Zwer ransomware (Virus Removal Guide) - Free Instructions
Zwer virus Removal Guide
What is Zwer ransomware?
Zwer ransomware – malicious program designed for money extortion
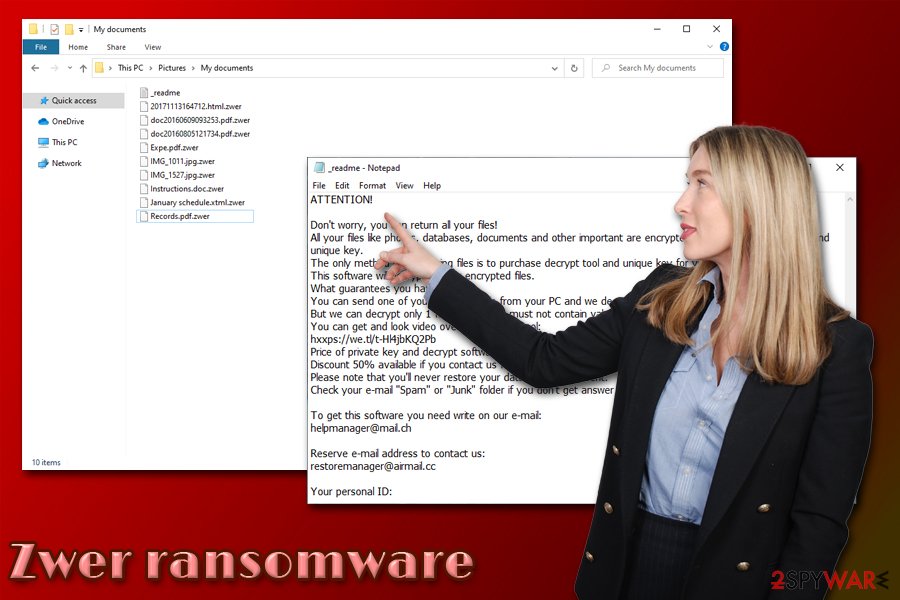
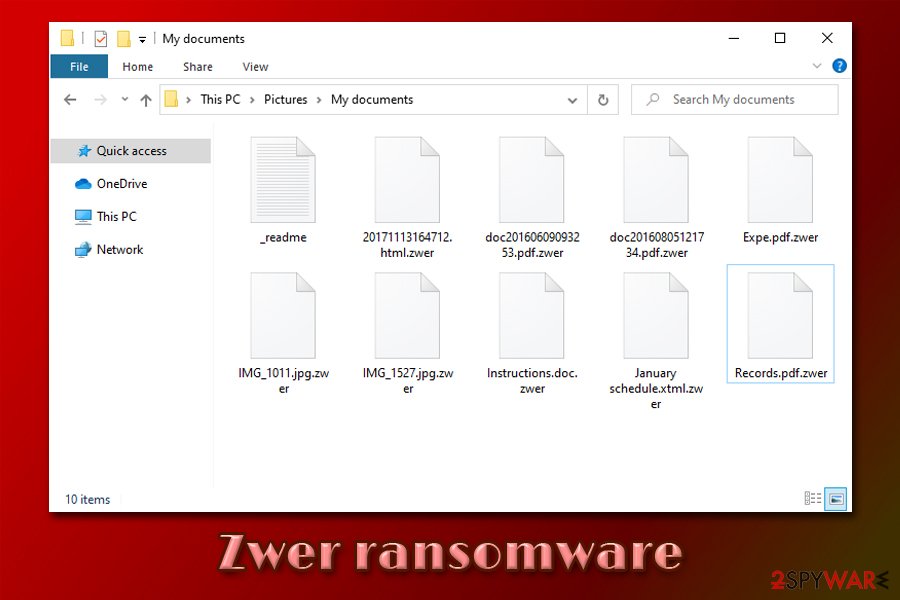
Zwer ransomware is a data locking malware that was developed by sophisticated hackers and is a variant of a malware family known as Djvu. The virus almost exclusively spreads via software cracks and is one of the most popular malware of such type, which targets regular consumers. The main purpose of the infection is to encrypt all music, video, document, picture, and other personal files by appending .zwer extension and preventing access to them.
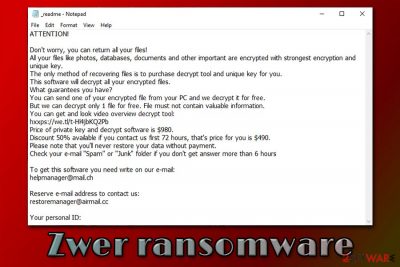
After the data locking process is complete, Zwer ransomware drops a ransom note called _readme.txt – this file serves as a direct message from the attackers. Inside the note, criminals claim that victims need to pay $490 in Bitcoin in order to recover a unique RSA[1] key to unlock files. For communication purposes, the attackers provide two emails – helpmanager@mail.ch and restoremanager@airmail.cc.
However, paying criminals is not recommended. There is a chance that Emsisoft's decryptor might be able to help you restore .zwer encrypted files, although it is only possible if ransomware used an offline ID to lock the data.
| Name | Zwer ransomware |
| Type | File locking virus, crypto-malware |
| Malware family | STOP/Djvu |
| Related files | b71d.tmp.exe |
| Detection |
One of the malicious executables that initiate the infection is detected as follows on Virus Total:
|
| Infection means | Most of Djvu variants are spread via software cracks or pirated program installers downloaded from third-party sources (torrents) |
| File extension | All non-system and non-executable files are appended with .zwer extension. Example of encrypted file: picture.jpg.zwer |
| Ransom note | _readme.txt is delivered into each folders with encrypted files |
| Features | Encrypts all files on the system; modifies Windows hosts file to prevent users' access to security-focused websites; injects data-stealing module into web browsers; |
| Malware removal | The best way to eliminate the infection is by scanning the computer with powerful security software, such as SpyHunter 5Combo Cleaner or Malwarebytes. Note: you will not be able to open .zwer files after you delete the infection from your computer, as a unique key is required for that |
| System fix | In case your Windows machine begins to crash or display errors after you get rid of the infection, scan it with PC repair software FortectIntego – it might eliminate virus damage and prevent the reinstallation of the operating system |
| Data recovery | The only secure and 100% effective method to restore .zwer files is by using backups. However, some users might be able to restore files by using Emsisoft's decryption tool. Additionally, in rare cases, third-party recovery software might be able to help – check for download links and usage instructions below |
Djvu/STOP malware family that the Zwer file virus belongs to is one of the most extensive ones, and so far, over 230 versions were released. Despite this, .kkll, .nlah, .pezi, .covm, and other variants do not differ much, although the attackers tend to use different contact emails for communication purposes most of the time.
Nonetheless, the ransom note _readme.txt is almost identical, and delivers the following information:
ATTENTION!
Don't worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
hxxps://we.tl/t-Hl4jbKQ2Pb
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that's price for you is $490.
Please note that you'll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don't get answer more than 6 hoursTo get this software you need write on our e-mail:
helpmanager@mail.chReserve e-mail address to contact us:
restoremanager@airmail.ccYour personal ID:
Initially, the attackers are asking for $980 for the Zwer ransomware decryptor, although they promise a 50% discount ($490) if the contact is made within 72 hours of the infection. Besides, they also offer to decipher one file that does not include sensitive information. These are all tricks that are meant to create a fake sense of trust about attackers' intentions and make users pay for the Zwer virus file recovery tool. Despite this, there is no guarantee that the attackers will send the unique key, as they might simply scam you by taking the money. The decryption tool might also fail to work in the first place.
While many malware of such type eliminate itself after the data locking process is complete, you should still remove Zwer ransomware with a reputable anti-malware software and only then attempt to recover your files. For malware termination, employ powerful security applications, and then scan the computer with FortectIntego PC repair program to avoid the Windows OS reinstallation.
Zwer ransomware could install the data-stealing module on your machine
Once the malicious file such as b71d.tmp.exe is executed on a Windows machine, it will execute a series of system changes in order to perform a successful file encryption process. For that, the malware creates subfolders inside %AppData%, %User% or %Temp% folder, and then populates malicious files all over the operating system.
After that, Zwer ransomware performs the following changes:
- Deletes Shadow Volume Copies to prevent a quick file recovery
- Opens and modifies Windows registry[2] keys in order to launch with each system boot;
- Creases new and terminates some vital processes;
- Modifies Windows hosts file to prevent users from accessing security-related websites and seeking help with decryption;
- Injects a data-stealing module into the web browsers (this feature is especially dangerous, as sensitive information such as credit card details could be stolen by the attackers if Zwer ransomware removal is not performed on time).
As soon as the compromised machine is ready, Zwer ransomware initiates file encryption process which targets the most commonly used types, such as PDF, MS Office, text, archive, and other files. During this development, malware is programmed to deliver users fake Windows update pop-up, as it misleads victims to believe that it is real.
However, as soon as the encryption is finished, users then notice that none of the personal files can be opened anymore, and the ransom note is present on the system, explaining that they have to pay for data recovery.
You can't open .zwer files: here's what you should do next
Most people who get infected with file locking malware have never previously had to deal with it. Therefore, it might be a terrifying experience for many, as the invaluable photos, important work, or school documents are no longer available. Users are generally confused about what to do next, as they cannot open .zwer encrypted files.
The correct course of action would be making a full backup of all the encrypted files (if you had backups, you could skip this step) – simply make a copy and place it on the USB stick or another external storage.
Once that is complete, you should then scan the computer with anti-malware software and eliminate the infection. This is were most users believe that anti-malware tools could help them to recover .zwer files, although it could not be further from the truth. Security software is designed to clean the system from malware, and it cannot decrypt data that was locked by ransomware.
To decrypt .zwer files, users can refer to several methods that we provide the instructions below. Possibly the best chance of recovery besides data backups is the Emsisoft's decryption tool. However, several rules should be met for the recovery process to be successful:
- .zwer files should be encrypted with an offline ID, which means that malware should have failed to contact its remote server. To check if that is the case for you, go to the C: drive on your computer and locate SystemID.txt or PersonalID.txt. Open the file – you should find the list of all the encrypted data IDs. If one of these entries ends with “t1,” an offline ID was used for your files, and it might be recovered with the Emsisoft decryption tool.
- If ransomware has failed to remove Shadow Volume Copies, you can recover files by using Windows Previous Versions feature or System Restore.
- Third-party recovery applications might be able to restore working versions of your files (however, this is not decryption!), as long as you did not use your computer a lot after the infection.
Watch out – Fake Djvu decryptor can encrypt .zwer files
Cybersecurity experts warn Djvu victims not to rely on offers to download free decryption tools for the latest variants of this ransomware family. At the beginning of June 2020, a strain of the Jigsaw ransomware has been found impersonating the long-awaited DJVU decrypter.
Spread via underground forums, phishing websites, and hacked ads, the alleged Djvu decrypter contains a malicious crab.exe executable, which stands for a ransomware payload. Unfortunately, victims who have their files already locked tend to act recklessly. Upon the phases of panic, the victims are looking for ways to unlock files, thus suchlike offers are extremely tempting.
However, once the user indicates the ID number, file extension, and clicks the “Scan now” button, the crab.exe file is launched allowing the ransomware to disable enable malicious processes, disable core Windows processes, turn security tools idle, etc.
The Zorab ransomware is a malicious piece of software, which re-encrypts files encrypted by any Djvu variant and appends .ZBR file extension to each of them. Besides, it removed the _readme-txt file developed by the first file-encrypting virus and leaves its own note –DECRYPT–ZORAB.txt.ZRB. The informational note demands people to write an email to zorab28@protonmail.com for further directions.
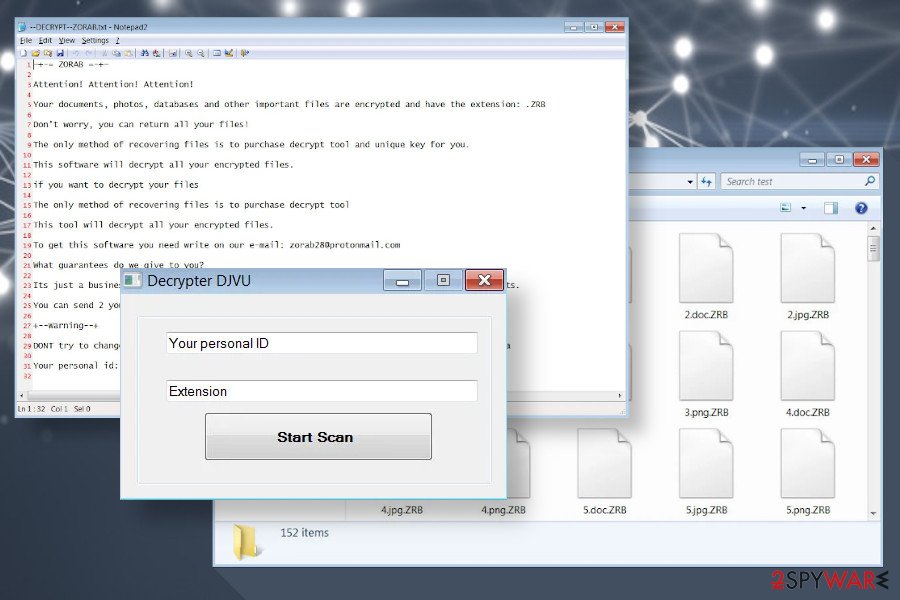 Zwer ransomware files can be double-encrypted by fake DJVU decrypter
Zwer ransomware files can be double-encrypted by fake DJVU decrypter
Unfortunately, just like the latest Djvu variants cannot be decrypted, .ZRB files cannot be recovered without the payment for criminals. However, researchers are under investigation of this threat, so do not rush to pay the ransom.
If you have been attacked by Zwer ransomware, which has been subsequently double-encrypted by Zorab ransomware, reboot your machine into Safe Mode with Networking and launch AV scanner.
NOTE: The fake DJVU decrypter tricks victims into believing that it's can recover the versions of Djvu based on online keys and launched after August 2019. That is not true. Zwer ransomware and its predecessors can't be decrypted for free.
Here's how ransomware managed to lock your files, and how to prevent it from happening in the future
As mentioned above, Djvu variants are mainly spread via software cracks. These files are used to bypass the licensing process of various applications and are essentially illegal. However, since cracks, keygens, loaders, and similar tools are widely popular, many do not even suspect that some of these could be malicious. Therefore it is highly advisable staying away from files that are download via torrent or similar insecure sites.
Another reason to stop downloading software cracks is that there is simply no way to check whether the file is actually malicious. Cracks, keygens, and similar tools are designed in a way that would break the code of another application. Therefore, even the most advanced security programs are going to flag the item as malicious, regardless if it is infected with malware or not.
Security experts from dieviren.de[3] also advise following these precautionary measures in order to avoid ransomware infections via the third-party websites that host illegal software downloads:
- Employ powerful anti-malware software with real-time detection feature and keep it updated at all times;
- Install ad-blocking browser extension to prevent the execution of background code within malicious ads;
- Pay attention to the file names that you download. For example, malicious actors often obfuscate file names by using double extensions, such as “file.mp4.exe”;
- Before downloading anything, check out user comments;
- Beware of copycat websites that mimic such sites like The Pirate Bay – these are riddled with malware;
- Set Java and Adobe Flash to run on click;
- Make sure all the latest updates are installed on your computer.
Finally, to negate most of the harmful ransomware infection effects, backup your files on a portable storage device or a remote cloud service.
Zwer ransomware removal explained
It is important to understand what type of changes the malware makes to the infected machine in order to remove Zwer ransomware in the correct way. First of all, you should go to the following location and delete the “hosts” file located there:
C:\Windows\System32\drivers\etc\
After that, you should make a full backup of the encrypted files – use something convenient like a USB stick, or upload all the data to a remote server (Google Drive, OneDrive, Dropbox). This will ensure that it will not get corrupted as soon as you perform Zwer ransomware removal. Note that encrypted files are not malicious, as they do not hold any malicious code inside of it.
Next, you should download and install a reputable anti-malware tool and perform a full system scan. In case there issues with the process, access Safe Mode with Networking, as we explain below. Finally, you can attempt the file .zwer file recovery process – we list all the solutions you can try below.
Getting rid of Zwer virus. Follow these steps
Manual removal using Safe Mode
In case the need arises during Zwer virus removal process, access Safe Mode with Networking:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Zwer using System Restore
You can use System Restore to eliminate malware from your system:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Zwer. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Zwer from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Zwer, you can use several methods to restore them:
Make use of Data Recovery Pro
Data Recovery Pro can sometimes help you to recover at least a portion of your files.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Zwer ransomware;
- Restore them.
Windows Previous Versions Feature might be useful when trying file recovery
If you have enabled System Restore prior to the infection, you can attempt to retrieve data with the help of the Windows Previous Versions feature.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer might save all your files
In case the virus failed to eliminate Shadow Volume Copies, use ShadowExplorer to recover your data.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Try out Emsisoft's decryption tool
Emsisoft decryptor is a tool that can help some of the Djvu ransomware victims. Keep in mind that it can only word for files that were locked with an offline ID. Note that this functionality is not available for all malware variants.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Zwer and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Josh Lake. What is RSA encryption and how does it work?. Comparitech. Tech researched, compared and rated.
- ^ Tim Fisher. What Is the Windows Registry?. Lifewire. Tech Untangled.
- ^ Dieviren. Dieviren. Cybersecurity advice and malware insights.





















