“Windows Troubleshooting” scam (Virus Removal Guide) - Tutorial
“Windows Troubleshooting” scam Removal Guide
What is “Windows Troubleshooting” scam?
“Windows Troubleshooter” scam raises technical support scams to a brand new level
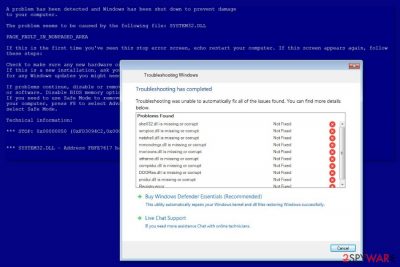
“Windows Troubleshooting” is a nasty example of technical support scam that spreads as cracked software installer. On the affected device it shows a fake Blue Screen of Death (BSOD)[1] and displays Troubleshooting Windows pop up that looks like legit Windows Troubleshooter. The purpose of the scam – to convince users into buying a fake Windows Defender Essentials program.
Typically tech support scam viruses ask to call fake support line in order to solve various problems, fix computer errors or clean cyber threats.[2] Users are often redirected to scam sites when browsing through insecure websites or after adware infiltration. However, “Windows Troubleshooting” support scam is different.
“Windows Troubleshooting” malware gets inside the system when user downloads and runs a particular cracked software installer. Once executed, malware alters Windows registry and downloads several files:
- csrvc.exe to kill Task Manager, Registry Editor, and Explorer.
- BSOD.exe to display a BSOD on the affected device.
- Troubleshoot.exe to deliver fake “Troubleshooting Windows” alert.
- Scshtrv.exe to upload a particular screenshot to the remote FTP server.
- adwizz.exe to display Banggood.com ads.
Therefore, it’s an advanced technical support scam that is capable of making changes to Windows operating system. Additionally, the malware takes screenshots of the active computer’s screen. The reason why does it is unknown. However, it uploads them to its remote FTP server located at 182.50.132.48.
This activity is highly suspicious and might lead to privacy-related issues. For this reason, victims should remove “Windows Troubleshooting” virus immediately with security software, such as FortectIntego.
Operation of the “Windows Troubleshooting” technical support scam
After the “Windows Troubleshooting” hijack, malware downloads previously mentioned files. The first to run is BSOD.exe which displays a fake Blue Screen of Death which says:
A problem has been detected and Windows has been shut down to prevent damage
to your computer.The problem seems to be caused by the following file: SYSTEM32.DLL
PAGE_FAULT_IN_NONPAGED_AREA.
The BSOD also gives instructions what users should do, such as restarting the computer, checking software and hardware. Additionally, you will hear an annoying beeping sound. However, this alert is followed by the appearance of fake “Windows Troubleshooting” window that delivers Error Code 0xc0000e9 and informs about missing .dll registry files:
Windows has encountered an unexpected error 0xc0000e9.
Your computer is missing .dll registry files resulting in computer failure.
The operating system is not able to load windows kernel files.
Repair windows kernel and .dll files with the help of technicians online to prevent hard drive crash or complete data loss. Rebooting the computer multiple times will result in permanent operating system failure.Click Next to diagnose and troubleshoot the problem.
Criminals promote Windows Defender Essentials program that is supposed to fix the problem. People have to pay $25 via PayPal, Debit or Credit card. However, it seems that they not only want to receive money from a fake program but obtain sensitive information, such as contact information or credit card details.
Clicking the “Next” button triggers a system scan. Once it’s over, victims will see a bunch of detected problems. In order to fix them, victims can either buy Windows Defender Essentials or contact Live Chat Support.
However, none of these options are good for “Windows Troubleshooting” removal. Chatting with fake support technicians won’t give any results. If you manage to reach them, they will find numerous reasons to make you obtain a phony software.
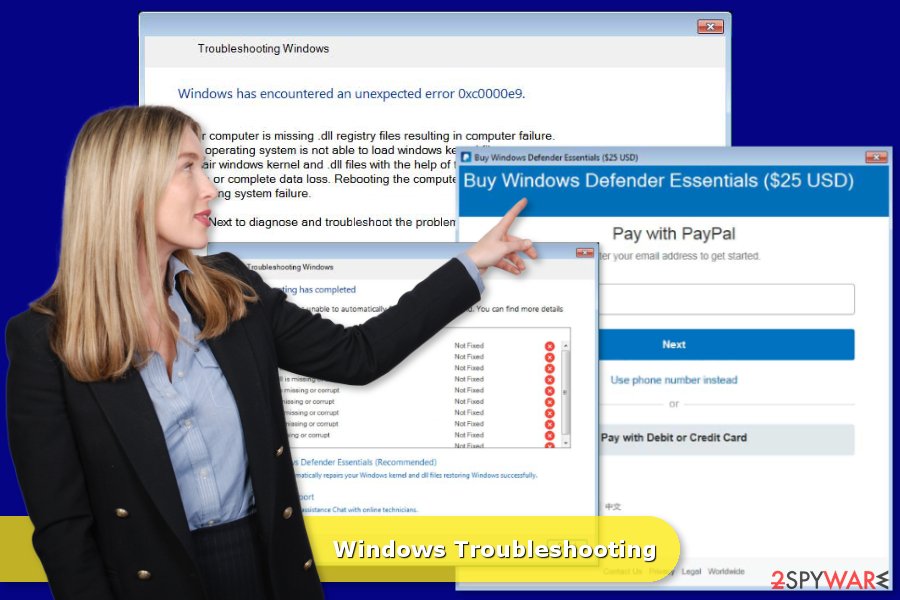
Windows Defender Essentials can fix fake errors
Clicking “Buy Windows Defender Essentials (Recommended)” option redirects to a PayPal page where users are asked to obtain the program for $25. As soon as the payment is made (not recommended), users are redirected to the http://hitechnovation.com/thankyou.txt website.
The one and the most important component of this site is “thankuhitechnovation” string which informs malware that the payment is made.
Meanwhile, the virus opens a new window that shows the process of fixing previously detected problems. Once it’s done, users can close the program and access their computers.
However, bypassing the lock screen in this way is not recommended. There’s a way to workaround this trickery, but before giving you instructions, we want to introduce tips to avoid such cyber threats in the future.
Malware spreads as a fake program
“Windows Troubleshooter” scam spreads as a cracked program. Security experts from Les Virus[3] note that installation of illegal programs usually leads to malware attack. Therefore, you should always use legit download sources and pay for the license. Also, you should never:
- download and install cracked software;
- install updates from pop-ups;
- install programs or updates from unknown third-party websites, torrents or other P2P networks.
Additionally, if you install freeware or shareware, you have to use Advanced/Custom installation settings instead of Quick/Recommended. This setup allows adjusting installation process and rejecting infiltration of potentially unwanted programs.
Remove “Windows Troubleshooting” scam
The first step of “Troubleshooting Windows” removal is to bypass the lock screen. Malware uses an easily breakable mechanism to check if a victim made a payment or not. However, you can easily workaround this problem by following these steps:
- Enter fake PayPal purchase screen.
- Click Ctrl + O keys to launch Open dialog box.
- Enter http://hitechnovation.com/thankyou.txt into Open box.
That’s all. You should be able to close the window and access your computer. However, “Windows Troubleshooting” removal is not over. You have to find and uninstall a malicious program from the computer that brought technical support scam to your device.
Even though you can uninstall the program manually, this cyber threat installed several executables and modified the system. Thus, fixing the computer is hard and difficult. In order to succeed and avoid possible damage, you should remove “Windows Troubleshooting” automatically using FortectIntego, Malwarebytes or other malware removal tools.
Getting rid of “Windows Troubleshooting” scam. Follow these steps
Manual removal using Safe Mode
If you cannot install or run malware removal software once you bypassed the lock screen, you should follow these steps. Rebooting to Safe Mode with Networking might solve the problem.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove “Windows Troubleshooting” scam using System Restore
If the previous method did not work, try System Restore. Then you should be able to activate automatic “Windows Troubleshooting” scam removal.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of “Windows Troubleshooting” scam. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from “Windows Troubleshooting” scam and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting malware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Blue Screen of Death. Wikipedia. The free encyclopedia.
- ^ Tech support scams. Microsoft. The official website.
- ^ Les Virus. Les Virus. Cyber security news and malware database.





















