Mughthesec (Virus Removal Instructions) - Free Guide
Mughthesec Removal Guide
What is Mughthesec?
Mughthesec – Mac virus that might remain undetected due to its effective evasion techniques

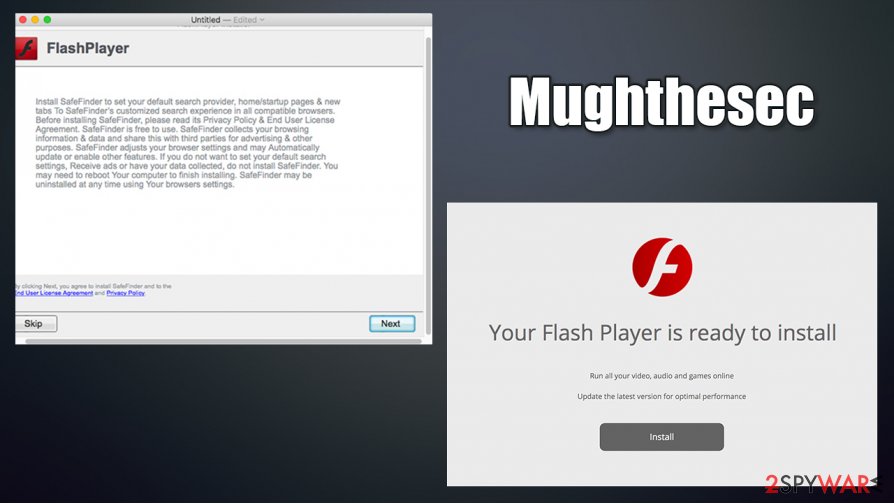
Mughthesec is a type of malware that usually attaches itself to Safari, Google Chrome, or another browser as an extension, although it also drops files on the system. Designed strictly for Macs, this malicious program gains access to the device behind users' backs, namely, fake Flash Player installers that could be encountered on malicious websites around the internet. These might be titled Player.dmg, while, during the installation, users might only see an Installer.app shown to them.
Once installed, the Mughthesec virus drops multiple malicious .plist files and establishes persistence by evading security software. It also installs several malicious apps designed for Macs, including the notorious scarware[1] Advanced Mac Cleaner. It also hijacks users' web browsers, sets the homepage to a.akamaihd.net, and delivers intrusive advertisements and sponsored links on a regular basis. Hence, its main goal is to gain revenue from ads and remain undetected on the infected machine for as long as possible.
| Name | Mughthesec |
| Type | Mac virus, adware |
| Distribution | This malware is typically installed via fake Flash Player updates |
| Dangers | Malicious actors could download additional payloads on the infected machine, steal information, and perform other nefarious actions while controlling the device remotely |
| Related files | Installer.app, Player.dmg, FlashPlayerInstaller |
| Removal | You can attempt to uninstall unwanted programs manually, as we explain below. However, the best results can only be achieved by using reputable security software, such as SpyHunter 5Combo Cleaner |
| Additional steps | After you eliminate the threat from your machine, you should change all your passwords and then perform repeated scan with FortectIntego to clean malware leftovers |
Fake Flash Player updates have been used to spread malware around for ages now, and Mac users are pretty much accustomed to this type of online scams. Upon accessing a malicious website, visitors are presented with a fake version of the plugin, with the claim that it is needed in order to display website contents or play multimedia.
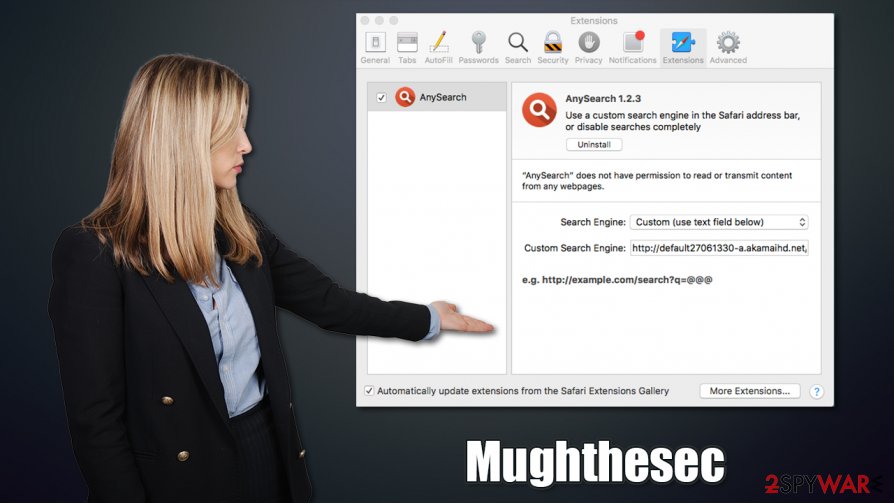
Unfortunately, to this day, users are still getting deceived by this old trick and end up installing potentially unwanted programs or malware on their systems. There could be many apps that would be disguised as the Mughthesec virus, thus making it virtually impossible to detect if the user is unaware that it is installed in the first place. For example, UniversalWebResults or AnySearch were found to be one of the main culprits of the infection.
Once installed, malware would deliver a pop-up, asking users to install the following applications:
These apps are very typical adware designed to use scam techniques to make users buy stuff online. Do not allow these to be installed on your system, as you will only infect your device further! After that, users will see their browsers completely messed up, as their homepage settings would be altered, and results redirected to Yahoo.
What is particularly interesting about this malware is its ability to avoid detection by most security software due to its effective evasion technique. Once launched, it deploys a binary that includes the names of the most common security applications used on Mac devices. However, updated versions of security software should be able to detect and stop the infiltration of the virus.
Due to malware's nature, one of the main ways to detect it on a Mac is by using a powerful Firewall. It can blog the insecure connection when the installed tries to establish it to download its malicious files onto a computer.
Another interesting feature of Mughthesec malware is that it tries to avoid analysis completely when it detects that a virtual machine is used. According to researchers:[2]
<…>it turns out that the installer actually doesn't do anything malicious, (besides actually installing a legit copy of Flash), if it detects it running in VM.
Nonetheless, it is important to clean the system properly when trying to remove Mughthesec virus from your system fully, and you might have to employ several tools for that, combining it with the manual instructions we provide below. FortectIntego can also be used as a tool to clean the leftovers of the virus if such need arises.
Fake Flash Player installers are prevalent on Macs – learn to avoid them
Flash Player has been terminated fully by Adobe in January 2021 and is no longer supported.[3] From a security standpoint, it is definitely good riddance, as this plugin has been possibly the most exploited tool by cybercriminals. There are two ways threat actors employ it for malicious deeds:
- Use fake installers to trick users into installing PUPs or malware;
- Exploit numerous software vulnerabilities found within the plugin.
Therefore, without exceptions, you should simply not use Flash – even the legitimate version. There is simply no need for it, as it has long been replaced with new technologies such as HTML 5. All the claims that it needs to be updated in order to view some online content are fake and a scam, so you should never listen to these requests.
While some fake installers may be signed with a valid certificate (making the infiltration of malware a much easier process, as signed files bypass the built-in Gatekeeper protection), most are not, so security software should be able to detect malicious versions of such files easily.
Manual Mughthesec removal might not be a straightforward process
In order to remove Mughthesec virus from your device, you need to eliminate all of its components, along with those that were brought in during the infection of the system. It includes the following files and folders:
~/Library/Application Support/com.Mughthesec/Mughthesec
~/Library/LaunchAgents/com.Mughthesec.plist
You also need to use launchctl to unload the payload that is running in the background with the following command:
launchctl unload ~/Library/LaunchAgents/com.Mughthesec.plist
Finally, you need to uninstall Any Search extension, along with all other unrecognized components on your browsers. To find out how to do that, you should check the instructions below.
However, if you are a novice computer user, we highly recommend performing automatic Mughthesec removal with an updated anti-malware software. You will not have to worry about malicious .plist files, and other components dropped by malware, as security applications are capable of automatically finding and deleting them.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Mughthesec. Follow these steps
Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
Make sure you uninstall Any Search extension from your Safari web browser, along with other suspicious ones. If the need arises, you can reset your web browser to bring it to its default state:
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Mughthesec registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting adware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Scareware. Wikipedia. The free encyclopedia.
- ^ Gavriel State. WTF is Mughthesec!?. Objective-See. Blog.
- ^ Mayank Parmar. Windows 10 update to kill off Adobe Flash Player permanently. Windows Latest. Microsoft product news and reviews.
