Cellsignclock.top scam (fake) - Free Guide
Cellsignclock.top scam Removal Guide
What is Cellsignclock.top scam?
Cellsignclock.top is a scam website that tries to make users provide their personal information

Cellsignclock.top hosts a scam, which is aimed at less IT-savvy computer users. Most commonly, people access this domain after being redirected from some other malicious website, which is of dubious origin (for example, free video streaming or an illegal program distribution). Likewise, random redirects on Google Chrome, Mozilla Firefox, MS Edge, or any other browser, might be a sign of an adware infection.
The website incorporates an array of various scams, ranging from Amazon gift cards to Congratulations you have won fake alerts. These phishing attempts have been around for many years: they imply that the visitor is somehow special and has been selected to participate in a survey. This allegedly allows users to be eligible to redeem an expensive gift, such as the newest iPhone, a gift card, PlayStation 5, and similar items.
The truth is, these promises are completely fabricated and none of the users would ever receive them because they simply do not exist. Cellsignclock.top scam is designed in a way to receive some type of benefits from users themselves; typically, crooks ask to provide credit card details, ask them to subscribe to useless services, or even download malicious software.
If you have come across this phishing attempt, you should immediately close down your browser tab and not interact with it. If you have participated in it, downloaded/installed something, or provided your personal details, you should check the sections below in order to remediate the situation. Also, an adware check is something that needs to be performed.
| Name | Cellsignclock.top |
|---|---|
| Type | Scam, phishing |
| Goal | To make users subscribe to useless services or provide personal information, including credit card details |
| Distribution | Redirects from other malicious websites, adware |
| Dangers | Redirects to malicious websites can result in unwanted site notifications, personal information disclosure to unknown parties (cybercriminals), monetary losses, installation of other potentially unwanted programs/malware |
| Elimination | To get rid of unwanted apps manually, you can follow our removal guide below. If the unwanted ads and other disruptive behavior does not stop, you should scan your computer with security software and delete all threats automatically |
| Further steps | Malware or adware infections can diminish the performance of your computer or cause serious stability issues. Use FortectIntego to remediate your device and ensure that the virus damage is fixed |
Why have you been redirected to Cellsignclock.top?
Redirects are normal within the internet sphere, and usually occur after a hyperlink (can be text, a button, or an image) is clicked. After clicking on these, users are then rerouted to places that make sense, for example, if you select the “About Us” section on a website, you expect to see a description of what it is about and who's creating it.
However, some redirects are deliberately done in a way that would link users to content they did not expect, and it is considered malicious behavior. These redirects typically lead people to websites that show various commercial content, some of which can even be malicious.
It is evident that legitimate websites that are cared for when it comes to cybersecurity do not engage in such practices, thus malicious redirects are likely to be encountered on dangerous websites, such as porn, gambling, or torrents. We highly recommend avoiding such places in the first place, as ransomware[1] or another type of infection might occur. Employing ad-blockers or web protection apps can help you avoid malicious redirects.
If you have been encountering scams such as Your system is infected with (3) viruses, Pornographic virus alert from Microsoft, or Mr Beast Giveaway, it is likely that there is adware installed on your system. These potentially unwanted programs spread in software bundles and via other deceptive methods and are typically associated with insecure advertising networks which push all sorts of internet nasties toward users.
In order to check whether your device is infected, you should perform a full system scan with powerful anti-malware software such as SpyHunter 5Combo Cleaner or Malwarebytes. These apps proved useful when dealing with potentially unwanted programs and even the toughest malware in the wild, so you can rest assured that your PC is clean. Also, we recommend using FortectIntego for a quick browser clean (or you can check the instructions below for a manual solution).
Survey scams bring crooks all sorts of benefits
Internet is incredibly vast, and not all websites are created for the sake of being informative or useful. Malicious actors create scam sites in order to trick users into doing something they normally wouldn't, and while most people would immediately leave a fake site, some do get fooled by these tricks, unfortunately.
Among others, survey scams have been around for years. They are very easy to create and are aimed at users who are gullible. Now, Cellsignclock.top propagates all types of scams, so you might encounter variants of it. Here's an example:
Today you have been randomly selected to take this survey. It will only take a minute and you will receive an amazing prize: Apple iPhone 13!
The message then proceeds by saying that only the “selected few” are eligible for this allegedly special opportunity, with the questions starting right below. Typically, these are a no-brainer to answer, and sometimes don't even include anything you need to know in particular. For example:
- “Do you like Google Chrome?”
- “Are you a male or a female?”
- “Which company created Google Chrome?”
These questions have nothing to do with customer satisfaction and are just there for visitors to believe that they are valid. They are not, and if you have been redirected to Cellsignclock.top, you should immediately leave the site.
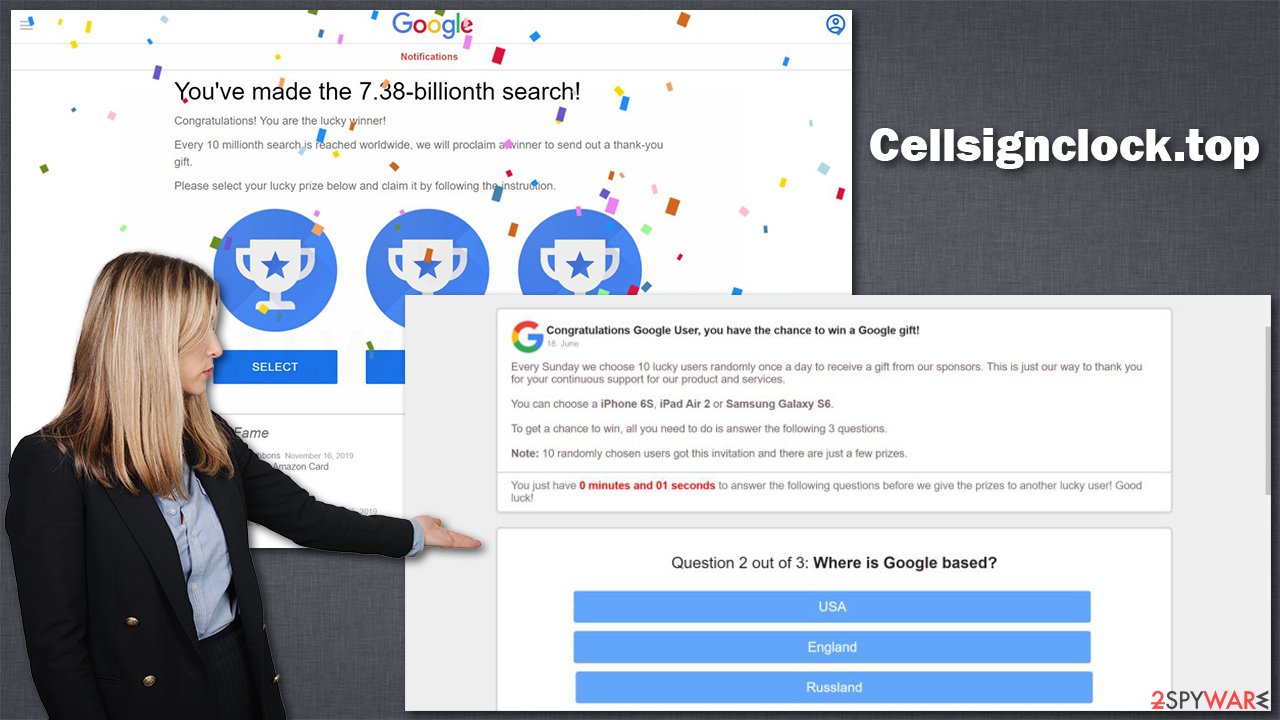
If you proceed with answering the questions, you would finally be forwarded to a landing page that would ask you to enter your name, email, Zip code, home address, or even credit card information. Usually, crooks use some type of excuse for this, like they need your details to verify you are a real user, or something similar.
It goes without saying that this information if in the wrong hands, might be used for many malicious purposes. You might be more prone to be targeted by further phishing[2] attempts or even have your identity stolen.
Note that scams commonly use names of well-known companies such as Microsoft, Amazon, Google, or Apple. It was meant to provide a fake sense of legitimacy. Keep in mind that none of these companies would offer random people to retrieve expensive items like these. Remember, if it is too good to be true, it likely is.
Checks to perform
In order to protect yourself from scams, you should employ tools like ad-blockers and security software. Also, be more skeptical and aware that random messages which claim that your system is infected or that you need to download something are always fake. Fake Flash Player Update prompts are commonly used in phishing attacks.
If you were tricked into complying with the request and filling in the required information, you should also use precautionary measures. For example, if you have entered your credit card details, contact your bank and explain what happened. The bank operators constantly deal with customers who were affected by fraud, and they will explain how to deal with the situation to protect your bank account from theft.
If you have provided your email or other account information, you should immediately change your passwords. Keep in mind that if you use the same password for multiple accounts, all of them could be compromised. Therefore, you should immediately change all of them and never reuse passwords in the future. Also, employing tools like password managers or two-factor authentication[3] can be particularly beneficial for any account security.
Getting rid of Cellsignclock.top scam. Follow these steps
Uninstall from Android
Uninstall unwanted programs from Android device:
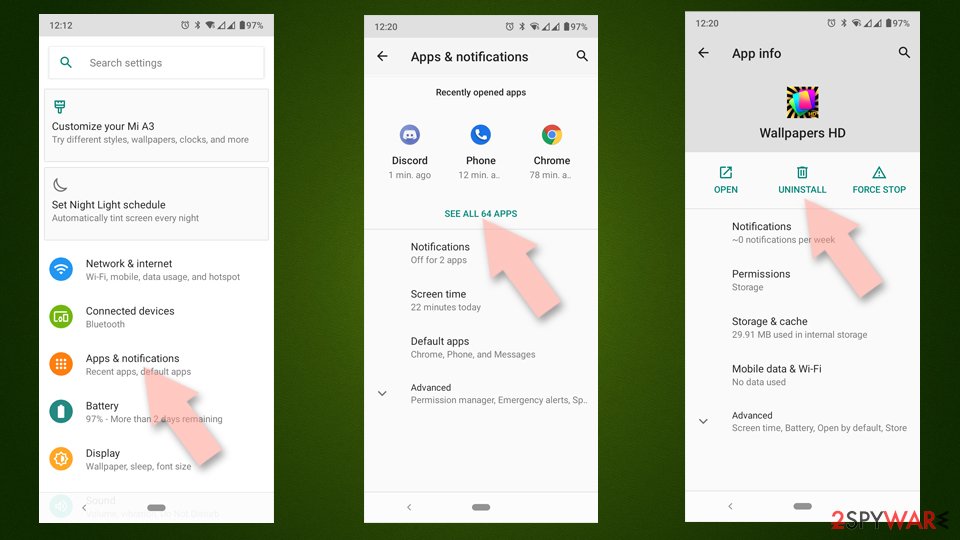
- Go to Settings -> Apps/Applications.
- Expand the full list of the installed apps.
- Scroll through the list and tap on a suspicious application once.
- Tap on it and select Uninstall.

- Reboot the device.
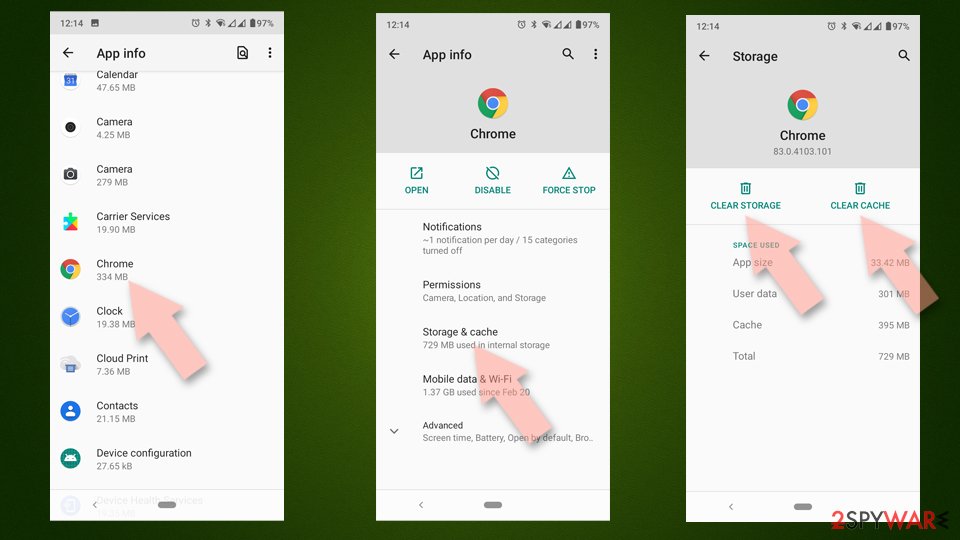
Clear Storage and data files on Android from Google Chrome or other apps:
- Go to Settings > Apps/Applications.
- Expand the full list of the installed apps.
- Tap on Chrome and select Storage & cache.
- Clear storage and clear cache of the app.

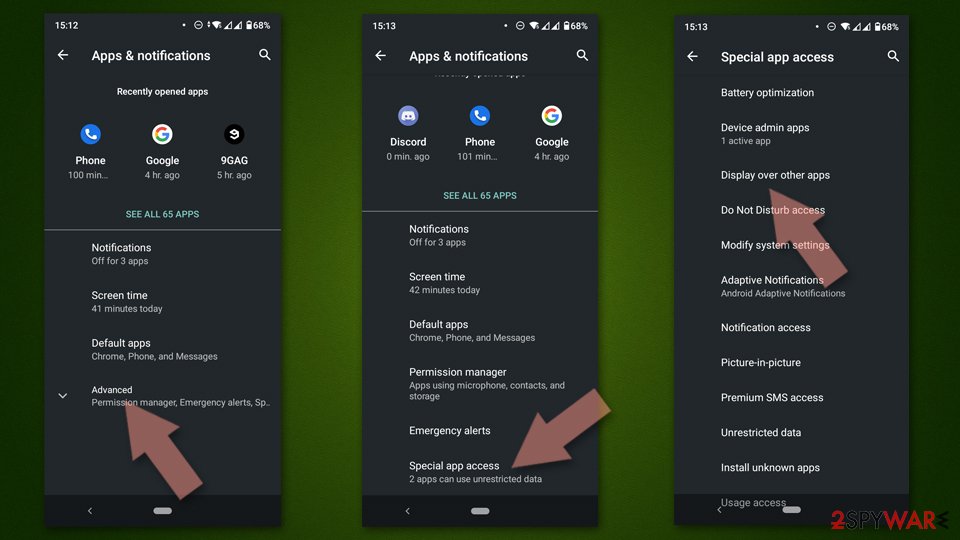
If you are seeing ads on top of other apps but are not sure what is causing it, perform the following steps:
- Go to Apps/Applications.
- Tap Advanced.
- Select Special App access.
- Tap on Display over other apps.

- Eliminate apps with these access rights enabled.
Uninstall from Windows
Instructions for Windows 10/8 machines:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

If you are Windows 7/XP user, proceed with the following instructions:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Delete from macOS
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Google Chrome
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Remove from Microsoft Edge
Delete unwanted extensions from MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Clear cookies and other browser data:
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Restore new tab and homepage settings:
- Click the menu icon and choose Settings.
- Then find On startup section.
- Click Disable if you found any suspicious domain.
Reset MS Edge if the above steps did not work:
- Press on Ctrl + Shift + Esc to open Task Manager.
- Click on More details arrow at the bottom of the window.
- Select Details tab.
- Now scroll down and locate every entry with Microsoft Edge name in it. Right-click on each of them and select End Task to stop MS Edge from running.

If this solution failed to help you, you need to use an advanced Edge reset method. Note that you need to backup your data before proceeding.
- Find the following folder on your computer: C:\\Users\\%username%\\AppData\\Local\\Packages\\Microsoft.MicrosoftEdge_8wekyb3d8bbwe.
- Press Ctrl + A on your keyboard to select all folders.
- Right-click on them and pick Delete

- Now right-click on the Start button and pick Windows PowerShell (Admin).
- When the new window opens, copy and paste the following command, and then press Enter:
Get-AppXPackage -AllUsers -Name Microsoft.MicrosoftEdge | Foreach {Add-AppxPackage -DisableDevelopmentMode -Register “$($_.InstallLocation)\\AppXManifest.xml” -Verbose

Instructions for Chromium-based Edge
Delete extensions from MS Edge (Chromium):
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Clear cache and site data:
- Click on Menu and go to Settings.
- Select Privacy, search and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Reset Chromium-based MS Edge:
- Click on Menu and select Settings.
- On the left side, pick Reset settings.
- Select Restore settings to their default values.
- Confirm with Reset.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

How to prevent from getting adware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Ransomware Definition. Trend Micro. Security blog.
- ^ Phishing. Wikipedia. The free encyclopedia.
- ^ Zack Wittaker. Cybersecurity 101: Two-factor authentication can save you from hackers. Tech Crunch. Startup and Technology News.