PRISM virus (Removal Instructions) - Jul 2019 update
PRISM virus Removal Guide
What is PRISM virus?
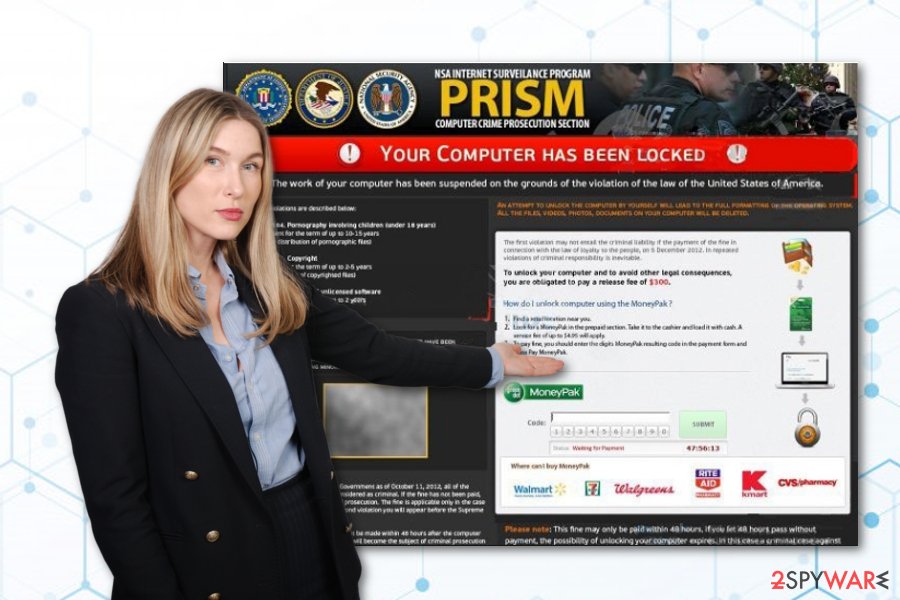
PRISM virus – a fine-demanding threat that pretends to be from the Computer Crime Prosecution Section

PRISM virus is a money-demanding malware that accuses users of violating the USA laws. This virus works as a scam, however, it also has earned the name of PRISM ransomware as its roots appear to come from Reveton trojan family. The scamming message presents false claims about illegitimate copyright, software usage, and children pornography activities. As a way to avoid prosecution is to transfer a fine of $300 via MoneyPak[1] in the 48 hours period. According to the message, paying such amount of money will also allow you to regain screen access.
| Name | PRISM virus |
|---|---|
| Type | Scam/ransom-demanding virus |
| Family | Reveton ransomware |
| Delivery | Exploit kits, unsecured pages, spam messages |
| Aim | To gather money from gullible victims |
| “Crimes” | Users are falsely accused of violating the USA laws by distributing pornography content, misusing copywriting texts, and using unlicensed products |
| Fine | Crooks urge payment of $300 to avoid prosecution |
| Payment conditions | The money needs to be transferred via MoneyPak in 48 hours |
| Similar malware | Metropolitan Police virus |
| Detection tool | After booting your computer in Safe Mode with Networking, we suggest using software such as FortectIntego to scan the entire system and search for possible relations to malware |
Believes in PRISM virus and its provided message will bring you only monetary losses as no NSA Internet Surveillance Program would report about illegitimate activities and penalties through these types of notifications. Additionally, try not to get tricked by the National Security Agency and similar logos that are here just to create a legitimate look.
PRISM MoneyPak ransom will cover your entire computer screen with its rogue message. Besides, this malware will supposedly identify your location and display a website that suits it. Nevertheless, the scam notification might also be written in different languages depending on the discovered location of the user. The English text looks like this:
NSA Internet Surveillance Program.
PRISM.
Computer Crime Prosecution Section.Your Computer has been locked!
Your computer has been locked due to suspicions of illegal content downloading and distribution.
Your case can be classified as occasional/unmotivated, according to 17 (U.S Code)
Thus it may be closed without prosecution.
Your computer will be unblocked automatically.In order to resolve the situation in an above-mentioned way you should pay a fine of $300 (MoneyPak)
PRISM virus is very similar to another similar scam named Metropolitan Police virus. This previous malware also presents itself to be from a law institution and accuses users of violating some laws by using pornography-related content that involves children. DO NOT believe in any of these claims as hackers are trying to gain benefit from you.
Besides just locking the screen, PRISM virus can disable various Windows functions to avoid detection and elimination. This allows the message to be displayed for a longer period of time and it has better chances of convincing users. Also, it is known that mostly these types of scams travel via exploit kits,[2] email spam, and third-party networks.
If you have found PRISM virus on your computer and it has prevented you from accessing your computer screen, you should boot your system in Safe Mode with Networking to disable any malicious ongoing processes. This should help you to get rid of the lock screen and will ease the termination process of the scam and any additional threats.
Before PRISM virus removal, you need to perform a thorough system check-up with a program such as FortectIntego. Once the scan is done, you will be able to see possibly-infected sources and all additional malicious components that might have come together with the scam. Once results are investigated, you can take actions toward the elimination process.
Our suggestion would be to remove PRISM virus with the help of anti-malware software as the automatical technique will provide you with a safer and more effective process. Besides, by trying to remove the cyber threat on your own, you might complete some crucial mistakes that can provoke a hard system or software damage.
Remember, DO NOT pay any ransom to the criminals as you will definitely be left scammed. DO NOT fall for believing in PRISM virus provided threatenings about imprisonment that is claimed to take up to 10-15 years for crimes involving pornography and 2-5 years as a penalty for misusing copyrighting rights and carrying tasks with unlicensed software.

Malware distribution sources and avoiding tips
IT technology experts from SenzaVirus.it website[3] have done intense research and found out that malicious scams, ransomware, trojans, and other malware are capable of reaching the system in different ways. However, the most popular ones are spam messages, exploit kits, infected hyperlinks, and outdated software.
The key to full computer security is the user's own cautiousness when carrying out browsing actions and computing work. First of all, you need to ensure that the websites you are visiting are safe for exploring and usage. Secondly, you should regularly update all of your software, including antivirus programs that are also crucial for system protection.
Furthermore, you should carefully manage all of your email messages. We suggest not to open any that fall in the “spam” section and send them straight to trash. Also, always identify the sender and do not access/download any attachments that have a questionable look. Better scan them with anti-malware and see what the check-up results say.
Complete the following to get rid of PRISM virus
PRISM virus might be provoked to appear on the Windows computer system by a Trojan horse[4] or similar malware. If you have been receiving a particular scam lately, note that almost in every situation there is some type of threat behind the rogue message's delivery. This malicious content needs to be eliminated together with the virus itself.
What you need to do is choose a malware detection tool and scan the entire computer system for infection signs. You can pick from these three: FortectIntego, SpyHunter 5Combo Cleaner, Malwarebytes. Once the check-up is done, you will be able to remove PRISM virus safely and successfully by cleaning all infected directories in your system.
Be careful and use only reputable tools for PRISM virus removal. Manual elimination for this threat and its “friends” is not a possibility in this case as malware might be hiding anywhere and hard to detect. Besides, trustworthy anti-malware will complete the process more effectively than a human being would be able to.
Getting rid of PRISM virus. Follow these steps
Manual removal using Safe Mode
Activate the Safe Mode with Networking feature and disable malicious processes on your Windows computer:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove PRISM using System Restore
Use the System Restore function to deactivate PRISM ransomware on your machine:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of PRISM. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from PRISM and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting malware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ MoneyPak. Bitcoin Wiki. Relevant info.
- ^ WHAT IS AN EXPLOIT KIT?. Palo Alto Networks.
- ^ LE NOVITÀ SU SICUREZZA E SPYWARE. SenzaVirus.it. Malware news.
- ^ What is a Trojan Virus?. Kaspersky. Resource center.







