Betabot virus (Removal Guide) - Jun 2018 update
Betabot virus Removal Guide
What is Betabot virus?
BetaBot – a trojan with an enhanced list of features

Betabot is a malicious trojan that shifted its functionality throughout the years. It was first spotted in March 2013 with an already impressive list of capabilities – remote connection, information grabbing, distributing ransomware, as well as disabling anti-malware software on the machine. The latest attacks of the malware were spotted by security researchers[1] using a 17-year old vulnerability in Windows software. The virus is available to purchase for as little as $120 on the black market, so many crooks are in a hurry to make use of it.
| SUMMARY | |
| Name | Betabot |
| Type | Trojan |
| First spotted | March 2013 |
| Capabilities | Stealing sensitive data, distributing ransomware, disabling anti-mawlare software, etc. |
| Distribution | Fake links, spam emails, etc. |
| Elimination | Automatic – download and install FortectIntego or SpyHunter 5Combo Cleaner and perform full system scan |
The Betabot virus is typically distributed through fake links in messaging apps, such as Skype or Facebook Messanger, as well as socially engineered emails. Malware starts its attack by showing users a bogus pop-up window, which may look legitimate, as it goes by the name of User Account Control pretending to be from Microsoft. Fortunately, users became suspicious of such behavior. Thus, hackers addressed this problem by creating another fake Windows pop-up – Critical Disk Error.
It informs users that the system has detected multiple corrupted files, giving two options to choose from:
- Restore files
- Restore Files and check disk for errors
Regardless of which option is picked, the User Account Control window pops up next, justifying the action mentioned above. As soon as the victim allows the malicious program to gain administrative rights, it makes several changes to the system, including Windows registry[2] modification, to be able to deny access to security websites and proper function of anti-malware software, as well as steal user's sensitive data, including banking information.
It may be quite tricky to remove Betabot because of the reasons mentioned above. Nevertheless, it is almost impossible to accomplish without the help of security software, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes. The worst part is that the malware should be spotted first, and that is quite a challenge in itself.
Trojan.Betabot may show no symptoms, but, as is typical with trojan horses, they may show some signs:
- Blue Screen of Death[3] error messages (stop errors);
- Non-responsive or crashing programs;
- Various other error messages;
- New files created without permission;
- Some files and folders deleted without permission;
- Slow computer performance, etc.
However, as we already mentioned, the malware may show no signs at all. That is why it is vital to be wary when using the internet and have security software with real-time protection function on at all times. If you are not sure if your system is infected, run anti-malware software in Safe Mode with Networking which would take care of safe BetaBot removal from your system.
Risk factors you need to know about BetaBot
The Betabot virus has earned its world fame by running its cyber campaign by stealing bank account passwords. After quietly invading the system, it spies on a user and continuously transfers the confidential data to a remote server. It also employs Neutrino exploit kit to continue the misdeeds. Likewise, victims suffer substantial financial losses.
In 2016 hackers struck again by enhancing the malware's capabilities. It joined forces with Cerber virus – dangerous ransomware[4] that locks up user's files and demands the ransom to be paid for the decryption key. Nevertheless, security experts never recommend contacting cybercriminals and instead return their data by using back-ups, official Cerber decryptor, or using third-party software. Summing up, the hackers were able to encrypt the data they targetted in the first place. So now their revenues will double as in both cases they obtain the wanted information.
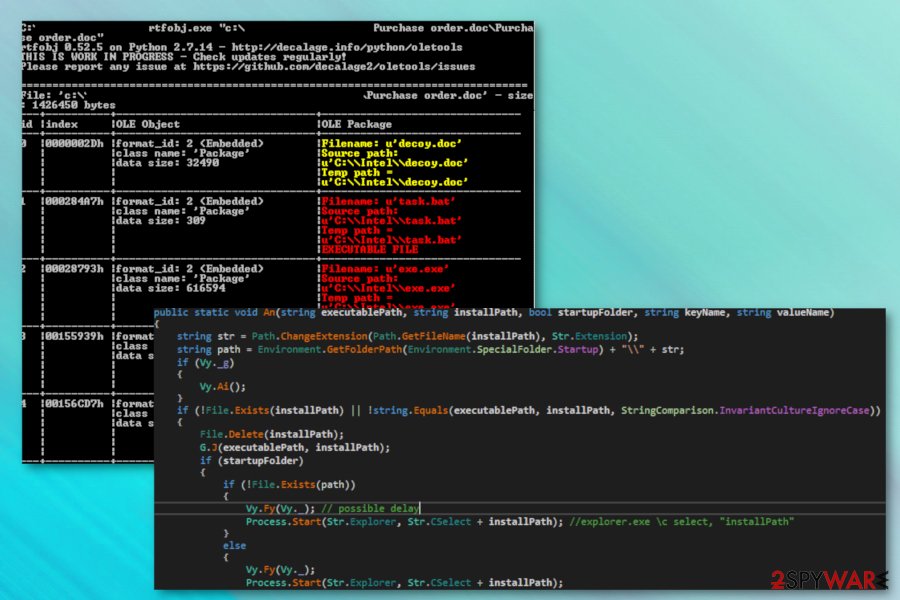
In June 2018, malware came back once again. It used Windows Word document trying to exploit a vulnerability which first appeared in 2000 in the Microsoft Equation Editor (EQNEDT32.EXE) component. Microsoft only discovered it in 2017 and patched the same year. The vulnerability allows hackers in inject ab OLE file into a specially crafted RTF file, which allows remote access to the PC.
All the embedded objects try to camouflage as legitimate Intel software files to avoid any suspicion:
- Inteldriverupd1.sct
- Task.bat
- Decoy.doc
- exe.exe
- 2nd.bat
Inteldriverupd1.sct uses Windows Script Component to create a new object which runs task.bat and then checks for the block.txt file in the temp folder. It then creates one if it is not detected, and then deletes itself. Then, the 2nd.bat launches the main .exe file and modifies registry entries to hide its tracks. During the process, malware connects to hxxp://goog[.]com/newbuild/t.php?stats=send&thread=0 server and then shows Decoy.doc after execution.
At the last stage, the Betabot virus copies itself to the Start menu. It also uses Command and Control server to communicate with attackers (onedriveservice[.]com), as well as redirects users to suspicious realms, most likely to earn extra revenue.

Learn to avoid malicious programs
Trojan horses are the sneaky type of viruses that are usually deployed using clever social engineering attacks. There are various methods malware can be distributed, but the most prevalent ones are these:
- Spam emails. Smartly written emails may sometimes trick even computer-savvy individuals. Thus, it is extremely important to notice a phishing email sign, and never open attachments;
- Phishing messages on social networks and other communication programs. Quite often, hackers simply drop a link, claiming that it is a video or a photo of the targeted individual (as in case of the Facebook virus). Remember, these links can even come from your friend list, as their accounts may be hacked or infected.
- Malicious websites. Avoid file-sharing sites and other suspicious domains. Do not download pirated software, and refrain from visiting porn, gambling, online dating and similar sites.
You should never trust notifications that pop up out of nowhere. Remember, they can be designed just as legit messages. As soon as you allow the admin rights, it will be too late, however.
Security researchers[5] recommend always patching your software and operating system on time, as well as employ a robust security tool that can prevent malicious infections.
Betabot removal guide using two methods
A trojan is undoubtedly not an ordinary computer virus. Since it operates in such insidious ways, you should not take it too lightly. That is why remove Betabot virus right away. For that purpose, scan the system with FortectIntego or Malwarebytes. These applications will help you get rid of the malware entirely.
Researchers recommend to download an anti-malware software on a healthy computer and insert it into a USB stick. Use the stick on the infected computer only after you enter Safe Mode with Networking, as explained below. This way, you can guarantee full BetaBot removal. After this is done, do not forget to format the USE stick to prevent accidental contamination.
When the virus infiltrates the system, you might not expect that it comes with a back-up – the ransomware. In that case, if you hesitate to perform Betabot removal, the file-encrypting malware might encrypt the files. If your personal files were encrypted by Cerber, we recommend using official decryptor that can be downloaded here. Finishing on a positive note, remember that proper cyber protection and your cautiousness work as a perfect combination decreasing the risk of getting infected by the cyber threat.
Getting rid of Betabot virus. Follow these steps
Manual removal using Safe Mode
To safely eliminate Betabot, you should enter Safe Mode with Networking:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Betabot using System Restore
You can also try using System Restore to delete the virus:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Betabot. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Betabot and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting trojans
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Wojciech. Betabot still alive with multi-stage packing. Medium. Security blog.
- ^ Tim Fisher. What Is the Windows Registry?. Lifewire. Tech Untangled.
- ^ Chris Hoffman. Everything You Need To Know About the Blue Screen of Death. How-To Geek. Site that explains technology.
- ^ Margaret Rouse. Ransomware. SearchSecurity. Cybersecurity site.
- ^ DieViren. DieViren. German security experts.





















