Herad ransomware (Removal Instructions) - Quick Decryption Solution
Herad virus Removal Guide
What is Herad ransomware?
Herad ransomware – a file-encrypting threat that offers a 50% decrease for the ransom price if victims show signs of contact in 72 hours
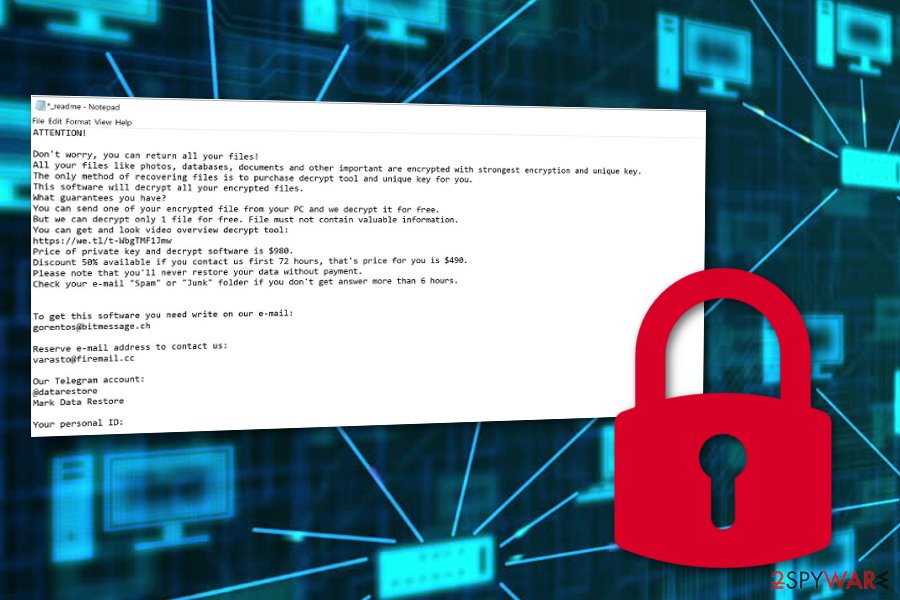
Herad ransomware is a newly discovered form of Djvu (STOP) virus that takes place on the Windows operating system. The dangerous cyber infection appends the .herad extension to every file that is met on its way. Once files end up encrypted, proper access is denied until the decryption tool is received. Criminals offer to pay a price of $980 after three days or an amount of $490 if contact is made in a time period of three days. Gorentos@bitmessage.ch and varasto@firemail.cc are email addresses provided in the _readme.txt ransom note. The same ransom-demanding message is used by other Djvu family members such as Godes ransomware, Cezor ransomware, Litar ransomware, Dalle ransomware, Vesad ransomware.
| Name | Herad |
|---|---|
| Type | Ransomware |
| Family | Djvu (STOP) virus |
| Similar malware | Godes ransomware, Cezor ransomware, Litar ransomware, Dalle ransomware, Vesad ransomware |
| Extension | .herad |
| Ransom note | _readme.txt |
| Price | A 50% decrease from $980 is offered if contact is made in three days |
| Email address | Gorentos@bitmessage.ch and varasto@firemail.cc |
| Detection | Try using software such as FortectIntego to detect malicious entries and objects in your infected Windows system |
Criminals who engage with the distribution of Herad virus and seek to benefit from this malware as much as possible, try to convince users of purchasing the decryption tool by providing evidence of its existence. The crooks offer to send one small file/document for free decryption, however, try not to fall for this trick.
Even though user reports claim that the official STOP decrypter does not work for Herad ransomware, you still should stay away from any types of offers to make payments. It is known that sometimes cybercriminals do not hold the decryption software or even if they do, they still might not handle it to you after the ransom is transferred.
Due to the scamming possibility, you should avoid making any contact with these people. An alternative would be to try some data recovery products from the list given at the end of this article. Of course, make sure that you deal with the infection first and successfully remove Herad ransomware from your computer system.
A suggestion of ours would be to download and install reputable antivirus software for a full system check-up. Tools such as FortectIntego or SpyHunter 5Combo Cleaner might appear to be really helpful. After the anti-malware performs a scan and detects infected sources, you will be able to continue with Herad ransomware removal and ensure that no malicious objects are left.
Be aware that Herad ransomware might initiate a quite bigger variety of activities than you might think at first. This file-encrypting virus is also known as a possible distribution source of AZORult Trojan virus just like other malware from the STOP ransomware category. Trojans are also dangerous as they might relate to data or money theft.
Furthermore, Herad ransomware might include a module that runs commands for Shadow Volume Copy[1] disabling. If this happens, you might run into more trouble while trying to recover your encrypted files. However, this is also is not a reason to rush and give away all of your money to the cybercriminals.
However, be careful while storing your future data as not to get lured in similar cyber attacks again. A piece of advice would be to purchase a portable drive or transfer data to a remote server where it can be kept away from cybercriminals who spread Herad ransomware and similar threats. Just make sure if you are using a USB drive,[2] you keep it unplugged from the machine when you do not need it.
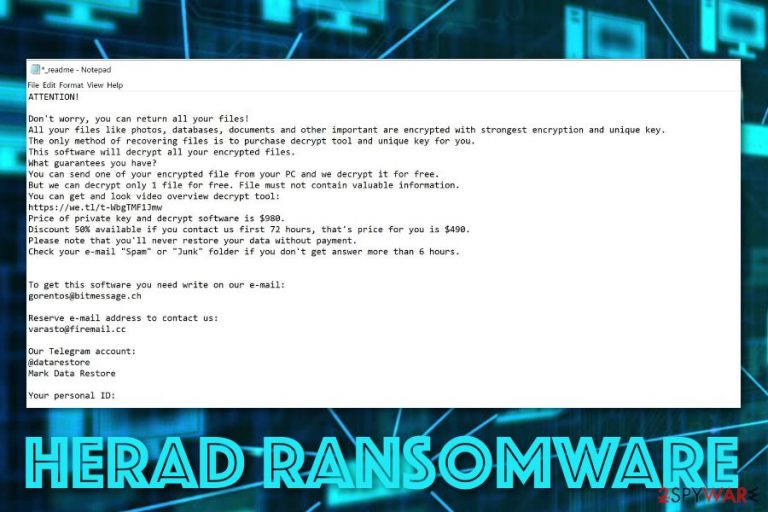
Note that the main signs of Herad ransomware residing on your computer are the .herad extension clipped to each encrypted file/document, suspicious processes running in the Task Manager, malicious entries in the Windows Registry, and the ransom-demanding message that looks like this:
ATTENTION!
Don't worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
hxxps://we.tl/t-g2wRDh3Pih
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that's price for you is $490.
Please note that you'll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don't get answer more than 6 hours.
To get this software you need write on our e-mail:
gorentos@bitmessage.ch
Reserve e-mail address to contact us:
varasto@firemail.cc
Our Telegram account:
@datarestore
Mark Data Restore
Your personal ID:
–
Email spam campaigns spread ransomware intensively
According to cybersecurity experts from NoVirus.uk,[3] ransomware viruses are intensively delivered through email spam campaigns. The crooks plant the malicious payload straight into legitimate-looking Word documents or Excel files. If the user executes such content, he/she will get the computer infected with malware.
For this not to happen, you have to take good care of your received email. Check all messages for possible grammar mistakes, always identify the sender, and evaluate your expectancies of important email lately. If you were not waiting for anything valuable to come, you should not risk opening the misleading email message.
Furthermore, ransomware threats can be spread through piracy networks, online-gaming websites, porn pages, gambling sites, and similar sources. Staying cautious while browsing throughout the Internet sphere is one of the best things you can do. Also, do not forget to think about antivirus protection for your machine.
Removal tips for Herad ransomware
Herad virus will definitely introduce itself once planted on your Windows machine by displaying a ransom note and encrypting files with the .herad appendix. If this happens, the only option for you left is to get rid of the cyber threat automatically as manual elimination is too risky for this case.
You should remove Herad ransomware with the help of reputable computer software. Also, a piece of advice would be to scan the entire system with tools such as FortectIntego, SpyHunter 5Combo Cleaner, or Malwarebytes. These programs will help you to identify all malicious locations and possibly-infected objects on your machine.
Before you start with Herad ransomware removal, you need to reboot your system with Safe Mode with Networking or launch System Restore to disable malicious ongoing processes. Once you do this and also terminate the threat, you can continue with some data recovery software that is also placed below.
Getting rid of Herad virus. Follow these steps
Manual removal using Safe Mode
Using Safe Mode with Networking might allow disabling malicious processes on your Windows computer:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Herad using System Restore
Turn on System Restore to deactivate the malware on your machine:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Herad. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Herad from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Herad, you can use several methods to restore them:
Data Recovery Pro might be a handy tool for file-restoring tasks:
Try using this software if you are looking for ways to recover your data:
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Herad ransomware;
- Restore them.
Use Windows Previous Versions feature for data recovery processes:
If you have enabled System Restore in the past, this method might appear very helpful to you.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Using Shadow Explorer might solve data encryption problems:
If Shadow Volume Copies of your files remain safe, you can give this method a try.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
There is only the STOP decrypter released recently as experts are still working on the decryption tool of Herad virus.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Herad and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Shadow Copy. Wikipedia. The free encyclopedia.
- ^ USB Flash Drive. Techopedia. Tech Terms and Definitions.
- ^ NoVirus.uk. NoVirus. Spyware and security news.







