Pywdu ransomware (Virus Removal Instructions) - Bonus: Decryption Steps
Pywdu virus Removal Guide
What is Pywdu ransomware?
Pywdu is a newly released member of the gradually expanding Snatch ransomware family
Pywdu ransomware is malware, which manifested at the end of June 2020. According to cybersecurity researchers, it belongs to the Snatch ransomware family, which has initially emerged back in 2018 and reproduced several deadly dangerous versions, including .FileSlack, .jupstb, .EGMWV, and others.
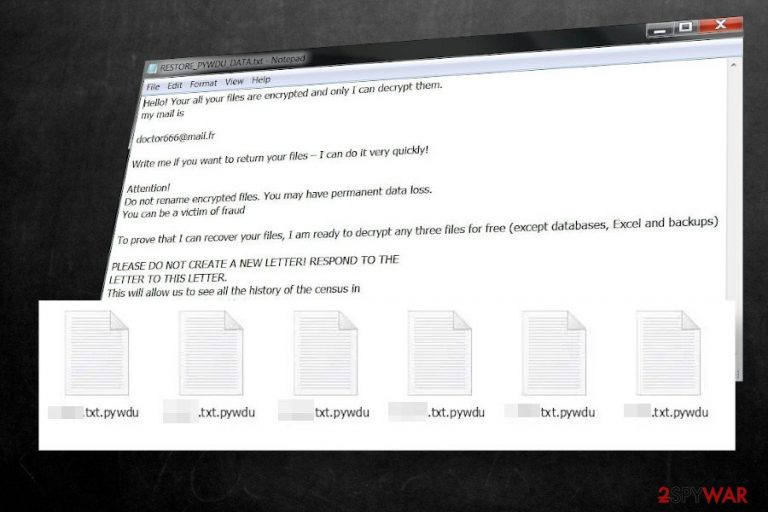
The Pywdu ransomware uses targeted spam email campaigns with an intention to attack corporations in particular, though it can end up on home users' PCs as well. Upon infiltration, it uses the AES encryption[1] algorithm to lock data on the targeted PC, which subsequently gets the .pywdu file extension (e.g. mydocument.docs.pywdu).
The attackers drop a ransom note RESTORE_PYWDU_DATA.txt on the desktop and demand victims to contact them via doctor666@mail.fr for further instructions. To prove gain victim's trust, crooks claim to restore three files for free, while the rest of the data will be recovered after paying the ransom. Unfortunately, the size of the redemption is not specified, though experts presume that the Pywdu virus developers set up the price depending on how many files have been locked.
| Name | Pywdu |
| Class | Ransomware / file-locking virus |
| Family | Snatch ransomware |
| File extension | The virus locks files by appending the .pywdu extension |
| Ransom note | RESTORE_PYWDU_DATA.txt |
| Encryption model | Based on its ancestors, the ransomware is likely to render AES-256 encryption algorithm |
| Contacts | doctor666@mail.fr |
| Distribution | The main dissemination technique – targeted spam email messages. However, it can also be distributed via software cracks, keygens, and unprotected RPDs |
| Decryption | Experts haven't yet developed a functional Pywdu decryptor. Therefore, you should either pay the ransom (not recommended), use backups or try alternative data recovery methods, such as Volume Shadow Copies |
| Ransomware removal | The only way to eliminate the package of the malicious files that comprise the Pywdu file virus is to use a professional anti-virus |
| This ransomware is capable of stopping important Windows processes, altering boot sequence, and creating malicious Windows registries. These changes are not restored during the virus removal. Thus, try to repait system damage with FortectIntego tool | |
There's no precise information on how Pywdu ransomware spreads. However, based on the previous variants of this ransomware and ransomware practice, in general, the following means are most likely to be used:
- Targeted spam emails (contain malicious attachment or hyperlink);
- Exploits;
- Pirated software, keygens, cracks;
- Fake software updates (mimicking Windows software updates, Flash Player updates, etc.);
- Backdoors (can be downloaded as a secondary payload via Trojans), etc.
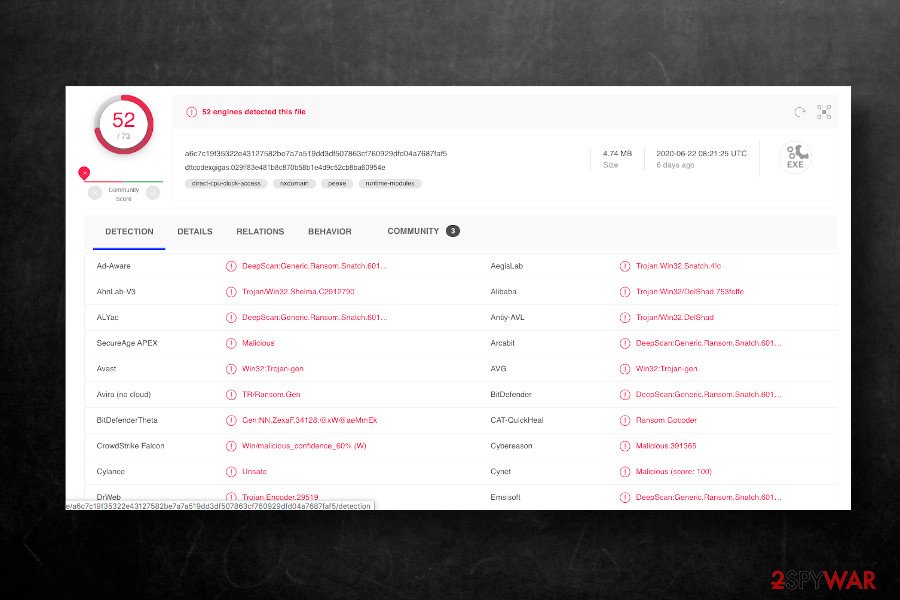
Upon the installation, the Pywdu virus stops several Windows processes, injects malicious files in the list of startup programs, and starts running malicious entries, the most active of which is dttcodexgigas.029ff83e481b8c870b58b1e4d9c52cb8ba60954e[2]. This particular processes initiates the following commands via an elevated PowerShell:
- vssadmin delete shadows /all /quiet
- sc queryex type= service
It means that the .pywdu file virus disabled Volume Shadow Copies, thus preventing the user from retrieving the locked files without paying the ransom (unless the victim has backups). After all malicious commands are executed, the virus runs a cipher to locked all personal data obtained on the infected machine. According to experts, the ransomware can encrypt the following file types:
.7z, .rar, .m4a, .wma, .avi, .wmv, .csv, .d3dbsp, .sc2save, .sie, .sum, .ibank, .t13, .t12, .qdf, .gdb, .tax, .pkpass, .bc6, .bc7, .bkp, .qic, .bkf, .sidn, .sidd, .mddata, .itl, .itdb, .icxs, .hvpl, .hplg, .hkdb, .mdbackup, .syncdb, .gho, .cas, .svg, .map, .wmo, .itm, .sb, .fos, .mcgame, .vdf, .ztmp, .sis, .sid, .ncf, .menu, .layout, .dmp, .blob, .esm,. 001, .vtf, .dazip, .fpk, .mlx, .kf, .iwd, .vpk, .tor, .psk, .rim, .w3x, .fsh, .ntl, .arch00, .lvl, .snx, .cfr, .ff, .vpp_pc, .lrf, .m2, .mcmeta, .vfs0, .mpqge, .kdb, .db0, .DayZProfile, .rofl, .hkx, .bar, .upk, .das, .iwi, .litemod, .asset, .forge, .ltx, .bsa, .apk, .re4, .sav, .lbf, .slm, .bik, .epk, .rgss3a, .pak, .big, .unity3d, .wotreplay, .xxx, .desc, .py, .m3u, .flv, .js, .css, .rb, .png, .jpeg, .txt, .p7c;
.p7b, .p12, .pfx, .pem, .crt, .cer, .der, .x3f, .srw, .pef, .ptx, .r3d, .rw2, .rwl, .raw, .raf, .orf, .nrw, .mrwref, .mef, .erf, .kdc, .dcr, .cr2, .crw, .bay, .sr2, .srf, .arw, .3fr, .dng, .jpe, .jpg, .cdr, .indd, .ai, .eps, .pdf, .pdd;
.psd, .dbfv, .mdf, .wb2, .rtf, .wpd, .dxg, .xf, .dwg, .pst, .accdb, .mdb, .pptm, .pptx, .ppt, .xlk, .xlsb, .xlsm;
.xlsx, .xls, .wps, .docm, .docx, .doc, .odb, .odc, .odm, .odp, .ods, .odt; (the list is not finite)
Upon file encryption, the victim can no longer access personal files and is blackmailed to purchase a decryption key to unlock .pywdu files. To inform the victim about the attack and awaited response, criminals leave a ransom note RESTORE_PYWDU_DATA.txt on the desktop, which shortly explains what has happened and demands to email them via doctor666@mail.fr.
Hello! Your all your files are encrypted and only I can decrypt them.
my mail is
doctor666@mail.fr
Write me if you want to return your files – I can do it very quickly!Attention!
Do not rename encrypted files. You may have permanent data loss.
You can be a victim of fraudTo prove that I can recover your files, I am ready to decrypt any three files for free (except databases, Excel and backups)
PLEASE DO NOT CREATE A NEW LETTER! RESPOND TO THE
LETTER TO THIS LETTER.
This will allow us to see all the history of the census in
one place and respond quickly to you.hurry up!
Those who have received the above-shown ransom note are strongly recommended not to lose once's minds. The ransomware is dangerous and can cost permanent file loss. However, we strongly recommend weighing all pros and cons before paying. Think twice whether the data that has been locked is worth hundreds of dollars and an affair with cybercriminals.
At best, you should immediately copy the encrypted files into an alternative data storage and remove Pywdu ransomware virus from the machine. For this purpose, you should restart the system into Safe Mode (the virus may block the processes of anti-virus programs) and run a robust anti-virus program.
Pywdu virus removal will not recover the encrypted data, as well as not recover the settings of the Windows OS. Therefore, you should try alternative data recovery methods (listed at the end of this article) and optimize the system with FortectIntego repair tool.
Ransomware is usually distributed via spam emails and pirated software
Ransomware is a type of virus that tops the charts of the most dangerous cyber infections. If it gets installed, the victim is endangered to lose personal files, money, or both. Therefore, experts keep warning Internet users about the most common ransomware distribution techniques to help people stay safe.
Unfortunately, criminals are too inventive and sophisticated to find out various means tricking people into accidentally running malicious files that carry ransomware. The prevailing technique, and still most successful, is malicious attachments appended to spam email messages.
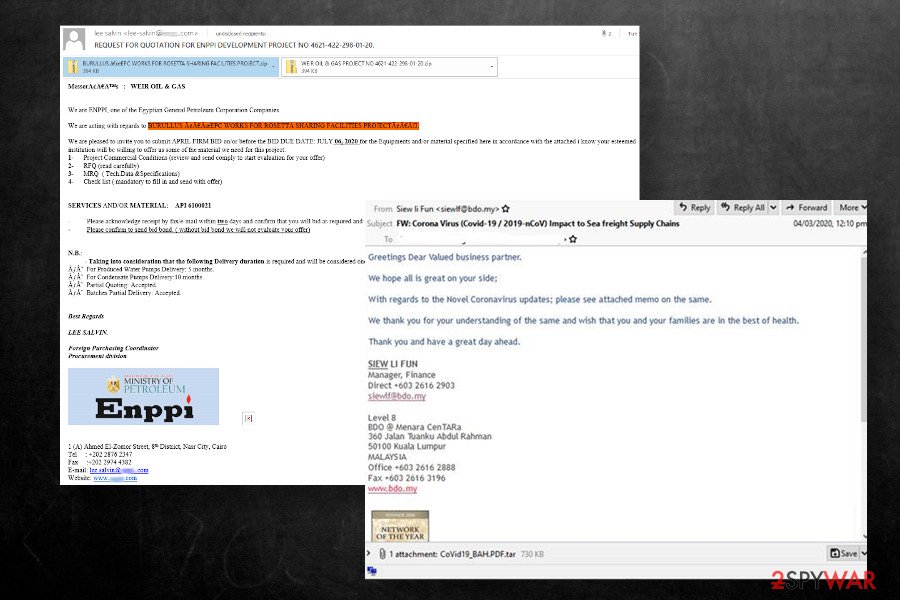
Apart from malspam, ransomware can be activated via software cracks, keygens, and other pirated content. Therefore, it's crucial to take precautionary measures to stay away from dangerous content. Dieviren.de[3] experts have excluded the basic precautionary measures that each user should mind:
- Download and use a robust anti-virus solution. At best, use the whole package of security software to ensure the highest protection level;
- Regularly install software updates, OS updates, and patch vulnerabilities
- Investigate every email before opening its attachments. Even if you received a message asking to confirm the order or check something, it doesn't mean that you can open the .doc, .pdf, .htm, or another type of attachment. Double-check the sender, look for grammar/type mistakes, and other hooks showing the email to be spam. You can also scan the attachment with an anti-virus tool if it has scan to e-mail function
- Use a strong password and VPN when using Remote Desktop Protocol;
- Stay away from dangerous websites (porn, gambling, P2P, torrent, etc.)
Delete Pywdu ransomware before trying to recover locked data
Indeed, finding all files encrypted by the .pywdu file virus is shocking and most of the users consider paying the ransom. Probably, paying the ransom seems to be the sole solution for those who keep important work files and archives on the system, family photos, and other documents and do not regularly make backups.
If you have backups on external hard drive or cloud, you have nothing to worry about. Remove Pywdu virus immediately using SpyHunter 5Combo Cleaner, Malwarebytes or alternative security tool, recovery the system with FortectIntego, and then recover .pywdu files from backups. If, however, you have no backups, we do not recommend paying criminals for their delinquent activities. Instead, eliminate the ransomware and try to recover data using alternative methods.
Unfortunately, Pywdu removal won't recover encrypted files. However, it is expected that experts will soon find a flaw in the ransomware file encryption model and generate a fully functional decryption tool. Therefore, we recommend copying locked files into the external storage, giving a try for third-party data recovery tools, and, in case of no luck, wait for a decryptor to be launched.
Getting rid of Pywdu virus. Follow these steps
Manual removal using Safe Mode
Since Pywdu virus may block security software, restart Windows into Safe Mode to run a scan.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Pywdu using System Restore
If Safe Mode failed to work, try the in-built System Restore feature.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Pywdu. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Pywdu from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.There's no functional Pywdu decryptor. Nevertheless, experts recommend trying third-party software for data recovery.
If your files are encrypted by Pywdu, you can use several methods to restore them:
Use Data Recovery Pro tool
Data Recovery Pro is a free tool for data recovery. It is usually used after system crash, though its powerful recovery engine may help to unlock at least some of the locked files.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Pywdu ransomware;
- Restore them.
Windows Previous Versions Feature might be of use
If you enabled System Restore prior to the attack, Windows Previous Versions Feature might work when trying to restore .pywdu files.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Shadow explorer won't work
As we have pointed out, this ransomware enabled a file, which runs PowerShell commands to delete Volume Shadow copies. Therefore, this method won't work.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Pywdu decryptor is in the development phase.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Pywdu and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Tarcísio Marinho. Ransomware encryption techniques. Medium. Cybersecurity news.
- ^ dttcodexgigas.029ff83e481b8c870b58b1e4d9c52cb8ba60954e file analysis. VirusTotal. Free file and URL scanner.
- ^ SICHERHEIT- UND SPYWARE-NEUIGKEITEN. Dieviren. Virus and spyware news.







