Remove Instagram virus (6 scam versions included)
Instagram virus Removal Guide
What is Instagram virus?
Instagram virus is a term used to describe malware or scam campaigns distributed on the known social media platform

Instagram virus is a term used to describe a group of malware[1] that circulates on the giant social media platform. It emerges in the form of advertisements and fake feeds. In 2016, a group of cybercriminals managed to crack Instagram's scam filter and started distributing “Instagram Ugly List 2016” feeds on behalf of the compromised account's user.
Soon after that, Zeus-related virus has been released. According to experts, crooks target users' accounts and start following people and like posts following the hack. Camouflaging Facebook, criminals also developed Who Viewed Me on Instagram? Scam, which may be used for the collection of user's names, log-in details, and other personal information. At the end of 2018, a new wave of the virus related to RayBan ads showed up.
The newest threats affecting the social network are called “The Nasty List”,[2] “The Hot List” and “I created this for you” virus. They operate very similarly to the previous scams as users are directed to a spoofed site asking to enter their credentials and give full access to their account.
| Name | Instagram virus |
|---|---|
| Classification | Malware |
| Symptoms | Suspicious posts and ads in the news feed, suspicious content posted on your behalf |
| Distribution | Bundling, malicious links, compromised software |
| Elimination | To get rid of the virus from your device, run a scan with anti-malware software |
| Recovery | After the termination, use FortectIntego for a speedy recovery from a virus infection; additionally, change your password, and enable two-factor authentication |
You probably have already heard about malware variants such as Facebook virus or Skype virus; in this article, we are going to define different forms of Instagram virus and provide information on how to protect yourself from malware that targets users of this social media application.
If you suspect that your device has been infected, we suggest you follow the virus removal guidelines (provided below the article) and remove the malicious program as soon as possible. You should also scan the device with anti-malware software – recommended ones are provided below the article.
Instagram virus variants (2021 update)
The Ugly List 2016 scam
It is a new virus that rapidly spreads through the social network with the help of infected accounts. The virus uses the compromised account to post a picture that says “Instagram Ugly List 2016,”[3] and tags random victim’s friends in the picture with a short comment “LOL how did your profile on the list,” “omg your profile on the list,” “this is crazy all you guys are there” or “wow u made the ugly list.”
If you have been tagged in such a picture, do not click on such notifications. Typically, such malicious posts provide a URL that points to a malware-laden website, which steals the user’s login details. A stolen account then is used for further virus proliferation. Please do not click on such eye-catching links and do not let your curiosity lead you to sites that compromise your social media account. If your account has been hacked, try to change your password, and if you can’t, report the problem to the support team.
Instagram followers virus
This virus is closely related to the infamous Zeus virus, which was initially used to steal credit card information from victims. Now the virus hacks accounts and converts them to zombies that follow people and like their posts.
So, if you have noticed suspicious posts in your feed, you should quickly change your password and also remove the virus that has your permission to like posts and follow people on your behalf. You should also take these permissions back by revoking app access.

Who Viewed Your Instagram Profile virus
There are bogus apps that falsely claim to be able to reveal people who viewed your profile on Instagram. Of course, all of us are curious, and it would be interesting to find out who repetitiously visits our social media accounts, but… Social network does not provide such feature and third-party apps that promise to reveal the names of people who visit your profile are simply lying to you. For example, apps like InstaCare – Who cares with me? or Who Viewed Me on Instagram? are developed by Turkyer Bayram – the same person who has created the infamous InstaAgent application that stole users’ login details and even posted unauthorized posts via victims’ accounts.
RayBan scam
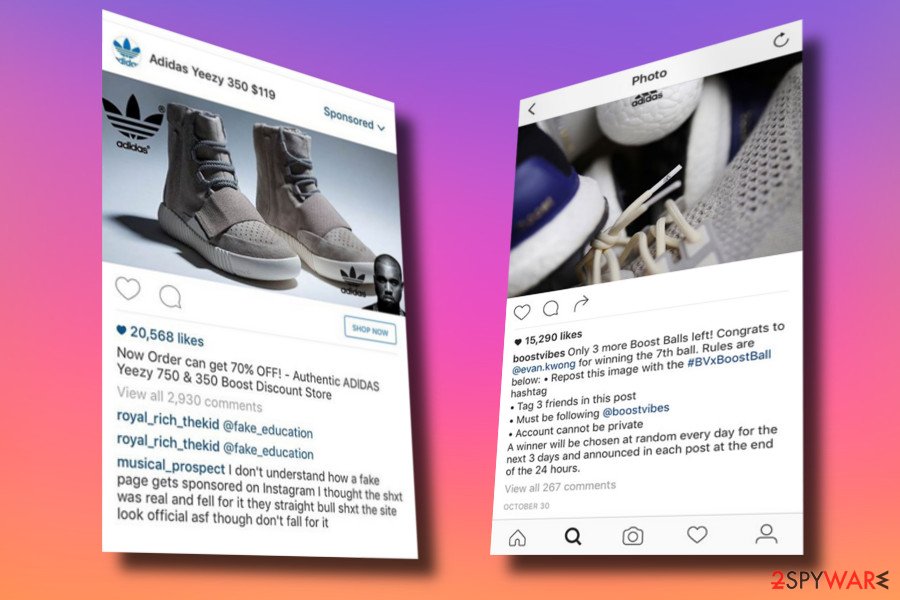
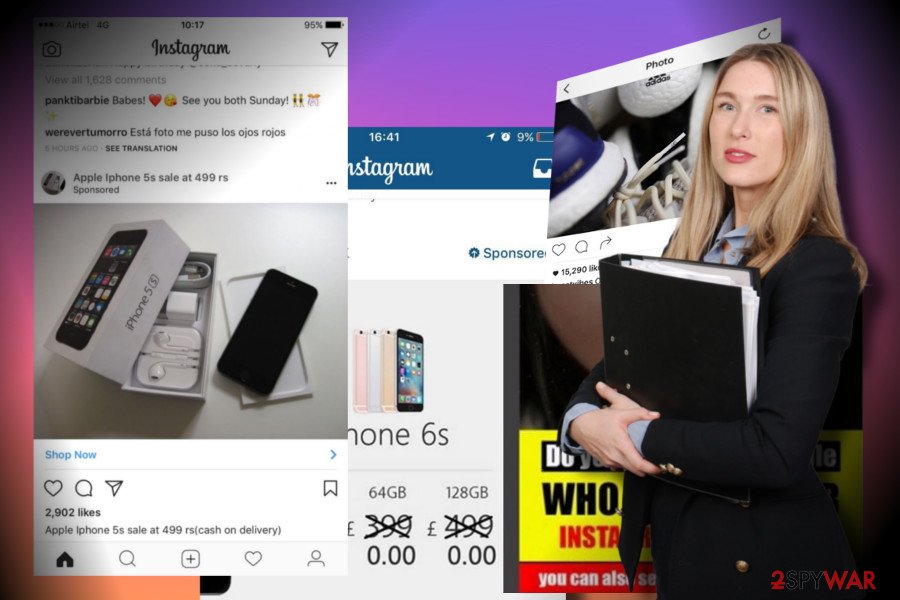
The community started expressing their concern about misleading ads offering discounted Ray-Bans or Ray-Bans for 90 percent.[4] Ads that keep interrupting users' feed and tag them every day were spotted in the middle of April 2018, however, the first signs of this scam are known to have come out three years ago (2019)!

Initially used on Facebook, the Ray-Ban scam turned to Instagram users. Therefore, the users of this particular platform should beware of a constant stream of friends tagging you and your relatives to buy luxurious Ray-Ban sunglasses with a great discount. Sometimes the RayBan virus manifests itself in the form of sponsored ads. However, people most frequently witness a photo from a friend with a group of people tagged in.
According to ESET researchers, this type of scam has been actively distributed via spam emails and targets UK, Japan, and Spain users in particular. NoVirus.uk[5] security experts claim that there are two possible reasons for the fake photos and ads, i.e., account hack or malware infection. Therefore, if you noticed questionable content related to RayBan, scan your PC with a reputable anti-virus and change your account's password.
The Nasty List Instagram scam
“The Nasty List” scam surfaced in mid-April 2019. Users started a conversation on Reddit,[6] claiming that their account got compromised after they clicked on the link in a direct message from a family member.
Users usually receive a message that starts with something as:
OMG your actually on here, @The_Nasty_List_918
omg your #15 on this list. So messed up
WTF you are literally on here
WOW. Your on here!!! ranked 100
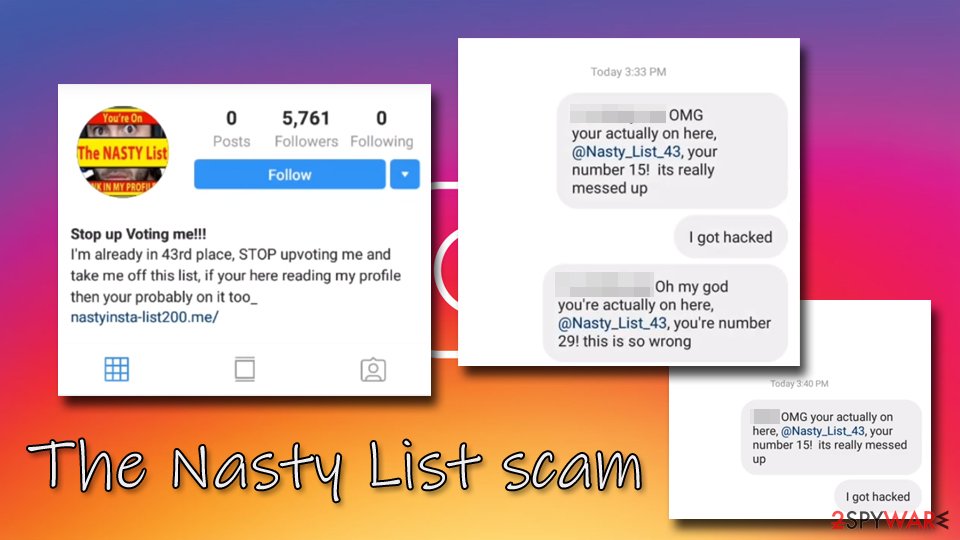
Naturally, this type of message immediately catches multiple users' attention, as it implies that the victim on “The Nasty List.” Soon after clicking on a link, users are directed to a fake profile that prompts them to click on another URL.
Those who proceeds are directed to a spoofed login page, which asks them to enter credentials. If looking closely, however, meticulous users would spot that the URL is not Instagram.com but rather nastylist-instatop50.me or similar. Nevertheless, the login page does look legitimate, so many users could give out their login details without giving a second thought about it.
As soon as credentials are entered, hackers can take over the account of the victim, which then they use to promote the Nasty List scam even further. Additionally, this would allow bad actors to change any type of details on the account, including phone number, email address, or password.
It is yet unknown what malicious plot behind the “Nasty List” hides, but criminals could sell the acquired login credentials on the Dark Web, or even establish a botnet that would distribute data-stealing malware.
If you entered your credentials into the spoofed login page, your account is compromised. Immediately change your password and check if your contact details were not changed by crooks. It is also worth noticing that those who had two-factor authentication[7] enabled can be sure that hackers were unable to access their accounts.
The Hot List scam
Just a week after “The Nasty List” scam showed up on Instagram, new fake messages surfaced – “The Hot List.” Just as its predecessor, the scam works practically identically.
Users receive a direct message from a person on their friend list – this just makes the scam more believable. It usually claims that the victim is on “The Hot List” and urges him or her to click on the link:[8]
I just saw a few of your photos on the @The_HotList_95 and they are already upvoted to #26!
If the bogus link is clicked, the user will end up on a fake profile, usually called “The Hot List” or “Everyone's on here Look.” From there, he or she will be asked to enter credentials on a spoofed page, which will allow the takeover of the account. From there, crooks can spread malicious messages to everybody on the hacked person's friend list.

As usual, if you fell a victim of “The Hot List” scam, make sure you reset your password and immediately enable two-factor authentication.
Malicious email and malware may be at the back of this infection
Although attacks against users is still not a very common phenomenon, we are sure that you have been tagged on shady pictures on social media at least once. Accounts that tag random users on photos that promise thousands of likers and followers typically urge to visit a particular website, which often appears to be untrustworthy or even malicious.
You should never click on vague links unless you know that the account that advertises it is legitimate and trustworthy. The second thing to remember is that applications that promise you unique access to the list of people who viewed your profile are usually deceptive, and you should stay clear of them.
You should never provide your login details to suspicious apps that promise to enormously increase your followers (they usually add bots that deletes after a while, so consequently you lose followers that you paid for). If you want to gather more followers and likers, focus on the content you pose, and better do not rely on suspicious vendors that suggest buying a pig in a poke.
Learn how to remove Instagram virus
If you suspect that your mobile device has a virus, you should scan it with an anti-malware program compatible with your device. We suggest using SpyHunter 5Combo Cleaner, Malwarebytes although any other reputable security application should work. After that, you should scan your machine with FortectIntego for the best results, as it will help you recover from malware infection. Finally, you should follow the instructions provided below to finish the virus removal and get rid of the virus remains.
- The first thing that you should do is to revoke and block suspicious apps that have permissions to act on your behalf and control your Instagram account. Log in to your account via a web browser. Don’t use the application – use a web browser.
- Go to your profile, then click Edit Profile. Next, click on Authorized Applications.
- Here, you can find a list of programs that have access to your account. You can find the Revoke Access button below each of these programs. Click it and hit Yes when a confirmation pop-up appears.
- Change your password.
In case you cannot log in to your account, contact Instagram directly. You can reach automated support via 650-543-4800, write an email to support@instagram.com or use Help center service.
How to prevent from getting malware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Jeff Goldman. Researchers Warn of Malware in Fake Instagram App for Android. eSecurity Planet. IT professional's top choice for Internet security news and analysis.
- ^ Linas Kiguolis. "The Nasty List" scam targets Instagram users' credentials. 2-spyware. Cybersecurity news and articles.
- ^ Cammy Harbison. Is Instagram 'Ugly List 2016' Real? Hack Scams Users Into Thinking They’ve Been Tagged, Then Takes Over Their Accounts. Player.One. In-depth, passionate coverage of the world of gaming and gamer culture.
- ^ Tess McClure. WTF is Happening With the Great Ray-Ban Insta Hack of 2018. Vice.com. Relevant news articles.
- ^ Novirus. Novirus. Virus and spyware news.
- ^ Anyone having a similar problem? (The Nasty List). Reddit. Social network platform.
- ^ Here’s Why Two-Factor Authentication Is So Important. Secure Swiss Data. Encrypted Email Service and Secure Collaboration.
- ^ New Phishing scam called ‘The Hotlist’ now targets the Instagram users. Cyware. Cybesecurity firm.
