OperativeEngine Mac virus (guide) - Chrome, Firefox, IE, Edge
OperativeEngine Mac virus Removal Guide
What is OperativeEngine Mac virus?
OperativeEngine is a potentially unwanted program with plenty of malicious features
Adload is an adware family that targets macOS users exclusively – OperativeEngine is one of the latest additions to this expansive strain. While many sources brand it as adware with browser-hijacking qualities, considering how much more severe the impact of its presence is, it can easily fall into the malware category. The application usually is not installed intentionally, as virus authors commonly use one of the following deceptive methods for propagation:
- Bundled software, typically downloaded from high-risk websites that distribute pirated apps;
- Fake Flash Player updates that can be encountered all over the web by accident.
Macs are usually considered to be more secure machines, as they always ask users to enter their credentials if an application is being installed from an unofficial source. However, since people believe that what they are installing is safe, they give OperativeEngine the consent to be installed with elevated permission on the system. This is where the malicious activities of the virus begin.
Those infected would immediately notice that there is an outsider on their web browsers – be it Safari, Google Chrome, or Mozilla Firefox – an extension that uses an icon of a magnifying glass in the teal background. The main goal of adware is to show users pop-ups, in-text links, banners, deals, offers, and other commercial material, and that is why the browser settings are instantly changed. Adload usually alters the search provider to Safe Finder and redirects search results to Yahoo, although this might differ from version to version.
However, this is just the tip of the iceberg of what is actually going on behind the scenes. In this article, we will explain how this malicious app works and how to eliminate it effectively.
| Name | OperativeEngine |
| Type | Mac virus, adware |
| Malware family | Adload adware strain, which targets macOS devices. Previous versions: SearchPrimaryData, SmartTechLookup, ExtendedService |
| Installation | Usually spread via fake Flash Player installers or bundled along illegal software downloaded from torrent and similar sites |
| Symptoms | OperativeEngine extension installed on the browser, along with an application of the same name; search and browsing settings altered to Safe Finder or another search provider; New profiles and login items set up on the account; ads and redirects lead to malicious sites |
| Removal | Manual elimination of Mac malware is possible, although not recommended to novice users. Instead, perform a full system scan with SpyHunter 5Combo Cleaner and remove all the malicious components automatically |
| System optimization | After you terminate the infection with all its associated components, we recommend you also scan your machine with FortectIntego for best results |
OperativeEngine distribution and ways to avoid it
As we already explained, most users would not install the app on purpose simply because it does not serve any. Some potentially unwanted applications seduce users with promises of a “faster” and “better” browsing experience, all while tracking them and showing them ads non-stop, all while providing no additional features. This is how users install PUAs themselves – they don't realize that they are useless.
When it comes to OperativeEngine, its distribution methods are on par with those used by cybercriminals. Fake Flash Player updates have been used to spread malware for years, and the problem is becoming even more severe for Apple device users in recent years.
Additionally, software cracks and pirated software websites are breeding grounds for malware. For example, one of the most prominent ransomware infections Djvu is spread almost exclusively via cracks or keygens,[1] infecting hundreds of people daily.
In order to void installation of Adload adware (as well as any other type of unwanted or malicious software), follow these tips provided by Novirus.uk[2] experts:
- Flash Player was terminated by Adobe in early 2021 and is no longer available as a plugin. It has been long replaced by newer technologies used for multimedia, and the fact that it had multiple vulnerabilities[3] made it insecure. In other words, users no longer require it to be installed on their devices, and all the requests to have them are fake.
- Software cracks and pirated programs should be avoided at all costs, as websites distributing them are usually very poorly regulated. They also employ ads from insecure advertising networks, which allows cybercriminals to insert malicious scripts which, under certain circumstances, would install malware without user interaction whatsoever.
The dangers of Adload
Once users enter their Apple ID before the installation is initiated, they give permission for the app to operate on a higher level in the system environment. There are several stages of the installation process – it ensures that macOS is hijacked, and users are unable to get rid of malware easily.
In order to stay as long on the system as possible, the app makes use of the built-in AppleScript, which tricks XProtect (the built-in anti-malware system from Apple) to trust it. This is one of the main reasons how the app can operate without any interruption and proceed with its malicious activities. However, all these changes are something regular computer users would never notice.
What they do see, however, is the extension that is installed on the web browser. By hijacking its homepage and new tab address, malware guarantees that users will be using the predetermined search provider, which is not Google or the default Safari search.
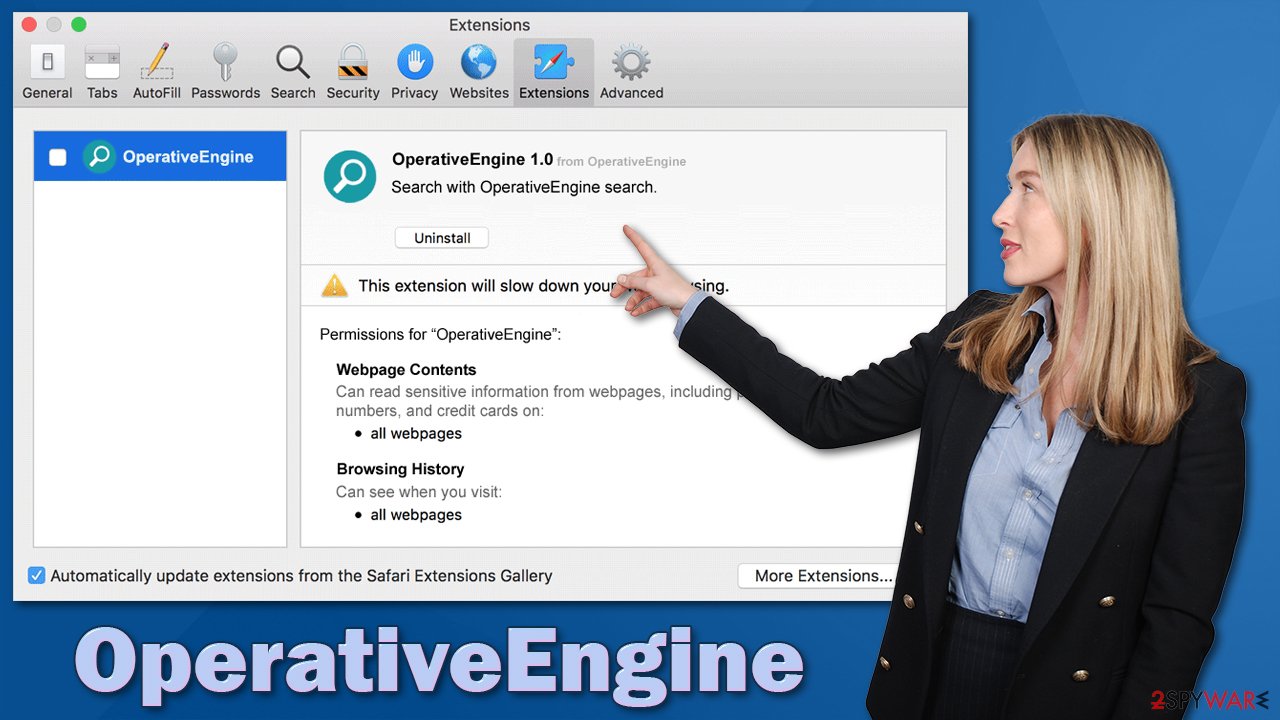
While using it, people quickly notice that their searches are filled with sponsored links and ads, which, once clicked, might lead to even more insecure places. Besides, it is likely to come across even more ads while browsing the web. The add-on is also capable of reading and harvesting sensitive information:
Permissions for “OperativeEngine”:
Webpage Contents
Can read sensitive information from webpages, including passwords, phone numbers, and credit cars on all webpagesBrowsing History
Can see when you visit all webpages
The worst part about this is that the extension is impossible to remove in a regular way, as the Remove button is usually grayed out. Even if it is not, the app returns very swiftly, hijacking the browser once again. As evident, you should not rely on this app and remove it as soon as possible.
Removal steps
As it is clear by now, getting rid of this intruder is not as easy as many other adware apps. Not only does it trick the automatic Mac protection to run freely, but it also populates dozens of .plist files, establishes Login items and new profiles – all these elements are used for persistence. this is one of the main reasons why many of its components might return despite being deleted.
If you are a regular user, we recommend you avoid meddling with system files and rather employ SpyHunter 5Combo Cleaner or Malwarebytes to do the job for you. We also provide manual elimination steps below.
- Open Applications folder
- Select Utilities
- Double-click Activity Monitor
- Here, look for suspicious processes related to adware and use the Force Quit command to shut them down
- Go back to the Applications folder
- Find ExtendedService in the list and move it to Trash.
The above steps might not be possible. If that is the case, you should look for malicious Profiles/Login Items to terminate:
- Go to Preferences and select Accounts
- Click Login items and delete everything suspicious
- Next, pick System Preferences > Users & Groups
- Find Profiles and remove unwanted profiles from the list.
Finally, it would help if you looked for leftovers – .plist files. These are configuration files that might enable adware to work more efficiently:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any suspicious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and delete all the related .plist files.

Regardless of which elimination option you choose, you should also take care of your web browser, as the leftovers might still be there. Also, it is generally recommended to clean cookies, cache, and other web data from time to time as a good practice for privacy and security. We recommend using FortectIntego for this, although it can also be done manually:
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Chome
- Click on Menu and choose Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies, and other site data, as well as Cached images and files.
- Click Clear data.

Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content, and press Clear.

How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Lawrence Abrams. Djvu Ransomware Spreading New .TRO Variant Through Cracks & Adware Bundles. Bleeping Computer. Technology news and support.
- ^ Novirus. Novirus. Cybersecurity advice and malware insights.
- ^ Flash Player : Security Vulnerabilities. CVE Details. Security vulnerability database.
