We have detected a Trojan virus (Removal Guide) - Microsoft Support Scam
We have detected a Trojan virus Removal Guide
What is We have detected a Trojan virus?
We have detected a Trojan virus – a typical browser scam that tries to intimidate users by claiming virus infections
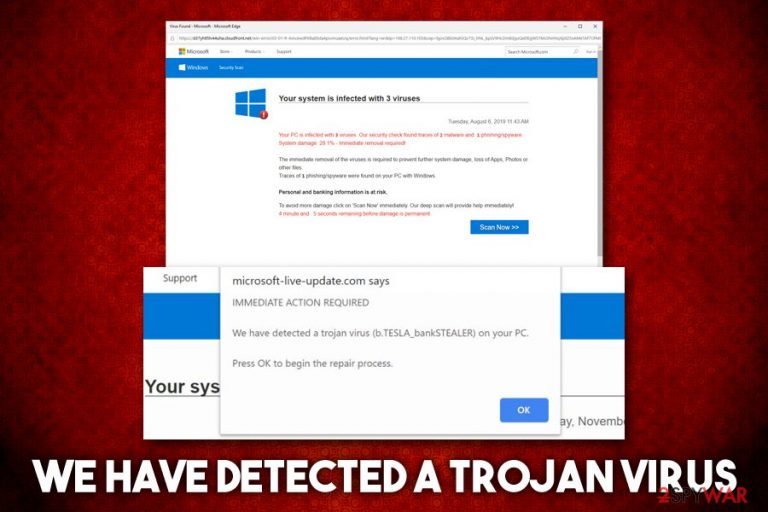
We have detected a Trojan virus is a fake alert that users might encounter on Google Chrome, Mozilla Firefox, Internet Explorer, or any other browser. The pop-up message claims that your computer is allegedly infected with b.TESLA_bankSTEALER, E.tre456_worm or other malware, and that immediate action is required in order to stop the devastating consequences like money and personal information disclosure to cybercriminals. In reality, We have detected a Trojan virus is nothing but a scam that should not be interacted with.
Crooks behind the scam use a well-known social engineering[1] technique of intimidation and count on users who are less familiar with malware and computer operation techniques. Additionally, We have detected a Trojan virus hoax also impersonates a well-known theme of Microsoft or Apple, implementing logos and web design of the tech giants. As evident, it is all fake and done to make victims believe that the party showing these fake notifications is a trusted company.
| Name | We have detected a Trojan virus |
| Type | Scam |
| Category | Fake alerts, redirects, intrusive ads and other symptoms might indicate adware infection |
| Scam family | Your system is infected with 3 viruses, IMMEDIATE ACTION REQUIRED |
| Related fake virus names | b.TESLA_bankSTEALER, E.tre456_worm, Tapsnake CronDNS, Dubfishicv |
| Infiltration | Users might start seeing fake alerts and redirects to suspicious sites due to adware infection. Nevertheless, they might encounter scam content after being redirected from another malicious site |
| Symptoms |
|
| Risks | Money loss, installation of other unwanted programs, personal data disclose to unknown parties or cybercriminals |
| Termination | If no computer infections are present, users should simply close down the tab that shows We have detected a Trojan virus scam message. However, it is mandatory to check the machine for adware – either by following our manual removal guide below or by scanning the machine with anti-malware software |
| Recovery & optimization | For best results, we suggest scanning your computer with FortectIntego – it can remedy the system that has been damaged by adware or malware infections |
We have detected a Trojan virus prompts might be triggered upon landing on one of the predetermined websites by accident, or be redirected by adware. The latter is known to deliver users intrusive pop-ups, in-text links, deals, offers, and other ads and install without acquiring proper permission from computer owners. Thus, while ignoring We have detected a Trojan virus alerts is the right thing to do, adware-induced redirects may need a much further investigation and actions to be taken for better online security.
Adware is usually installed with freeware/shareware applications from third-party sites – the developers incorporate optional components into installers without adequately disclosing them to end-users. This is done deliberately, as each of the installs provides profits from affiliates. Unfortunately, users then end up with potentially unwanted programs on their machines, which result in them being exposed to such online scams like We have detected a Trojan virus.
Most of the users who simply happened to stumble upon We have detected a Trojan virus scam should not pay attention to it and never download any suggest programs. We have detected a Trojan virus removal is only needed if the adware is also involved. To check that, we recommend following our instructions below or scanning the machine with anti-malware software. If PUPs are detected, they should be immediately terminated. To recover from unwanted consequences like program crashes or system slowdowns after adware infections, we suggest using FortectIntego.

The anatomy We have detected a Trojan virus scam
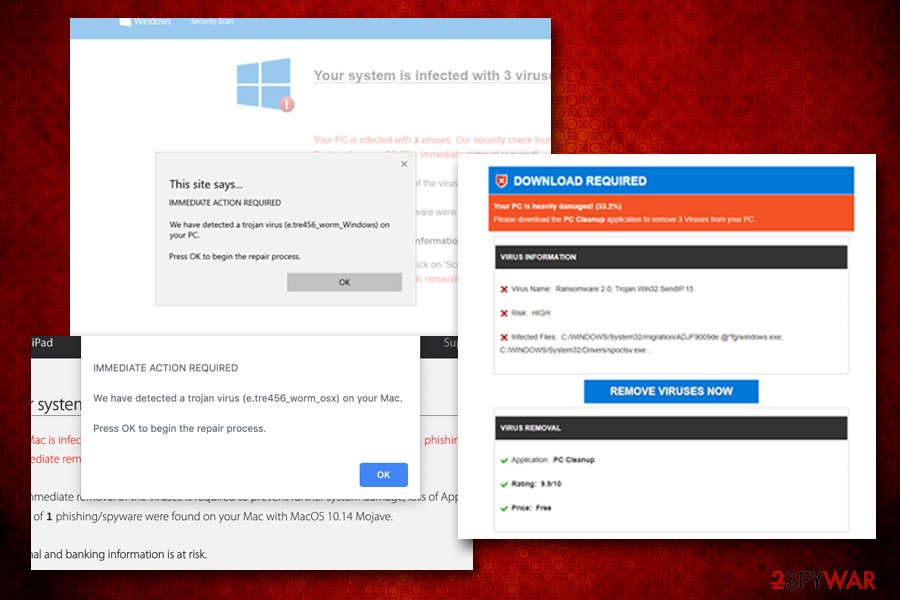
We have detected a Trojan virus belongs to one of the largest scam families around – Your system is infected with 3 viruses. This multi-stage social engineering attack usually begins with adware that directs users to potentially dangerous websites (nevertheless, some might simply land on the dangerous page by accident). In most of the cases, the domain names try to use words that are related to tech giants such as Microsoft or Apple – this is another social engineering trick.
Despite means how users end up on unsafe sites like Apple.com-mac-optimizing.live, Microsoft-live-update.com, the content remains the same, and the pop-up message that immediately shows up reads:
IMMEDIATE ACTION REQUIRED
We have detected a trojan virus (b.TESLA_bankSTEALER) on your PC.
Press OK to begin the repair process
Because crooks behind We have detected a trojan virus scam try to impersonate Microsoft, some users might believe these fake claims. However, it is important to notice that the domain name does not, in fact, comes from Microsoft. The real website would only include “microsoft.com” without any additional words – this is simply a way to confuse less experienced users.
Upon pressing OK, users would be presented with a threatening message, claiming that multiple viruses have already infected the system and that some of it are damaged. Malicious actors also come up with bogus timers that add to tension users may experience – it creates a sense of urgency and the need to act fast. Unfortunately, that is the worst thing that users who encounter We have detected a trojan virus scam can do, as they will be prompted to download bogus software to allegedly remove viruses found on the machine.
In most of the cases, the offered software is useless scareware[2] that will ask you to spend money on its full license after showing you more fake scan results, claiming damage to the computer. Do not download, install, or buy this software – it is a scam, and We have detected a trojan virus fake alert is used as a means to install PUPs or malware on your machine.
While there is a low chance that your system is infected with a trojan or something even more sinister, you should perform some checks just to be sure. Thus, the following actions to be taken after encountering We have detected a Trojan virus scam:
- Do not interact with the fake site and do not press the “Scan Now” button;
- Do not download anything suggested on the site;
- Close down the browser or the tab the malicious site content was displayed;
- Check our manual removal guide for PUPs below – you might be able to find unwanted apps installed by yourself;
- Scan your computer with anti-malware software;
- If adware or other infections are found, reset all the installed browsers.
Finally, adware or malware that induce We have detected a Trojan virus redirects might cause damage to your system, which might start crashing or showing error messages. To avoid that, we recommend maintaining system stability with FortectIntego.
Do not get tricked by software bundle packages and avoid adware infiltration
Experts[3] say that there are two different ways how adware might have ended up on your computer: you either installed it along with other software from third-party sites or you installed it deliberately without known that the app is ad-supported. If the latter is the case, we advise you to read up program reviews online before downloading anything, as they can often indicate if the app engages in dodgy practices post-installation.
Whoever, in most of the cases, users install PUPs with freeware, as they rarely pay close attention to the installation process of new programs. Unfortunately, but third-parties are happy to abuse this fact and often insert optional components into a single software package. While there is nothing illegal about offering users promotions, the way it is done matters a lot.
Unsolicited installation of software is something that is considered to be malicious behavior. Nevertheless, third-parties often can disguise by claiming that all the information was presented during the installation – and, technically, they will be correct. Software bundling often uses pre-ticked boxes, deceptive deals, misplaced buttons, and other techniques to make users miss the PUP. This way, they install adware on their systems without realizing it.
To avoid that, you should always pay close attention to the installation process of third party applications – uncheck all the boxes, decline all the deals, watch out for deceptive button placements and always opt for Advanced/Custom settings. Another important step is to stay away from pirated software and cracks – these can result in such dangerous threat infections like ransomware.[4]
We have detected a Trojan virus elimination guide
We have detected a Trojan virus removal depends on whether or not your system is infected with adware. Because PUPs travel in software bundles, you might not even be aware that your machine is affected in the first place. Nevertheless, finding the unwanted programs on the computer might be a challenge to some, especially if they use dozens of browser extensions from unknown origin or applications downloaded from less secure sites.
Therefore, we advise you to check your computer with anti-malware software if you are not that familiar with IT practices in order to avoid the uninstallation of the application that is actually needed. If you are confident enough – check the detailed instructions below and remove We have detected a Trojan virus adware yourself. Note that, if your system is clean, you should simply ignore the fake alert and never install anything offered on scam sites, although keeping a reliable security tool on the system is mandatory.
After you terminate adware, you should also reset all the installed browsers, as browser setting changes initiated by adware might only be reverted that way.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of We have detected a Trojan virus. Follow these steps
Uninstall from Windows
To remove We have detected a Trojan virus-related PUP, perform the following steps on your Windows machine:
Instructions for Windows 10/8 machines:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

If you are Windows 7/XP user, proceed with the following instructions:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Delete from macOS
Adware is a common problem for Mac users. Proceed with the following if you want to get rid of it:
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Microsoft Edge
Delete unwanted extensions from MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Clear cookies and other browser data:
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Restore new tab and homepage settings:
- Click the menu icon and choose Settings.
- Then find On startup section.
- Click Disable if you found any suspicious domain.
Reset MS Edge if the above steps did not work:
- Press on Ctrl + Shift + Esc to open Task Manager.
- Click on More details arrow at the bottom of the window.
- Select Details tab.
- Now scroll down and locate every entry with Microsoft Edge name in it. Right-click on each of them and select End Task to stop MS Edge from running.

If this solution failed to help you, you need to use an advanced Edge reset method. Note that you need to backup your data before proceeding.
- Find the following folder on your computer: C:\\Users\\%username%\\AppData\\Local\\Packages\\Microsoft.MicrosoftEdge_8wekyb3d8bbwe.
- Press Ctrl + A on your keyboard to select all folders.
- Right-click on them and pick Delete

- Now right-click on the Start button and pick Windows PowerShell (Admin).
- When the new window opens, copy and paste the following command, and then press Enter:
Get-AppXPackage -AllUsers -Name Microsoft.MicrosoftEdge | Foreach {Add-AppxPackage -DisableDevelopmentMode -Register “$($_.InstallLocation)\\AppXManifest.xml” -Verbose

Instructions for Chromium-based Edge
Delete extensions from MS Edge (Chromium):
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Clear cache and site data:
- Click on Menu and go to Settings.
- Select Privacy, search and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Reset Chromium-based MS Edge:
- Click on Menu and select Settings.
- On the left side, pick Reset settings.
- Select Restore settings to their default values.
- Confirm with Reset.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
Adware leaves traces in web browsers even after it is removed. Here's how to reset Google Chrome to avoid unwanted redirects and ads in the future:
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of We have detected a Trojan registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ What is Social Engineering?. Webroot. Security blog.
- ^ Scareware. Wikipedia. The free encyclopedia.
- ^ Bedynet. Bedynet. Cybersecurity news and insights.
- ^ Bradley Barth. Downloads of cracked software distribute ransomware via adware bundles. SC Magazine. Security news.
