ProductEvent (Removal Instructions) - Free Guide
ProductEvent Removal Guide
What is ProductEvent?
ProductEvent is adware application for macOS that gets installed along free software from third-party sites or via fake updates

ProductEvent is software that users might discover on their Mac computers seemingly out of nowhere, as it is often bundled with freeware or is installed via fake updates. It specializes in displaying various in-text links, pop-ups, auto-plays, pop-unders, banners, and other advertisements on Safari, Google Chrome, and Mozilla Firefox browsers. Nevertheless, the developers promote the app as a useful tool that can assist users with their web browsing activities. ProductEvent is nothing more but an adware program and should not be kept on any Mac system, as it might result in unsatisfactory web browsing experience, money loss, installation of other potentially unwanted programs – or even malware.
Because ProductEvent is a potentially unwanted application that is ad-supported, it is highly likely to gather information about users' web browsing habits. In some cases, the data might be personally-identifiable and, if leaked to inappropriate parties, might be used for malicious purposes, such as fraud.[1]
| Name | ProductEvent |
| Type | Adware, Mac virus |
| Systems affected | macOS, Mac OS X |
| Symptoms | Users who get infected with adware are usually unaware why they see the following symptoms:
|
| Risks | Adware might bring users to insecure sites that promote potentially malicious apps or ask to disclose personal information, such as credit card details. This might result in malware infections, money loss, or personal information usage in fraud campaigns |
| Installation | Users usually install ProductEvent involuntarily either via software bundles or by getting tricked by fake updates (Flash, Java, etc.) |
| Removal | You can terminate potentially unwanted programs using anti-malware software automatically or by following our manual guidelines below |
| Optimization & recovery | To ensure fast recovery from adware infection and high-performance of your Mac, scan it with FortectIntego |
ProductEvent ads appearance often comes as a surprise to users, as it uses deception to get installed on Mac systems. In most of the cases, users let it in during the installation of freeware/shareware from third-parties, as they are required to enter their passwords during the process. Alternatively, the ProductEvent virus might be installed after users get tricked by fake Flash Player update prompts – they might be encountered on a multitude of malicious sites on the internet.
The developers of ProductEvent adware seek to gain monetary benefit from clicks that users make and predetermined websites that they visit. Without a doubt, these practices do not bring any benefits to users, as they have to deal with coupons, deals, offers, and other promotional content regularly – it might even hinder the underlying content of the site. However, intrusive ads are not the only reason to remove ProductEvent.
Just as many other adware programs, ProductEvent might collect a variety of information about users, for example:
- IP address;
- Geolocation;
- Technical information about the device;
- ISP;
- Links clicked;
- Sites visited;
- Bookmarks added, etc.
Cookies, web beacons,[2] and other tracking technologies are used to collect the data. Because ProductEvent is published by an unknown developer, there are no legal documents bounding the app to protect this information in any way. Thus, it might be sold for marketing purposes or end up in the hands of cybercriminals.

ProductEvent is one of the apps that belong to series of adware developed for Mac operating systems that use the same icon and operates practically identically – it is highly likely that the distributor of these apps is the same (other examples include IdeaShared, SystemJump, LookupShare, Coordinator Plus, etc.). It is a very common practice when it comes to PUPs – the same applications are re-skinned and distributed as new ones. This is done in order to avoid a bad reputation, as well as the detection of anti-malware software on the host computer.
ProductEvent removal usually should not be difficult, although some users said that they struggled with the process. If you want to get rid of the unwanted app properly, scan your machine with anti-malware and then reset all the installed browsers, as explained below. For best results, we advise using FortectIntego as well.
Try avoiding apps from third-party sources
There are several applications that can be downloaded from the third-party official websites and be entirely safe (for example, anti-malware apps). Due to the functionality of anti-virus software, these applications cannot be placed on the official Apple stores, as they require special permissions to ensure system security. However, this is merely one of a few exceptions, and most of the third-party sites should not be used to download new applications.
App Store currently offers 1,8 million applications for users to download.[3] While recent events showed that some malicious apps might be inserted into official sources as well, chances of that happening are extremely low. Thus, considering such a large number of applications available, there is no need to use third-party sites in the first place. In most of the cases, users infect their Macs when installing software from websites that host pirated content (torrents, warez) or various other app hosting sites.
To avoid that, stick to official sources when looking for new apps. If you absolutely have to download something from a third-party, make sure you pay close attention to the installation process to avoid the installation of optional components. For example, freeware developers often use fine print texts, misleading offers, misplaced buttons, pre-ticked boxes, and similar deceptive methods. Thus, when prompted, opt for Advanced/Custom settings and get rid of all the unwanted apps.
Get rid of ProductEvent adware from your macOS
Manual ProductEvent removal might be a little difficult sometimes, as adware commonly uses various techniques to increase the persistence on the computer. For example, multiple components are dropped into different sections on the operating system, and finding them might be problematic, especially for a novice user. Therefore, it is best to trust reputable anti-malware that could locate these entries automatically and get rid of them in just a few moments.
Nevertheless, if you decide to remove ProductEvent by yourself, you should remember that moving the app to trash is hardly going to be enough. Before doing so, you should check your Activity Monitor for suspicious processes and shut them down. After that, examine the following locations on your Mac, and delete suspicious entries:
- ~/Library/LaunchAgents
- ~/Library/Application Support
- ~/Library/LaunchDaemons
After termination of ProductEvent adware, make sure you reset each of the installed browsers, as explained below.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of ProductEvent. Follow these steps
Delete from macOS
To get rid of ProductEvent virus from your macOS, please perform the following steps:
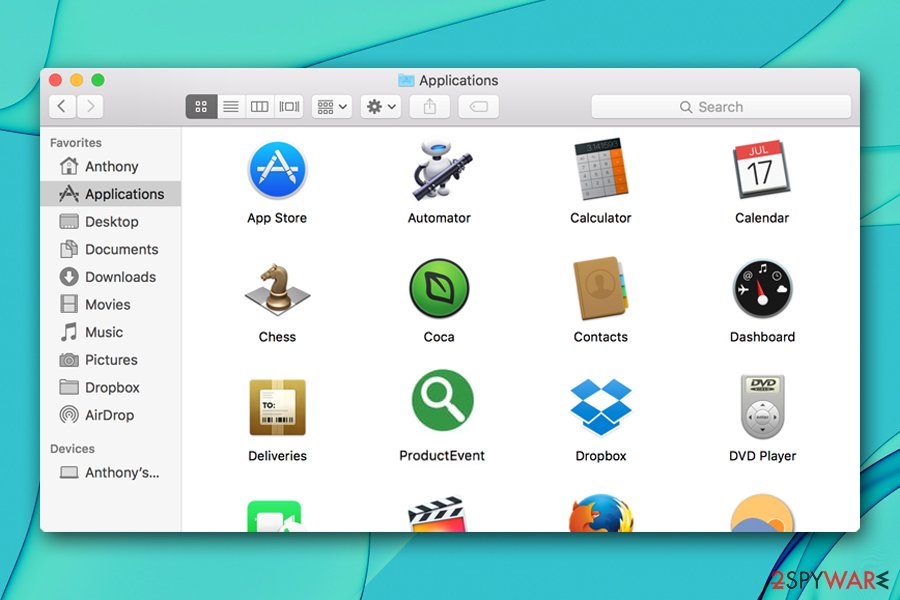
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
Adware affects settings of the installed web browsers. Make sure you rest Google Chrome as soon as PUP is terminated:
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of ProductEvent registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Megan Leonhardt. Here’s everything a cyber criminal can do if they steal your credit card. CNBC. Stock Markets, Business News, Financials, Earnings.
- ^ Web beacon. Wikipedia. The free encyclopedia.
- ^ J. Clement. Number of apps available in leading app stores 2019. Statista. Statistics site.












