Mac virus. Its prevalence, main versions and removal (2019 guide)
Mac virus Removal Guide
What is Mac virus?
Mac virus is an infection that can affect the system and create damage using different types of malicious code

Mac virus is a term used to describe infections that specifically target Mac operating systems and includes adware, browser hijackers, trojans, backdoors, and other malware. While mild infections might be just a nuisance, threats like OSX/Shlayer can sneakily install various potentially unwanted programs in the background, disable Gatekeeper security agent and compromise victims' online safety.
Most users might not even notice the infection, as the most dangerous threats, are designed in a way that prevents users from spotting them right away. Nevertheless, if your Mac is behaving strangely, for example, you see apps like Advanced Mac Cleaner installed without your consent, or Google Chrome, Safari, or another browser is continuously showing you ads, it is most likely that you are infected with a Mac virus.
However, some computer behavior, like slowdowns, might not be related to any infections and might be related to configuration problems, or merely outdated software. Therefore, it is important to know whether or not your device is infected, and if it is – threat removal should be performed as soon as possible to avoid such consequences as further malware infection, money loss, or even identity fraud.[1]
| Name | Mac virus |
| Type | Adware, browser hijackers, scareware, spyware, trojans, ransomware, droppers, cryptominers, and other malware |
| Targeted systems | macOS, Mac OS X, iOS |
| Distribution methods | Software bundling, fake Adobe Flash updates, spam emails, hacked websites, torrent sites, etc. |
| Risk factors | Installation of other malware, sensitive data exposure, redirects to scam or phishing sites, loss of money, identity theft or fraud, etc. |
| Termination | In some cases, the built-in protection is not enough to delete Mac malware. Thus, install reputable security software and perform a full system scan |
| Recovery | To restore normal macOS operation after virus infection, use FortectIntego |
Depending on the type of infection, Mac virus can use a variety of methods to get into your device. Adware and browser hijackers usually spread as browser plugins, or standalone applications that pretend to be useful – they are referred to as scareware by security researchers.[2] Nevertheless, more severe malware is usually propagated with the help of more sophisticated methods, such as:
- Hacked sites;
- Fake updates (especially Adobe Flash[3] or Java, which was eventually killed by Apple in 2012)[4];
- Torrent sites;
- Spam emails;
- Exploits, etc.
These methods are usually used by more dangerous threats, such as backdoors, RATs,[5] ransomware, cryptojackers, and many others.
To find out if your Mac device is infected, you should scan it with reputable security software, such as SpyHunter 5Combo Cleaner or Malwarebytes, and remove the Mac virus for good. In other cases, however, you will most be able to eliminate potentially unwanted programs manually, although that is not a rule either. Finally, if you do find an infection, terminate it and then scan it with FortectIntego – it can restore Mac's operation and fix virus damage.
Mac is not the operating system that can be considered immune to malware
For years, many users believed that Macs could not get infected by viruses simply because of the way the machines are designed. Indeed, your device will not allow you to install applications from anywhere else apart from the official App store, by default at least. Besides, built-in protection tools like Xprotect keep malicious software at bay.
Nevertheless, Mac viruses do exist, and they manage to bypass Apple's security measures, as more and more sophisticated malware is created by hackers. While it is true that Macs are less prone to be infected than Windows machines, they are not immune to viruses. Unfortunately, there are hundreds if not thousands of Mac users who still believe that Macs do not get infections and fail to use even basic security measures.

While Mac virus is generally a rare occasion, adware and phishing that relates to Macs have increased dramatically over the years. In 2019, the macOS infection rate increased by 60% in comparison to the previous year, while 2016 to 2017 resulted in 270% increase.[6] Therefore, do not ignore warnings from cybersecurity experts, and adequately protect your machine from infections – install security software, keep your device updated, and use caution when installing new applications or browsing the web.
Mac optimizing tools have become one of the most common types of PUP out there
One of the most common Mac virus examples is fake optimization software, otherwise known as scareware. These tools are created to deliberately mislead users into thinking that their machines are in deep trouble by either claiming severe virus infections or flagging false positives.[7]
Nevertheless, the main goal of such software is to make users pay for its full version, instead of actually helping them fix their computers. In fact, bogus optimization tools might not only fail to deliver but also disrupt the normal operation of Mac by deleting necessary files or affecting other system elements.
Below you will see the most prevalent versions of the cyber infection that relates to the scareware category – make sure you terminate any type of such programs if they land on your device.
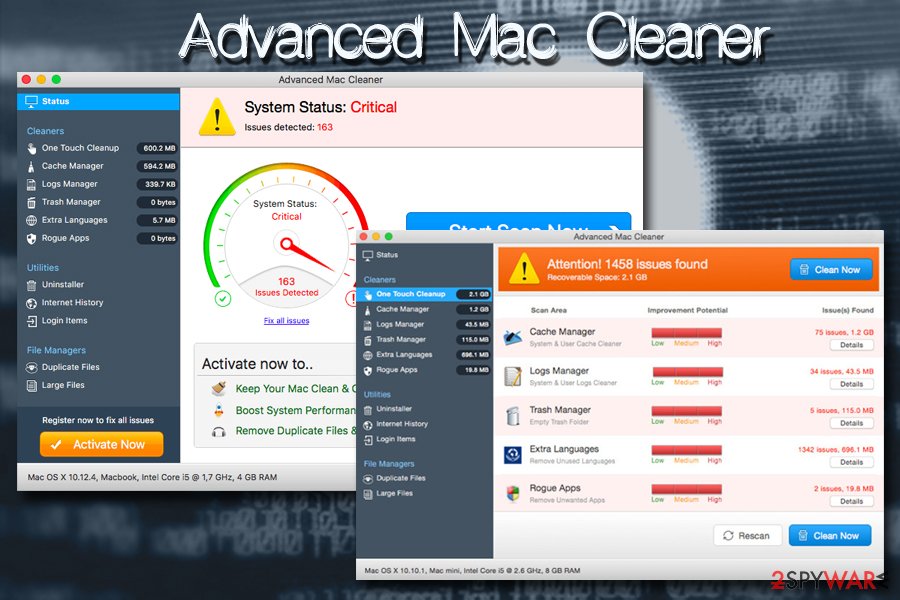
Advanced Mac Cleaner
Advanced Mac Cleaner is one of the most notorious Mac viruses in the wild – it gets installed into systems via software bundles, via fake Adobe Flash updates, or infiltrated by malware downloaders like Shlayer trojan.
Advanced Mac Cleaner is a piece of software that is specifically designed for Macs and belongs to the scareware category. These potentially unwanted programs usually focus on scamming users and making them buy a full version of the application. Advertised as “system optimizers,” such tools usually show fake scan results, claiming dangerous computer infections or other discrepancies that need to be fixed immediately.
Quite often, users are also scared with specific timers, red flashing text, and other social engineering tricks. While most of the savvy computer users are aware of the scam scheme, the elderly or those who are not familiar with the world of computing often believe the lies and end up spending money on useless software like Advanced Mac Cleaner.
Mac Auto Fixer
Mac Auto Fixer is another scareware application that operates very similarly to all the tech support scams that are designed for Macs. Designed by PCVARK, one of the most controversial software developers out there,[8] it is promoted as a tool that can clean and speed up the Mac computer, while in reality, it is a fake system optimizer designed to scam users into buying its full version.
In reality, Mac Auto Fixer is a type of Mac virus that will not optimize, clean, or improve the operation of your computer. In fact, the software is also often included on scam sites that claim fake virus infections – users typically get redirected to such rogue sites by adware – a type of potentially unwanted application that focuses on displaying ads on all websites that they visit.
Therefore, if you see that Mac Auto Fixer performing scans on your computer out of nowhere, it is best to remove it immediately. While the tool is not dangerous, it might result in money loss and will keep reminding that it is thereby claiming fake virus infections.
Mac Tonic
Mac Tonic is another fake system optimizer and a potentially unwanted program designed for Mac operating systems. While many will find this application on their computers soon after the installation of freeware or shareware, the app was known to be spread with the help of fake Adobe Flash and Adobe Shockwave updates.
The application has the typical behavior of a PUP:
- gets installed without users noticing;
- instantaneously performs system scans claiming various problems and infections;
- asks users to buy its full version to fix their machines;
- constantly displays ads that promote its full version;
- adds entries to the system that prevents easy Mac Tonic removal.
Therefore, if you found it on your device, do not pay attention to any claims that the application makes, and immediately delete it either manually or automatically – pick the latter option if you struggle to terminate it by yourself.

Hijackers, adware, other malicious programs are spreading on macOS too
QSearch
QSearch is a browser hijacker that was explicitly crafted for Mac operating systems but can affect any type of browsers, including Google Chrome, Safari, Mozilla Firefox, Opera, and others. The potentially unwanted program specializes in taking over users' browsers by setting the homepage and new tab URL to qsearch.cc or analytics.qsearch.cc and then displays fake search results that are filled with sponsored links.
The scheme is straightforward and quite similar to adware – QSearch developers accumulate revenue each time the deceptive links are clicked – a program that is called pay-per-click. Therefore, the more ads and pop-ups it displays the more money software authors gain.
Unfortunately, the end-users experience is completely forgotten, as they have to deal with QSearch hijack, which can pose security risks:
- Alternative search results that not necessarily are useful, and might sometimes prevent finding relevant information;
- Some text on sites is turned into hyperlinks;
- Pop-up ads appear on sites that are legitimate and do not serve ads usually;
- Phishing sites might result in a money loss or installation of bogus software;
- Information tracking might expose even private data to unknown third parties.
MyShopcoupon
MyShopcoupon is a plugin that allegedly helps users to find the best deals online and save some money while doing so. While theoretically, it sounds like a great option to find the best coupons, offers, and discounts while shopping online, the activity of this potentially unwanted application often disappoints Mac users.
As soon as users install MyShopcoupon, they can quickly see that their web browsers are filled with advertisements that come in the forms of pop-ups, in-text links, banners, blinking windows, and other intrusive content that disturbs web browsing sessions, instead of actually helping users find relevant information or products they are interested in.
Besides the intrusive ads, MyShopcoupon also tracks users that have the application installed. The gathered data includes:
- IP address;
- Geolocation;
- Cookies;
- Search queries;
- Sites visited and the duration of the visit;
- Links clicked;
- System information, such as OS versions, etc.
While this Mac virus is not as dangerous as keyloggers or data stealers, it can still damage the web browsing experience and might lead to insecure websites.
Mac Detected TAPSNAKE infection
Mac Detected TAPSNAKE infection is a scam used to get personal details from people by tricking them into calling provided numbers. There are numerous versions of this scam scaring users into believing that the Tapsnake, CronDNS, and Dubfishicv viruses were detected. You must stay away from calling any amount from the pop-up or a warning message like this. The message delivers the awarning like this:
****Dont Restart Your Computer ****
Mac Detected TAPSNAKE infection, The Infections detected, indicate some recent downloads on the computer which in turn has created problems on the computer.Call Mac professionals at 800-130-1949 and share this code B2957E to the Technician to Fix This.
PLEASE DO NOT SHUT DOWN OR RESTART THE COMPUTER, DOING THAT MAY LEAD TO DATA LOSS AND POSSIBLE FAILURE OF THE OPERATING SYSTEM, AND POTENTIAL NON BOOTABLE SITUATION RESULTING IN COMPLETE DATA LOSS. CONTACT LIVE CERTIFIED TECHNICIANS TO RESOLVE THE ISSUE CALLING TOLL FREE: 800-130-1949
Exit windows like this because any interaction with these alerts can lead to more severe issues than the Mac virus itself. You need to get a reliable anti-malware tool and clean the machine thoroughly because all these symptoms often are caused by PUPs – cyber intruders that come behind your back.
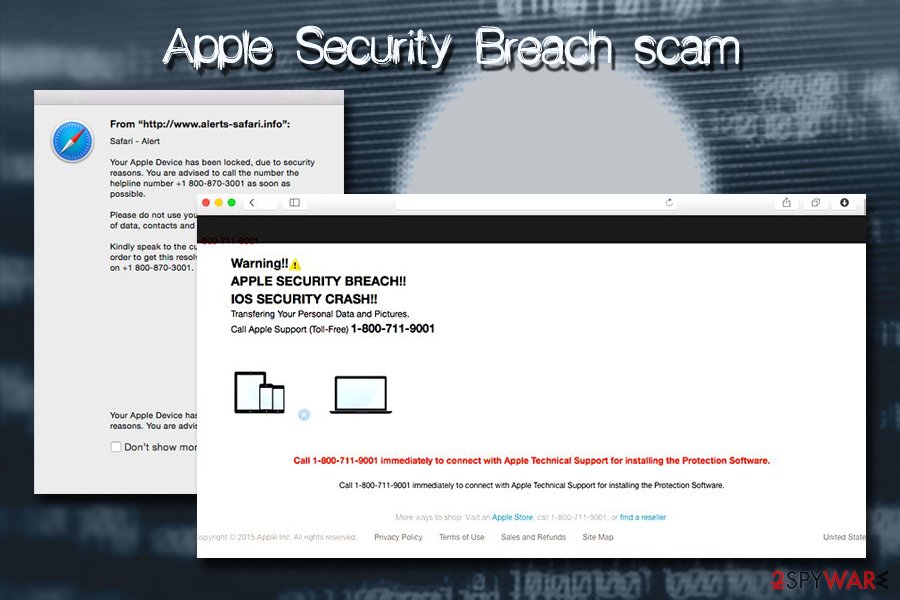
Mac OS X is infected (4) by viruses
Mac OS X is infected (4) by viruses is yet another social engineering campaign based on the lock screen that claims about malware's activity on the system. This scam focuses on tricking people into calling support for an immediate fix. However, this is a technical support scam that is closely related to adware. Once such a virus infects the system, it modifies it and starts showing fake warnings.
Mostly, the malware aims to steal account logins, other credentials like passwords or credit card details. However, this scam can also be used to infect the system with other malware or just sign the victim for the useless services that will be revealed only when the telephone invoice is inspected. Keep in mind that the message which is delivered to your web browser once you start browsing is nothing but a scam! Ignore it to avoid giving the attacker the remote access to your machine!
It is possible to avoid infections and keep the machine free of malware
As we already mentioned, the most common infections that plague Macs are adware and similar, potentially unwanted programs. While initially seen as harmless, they can compromise the device's security and result in much more severe infections, so having adware is not safe at all.
To protect yourself from rogue software that continually displays ads, redirects you to phishing or scam sites, and tries to convince you that the Mac is infected, you should never download applications from third-party websites and only trust official sources like App Store or Chrome web store. Nevertheless, even then it does not render your Mac immune to unwanted programs.
Therefore, you should always pay close attention to the installation process of all apps you are installing, even the legitimate ones. Always read through the installation instructions, do not skip through steps, and terminate all the suggested optional apps in the Advanced/Custom mode.
Additionally, one of the best security advice would be installing and running comprehensive security software that would prevent the most dangerous mac viruses from entering, and also making sure that your system is updated to the latest version. Just like Windows, Apple's software is not perfect and holds vulnerabilities that hackers can exploit in order to infiltrate malware automatically. While such threats are rare, it is always best to keep your system patched to avoid infections.[9]
Know more about Mac viruses in the dedicated section
While Mac is generally considered to be a much safer operating system than Windows, it is not entirely true. Experts estimate that around 1 billion computers run Windows, while approximately 100 million users choose a Mac.[10] Therefore, it makes sense for cybercriminals to create more malware for the most dominating computer system, as it increases the count of potential victims.
Nevertheless, Mac viruses do not step down when it comes to diversity, sophistication, prevalence, and other features of malware. As a result, users might encounter the following categories or Mac virus:
- Adware
- Browser hijackers
- Fake system optimizers
- Cryptominers
- Banking Trojans
- Ransomware
- Info-stealers
- Keyloggers, etc.
Regardless of which type of Mac virus your machine is suffering from, it is vital to delete it, as such infections can result in a sensitive information disclosure to cybercriminals, money loss, installation of other malicious software, etc. Additionally, your computer might be added into a botnet, which would turn it into unstoppable spam machine that sends fake messages to all the contacts on Facebook, email, Skype, etc.
For more information and types of Mac virus, refer to our Mac viruses category.

Delete Mac virus from your system to prevent additional issues
If your system is showing infection symptoms, you should immediately take action and remove Mac virus from your computer immediately. However, there are two different ways to terminate infections – manual and automatic. While both of them can be just as effective as each other, the latter gives users a benefit of preventing infections in the future.
If your Mac suffers from a browser hijacker or adware, you will most likely we able to perform a full malware removal by simply moving the unwanted app to Trash and cleaning /Library/LaunchAgents, /Library/Application Support and /Library/LaunchDaemons folders. Nevertheless, if you are unsure how to do that, you should instead install security software and terminate unwanted apps automatically.
Besides, more severe threats like trojans and similar viruses make substantial modifications to Mac systems, so terminating these infections manually would be almost impossible. Thus, download SpyHunter 5Combo Cleaner or Malwarebytes in order to get rid of Mac virus for good and then scan your device with FortectIntego for best results.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Mac virus. Follow these steps
Delete from macOS
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Microsoft Edge
Delete unwanted extensions from MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Clear cookies and other browser data:
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Restore new tab and homepage settings:
- Click the menu icon and choose Settings.
- Then find On startup section.
- Click Disable if you found any suspicious domain.
Reset MS Edge if the above steps did not work:
- Press on Ctrl + Shift + Esc to open Task Manager.
- Click on More details arrow at the bottom of the window.
- Select Details tab.
- Now scroll down and locate every entry with Microsoft Edge name in it. Right-click on each of them and select End Task to stop MS Edge from running.

If this solution failed to help you, you need to use an advanced Edge reset method. Note that you need to backup your data before proceeding.
- Find the following folder on your computer: C:\\Users\\%username%\\AppData\\Local\\Packages\\Microsoft.MicrosoftEdge_8wekyb3d8bbwe.
- Press Ctrl + A on your keyboard to select all folders.
- Right-click on them and pick Delete

- Now right-click on the Start button and pick Windows PowerShell (Admin).
- When the new window opens, copy and paste the following command, and then press Enter:
Get-AppXPackage -AllUsers -Name Microsoft.MicrosoftEdge | Foreach {Add-AppxPackage -DisableDevelopmentMode -Register “$($_.InstallLocation)\\AppXManifest.xml” -Verbose

Instructions for Chromium-based Edge
Delete extensions from MS Edge (Chromium):
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Clear cache and site data:
- Click on Menu and go to Settings.
- Select Privacy, search and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Reset Chromium-based MS Edge:
- Click on Menu and select Settings.
- On the left side, pick Reset settings.
- Select Restore settings to their default values.
- Confirm with Reset.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Mac registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting mac viruses
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Malware – A Vulnerable Computer means a Vulnerable Identity. NBS. National Benefit Services.
- ^ Novirus. Novirus. Security and spyware news.
- ^ Lory Gil. Malware disguised as Adobe Flash is targeting macOS. iMore. Latest iPhone, iPad, Apple news, deals, reviews, news, and how-tos.
- ^ Alex Heath. Apple Kills Java On The Mac To Fight Malware Like Flashback. Cult of Mac. Tech and culture through an Apple lens.
- ^ Margaret Rouse. RAT (remote access Trojan). SearchSecurity. Information Security information, news and tips.
- ^ Jonny Evans. Warning as Mac malware exploits climb 270%. Computerworld. IT news, careers, business technology, reviews.
- ^ False Positive. Techopedia. Where IT and Business Meet.
- ^ PCVARK plays dirty. Malwarebytes Labs. Security blog.
- ^ Andy Greenberg. Hack Brief: Google reveals "Buggycow." a rare macOS zero-day vulnerability. Wired. International magazine.
- ^ Tom Warren. Apple reveals Windows 10 is four times more popular than the Mac. The Verge. News site that covers the intersection of technology, science, art, and culture.
