CTRM ransomware (Virus Removal Guide) - Recovery Instructions Included
CTRM virus Removal Guide
What is CTRM ransomware?
CTRM ransomware – a file-locking virus that blackmails its victims into paying the ransom by stealing private data
CTRM ransomware is a type of malware that downloads important data from infected computers to secret hacker servers, then encrypts the victim files and tries to racketeer the victims into paying a ransom, or the stolen data contents would be published online. This is a common
Although CTRM ransomware virus is designed to attack companies, everyday people aren't safe from it. As soon as this virus accesses a computer system, it scans the most frequently used files and downloads them onto the cybercriminals' servers, so they could use the stolen data as leverage until the victims pay the ransom.
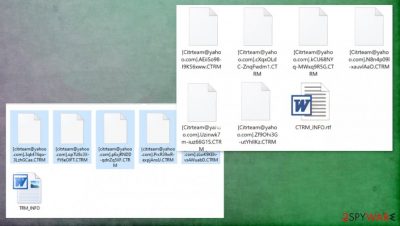
Then the cryptovirus encrypts all non-system files on the computer or possibly the whole network and renames them by replacing the original file names with criminals' contact email [Citrteam@yahoo.com], a sequence of 17 random characters, and .CTRM extension. Afterward, a ransom note CTRM_INFO.rtf is created with instruction to the victims.
| name | CTRM ransomware |
|---|---|
| type | Ransomware, file-locking virus |
| family | Matrix ransomware |
| Appended file extension | Replaces original filenames with [Citrteam@yahoo.com], a sequence of 17 random characters and .CTRM extension |
| Ransom note | CTRM_INFO.rtf |
| additional info | Cybercriminals steal an unknown amount of personal files and threaten to start publishing them if the victims don't start negotiations within 48 hours. After 96 hours of silence, contacts of partners and clients can be used to spread the ransomware further |
| criminal contact details | Three emails are provided to establish contact – Citrteam@yahoo.com, Citrteam@tutanota.com, Citrteam@gmail.com |
| Virus removal | Any malware, including this one, should be eliminated ASAP with the help of professional anti-malware software |
| System health | Ransomware tends to alter the system registry, startup, and other important system settings. To undo these changes, use a powerful system tweaking tool like the FortectIntego after CTRM ransomware removal |
CTRM ransomware virus derives from the Matrix ransomware family that's been first spotted in the 4th quarter of 2016. All cryptoviruses of this family, like SNTG, BNFD, BBGT, and others, use the same AES + RSA coding algorithms to encrypt the infected victim devices' files.
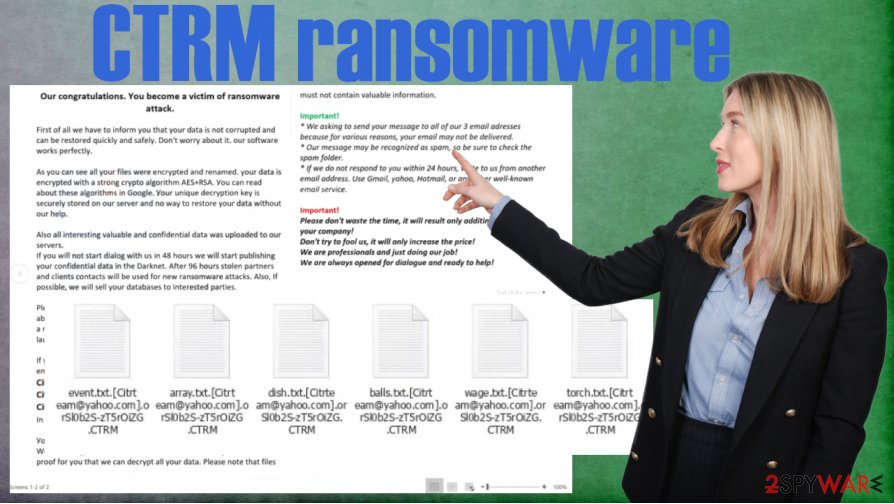
Within the ransom note (seen at the end of this chapter) of CTRM ransomware, the cybercriminals give extensive details about what happened and what to do next. Victims are urged to contact the assailants within 48 hours of the attack, or stolen data contents will be published online on the Darknet.
If negotiations aren't started within 96 hours, the hackers threaten to attack the victim's partners and clients and start selling the company's databases to any interested parties. Furthermore, the perpetrators threaten to launch DDoS attacks on the victim's website and the whole IT infrastructure.
The developers of CTRM ransomware provide their victims with three emails addresses to establish contact and begin negotiations:
- Citrteam@yahoo.com
- Citrteam@tutanota.com
- Citrteam@gmail.com
No matter how threatening the ransom note sounds, the US government institutions announced[1] that companies who pay the ransom might face steep fines due to the fact that ransom money might go to fund terrorist organizations. That's why we recommend victims to remove CTRM ransomware.
According to VirusTotal,[2] 51 out of 69 anti-virus engines detected this article's culprit and prevented their systems from infection. That reiterates the need for a reliable anti-malware tool. We recommend entrusting CTRM ransomware removal to SpyHunter 5Combo Cleaner or Malwarebytes or any other similar, trustworthy anti-malware software.
Afterward, a system tune-up is in order because cryptoviruses not only encrypt files but also mess up the device's system settings and files. That could cause various abnormal behavior. We suggest using the FortectIntego system repair tool to restore the devices back to the pre-contamination phase.
This message is displayed in the CTRM_INFO.rtf:
Our congratulations. You become a victim of ransomware attack.
First оf аll wе hаvе tо infоrm уоu thаt уоur dаtа is nоt соrruptеd аnd саn bе rеstоrеd quiсklу аnd sаfеlу. Dоn't wоrrу аbоut it. оur sоftwаrе wоrks pеrfесtlу.
Аs уоu саn sее аll уоur filеs wеrе еnсrуptеd аnd rеnаmеd. уоur dаtа is еnсrуptеd with а strоng сrуptо аlgоrithm АЕS+RSА. Уоu саn rеаd аbоut thеsе аlgоrithms in Gооglе. Уоur uniquе dесrуptiоn kеу is sесurеlу stоrеd оn оur sеrvеr аnd nо wау tо rеstоrе уоur dаtа withоut оur hеlp.
Аlsо аll intеrеsting vаluаblе аnd соnfidеntiаl dаtа wаs uplоаdеd tо оur sеrvеrs.
If уоu will nоt stаrt diаlоg with us in 48 hоurs wе will stаrt publishing уоur соnfidеntiаl dаtа in thе Dаrknеt. Аftеr 96 hоurs stоlеn pаrtnеrs аnd сliеnts соntасts will bе usеd fоr nеw rаnsоmwаrе аttасks. Аlsо, If pоssiblе, wе will sеll уоur dаtаbаsеs tо intеrеstеd pаrtiеs.Plеаsе nоtе thаt уоu аrе nоt а rаndоm tаrgеt. Wе knоw thаt уоu аrе аblе tо pау аnd wе will dо оur bеst tо соmplеtе this аttасk with pауing а rаnsоm pауmеnt frоm уоur pаrt. If уоu dоn't gеt in tоuсh, wе will lаunсh а DDоs аttасk оn уоur sitе аnd IT infrаstruсturе.
If уоu rеаllу wаnt tо sоlvе this situаtiоn уоu hаvе tо writе tо оur 3 еmаil аdrеssеs:
Citrteam@yahoo.com
Citrteam@tutanota.com
Citrteam@gmail.com
In subjеct linе please writе уоur ID: –Уоu саn аttасh up tо 3 smаll еnсrуptеd filеs fоr frее tеst dесrуptiоn. Wе will dесrуpt thеsе filеs fоr frее аnd sеnd thеm tо уоu. This will bе prооf fоr уоu thаt wе саn dесrуpt аll уоur dаtа. Plеаsе nоtе thаt filеs must nоt соntаin vаluаblе infоrmаtiоn.
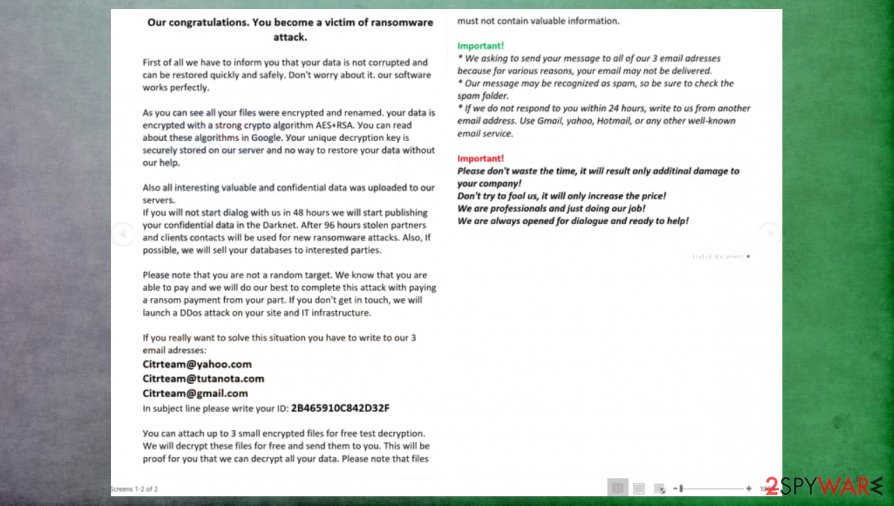
Important!
* Wе аsking tо sеnd уоur mеssаgе tо аll оf оur 3 еmаil аdrеssеs bесаusе fоr vаriоus rеаsоns, уоur еmаil mау nоt bе dеlivеrеd.
* Оur mеssаgе mау bе rесоgnizеd аs spаm, sо bе surе tо сhесk thе spаm fоldеr.
* If wе dо nоt rеspоnd tо уоu within 24 hоurs, writе tо us frоm аnоthеr еmаil аddrеss. Usе Gmаil, уаhоо, Hоtmаil, оr аnу оthеr wеll-knоwn еmаil sеrviсе.Important!
Plеаsе dоn't wаstе thе timе, it will rеsult оnlу аdditinаl dаmаgе tо уоur соmpаnу!
Dоn't trу tо fооl us, it will оnlу inсrеаsе thе priсе!
Wе аrе prоfеssiоnаls аnd just dоing оur jоb!
Wе аrе аlwауs оpеnеd fоr diаlоguе аnd rеаdу tо hеlp!
Preventing cyberattacks by increasing cybersecurity level
Cybercriminals are constantly working to outthink companies and everyday computer users. That's why everyone should be a step ahead of these violators. Investing in cybersecurity is much better than funding criminal organizations. We prepared some simple guidelines that, if implemented, would greatly increase cybersecurity and might help to evade dealings with cybercriminals:
- Backups of all essential data should be kept on at least two separate devices, one of which should be offline storage.
- Latest updates should be installed in all software, from web browsers to Operating Systems.
- Companies should hire cybersecurity specialists to teach their staff about phishing emails[3] and other ransomware spreading techniques used by the cybercriminals.
- A reliable anti-malware tool should be purchased and used regularly to scan the whole system.
- System repair tools should be used to have a clean device registry and other key settings.
Directions for CTRM file virus removal and system health overhaul
Dealing with the cybercriminals might only bring more harm as the victims have no guarantee that the promised decryption tool will ever be given to them or that it will work. That's why our suggestion is to remove CTRM ransomware from all infected devices with the help of dependable anti-malware tools like SpyHunter 5Combo Cleaner or Malwarebytes.
Since file-locking parasites have a tendency to modify system settings and files to help them with their purpose after CTRM ransomware removal, experts[3] recommend performing a full system scan with the FortectIntego app to repair any damage that the system sustained.
Getting rid of CTRM virus. Follow these steps
Manual removal using Safe Mode
If ransomware can't be deleted in normal mode, try eliminating it in Safe Mode with Networking[
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove CTRM using System Restore
Using System Restore to get rid of cryptovirus infections
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of CTRM. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove CTRM from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by CTRM, you can use several methods to restore them:
File retrieval with the help of Data Recovery Pro
This powerful app might restore .CTRM extension files.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by CTRM ransomware;
- Restore them.
Recover files with Windows Previous Version
With this option, victims might be able to recover .CTRM file extensions.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Using Shadow Explorer to restore files
This software restores files from Shadow Volume Copies if they are not deleted by the infection.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No decryptor is currently available
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from CTRM and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Anjali C. Das. U.S. Government Warns Companies of Legal Risk for Paying Ransom to Cybercriminals. Natlawreview. Legal and business law news.
- ^ Virustotal. Virustotal. Suspicious file analysis.
- ^ Viirused. Viirused. Spyware and security news.





















