Like Dark browser hijacker (Free Instructions)
Like Dark browser hijacker Removal Guide
What is Like Dark browser hijacker?
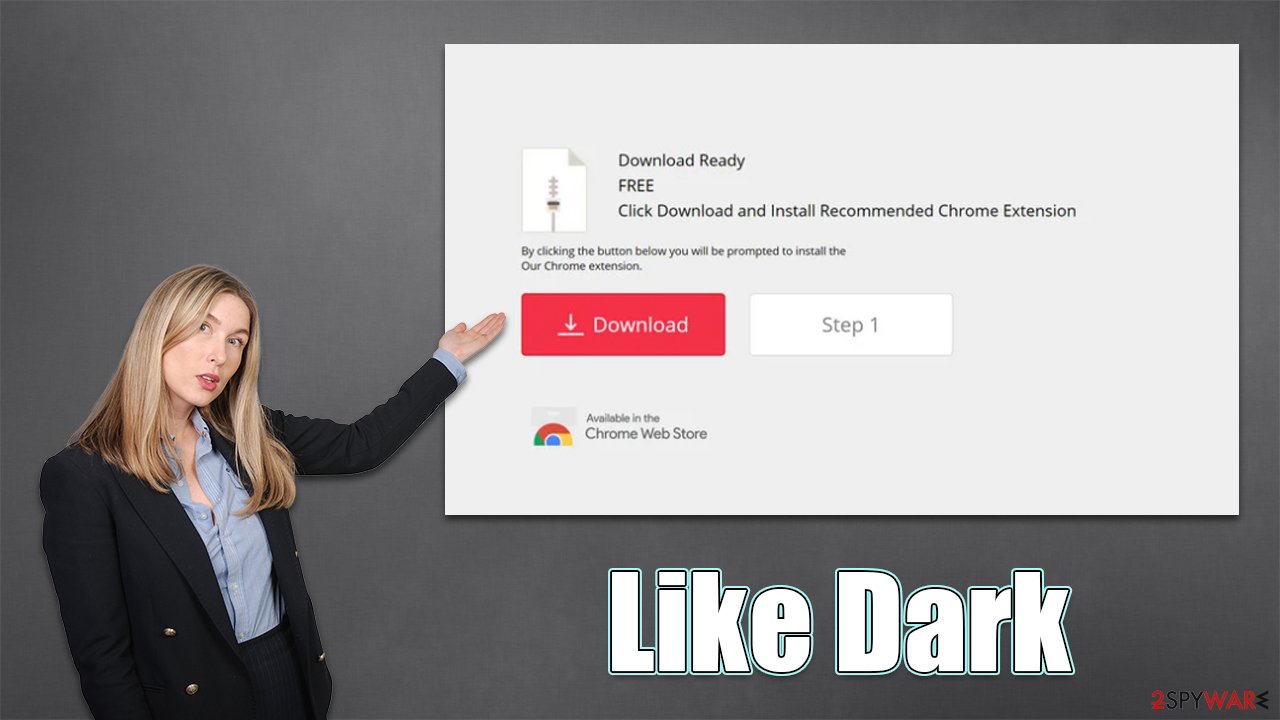
Like Dark is a potentially unwanted application that shows ads when you search the web

Like Dark is a browser extension that promises to provide a simple dark mode for all the pages that you access when browsing the web. In reality, upon installation, the app would hijack[1] the homepage and other preferences of Google Chrome, Mozilla Firefox, MS Edge, or another compatible browser.
Due to the presence of the app, you can expect to see modifications to the search results, as they would be filled with sponsored links and ads. Likewise, the search provider might be swapped to Yahoo, Bing, or another one, which would already result in a rather annoying experience for most.
The advertisements might also be seen on other visited websites, and users might be more likely to encounter phishing, scam, or similar misleading websites while browsing the web. Like Dark might also track user information in the background and share it with third parties. We recommend removing the app for a better browsing experience.
| Name | Like Dark |
|---|---|
| Type | Browser hijacker, potentially unwanted application |
| Distribution | Software bundles, ads, redirects |
| Symptoms | Homepage and new tab address hijacked by the extension; promotional links are displayed as top search results; intrusive ads on various visited websites |
| Risks | Installation of other potentially unwanted programs/malware, personal data disclosure to unknown parties, monetary loss |
| Elimination | To remove the unwanted browser extension, you should access your browser's settings section. You should also check for other PUPs or malware with an SpyHunter 5Combo Cleaner anti-malware |
| Other tips | We recommend scanning the system with PC repair and maintenance utility FortectIntego to remove leftover files and ensure system operation integrity |
The dark mode browser hijacker family
Browser hijackers are relatively widespread, and there are many families out there. In this case, Like Dark is just one of many browser extensions that is a mere copy of its previous versions – Flow Dark, Mini Dark, Real Dark, and many others. Evidently, the name is not the only thing that resembles those earlier versions, as they are just mere copies of one another.
It is not uncommon for potentially unwanted browser extensions to be rebranded and offered as brand new apps, despite them having no differences in terms of functionality. It is easy to do and helps to avoid bad publicity.
Speaking of functionality, Like Dark is not different from its predecessors – it seemingly offers a dark mode for all visited pages. However, this feature is already included in most modern web browsers, and you can swap to dark mode via the settings menu. This makes the application rather useless.
Tips to avoid unintentional installation
If you have noticed an application on your system or browser you think you have never installed, it is likely that it got in along with freeware you downloaded from third-party sources. Software bundling[2] is one of the most commonly used distribution techniques for browser hijackers and other PUPs (in some cases, even malware), as it works particularly well for those who do not pay close attention to the installation process of new programs.
For example, users are known to simply click “Next” several times until the process is finished and the desired app is installed. What they didn't notice was that there were pre-ticked checkmarks or misplaced buttons during the installation process, which automatically allowed the installer to download and implement optional components automatically.
Thus, you should always pay close attention to the installation process of new apps – read the fine print, watch out for misplaced buttons, pre-ticked boxes, and, most importantly, always choose Advanced mode instead of Recommended one.
PUPs might also spread via misleading messages and ads you may encounter while browsing the web (usually, less trustworthy websites). You might be told that you have to update some popular software installed on your device, for example, Flash Player or Chrome browser. Note that Flash has been discontinued so all requests to update it are fake.[3]
Once launched, the installer would install a potentially unwanted application instead, with you thinking that you installed an update instead. Please don't get fooled by these methods, as you might be tricked into installing dangerous programs on your system, let alone browser hijackers.
Removal of Like Dark browser hijacker
Evidently, to remove the browser hijacker, you have to uninstall the extension from Chrome or another browser that you use. This process is relatively easy, although if you have never done this before, we provide the instructions below. Note that if you notice other add-ons you have never installed yourself, remove them at once.
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Mozilla Firefox
- Open the Mozilla Firefox browser and click on the Menu (three horizontal lines at the window's top-right).
- Select Add-ons.
- Here, select the unwanted plugin and click Remove.

MS Edge (Chromium)
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

MS Edge (legacy)
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

To stop potentially unwanted programs and other third parties from tracking your data, you should clean your browser caches at least sometimes. This is particularly useful after the removal of PUPs. You can proceed with the instructions below or employ powerful optimization software FortectIntego, as it could automatically do a lot of maintenance work.
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content, and press Clear.

MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

MS Edge (legacy)
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Finally, to ensure that your device is not infected with more nasty stuff (you might never know until you check your system, as most aggressive adware and malware are stealthy), you should scan your system with Malwarebytes or SpyHunter 5Combo Cleaner security software.
How to prevent from getting browser hijacker
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ What Is Browser Hijacking?. Kaspersky. Resource Center.
- ^ Bundled software. Computer Hope. Free computer help.
- ^ Tim Brookes. Adobe Flash is Dead: Here’s What That Means. How-To Geek. Site that explains technology.
