“Possible Suspicious Activity” virus (Removal Guide) - Oct 2017 update
“Possible Suspicious Activity” virus Removal Guide
What is “Possible Suspicious Activity” virus?
“Possible Suspicious Activity” alerts come from tech support scammers
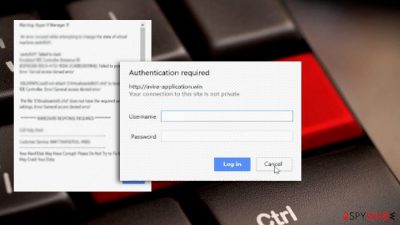
“Possible Suspicious Activity” virus defines a browser-based tech support scam. It is universal as it plagues Chrome, Internet Explorer, Firefox, and Microsoft Edge. This sample of scam is more elaborate. Unlike the majority of online deceptions which terrify users with Zeus virus and Facebook login as well as email account log-in data theft, this time, the crooks tied in more technical details to make the scam more realistic.
When users get redirected to a scam site, first of all, the message pops up stating that:
Customer, your system has detected possible suspicious activity. Please call the toll-free number below for a Microsoft Certified technician to help your resolve the issue:
For your safety, please of not open Internet browser to avoid data corruption to the registry of your operating system.
(…)CONTACT MICROSOFT CERTIFIED TECHNICIANS TO RESOLVE THE ISSUE CALLING TOLL FREE 8447756410.
A couple of other alerts follow the latter. The next is called “Warning! Hyper-V Manager.” The very program, Hyper-V Manager, is a virtualization platform introduced by Microsoft in 2008.[1]
Thus, the racketeers loaded a few definition of real programs to persuade users. Though they crowd the pop-up alert with technical details and definitions, the key thing which reveals the origin of the scam is the phone number.
Despite how realistic the scam might seem, if it includes the phone number or an email address, exit the page and clean the browser. The majority of browser-based tech scams are not destructive.
Claims that your data will be corrupted or lost are just lies. However, some online deceptions may temporarily hijack your browser. Thus, clicking on the button “Prevent this page from creating additional dialogues” may not work.
You will need to force shut-down on the browser. In addition, it is recommended to remove “Possible Suspicious Activity” scripts from the browser. You can do so with the assistance of FortectIntego or Malwarebytes.
October 2017: “Antivirus Detected Some Suspicious Activity” virus starts spreading online
On October 30th, researchers discovered a brand new scam using “Antivirus Detected Some Suspicious Activity” line to trick unsuspecting users into calling fraudsters via provided “toll-free” number. This time, scammers suggest dialing +1-844-665-6888 number for help directly from “Microsoft Technicians.” Calling the fraudsters won't help to resolve the imaginary issue that the deceptive alert warns you about.
Scammers will simply ask you to follow their commands that can eventually result in data loss or a severe computer infection. The pop-up typically appears on pages that look like Microsoft's Support page or another related site because it is filled with forged company's logos all over. Do not let these cheap tricks fool you and convince you to call scammers. Otherwise, you might end up giving them remote access logins or credit card details to people who will use such data for illegal purposes.
Remove “Antivirus Detected Some Suspicious Activity” virus as soon as you can and make these fake alerts disappear once and for good. You can detect the malware sending you these pop-ups using anti-malware or anti-spyware programs that we mentioned earlier.
Keep your computer safe and learn to identify tech support scams
Browser-based tech support scams scripts might be foisted in a variety of websites. Observing the tendency, most likely, you could get directed to such scam when you browse illegal movie streaming sites or torrent sharing domains.
Likewise, “Possible Suspicious Activity” hijack might have occurred as a result of such technique. On the other hand, even if you are cautious, a tech support page might appear if you click on a legitimate ad or banner.[2]
Note that you should be wary of corrupted apps and extensions. They might be a harbinger of a PC version of a tech support scam. The latter cause more elimination troubles. Now let us review “Possible Suspicious Activity” scam removal options. 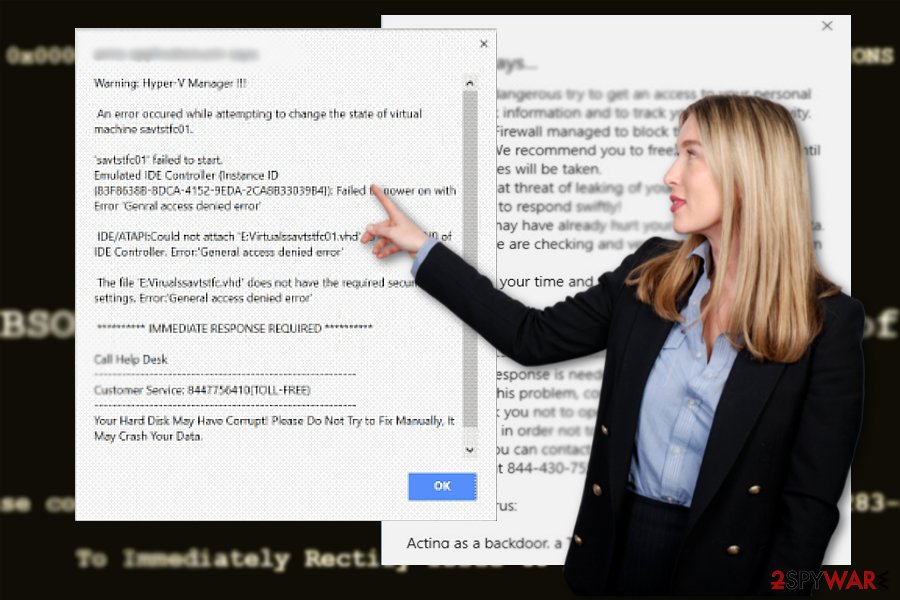
Remove Possible Suspicious Activity virus with ease
First of all, you need to exit the tech support scam site. Click on CTRL+SHIFT+ESC. Find your browser commands in the Task Manager, right-click on them and then choose “End task.”
Now restart the browser. Enter the Settings and clear cookies as well browsing data. In case the redirect page still emerges, reset the browser to remove “Possible Suspicious Activity” virus elements.
It is also advised to scan the browser. The tool will complete “Possible Suspicious Activity” removal procedure. This scam might appear not only in English but in French, Hungarian or Estonian[3] sites.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of “Possible Suspicious Activity” virus. Follow these steps
Uninstall from Windows
Instructions for Windows 10/8 machines:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

If you are Windows 7/XP user, proceed with the following instructions:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Delete from macOS
Mac OS users should be wary of “Possible Suspicious Activity” scam types. Theey might be targeted with the iOS counterparts of this felony.
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Microsoft Edge
Delete unwanted extensions from MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Clear cookies and other browser data:
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Restore new tab and homepage settings:
- Click the menu icon and choose Settings.
- Then find On startup section.
- Click Disable if you found any suspicious domain.
Reset MS Edge if the above steps did not work:
- Press on Ctrl + Shift + Esc to open Task Manager.
- Click on More details arrow at the bottom of the window.
- Select Details tab.
- Now scroll down and locate every entry with Microsoft Edge name in it. Right-click on each of them and select End Task to stop MS Edge from running.

If this solution failed to help you, you need to use an advanced Edge reset method. Note that you need to backup your data before proceeding.
- Find the following folder on your computer: C:\\Users\\%username%\\AppData\\Local\\Packages\\Microsoft.MicrosoftEdge_8wekyb3d8bbwe.
- Press Ctrl + A on your keyboard to select all folders.
- Right-click on them and pick Delete

- Now right-click on the Start button and pick Windows PowerShell (Admin).
- When the new window opens, copy and paste the following command, and then press Enter:
Get-AppXPackage -AllUsers -Name Microsoft.MicrosoftEdge | Foreach {Add-AppxPackage -DisableDevelopmentMode -Register “$($_.InstallLocation)\\AppXManifest.xml” -Verbose

Instructions for Chromium-based Edge
Delete extensions from MS Edge (Chromium):
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Clear cache and site data:
- Click on Menu and go to Settings.
- Select Privacy, search and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Reset Chromium-based MS Edge:
- Click on Menu and select Settings.
- On the left side, pick Reset settings.
- Select Restore settings to their default values.
- Confirm with Reset.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of “Possible Suspicious Activity” registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Andrew Zhelezko. What is Hyper-V technology?. Veeam. Veeam backup and Replication.
- ^ David Bisson. Taboola ads exploited to serve up tech support scams. GrahamCluley. Award-wining cyber security news, advice and opinion.
- ^ Eliminate computer threats. Virused. Cyber security news in Estonian.























