What is Background Container.dll? Should I remove it?
BackgroundContainer.dll is the file associated with the browser hijacker, so it causes Windows startup errors
BackgroundContainer.dll is the file causing errors due to the infection on the system. Constant errors indicate the potentially unwanted program, in this case – a browser hijacker that is called various names: Search.Conduit.com virus, Storage.Conduit.com virus, or Conduit virus. These programs have initiated various problems for PC users because they have the ability to hide deep inside the system and cause continuous redirects, slowdowns, and similar issues. Although DLL files are a dynamic link library files used to hold various codes and procedures needed for Windows programs, this is a file associated with an unwanted and possibly malicious program.[1]
| Name | BackgroundContainer.dll |
|---|---|
| Type | Dynamic link library |
| Associated | Conduit virus |
| Dangerous? | Related with browser hijacker, other PUPs |
| Symptoms | Causes system errors, unwanted content, advertisements, redirects. All this behavior diminishes users' time online |
| Distribution | Comes with a potentially unwanted program, gets downloaded from the infected email |
| Damage | Can lead to more severe malware infiltrations, stolen personal information |
| Elimination | Get Malwarebytes and remove BackgroundContainer.dll. Use FortectIntego to keep the system free of PUPs |
Most browser hijackers push fake search engines and other rogue applications. This PUP changes browser settings without users consent and permission. In addition to that, Background Container.dll may be set to collect personally identifiable information and use it for questionable activities as a more severe malware – trojan. Various commonly found files get delivered as banking credentials, personal data, or password stealing malware. The fact that DLL is the type of file, people often don't pay enough attention to such intruders.
When PUP come to the system you can also notice other files, like SPSetup.exe and other executables that ensure persistence of the application or launches additional processes. You can check if BackgroundContainer.dll virus is a trojan or the PUP-related file by scanning the machine with FortectIntego. Nevertheless, this system check indicates all issues with your machine and malicious files, programs that you need to terminate or corrupted files that may cause errors.[2]
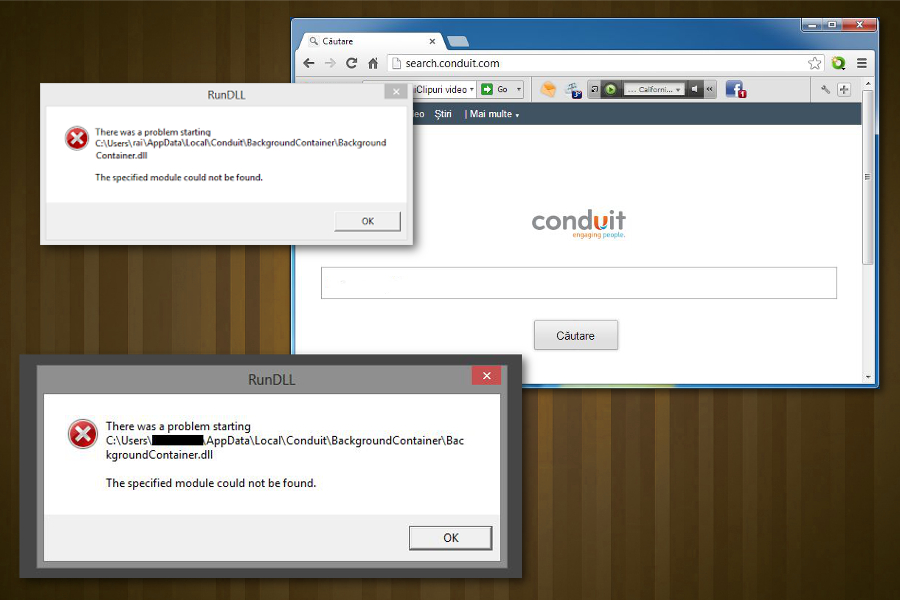
If your computer has ever been infected with any of these browser hijackers, you may start receiving an annoying error message that says that there is a problem with starting a particular scheduled task. In most of the cases, BackgroundContainer.dll errors appear every time you start your computer and claims:
Error loading C:/User/(User name)/ AppData/Local/ Conduit/BackgroundContainer/BackgroundContainer.dll
The specified module could not be found.
OR
RUNDLL
There was a problem starting C:/User/(User name)/ AppData/Local/ Conduit/BackgroundContainer/BackgroundContainer.dll
The specified module could not be found.
Unwanted programs like Background Container.dll – related hijacker causes problems related to privacy, browsing safety because applications as such track data regarding users' time online. The ad-supported program gets access to search queries, IP addresses, location, most viewed sites, and similar information.
Since such data, when collected can be used to create malvertising campaigns, experts[3] recommend performing BackgroundContainer.dll removal as soon as noticing suspicious activity regarding the file and the PUP. You don't need to worry about damage to your system. If the file is associated with the unwanted application – you can freely remove it from the computer.
Try to avoid clicking on any redirects, pop-up advertisements or banners delivered on the screen. This way you can prevent any unwanted infiltrations. Indicate the purpose of this file by scanning the system thoroughly, and remove BackgroundContainer.dll when the tool shows the results.
Opt for Custom freeware installations to avoid cyber infiltrations
Potentially unwanted programs like hijackers or rogue tools, adware come to the targeted system via insecure installations, when the user chooses to go for Recommended or Quick installations. This is the easiest way to spread PUPs because freeware providers can bundle their products and make sure that all packed programs get automatically installed. You can choose Advanced or Custom installations and avoid cyber infections.
When it comes to malicious files and more severe malware that can be hidden behind a common type of DLL or EXE file, the distribution methods involve spam email campaigns. When the email looks legitimate, not every time it is sent from the company or service, it seems to be sent from.
You should beware red flags like file attachments, services you don't use as senders. Delete received unknown email because once you open the infected file, other data can get installed on the system without your knowledge.
Terminate the BackgroundContainer.dll
If you have ever been bothered by this message, it means that the scheduled task tries to locate the needed DLL file and load it, but the module can no longer be found. If that is the case, you should eliminate Background Container.dll with the help of Task Scheduler. For that, you can follow these steps:
- Go to Control Panel and go to Administrative Tools
- Here, open Task Scheduler -> Task Scheduler Library.
- Now look for a task, which could be related to BackgroundContainer.
- Right-click on the task and select Delete.
- Exit Administrative tools and restart your computer.
However, the appearance of RunDLL error message may also mean that Conduit virus or some of its leftovers are hiding somewhere inside your computer. For making sure that your PC is safe, open Task Manager and look for Conduit-related entries. Also, scan your computer with FortectIntego, Malwarebytes or SpyHunter 5Combo Cleaner and remove BackgroundContainer.dll from the system alongside all the malicious files.
You need a thorough BackgroundContainer.dll removal with anti-malware tools because this file is associated with the malicious program or can even install additional files and applications without your knowledge and permission. During the full scan on the computer, all threats get deleted.
- ^ Dynamic-link library. Wikipedia. The free encyclopedia.
- ^ Analysis if SPSetup.exe. Virustotal. Online malware scanner.
- ^ Virusi. Virusi. Spyware related news.

