Everbe ransomware (Virus Removal Guide) - updated May 2020
Everbe virus Removal Guide
What is Everbe ransomware?
Everbe ransomware is a multi-variant cryptomalware that appends various extensions to the affected files
Everbe is a file locking virus that was released in March 2018 and since then has been reaching targets worldwide by using multiple attack vectors. Malware receives regular updates, although threat actors usually take around a month's break before releasing a new variant. Initial versions appended .everbe or .eV3rbe file extension after performing file encryption with the help of AES + RSA encryption algorithms; then malicious actors used .embrace, .volcano, and many others. The most recent variant was Everbe 3.0 ransomware that was spotted infecting users in March 2020, and appended .CULEX extension to files.
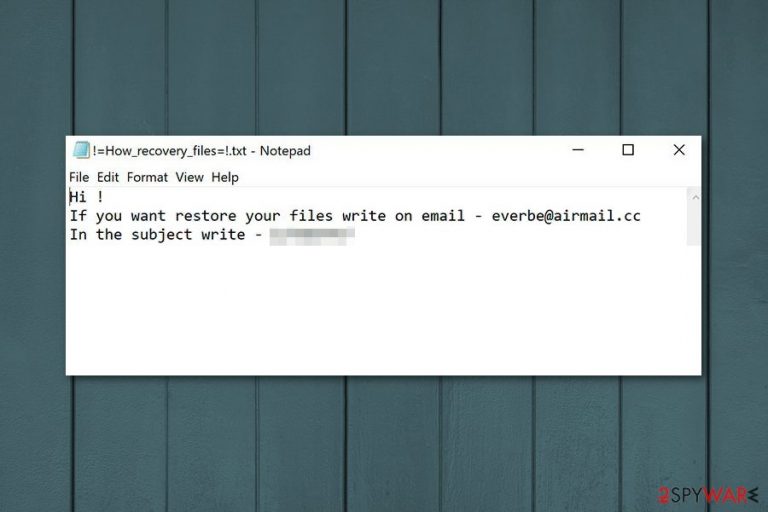
As it is typical to ransomware, Everbe virus also leaves a ransom note behind, under such names as !=How_recovery_files=!.html, EVEREST LOCKER.txt, !#_How_to_decrypt_files_#!.txt, readme.txt, and many others. Over the years, the contents changed inside, providing a different contact email address.
So far, there are three major releases of malware, including Everbe 1.0, Everbe 2.0, and Everbe 3.0. While the two latest versions cannot be decrypted, all 1.0 variants can be recovered with the help of InsaneCryptDecryptor, available for free. Unfortunately, there is no guarantee that the tool will work for all victims, so we provide alternative methods for data recovery below.
| Summary | |
|---|---|
| Name | Everbe |
| Type | Ransomware |
| variants |
|
| Encryption algorithm | Malware uses AES/DES to lock files and RSA is used for key encryption |
| Danger level | High. Makes system changes and encrypts files; demands a ransom |
| Ransom note | !=How_recovery_files=!.txt or !=How_recovery_files=!.html, and others |
| Appended file extension |
.[everbe@airmail.cc].everbe; .[embrace@airmail.cc].embrace; .pain; [eV3rbe@rape.lol].eV3rbe; .[hyena@rape.lol].HYENA; .[thunderhelp@airmail.cc].thunder; .[yoursalvations@protonmail.ch].neverdies; [neverdies@tutanota.com].neverdies; .[Divine@cock.lu].divine; .[Evil@cock.lu].EVIL; .[notopen@cock.li].NOT_OPEN; .[Everest@airmail.cc] .EVEREST; .[Youhaveonechance@cock.li].lightning; .seed; .[DeAdmin@cock.li].DEADMIN; .Oypl7T1i9; .[Culex@cock.li].CULEX; |
| Contact email addresses | everbe@airmail.cc, embrace@airmail.cc, pain@cock.lu, pain@airmail.cc; hyena@rape.lol; hyena@cock.lu; thunderhelp@airmail.cc; yoursalvations@protonmail.ch; neverdies@tutanota.com, and many others |
| Data recovery | All variants belonging to Everbe 1.0 can be decrypted with the help of InsaneCryptDecrypter. |
| Malware removal | Do not attempt to eliminate ransomware manually but instead employ anti-malware software for the purpose – we recommend using SpyHunter 5Combo Cleaner or Malwarebytes |
| System fix | If you face random crashes, errors, and other stability issues after malware elimination, scan your system with FortectIntego to fix virus damage |
When the name is changed data immediately becomes compromised and unusable due to a sophisticated encryption algorithm. Everbe ransomware virus then generates a ransom note and spreads copies in all of the existing folders. This os just one of the examples, as ransom note contents differ with each Everbe virus versions:
Hi !
If you want to restore your files write on email – everbe@airmail.cc
In the subject write – [redacted victim ID number]
As you can see from the quote above, this short message encourages users to contact developers via everbe@airmail.cc email, if they want to restore encrypted data. The ransom note also provides unique victim’s ID which is asked to enter in the subject line of the email.
However, we do not recommend contacting the creators of Everbe ransomware and following their instructions. There’s no doubt that they will ask Bitcoins or another cryptocurrency in exchange for unique decryption key created for each victim. But once cybercriminals receive the payment, they might disappear and leave you with a bigger loss.
No matter how much you need to get back your files, you should remember that there are no guarantees that crooks keep their promise and help with data recovery.[1] Additionally, paying the ransom gives no results in Everbe removal. Hence, your computer remains vulnerable and sluggish. Besides, there is a free decryptor available,[2] so there is no need to pay hackers.
Keep in mind that you need to remove Everbe ransomware first before you can proceed with data recovery. However, if you do not have backups, you can try using additional tools that we have presented at the end of the article. If they do not help, you should remain patient and wait for malware researchers to create a free decryptor. Finally, if your computer starts lagging and crashing after Everbe ransomware termination, you can make use of FortectIntego to fix virus damage quickly.
Different Everbe family variants
The good news is that Everbe decryptor can help while dealing with two variants of malware — Embrace and Painlocker. Although, this only work for these firstly discovered ones because hackers are known to modify the code of ransomware so that decryptor would not work. These versions came out quickly one after another, each having a new name altogether.
Once more, two new versions came out in July 2018. Everbe 2.0 and Hyena Locker are not decryptable yet. The previous tool does not work. These two are similar and have lengthy ransom notes containing new contact emails (two for each version) and new file extensions.
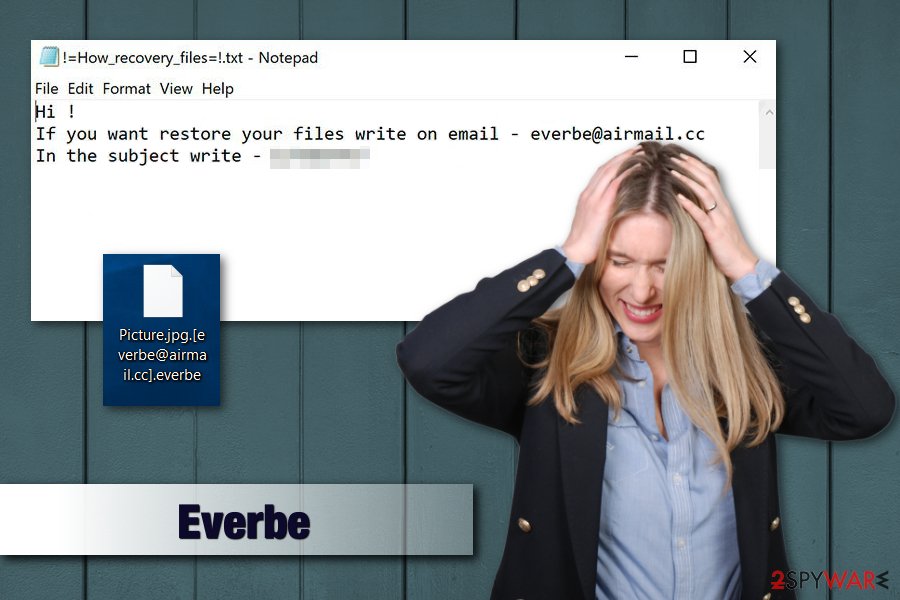
Embrace ransomware
Embrace ransomware made a comeback as the first continuation of Everbe malware. It spread through unprotected RDP, using malicious attachments in spam emails or was injected into malicious websites. It used the same encryption algorithm (AES or DES) to lock up files and added [embrace@airmail.cc].embrace. For example, a file called picture.jpg would be turned into picture.jpg.[embrace@airmail.cc] .embrace.
The ransom note !=How_recovery_files=!.txt slightly differs from the first variant and urges users to contact hackers via embrace@airmail.cc. Victims are also warned that in case the payment will not be made within seven days, the price of ransom will double. It is unknown how much money crooks ask for; however, prices usually range between $500 and $1500, and payments are executed in Bitcoin or another cryptocurrency.
As usual, we recommend users to ignore ransomware authors and remove Embrace virus from the machine ASAP.
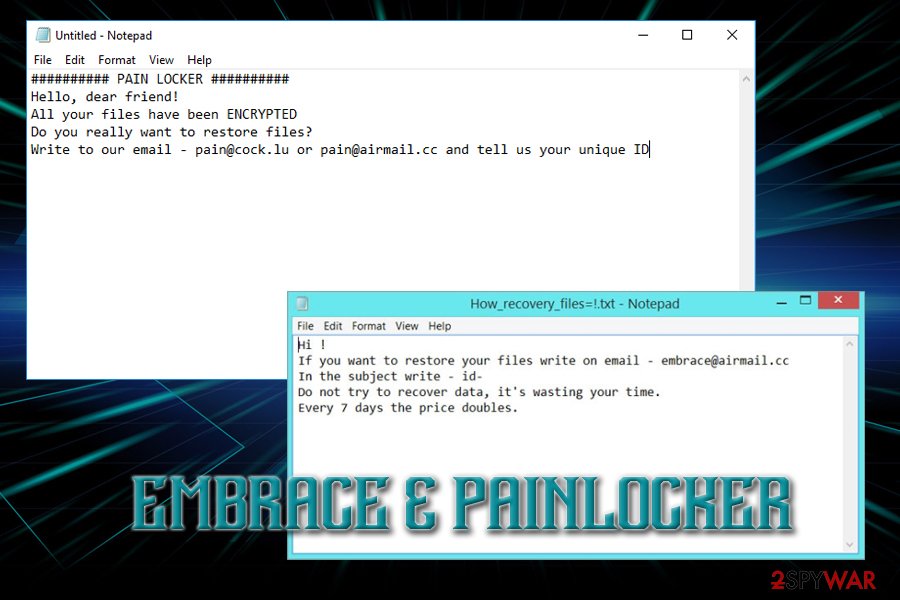
PainLocker ransomware
PainLocker is the latest addition to Everbe crypto-malware family. It adds [pain@cock.lu].pain appendix to each of the files and generates ransom note of the same name – !=How_recovery_files=!.txt., which states the following:
########## PAIN LOCKER ##########
Hello, dear friend!
All your files have been ENCRYPTED
Do you really want to restore files?
Write to our email – pain@cock.lu or pain@airmail.cc and tell us your unique ID
Painlocker wants users' money. Thus, these hackers are not your friends (as they self-proclaimed)! Even though the decryptor works for this version of the virus as well, in rare cases it may not work for you. Therefore, it is vital to keep regular backups and employ reputable security software which could detect malicious threats and eliminate them before they can enter. If you found your files encoded, hurry up and remove PainLocker using an anti-malware tool.
Everbe 2.0 ransomware
This version came out in July 2018 as the second version to the main ransomware Everbe virus. Security experts were convinced that the virus will remain decryptable. However, decryption tools that have already been presented do nothing to recover files encrypted by this ransomware version. This variant is appending .[eV3rbe@rape.lol].eV3rbe file extension or .[thunderhelp@airmail.cc].thunder appendix to the target data.
The particular version is using AES-256 encryption method. This version offers to test its decryption capabilities by decrypting three the most important victim's files. The ransom amount is still unknown, so it is possible that the ransom you need to pay depends on the time you take to contact the criminals. However, we highly do NOT recommend contacting cybercriminals. Instead, you should try the data recovery steps given at the end of this post.
Hyena Locker ransomware
Hyena Locker is the fourth version of the ransomware which showed up in July 2018. It is using three-paragraph ransom note to suggest its victims sending files to test the decryption procedure. This is offered so you can believe that the payment you send to cyber criminals will guarantee you the full decryption of your files.
Hyena is using .[hyena@rape.lol].HYENA file extension while marking encrypted files and generates the key which is saved on a remote server which belongs to hackers. Just like Verbe 2.0, it is using AES-256 encryption chiper. The virus is still undecryptable.
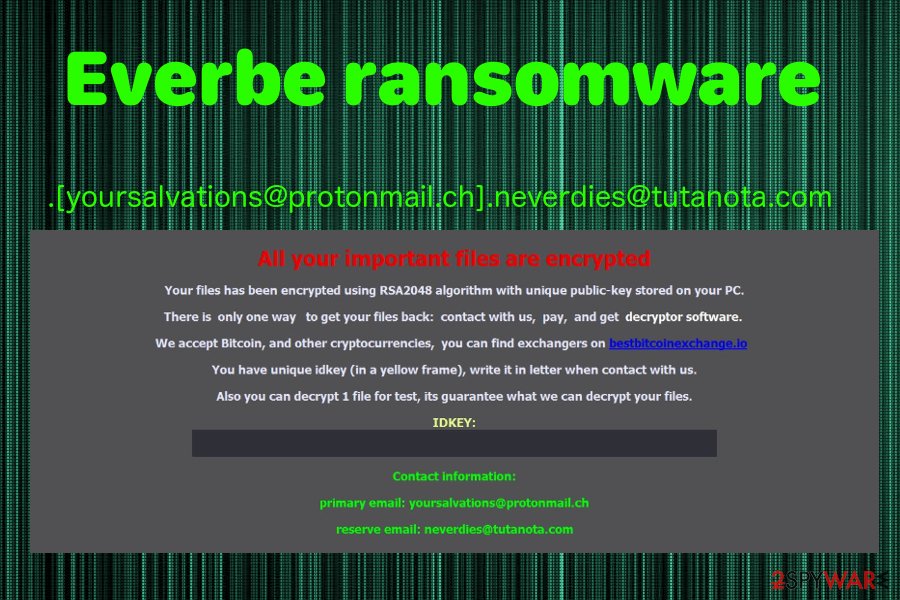
.[yoursalvations@protonmail.ch].neverdies@tutanota.com file extension virus
On November 22 2018, the newest Eveerbe ransomware variant was discovered. This virus comes with a typical lengthy file extension – .[yoursalvations@protonmail.ch].neverdies@tutanota.com. This version encrypts users' personal data using the RSA-2048 encryption algorithm and marks them with the mentioned marker.
Then it delivers a ransom message in the file named as the previous versions – !=How_recovery_files=!. However, it shows up as a program window on the screen stating about the encryption and suggesting to contact developers via yoursalvations@protonmail.ch or neverdies@tutanota.com. You shouldn't do so and remove this virus instead. Based on the detection rate, you can use Fortect for the job.[3]
Culex Locker ransomware
The release of Everbe ransomware was relatively successful to the attackers, as they followed with new variants at a regular pace. However, malware kept a low profile during 2019, just to come back in March 2020 with a new release of Culex Locker version, or otherwise known as Everbe 3.0.
Using a variety of different attack vectors, Culex ransomware typically reaches users' PCs unnoticed and immediately begins Windows system modification. This allows the virus to perform the file encryption process, which appends the extension .[Culex@cock.li].CULEX to each of the files. Then, malware drops the !_HOW_RECOVERY_FILES_!.txt message to users, which reads:
>>>>>>>>>>>>>>>>>>>>>>>>>>>> CULEX LOCKER <<<<<<<<<<<<<<<<<<<<<<<<<<<<
HELLO, DEAR FRIEND!
1. [ ALL YOUR FILES HAVE BEEN ENCRYPTED! ]
Your files are NOT damaged! Your files are modified only. This modification is reversible. The only 1 way to decrypt your files is to receive the decryption program.2. [ HOW TO RECOVERY FILES? ]
To receive the decryption program write to email: culex@cock.li And in subject write your ID: ID-xxxxxxxxx We send you full instruction how to decrypt all your files. If we do not respond within 24 hours, write to the email: culex@cock.lu3. [ FREE DECRYPTION! ]
Free decryption as guarantee. We guarantee the receipt of the decryption program after payment. To believe, you can give us up to 3 files that we decrypt for free. Files should not be important to you! (databases, backups, large excel sheets, etc.)>>>>>>>>>>>>>>>>>>>>>>>>>>>> CULEX LOCKER <<<<<<<<<<<<<<<<<<<<<<<<<<<<
Macro-filled documents from spam emails distribute ransomware payload
The main way how ransomware is being spread on the web and installed on computers is spam emails.[4] They often include malicious attachments that execute download and installation of malware to your computer. Letters can be called like they are from real and big companies like PayPal, DHL, LinkedIn, and others.
Additionally, infected email attachments usually look safe to open. Creators of malware often inject malicious code into Word or PDF documents. In some cases, ransomware might arrive in the ZIP archive. So, you should be extremely careful with received emails.
Security specialists from NoVirus.uk[5] also warn that authors of malware might use other methods to spread the file-encrypting virus, such as:
- Unofficial software download sources or peer-to-peer networks that promote and offer to install suspicious programs;
- Fake updaters might include malware instead of being upgrading any software;
- Security pop-ups might ask to install fake security programs that are malware;
- Malicious ads placed on both legit and high-risk websites.
To avoid infiltration of such cyber threat, you should be not only careful with emails and learn how to identify tricky messages sent by hackers, but also follow major security tips, such as avoiding visiting potentially dangerous sites, downloading programs from ads or unauthorized download sites. Additionally, data backups and installation of antivirus program helps to minimize the risk of ransomware attack.
Eliminate Everbe immediately and clean the system
Everbe removal needs to be done using the anti-malware program. Ransomware creators upgrade their codes and make viruses more evolved each time the new version comes out. We recommend using SpyHunter 5Combo Cleaner and Malwarebytes for cleaning your computer and then fixing damaged system files with FortectIntego to avoid Windows reinstallation. However, feel free to use your beloved anti-malware program, but do not forget to update it first!
Additionally, ransomware virus can block access to the security program or its installation process. So you might need to do other steps that are mentioned in a removal guide below.
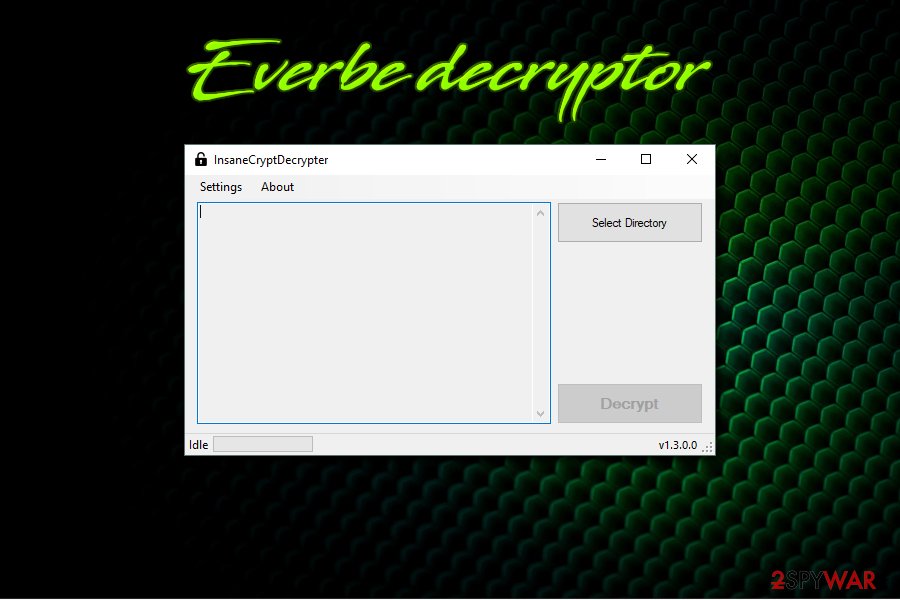
Once you remove Everbe from the machine, you can begin the data recovery procedure. You should first try to gain access to your files back by using Embrace Decryptor or InsaneCryptDecrypter. These tools should be helpful with almost every version of this ransomware. In case it does not work for you, below you can see other options for restoring your data.
Getting rid of Everbe virus. Follow these steps
Manual removal using Safe Mode
If you cannot run automatic Everbe removal, follow these steps:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Everbe using System Restore
Try System Restore feature on your device to terminate Everbe ransomware:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Everbe. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Everbe from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Everbe, you can use several methods to restore them:
Try Data Recovery Pro to restore missing files
It's not an official Everbe decryptor, but it can help to recover some of the encrypted files.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Everbe ransomware;
- Restore them.
Take advantage of Windows Previous Versions feature
If System Restore was enabled before ransomware attack, you could copy individual files by following these steps:
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Try Shadow Explorer to restore files encrypted by Everbe ransomware virus
If malware did not delete Shadow Volume Copies, this tool might be useful:
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Use Embrace Decryptor
Security researchers Michael Gillespie and Maxime Meignan recently created a decryptor which can be used to recover your files affected by Everbe for free. This works for Everbe, Embrace and Painlocker only. You can download the tool from here. Additionally, in 2018 December, security researchers presented a decrypter for .everbe, .embrace, .insane, .deuscrypt, .pain, .volcano, .twist and .Tornado file extensions. You can get it by clicking this link.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Everbe and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ David Glance. WannaCry hackers had no intention of giving users their files back even if they paid. The Conversation. In-depth analysis, research, news and ideas.
- ^ Embrace decryptor. Github. File hosting service.
- ^ Detection rate of Everbe. Virustotal. Online malware scanner.
- ^ Danny Palmer. Double trouble: This ransomware campaign could infect your PC with two types of file-locking malware. ZDNet. Technology news, analysis, comments and product reviews.
- ^ No Virus. No Virus. British cyber security news.







