Microsoft.com-input11.info ads (Removal Guide)
Microsoft.com-input11.info ads Removal Guide
What is Microsoft.com-input11.info ads?
How should you react to Microsoft.com-input11.info ads?
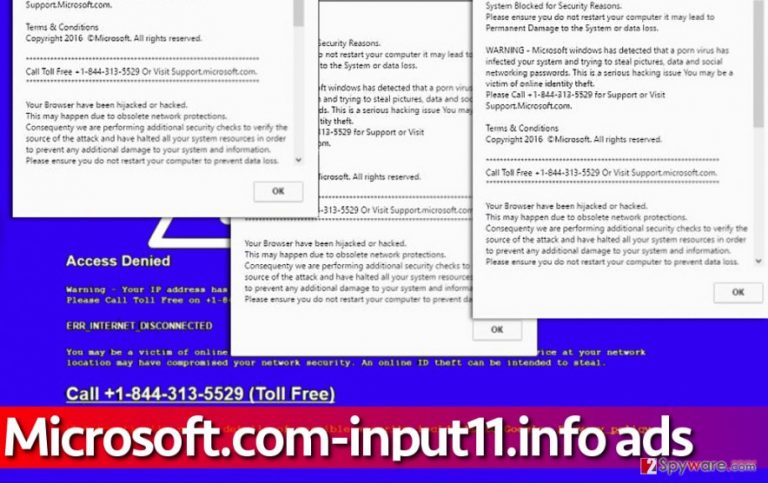
Microsoft.com-input11.info virus is a typical malicious program that falls into tech support scam malware family. Just like the rest of these phony programs, Microsoft.com-input11.info malware attacks user’s web browsers and employs them for placement of bogus alerts. These alerts are designed to scare the computer user and make him believe that the system is heavily contaminated with viruses of unknown origin. This particular virus commands to contact Microsoft technicians at one of the following numbers: +1-844-313-5529, +1-800-610-8993, +1-866-507-946, or +1-855-336-5598. You should NOT call any of these numbers because they will connect you with a tech support scammer, who will try to dupe you into believing that the system is actually infected. These scammers have no shame, and they don’t care about your financial situation. They just want to extort money, sensitive data or anything that they can use for profit. Do not let these scammers deceive you and better do not try to taunt them – just don’t call them, and in case they call you, just hang up.
The aim of technical support scammers is usually the same – make money by making the victim purchase some useless programs or services that allegedly can fix a compromised computer. Examples of viruses that advertise tech support malware include “Your Microsoft Computer has been blocked” virus, Adobe Flash Tech Support Scam virus and more. In reality, there are usually no threats that need to be fixed, except the tech support malware itself. For Microsoft.com-input11.info removal, use a good and reliable anti-malware tool like FortectIntego. You do not want to use some amateur tool that is likely to mess up your system instead of repairing it. To remove Microsoft.com-input11.info virus with the antimalware program, just start a full system scan and sit back. Wait until it finishes scanning the system and then command it to clean detected threats.
How tech support scam pop-up viruses are distributed?
Your computer can get affected by this or similar malware if you tend to ignore safe browsing rules. Please remember that the Internet is full of interesting content, but it is also full of content uploaded by cyber criminals. So if someone has sent you a message saying, “omg is that you in this video” or if you have received an email stating that someone has sent you $1000 via PayPal, that is likely a scam and you shouldn’t blindly click on links or email attachments that accompany such messages. What is more, you should rethink the software installation routine that you practise. Do you check what’s behind Custom or Advanced settings when installing new software on the system? If not, you risk installing bundled downloads, which are typically presented as “recommended third-party software.” To reject unneeded programs, deselect the ticks proving your acceptance.
Learn how to uninstall Microsoft.com-input11.info malware
If your browser has been affected by this filthy malware, you should not think that the system is contaminated with unknown and very dangerous viruses. Typically, it is enough to remove Microsoft.com-input11.info virus itself to solve the problem. However, scanning the system with a proper anti-malware tool will reveal and remove all spyware or malware related files, which is obviously a good thing. Please take into account that Microsoft.com-input11.info removal might be stopped by virus’ attempts to block your security software. In such case, follow these instructions and reboot your PC as explained below.
Getting rid of Microsoft.com-input11.info ads. Follow these steps
Manual removal using Safe Mode
Please read these explanations attentively. You will need to start your personal or work computer in a particular mode that deactivates almost all startup items and starts a minimal set of device drivers. When you do this, you can download or start a chosen antimalware software to clean the computer from Microsoft.com-input11.info virus.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Microsoft.com-input11.info and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting malware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
