Foodtab.club browser hijacker (Free Instructions)
Foodtab.club browser hijacker Removal Guide
What is Foodtab.club browser hijacker?
Foodtab.club is your typical browser hijacker that pretends to be useful

Potentially unwanted applications are something that most people come across at least at some point, although not everyone properly knows what they are or how they operate. The first common sign that most people face is the mysterious appearance of the app itself, with some not even knowing that it is present of the device. In this case, users would firstly see changes to their homepage, which would be swapped to Foodtab.club.
The appearance can be easily explained and is not actually so mysterious – potentially unwanted programs[1] are usually placed into software bundles, which are downloaded from third-party websites and unintentionally installed thanks to pre-ticked checkboxes, fine print, Recommended settings, and other tricks. In other cases, users might also believe that the functionality of a browser hijacker is useful and install it intentionally.
This particular instance of browser hijacking is related to an extension known as Food Club. As the title itself suggests, the app is focused on food and everything about it, or at least it looks so initially. The truth is that it doesn't provide any benefits for food lovers and instead uses its presence to change the way users browse the web in a way they would be exposed to as much commercial material as possible.
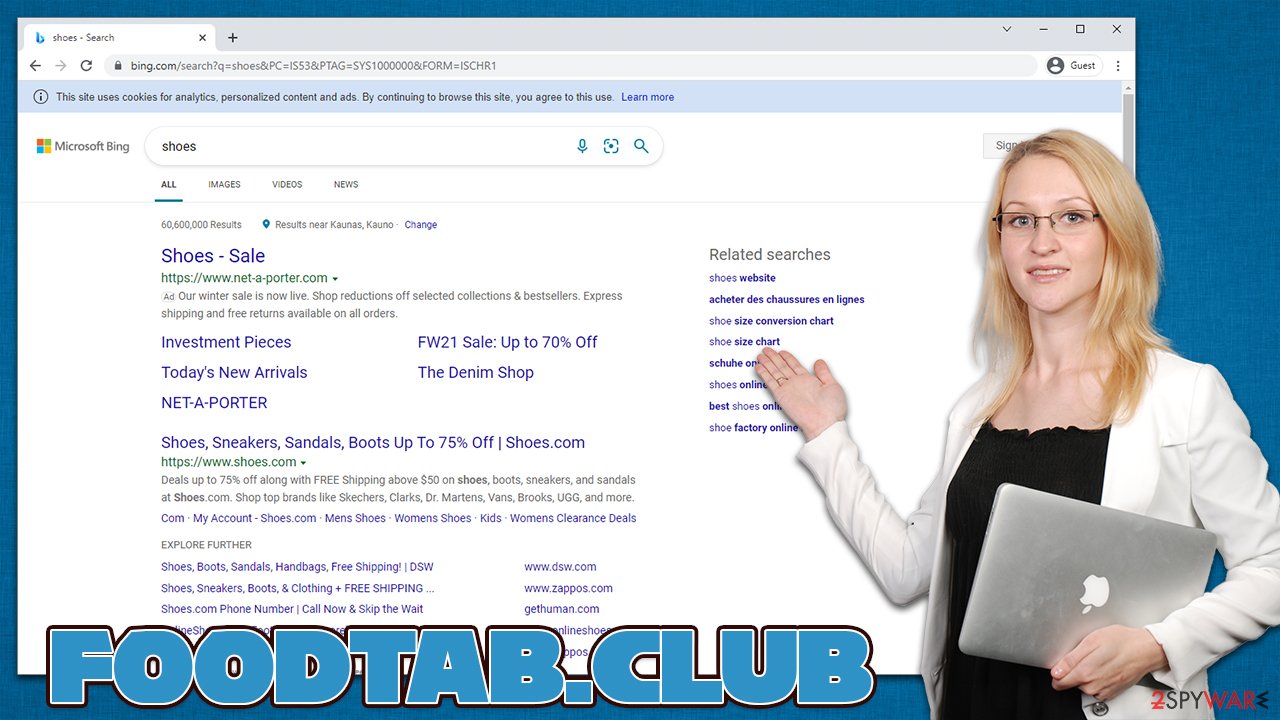
The commercial content manifests itself mostly as additional links presented at the top of search results of a search provider which is no longer the same. In most cases, people would see that Foodtab.club search box would reroute them to Bing or another service provider, depending on their location. While these are perfectly legitimate, the generated ads are not and are the sole work of the hijacker.
| Name | Foodtab.club |
|---|---|
| Type | Browser hijacker |
| Distribution | Software bundles, third-party websites, deceptive ads, fake Flash Player updates |
| Symptoms | A new extension, Food Tab, is installed on the browser; homepage and new tab address are altered to the hijacker's one; a customized search engine redirects all searches to Bing or another provider; search results are filled with ads |
| Risks | While browser hijackers rarely pose a danger in terms of security point of view, users might end up installing other suspicious or unwanted software, suffer monetary losses due to ads, as have their privacy compromised |
| Uninstall | You can browser hijackers by following the manual guide below or by scanning the computer with powerful SpyHunter 5Combo Cleaner anti-malware software |
| Additional tips | After you eliminate all PUPs from your system, make sure you clean your web browsers and repair system files. You can also do that automatically with FortectIntego |
Potentially unwanted programs have been around for many years now and, just like any other software out there, evolved over time. It all started with toolbars that were so prominent as soon as they were available for the web browsers. At that time, many browser hijackers were also installed as standalone applications that would alter browser settings as well.
Security researchers were referring to many of such apps as spyware[2] due to their excessive information tracking capabilities. While data collection to this day is a trait of most apps and websites, the practice was much more extreme back then. Information such as emails, names, and even account passwords was sometimes harvested and shared.
Nowadays, browser hijackers are one of the most common potentially unwanted program types out there and usually take up the form of browser extensions – they are very easy and cheap to make and provide functionality that allows collecting the ad revenue for ad clicks from users with ease.
We have previously discussed hijackers such as Pure Dark, ProTabs, Color Darker, or Easysearch.club – these are just a few examples of apps that take over the homepage with their own settings.
Dangers of advertisements
Ads are something that most consumers despise. They have been disrupting the TV programs on a regular basis, making people wait for their show to continue. It was inevitable that they would be transferred to the internet sphere, as nowadays more than half of the population uses it.
Ads are not always bad, per se, as they help fund projects and websites that otherwise might be impossible. Unfortunately, even the most popular outlets or high-profile companies abuse advertisements to gain as much revenue as possible. This often comes at the cost of user satisfaction and negative experience, as an overwhelming number of ads can be very intrusive – they interfere and even move website content, making people click on links they did not intend to.
Browser hijackers usually employ a more discrete way to expose users to ads, and that's the altered search results and change of the search provider. This, however, might be very annoying to those who are already used to their own browser preferences. Some hijackers might even put misleading and dangerous links in there, compromising user safety and computer security in the process.
Most of the browser hijackers, including Foodtab.club, are usually presented as some type of apps that would be allegedly useful. They often feature names that are allegedly associated with their functionality, e.g., Food Tab is meant to provide recipes and similar information related to the topic.
Behind the regular functionality of a simple search engine, this app does not provide any of it – the only difference is that the homepage incorporates a few links to popular websites such as Gmail or Twitter. It goes without saying that most modern browsers are customizable, and the links can be set according to every person's interests without additional browser extensions.
Foodtab.club removal steps
Unexpected browser changes should never be ignored, as the reason behind it can be something more sinister than a simple hijacker. Some malware changes the browser settings as a part of its routine for more ad monetization. Luckily, most browser hijackers are very easy to remove, especially if they come in the form of a browser extension.
1. Remove the browser extension
If your homepage has been changed to Foodtab.club, the extension responsible for the change is Food Tab, so you should look for it in your browser settings. Keep in mind that there could be other potentially unwanted apps installed as extensions, so remove those as well.
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the window's top-right).
- Select Add-ons.
- In here, select the unwanted plugin and click Remove.

MS Edge (Chromium)
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

2. Scan your system with an anti-virus
After you get rid of the unwanted extension, you should then ensure that your system is free from malware and other potentially unwanted programs that could be much stealthier. Various techniques can be used by malicious software to mask their presence – they often run in the background without visible windows. They can also inject the malicious code into processes[3] so they would avoid detection by some apps.
We recommend running a scan with SpyHunter 5Combo Cleaner or Malwarebytes anti-malware tools, although make sure that they are both updated to the latest version so that the latest virus database would be used. Security apps are also extremely useful when dealing with potentially unwanted programs, especially the more aggressive ones.
3. Clean your browsers
Your final step is to ensure that cookies, caches, and other web data are eliminated from the browser. This will ensure that the tracking activities are no longer taking place. Likewise, overly full caches might result in errors and even security issues in some cases.
You can employ FortectIntego to do this step automatically or follow the instructions we provide below. Remember to do this every now and then for the best browsing experience in the future.
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

MS Edge
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

How to prevent from getting browser hijacker
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Chris Hoffman. PUPs Explained: What is a “Potentially Unwanted Program”?. How-to Geek. Site that explains technology.
- ^ Spyware. Wikipedia. The free encyclopedia.
- ^ Process Injection Techniques. Cynet. Security research blog.
