TabX browser extension (Chrome, Firefox, IE, Edge) - Tutorial
TabX browser extension Removal Guide
What is TabX browser extension?
TabX is a potentially unwanted browser extension that takes over users' browsers upon installation
TabX is a browser hijacker that you may find attached to your Google Chrome, MS Edge, or another browser out of a sudden. If you are wondering where this extension came from, it is likely that you have it installed along with freeware[1] downloaded from third-party websites, although fake updates and similar misleading ads could be the reason also.
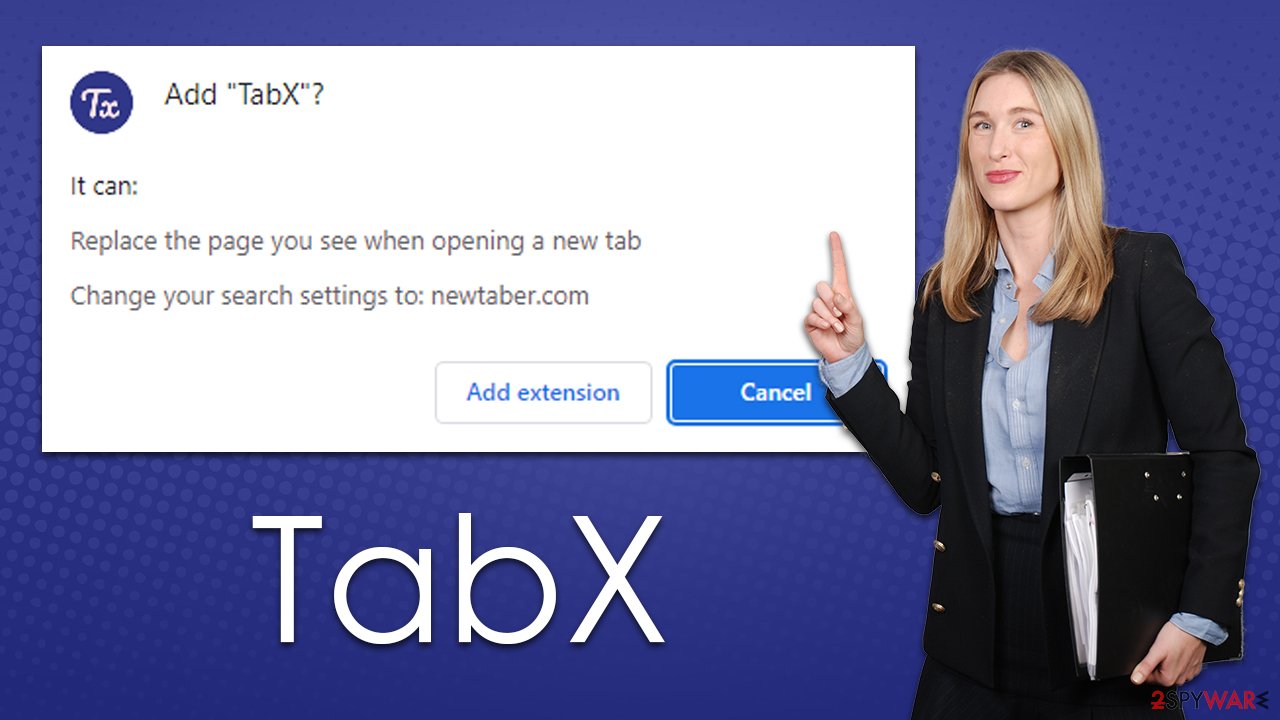
Once installed, TabX hijack occurs immediately, and people can quickly see that their browsers are no longer the same. To be more precise, the homepage and new tab are now set to newtaber.com – a dubious search engine.
By using the search box appended to the start page, as well as the URL bar, users would be subjected to alternative search results which manifest as sponsored links at the top. Likewise, the app may use a different search provider, for example, Yahoo, Bing, Searchlee, and similar. To top it all off, the TabX hijacker would track user information continuously, which may put their privacy at risk.
| Name | TabX |
| Type | Browser hijacker, potentially unwanted browser extension |
| Distribution | Software bundles, ads, redirects |
| Symptoms | Homepage and new tab address hijacked by the extension; homepage and new tab set to newtaber.com; promotional links are displayed as top search results; intrusive ads on various visited websites |
| Risks | Data tracking from various third parties, exposure to malicious ads, redirects to phishing sites |
| Removal | You can eliminate the browser hijacker by adjusting your browser's settings. Scanning your system with SpyHunter 5Combo Cleaner security software will confirm that there is no adware or malware running in the background |
| Other tips | We recommend that you use the FortectIntego tool to clean your web browsers and repair any damaged system files after removing all potentially unwanted programs. |
Browser hijackers: how do they spread, and how to avoid them?
The popularity and usage of a browser hijacker, from its creators' point of view, highly depends on how the app is distributed and marketed. Unfortunately, potentially unwanted applications are known for their deceptive distribution methods, and the TabX virus is not an exception.
The majority of users like to get free programs from third-party websites, and that's where the most unwanted applications originate. People frequently skip over installation procedures and clickthrough phases without reading the instructions, allowing optional components to get in.
To prevent this, you should always pay close attention to the installation process of new applications you download from unofficial sources, although keep in mind that software cracks and similar pirated program sites should be avoided altogether, as you may get infected with ransomware[2] or other nasty malware. Pick Advanced/Custom settings when presented with such an option and remove all the ticks from pre-ticked checkboxes.
Alternatively, you could also download the unwanted extension after being tricked by fake websites that promote them, for example, Accelers.cloud, Adshome.xyz, or Updatefreeintenselytheproduct.vip. It is recommended not to pay attention to messages which claim that something is missing or needs to be updated – you are likely to install potentially unwanted or malicious software on your device.
Why you shouldn't trust browser hijackers
Although browser hijackers rarely result in malware infections, the sponsored links provided at the top might include ads for potentially unwanted applications. Thus, if you have a PUP installed, you are more likely to see ads that promote other browser hijackers or adware.
Other than the aggravating and potentially hazardous advertising, TabX is also recognized for its data monitoring abilities. Search queries, visited websites, clicked links, timestamps, technical device information, ISP, and similar information are usually gathered automatically using tracking cookies, web beacons[3], pixels, and various tracking systems. This may lead to potential privacy concerns that should be avoided.
TabX is a browser hijacker, which means it changes your browser settings and prevents you from reversing these changes. In order to stop the redirects to alternative search results, you must remove the TabX extension from your browser. We explain how to do this below.
How to remove the unwanted extension from your system
Browser extensions are the most popular form of potentially unwanted programs, and TabX spreads as such. The extension is easy to produce and maintain, and it also provides enough functionality to push ads to those who have it installed. There are a few other things you should do after, but let's start with the elimination of the add-on.
Step 1. Remove the extension
To get rid of the extension, you should access browser settings. It is worth noting that most modern browsers have the “Extensions” button next to the settings menu/URL bar – you can remove unwanted apps using this method as well. Alternatively, proceed with the following steps:
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the window's top-right).
- Select Add-ons.
- In here, select the unwanted plugin and click Remove.

MS Edge (Chromium)
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

MS Edge (legacy)
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Step 2. Clean browser caches
As previously mentioned, browser hijackers use various items to track users' daily browsing sessions. While most of the information is anonymous, some of it may be private. For example, if search queries are collected, they may include details such as names or phone numbers, making them private data. Likewise, IP address is considered personally identifiable information in many US jurisdictions and countries.
You can stop data tracking with the help of the FortectIntego maintenance utility or by following the instructions below:
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content, and press Clear.

MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

MS Edge (legacy)
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Step 3. Scan with anti-malware
Your final task is to scan your system with anti-malware software. This is especially relevant if you frequent high-risk websites (torrents, X-rated, gambling sites) or have no clue where the hijacker came from in the first place, so there could be other potentially unwanted or malicious programs running in the background without you knowing anything about it. For best results, employ SpyHunter 5Combo Cleaner or Malwarebytes, although any other security tool should suffice as well.
How to prevent from getting browser hijacker
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ What Is Freeware?. Lifewire. Tech News, Reviews, Help & How-Tos.
- ^ Ransomware. Imperva. Application and data protection.
- ^ Cookies and Web Beacons. NTT. NTT Communications.
