Login Session Authentication scam email (fake) - Free Guide
Login Session Authentication scam email Removal Guide
What is Login Session Authentication scam email?
Login Session Authentication scam email tries to gain access to users' passwords
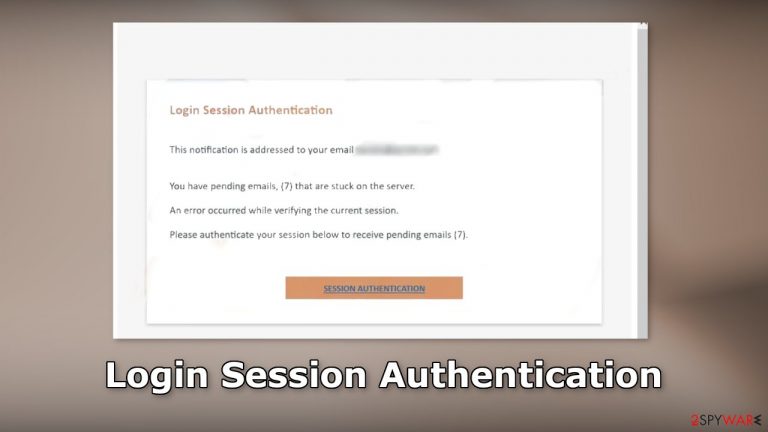
Login Session Authentication is a fake message entirely crafted by crooks to lure out users' login details. The email is made to look like an important message from the email service provider. Users are told that several emails are “stuck” and they need to authenticate a session to receive them.
| NAME | Login Session Authentication scam email |
| TYPE | Phishing attempt; fraud |
| SYMPTOMS | Users receive a message, saying that they have several pending emails that are stuck |
| DANGERS | The email scam can lead to stolen accounts, unauthorized purchases, identity theft, or virus infections |
| ELIMINATION | If you clicked on any malicious links, you should scan your machine with anti-malware tools |
| FURTHER STEPS | Use FortectIntego to clear your browsers and get rid of any remaining damage |
Social engineering methods
The full message in the Login Session Authentication scam email reads as follows:
Subject: Authentication error in ******** on 8/8/2022 11:04:04 a.m.
Login Session Authentication
This notification is addressed to your email ********
You have pending emails, (7) that are stuck on the server.
An error occurred while verifying the current session.
Please authenticate your session below to receive pending emails (7).
SESSION AUTHENTICATION
This email was sent to ******** because it contains important information about your account. If you previously unsubscribed from Identity Guard®️ marketing emails, you will no longer receive special offers but will continue to receive emails related to your account. If you believe you have received this email in error, please forward it to our customer service at ********
We will never ask you for personal information in an email. We respect your privacy. If you no longer wish to receive marketing emails from Identity Guard®️, you can unsubscribe at any time.
2021 ******** Inc.
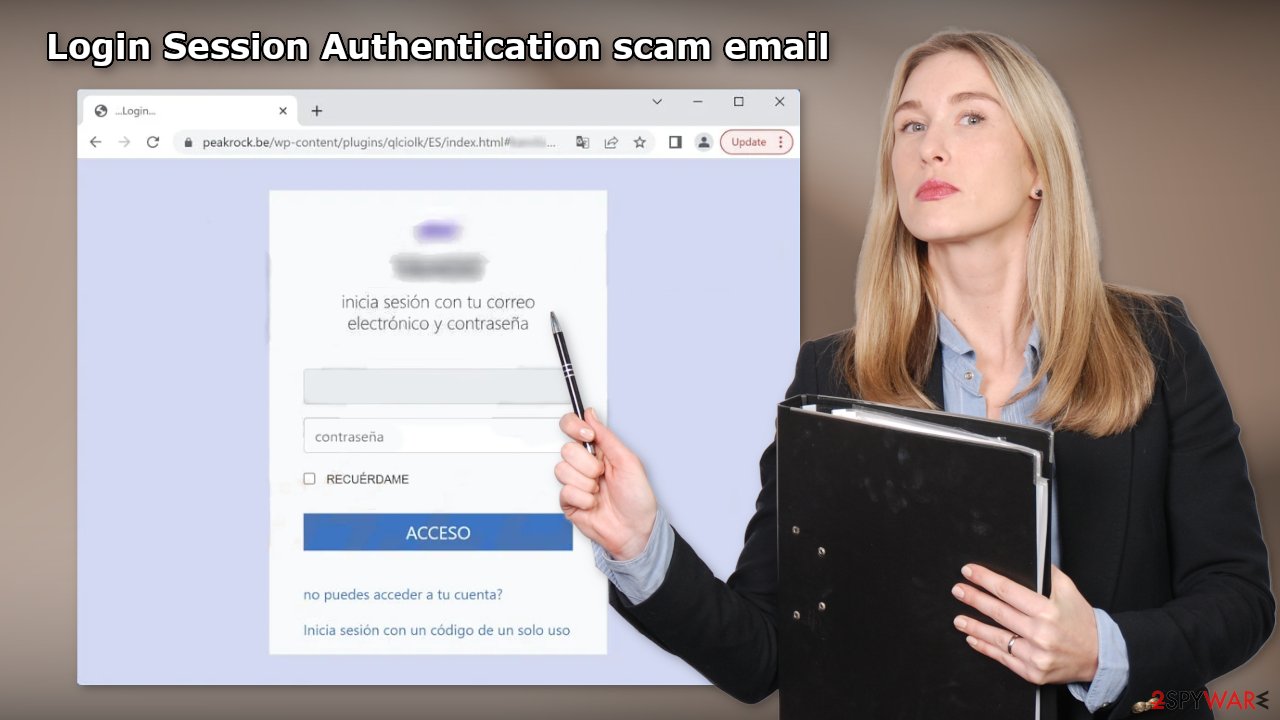
The email says that an error occurred while trying to verify a current session so users cannot receive emails. They are asked to press the “SESSION AUTHENTICATION” button to fix the issue. However, when users do that, a phishing[1] website appears that looks like a login window of their email provider.
If users enter their email address and password into the login window, they give away their details to fraudsters. With that information, crooks can steal several accounts if people use the same password. If you have fallen for this scam, we urge you to change your passwords as soon as possible.
Email is used quite frequently to extract personal information. We previously wrote about many other email scams, like Webmail Manager, FedEx Corporation, and Geek Squad. Most of the time, fraudsters use social engineering techniques[2] to disguise the emails as important and urgent letters from well-known companies to not cause any suspicion.
If you receive an email that you doubt is real, you should always contact the company's support that the email supposedly came from and ask them if the email address that you received the message from, belongs to them. You can also compare previous emails that you received from that company and see if the branding, logos, and style are the same. Read the message fully, and if you find any grammar or spelling mistakes, there is a big chance that the email is fake.
Check your system for malware infections
If you opened any shady email attachments or clicked on unknown links, you might have been infected by malware.[3] Crooks often use email to spread their malicious programs. They can do it by including an infected attachment or malicious links.
We recommend using SpyHunter 5Combo Cleaner or Malwarebytes security tools that will scan your machine, eliminate it, and prevent such infections in the future by giving you a warning before a malicious program can make any changes. Crooks often disguise their malicious programs as “handy” tools so they would be more difficult to identify for the average user.
People also often fail to eliminate all the related files and entries which could lead to the renewal of an infection. The program could have any name and icon, so this step is best performed by anti-malware tools. However, if manual removal is what you prefer, we have instructions for Windows and Mac machines:
Windows 10/8:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

Windows 7/XP:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Mac:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Repair the damaged operating system
Performance, stability, and usability issues, to the point where a complete Windows reinstall is required, are expected after malware infection. These types of infections can alter the Windows registry database, damage vital bootup and other sections, delete or corrupt DLL files, etc. Once a system file is damaged by malware, antivirus software is not able to repair it.
This is why FortectIntego was developed. It can fix a lot of the damage caused by an infection like this. Blue Screen errors,[4] freezes, registry errors, damaged DLLs, etc., can make your computer completely unusable. By using this maintenance tool, you could avoid Windows reinstallation.
- Download the application by clicking on the link above
- Click on the ReimageRepair.exe
- If User Account Control (UAC) shows up, select Yes
- Press Install and wait till the program finishes the installation process
- The analysis of your machine will begin immediately
- Once complete, check the results – they will be listed in the Summary
- You can now click on each of the issues and fix them manually
- If you see many problems that you find difficult to fix, we recommend you purchase the license and fix them automatically.

How to prevent from getting spam tools
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Phishing. Wikipedia, the free encyclopedia.
- ^ Cynthia Gonzalez. Top 8 Social Engineering Techniques and How to Prevent Them [2022]. Exabeam. Information Security.
- ^ Malware. Malwarebytes. Cybersecurity Basics.
- ^ Tim Fisher. Blue Screen of Death (BSOD). Lifewire. Software and Apps.
