Backdoor:MSIL/AsyncRAT (Virus Removal Guide) - Free Instructions
Backdoor:MSIL/AsyncRAT Removal Guide
What is Backdoor:MSIL/AsyncRAT?
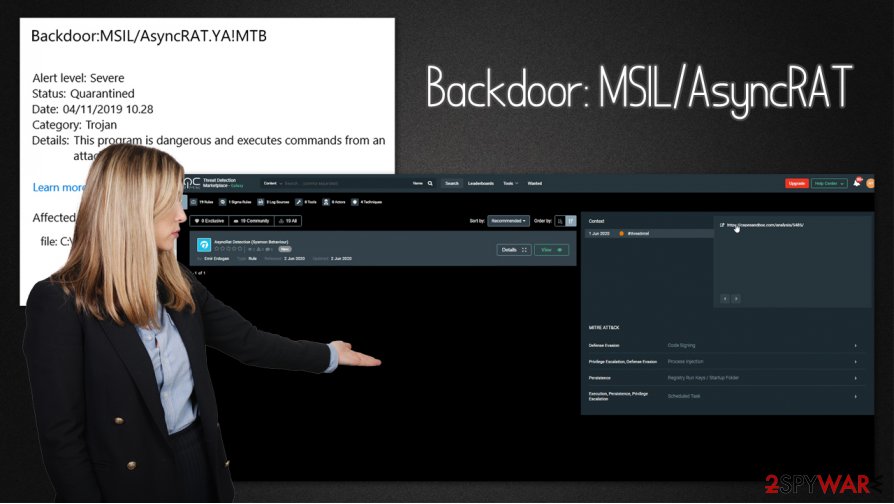
Backdoor:MSIL/AsyncRAT – a dangerous malware attack that can result in a complete computer compromise

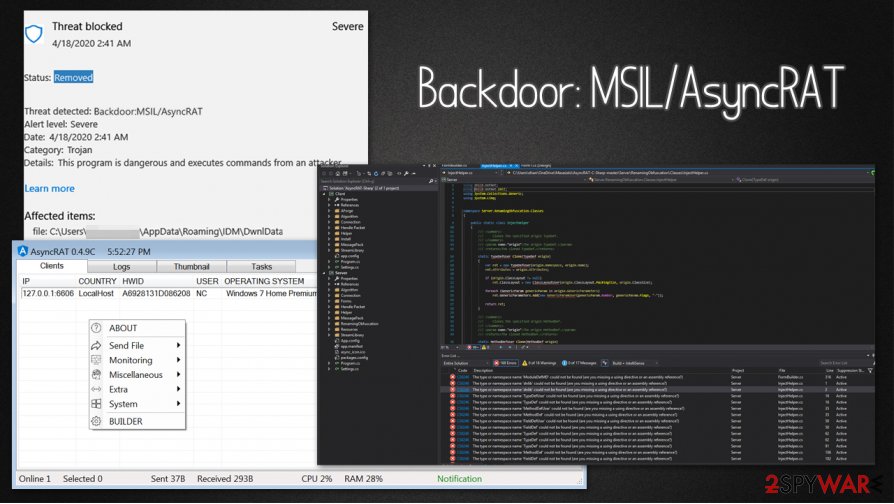
Backdoor:MSIL/AsyncRAT is Microsoft's detection name for a Remote Access Trojan known as AsyncRAT. This malware belongs to a category of programs that initially can be used for surveillance or educational purposes – This particular RAT is available as an open-source project for Windows. However, many malicious actors or cybercriminal groups employ these tools for nefarious purposes and inject them into companies' or users' computers, as well as networks, illegally. As a result, they serve as malware that opens a backdoor on a compromised system, allowing the attackers to perform all types of malicious actions.
Backdoor:MSIL/AsyncRAT includes an array of features that can be used for extensive monitoring practices. It can capture screenshots, view the status of anti-virus software installed on the system, log keystrokes, implement anti-analysis mechanisms to prevent detection, retrieve passwords and other sensitive data, and much more.[1] Without a doubt, malware can result in devastating consequences, including financial losses, personal data compromise, or even identity theft.
| Name | Backdoor:MSIL/AsyncRAT |
| Type | Backdoor, Remote Access Tool (open source), Remote Access Trojan (RAT) |
| Programming language | C# |
| Operating system | Windows |
| Distribution | Botnets, malicious spam emails, fake updates, web injects, Remote Desktop connections, etc. |
| Capabilities | Other malware injection, system and user input monitoring (taking screenshots, stealing passwords, keylogging, etc.), anti-analysis, etc. |
| Associated risks | Monetary losses, increased probability of phishing attack, personal information (credit cards, logins, social security numbers) leak, identity theft, infiltration of other malware |
| Removal | Disconnect the compromised machine from the network, access Safe Mode with Networking (if needed), and perform a full system scan with anti-malware software |
| System fix | Malware can significantly damage Windows components – these actions can sometimes not be reverted by anti-malware solutions. A unique repair tool FortectIntego can find the damaged entries and replace them with working copies without having to reinstall a Windows machine |
Backdoor:MSIL/AsyncRAT virus mainly targets organizations and is used in large-scale malicious operations. The malware was previously spotted being used by several cybercriminals groups, such as TA2719,[2] Mo Lou Qi, and others. Likewise, it was implemented within a Spamhaus botnet, which was also responsible for the delivery of other malware, including Nanocore, Agent Tesla, Remcos, Azorult, NjRat, and many others.
Despite this, since the AsyncRAT is delivered via several widespread distribution methods (for example, various cybercriminal groups might take a different approach and distribute malware via malicious spam email attachments or break in via the insecure Remote Desktop connection), home users could also be affected by it. Many already spotted Microsoft Defender flagging this infection and preventing its entrance. There were several versions of the infection observed, which include:
- Backdoor:MSIL/AsyncRAT!MTB
- Backdoor:MSIL/AsyncRAT.YA!MTB
To understand Backdoor:MSIL/AsyncRAT, it is important to understand what a backdoor is and how it correlates with its RAT functionality. As previously mentioned, Remote Access Trojans are legitimate tools that are misused by cybercriminals to monitor computers and networks illegally. They are often utilized in high-scale attacks against corporate networks for spying purposes.
A backdoor is generally a type of a Trojan that can bypass regular security measures implemented on the machine. As soon as it is installed, it allows criminals to gain administrator permissions and move laterally on the network. Thus, backdoor such as Backdoor:MSIL/AsyncRAT malware can be used to combine infected machines into a botnet that is used for delivering spam or performing DDoS attacks.
While the built-in Microsoft's security scanner can typically take care of the threat, it might also fail to eliminate all the malicious components that the Backdoor:MSIL/AsyncRAT malware brings into the PC. Besides, since a backdoor functionality allows the attackers to proliferate other malware (for example, Wacatac Trojan or Copa ransomware), it is highly recommended to scan the machine with an additional security program, such as SpyHunter 5Combo Cleaner or Malwarebytes.
If the virus is tampering with your security software, you should access Safe Mode with Networking, as we explain below, and then download the anti-malware from there. Performing a full scan of the system should complete a full Backdoor:MSIL/AsyncRAT removal. Note that some variants of malware can sometimes disable Windows Defender as soon as it manages to reach the machine, so experts highly recommend secondary protection measures.[3]
Finally, serious malware infections can straight out damage Windows system files, resulting in serious stability issues. In some cases, victims have to reinstall Windows in order to recover from a serious malware attack. To avoid that, we recommend using FortectIntego – this unique repair tool can fix virus damage and replace damaged Windows components with new ones.
The different approach of cybercriminal gangs: RAT distribution methods explained
As explained above, several different cybercriminal groups take on Remote Access Trojans (open source[4] tools are especially popular) and place them on corporate networks or home computers without permission. Hence, there are many different approaches that the threat actors can take.
Here are some of the methods that can be used by cybercriminals to deliver a RAT and a backdoor onto a system:
- Another backdoor. Malware is incorporated into a complicated network and APT groups are often collaborating to maximize the profits of the illegal activities;
- Email spam or targeted emails. Phishing messages arriving in users' inboxes have been used for years, and remain one of the main attack vectors for the most prolific malware;
- Software vulnerabilities are also often chosen as the main way to deliver the malicious payload. Due to randomized nature of the attack, only those who have unpatched software installed on their systems can get infected this way;
- Repacked installers and software cracks can be placed on various websites across the web, pretending to be legitimate programs or pirated ones;
- Insecure Remote Desktop connections that are open to the internet are one of the primary choices for a corporate network break-in and exploitation.
To prevent the infection of malware, users and enterprises should ensure that adequate security measures are practiced on a regular basis. Advanced anti-malware software, regular software updates, familiarization with phishing techniques are among the primary ways of securing a computer or a network from intrusions.
Employ advanced security tools to remove Backdoor:MSIL/AsyncRAT malware
Since the AsyncRAT virus can use different distribution methods, the message of detection can be encountered at any time. To evaluate the situation better, you should always access the logs of your security software and check what exactly happened. Your anti-malware should also inform you whether it managed to remove Backdoor:MSIL/AsyncRAT successfully.
If going through the logs, you noticed that some of the components had not been deleted, it means that Backdoor:MSIL/AsyncRAT removal is not complete. In such a case, we suggest you disconnect your computer from a LAN or other network, access Safe Mode with Networking, and perform a full system scan from there. To ensure that the malware is eliminated for good, we also recommend scanning the device with a different security application.
Getting rid of Backdoor:MSIL/AsyncRAT. Follow these steps
Manual removal using Safe Mode
If malware is tampering with your security software, employ Safe Mode with Networking to ensure that your anti-malware cannot be intercepted:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Backdoor:MSIL/AsyncRAT using System Restore
System Restore can also be an effective method when trying to delete malware such as AsyncRAT:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Backdoor:MSIL/AsyncRAT. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Backdoor:MSIL/AsyncRAT and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting backdoors
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Do Son. AsyncRAT-C-Sharp v0.5.7B releases: Open-Source Remote Administration Tool. Security Online. Information Security.
- ^ Threat Actor Profile: TA2719 Uses Colorful Lures to Deliver RATs in Local Languages. Proofpoint. Security blog.
- ^ Zondervirus. Zondervirus. Cybersecurity advice and malware insights.
- ^ What is open source?. Red Hat. World's leading provider of enterprise open source solutions.







