ransomware used in widespread attacks all over the world. SecureList. Information about viruses, hackers and spam.
- ^ Past 24 hours WannaCry infection map. Cyberwar. Live UA Map.
- ^ Didier Stevens. Quickpost: WannaCry’s Mutex Is MsWinZonesCacheCounterMutexA0 (Digit Zero At The End). Didier Stevens blog.





















