WebAge Mac virus (Free Guide)
WebAge Mac virus Removal Guide
What is WebAge Mac virus?
WebAge is a malicious Mac application that can steal your personal data
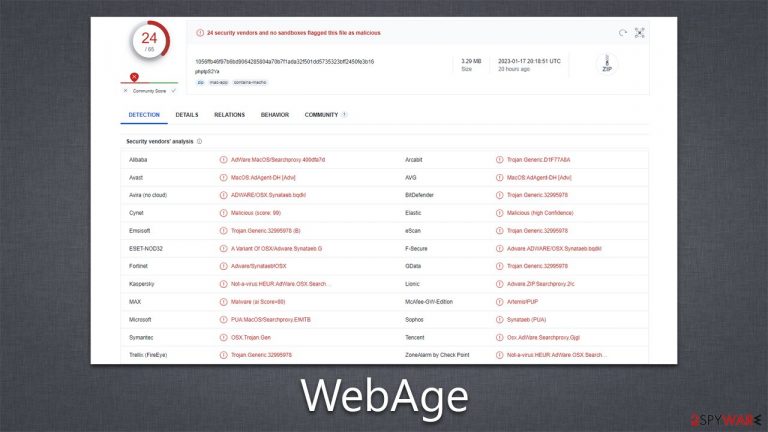
Cybercriminals have created WebAge, a malicious Mac app that can infect your device when you download malware-laced pirated software installers or interact with fake Flash Player updates. This virus stems from a well-known malware family Adload, which is known to bypass Apple's XProtect security system and alter various areas within the system in order for it to remain undetected. Furthermore, users unknowingly provide their credentials, allowing these changes to proceed without interruption.
One of the very first signs that someone may encounter is a change in behavior from their usual browser: Safari, Chrome, Firefox, and others. This alteration might be due to the WebAge extension, which has been installed – this could adjust homepage settings as well as other new tabs such that people would no longer have access to their default choices. Third parties can also insert alternative search providers accompanied by various associated issues like tracking data and an overabundance of sponsored links during every session.
| Name | WebAge |
| Type | Mac virus, adware, browser hijacker |
| Malware family | Adload |
| Distribution | Fake Flash Player installers or pirated software from high-risk sources |
| Symptoms | A new extension is downloaded to the browser, along with a matching app; search and browsing preferences are changed to use a different search engine; new user profiles and login items are created on the account; intrusive advertising and redirects |
| Removal | You can employ powerful security software to check your system for infections, for example, SpyHunter 5Combo Cleaner. The manual malware uninstall guide is also available below |
| System optimization | After you terminate the infection with all its associated components, we recommend you also scan your device with FortectIntego to clean your browsers and other leftover files from the virus |
How WebAge is spread and how to avoid other Adload versions
Adload is one of the most prominent malware families targeting Macs, with hundreds of variants under its belt – OperativeQueue, DigitalSection, and IdentityStack are among the most recent ones spreading around in the wild. Its success, at large, is dependent on its distribution, which is rather simple but highly effective.
Mac malware often spreads through the use of fake Adobe Flash Player installers. These installers are typically downloaded from untrusted websites or through email attachments and appear to be legitimate Adobe software. However, this plugin has been long discontinued by Adobe, and if you see any requests online to download Flash, you should ignore them because they are all fake.
Torrents are a method of downloading files through a peer-to-peer network, where users share files with each other. Cracks are illegal software modifications that bypass software's security features and allow the user to use the software without purchasing a license, and can also be downloaded from these illegal websites. It is possible for a Mac to become infected with malware if a user downloads a cracked version of software from a torrent, especially when they ignore warnings from security software.
To protect yourself from Adload malware, it's important only to download software from trusted sources and to be cautious of any unexpected or unsolicited emails or messages containing links or attachments. Additionally, it is recommended to run anti-malware software on your Mac and keep the software and the operating system updated regularly. Also, keep an eye on suspicious activity on your browser. Such as unexpected new extensions, pop-ups, and redirections. Be aware and take action if you see any of these signs.
How to remove the virus effectively
While Apple products are generally regarded as secure, this does not mean that they are immune from all sorts of viruses and malware. In reality, adware is one of the most common Mac security issues because users can be tricked into downloading something malicious without being aware it's unsafe. Even with safety measures in place, these kinds of threats may still find a way to get through if someone isn't paying close attention.
When installing WebAge, users are required to enter their Apple ID credentials, which allows the malware to perform actions as programmed by hackers and create new Login items, bypass the removal of security features and continue operating even if some components are removed.
To ensure your computer is free from viruses and malware, we highly recommend you use either SpyHunter 5Combo Cleaner or Malwarebytes security software. If manual removal is more to your liking, please follow the steps outlined below; however, be aware that this approach may not always eradicate the virus completely, as symptoms could return later on. No matter which method of removal you choose – manual or automatic – cleaning out web browsers should always be done for optimum results.
Remove the main app components
To guarantee successful malware removal, the first step is to shut down any background processes associated with it. To do this, open your Activity Monitor and follow these steps:
- Open Applications folder
- Select Utilities
- Double-click Activity Monitor
- Here, look for suspicious processes related to adware and use the Force Quit command to shut them down
- Go back to the Applications folder

- Find the virus name in the list and move it to Trash.
The PLIST files are small config files, also known as “Properly list.” They hold various user settings and hold information about certain applications.
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and delete all the related .plist files.

When the virus infiltrates, it will create new user profiles and login items to ensure continued presence. This is likely why you are unable to remove the application or extension from your system.
- Go to Preferences and select Accounts
- Click Login items and delete everything suspicious
- Next, pick System Preferences > Users & Groups
- Find Profiles and remove unwanted profiles from the list.
Finally, you should take care of your browsers by removing the extension component, although this may not always be possible, so you might have to reset the browser instead. To clean cached files automatically, you can employ the FortectIntego maintenance tool, although you can find manual steps below as well.
Getting rid of WebAge Mac virus. Follow these steps
Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

Remove from Google Chrome
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

How to prevent from getting mac viruses
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
