WouldLatest Mac virus (Free Guide)
WouldLatest Mac virus Removal Guide
What is WouldLatest Mac virus?
WouldLatest is a Mac virus that might put your personal safety at risk
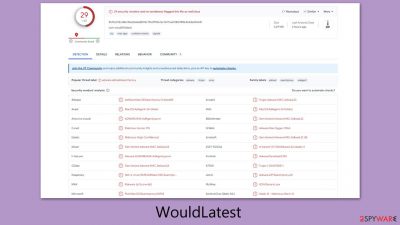
The recent emergence of the WouldLatest Mac virus, a new strain in the Adload malware family, presents a significant security risk for Mac users. This virus primarily targets web browsers, manipulating their function to redirect users to harmful websites and potentially extracting sensitive personal data. The intent behind this data extraction often includes unauthorized sales or misuse on various illicit platforms.
WouldLatest is particularly resilient, incorporating multiple components and sophisticated strategies to avoid detection and removal. This resilience poses a challenge for users, as incomplete removal attempts may lead to the virus reactivating and inflicting further damage on the system.
For Mac users, immediate and thorough action is essential to eliminate the WouldLatest virus and protect both the integrity of their systems and the confidentiality of their personal information. The following detailed guidance is aimed at assisting users in effectively removing this malware threat.
| Name | WouldLatest |
| Type | Mac virus, adware, browser hijacker |
| Malware family | Adload |
| Distribution | Third-party websites distributing pirated software, software bundles, fake Flash Player updates |
| Symptoms | An extension installed on the browser with elevated permissions, along with an application of the same name; new profiles and login items set up on the account; malicious ads shown during web browsing activities; search and browsing settings changed to another search provider |
| Removal | You can remove Mac malware effectively with the help of a powerful security tool, such as SpyHunter 5Combo Cleaner. If you want to attempt to get rid of the threat yourself, check the manual guide below |
| System optimization | By cleaning web browser caches and web data, you would ensure that third parties can no longer track you – use FortectIntego for this task |
Adload and its long history: new variants keep emerging
In the past, Mac devices were widely perceived as impervious to the array of cyber threats affecting other operating systems. This belief has been dispelled by the evolving landscape of cybersecurity and the advancement of cybercriminal tactics, demonstrating that Macs are indeed vulnerable to various digital threats.
Central to this changing scenario is the Adload malware family, notorious for producing numerous variants like NavigateEngine, UpgradeIndex, and QueueWindow since its first appearance. These variants, while showing some differences, typically share similar operational and distribution characteristics.
Adload infections can be identified by a distinctive magnifying glass icon used for both its primary application and related browser extensions. This is a consistent feature across its different forms.
Despite being categorized as adware, the implications of WouldLatest, a member of the Adload family, are substantially more severe than mere ad displays. Its functionalities, aligning more with conventional malware, underscore its status as a significant risk to Mac users. This scenario exemplifies the growing complexity and severity of threats that modern Mac systems face, underlining the importance of robust security measures.
Distribution and avoidance techniques
Adload malware variants, such as WouldLatest, primarily spread through two methods. The first is through cracked software installers, which are illegitimate modifications of genuine software offered on untrustworthy websites. Many users, under the impression of acquiring a free version of a paid application, inadvertently download these installers. Unbeknownst to them, these often contain malware, including Adload variants, which get installed alongside the desired software.
The second method is the use of fake Flash Player update prompts. These deceptive notifications usually appear on harmful websites, misleading users into believing they are downloading necessary updates for Adobe Flash Player. In reality, these are malware downloads disguised as updates.
To prevent Adload or similar malware infections on Macs, several steps can be taken. Firstly, downloading software should be restricted to official websites and legitimate app stores. This reduces the risk of encountering harmful installers. Additionally, users should be cautious of pop-up ads, especially those purporting to be software updates, as these can be deceptive.
Maintaining the latest security patches for both the Mac and installed software is crucial. This helps close vulnerabilities that could be exploited by malware. Using reputable anti-malware software and keeping it up-to-date can provide an additional layer of defense.
Furthermore, users should be careful when clicking on links or downloading attachments in emails, as these can be gateways for malware. Finally, practicing safe browsing habits, such as steering clear of suspicious websites and links, is essential in protecting personal information and data from potential cyber threats.
Effective removal of WouldLatest malware
Just like other malware variants, removing WouldLatest presents unique challenges due to its ability to gain elevated system privileges. It not only deposits harmful files on the system but also creates new user profiles and login items. It can evade detection by standard security mechanisms like XProtect and Gatekeeper, thanks to its use of AppleScript. Simply deleting the core files of the main application or extension often proves insufficient, as they can regenerate.
For a comprehensive removal, employing anti-malware tools, such as SpyHunter 5Combo Cleaner or Malwarebytes, is advisable. These specialized software solutions are designed to detect and eradicate malicious files, including those with persistence capabilities. To maintain effectiveness against evolving cyber threats, it's crucial to keep these anti-malware tools updated.
If you choose to manually remove the malware, detailed instructions are provided below. However, be aware that incomplete removal may leave remnants that enable the virus to reappear. The manual process should start with the Activity Monitor, where you can halt any processes linked to WouldLatest. Following this, you can proceed to delete the primary application.
Additionally, thorough system optimization and clearing of browser caches are essential steps in the removal process. Tools specifically designed for system optimization like FortectIntego can be instrumental in ensuring that no traces of the virus remain. While manual removal instructions are available, the automated method using specialized software is generally more effective and is strongly recommended for ensuring the complete eradication of WouldLatest from your Mac.
Manual elimination
Malware often employs background processes to execute its intended actions covertly. Consequently, prior to initiating the removal of the primary malware application, it is critical to ascertain whether any active background processes could impede the removal process. To perform this check, follow these steps to access the Activity Monitor on your Mac and terminate these processes:
- Open the Applications folder and go to Utilities
- Double-click the Activity Monitor and shut down all the suspicious processes.
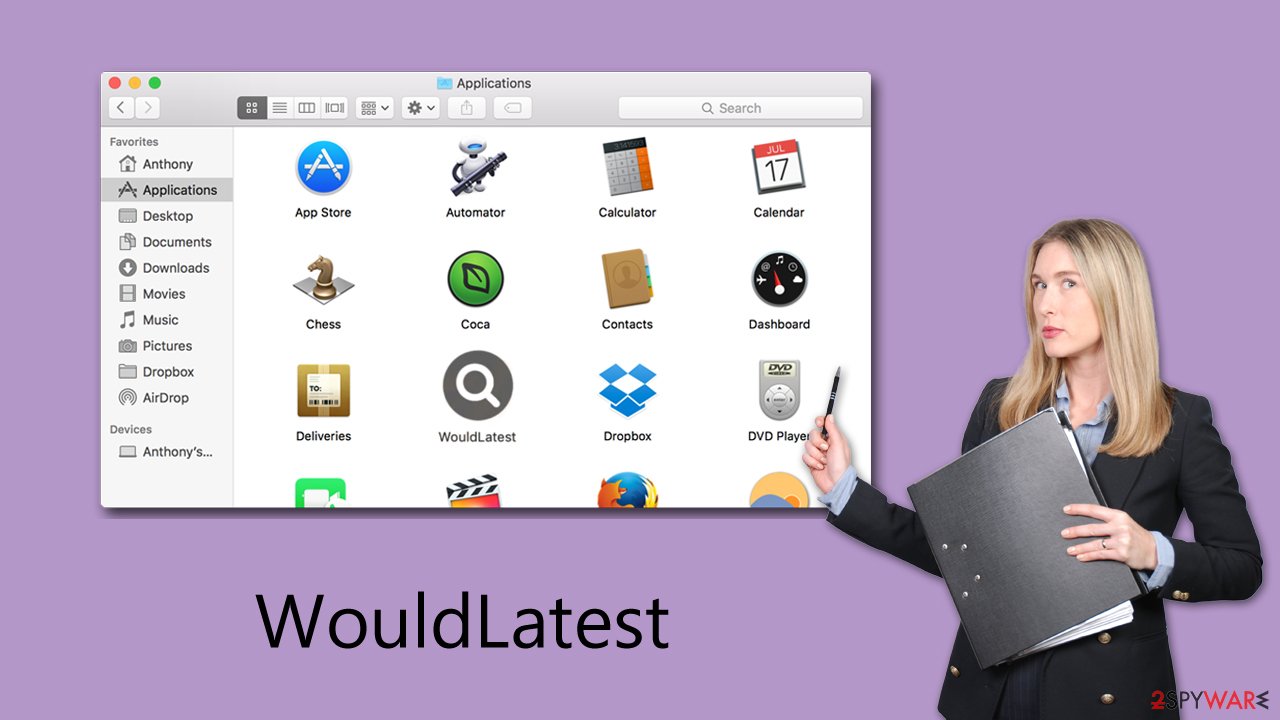
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
![Uninstall from Mac 1 Uninstall from Mac 1]()
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)
Your next task is to remove all the virus-related Login items and new Profiles that could be used by it.
- Go to Preferences and pick Accounts
- Click Login items and delete everything suspicious
- Next, pick System Preferences > Users & Groups
- Find Profiles and remove unwanted profiles from the list.
Small configuration files known as PLIST can hold various settings information. They might prevent the virus from being removed properly.
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and delete all the related .plist files.
![Uninstall from Mac 2 Uninstall from Mac 2]()
Clean your browsers
The extension component plays a crucial role in the operation of the malware. It instigates significant modifications to critical browser settings, including the homepage, new tab address, and search provider. These alterations facilitate the continuous delivery of intrusive advertisements to the user. More concerning, the extension grants the malware access to and the ability to collect all data entered into the browser, potentially including sensitive information like account passwords and credit card details.
For those who opted for the automatic removal method, the extension should have already been eliminated, mitigating further concerns. However, if you selected the manual removal approach, it is imperative to confirm the successful deletion of the extension.
Getting rid of WouldLatest Mac virus. Follow these steps
Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

Remove from Google Chrome
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

How to prevent from getting adware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.












