EFax email virus (Free Guide) - Removal Instructions
eFax email virus Removal Guide
What is eFax email virus?
eFax email virus is the spam email campaign that spreads trojans and RAT malware via phishing attachments
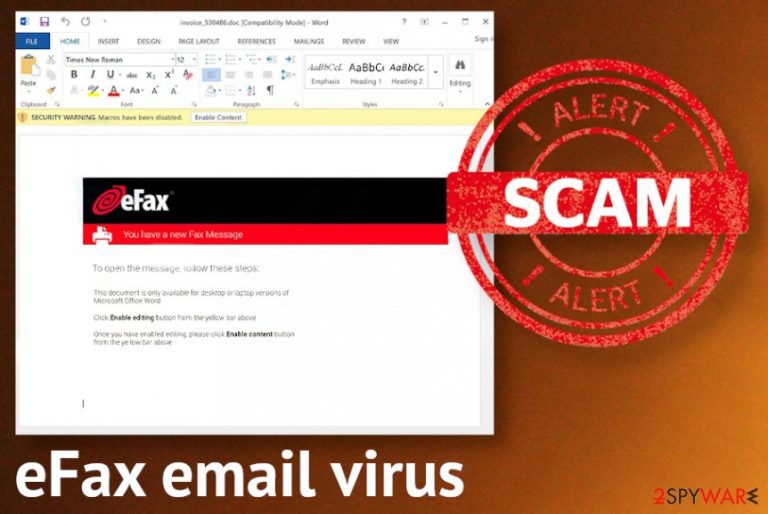
eFax scams, in particular, include file attachments that contain Microsoft Excel spreadsheets or ZIP files, Word documents. Victims need to enable malicious macros on such documents, and that is easily done with misleading text and buttons encouraging to allow the content and prompt the information that is supposedly important. Executable files and other triggers automatically download the Dridex trojan or Remote Manipulator System Remote Access Tool, as some news reports state.[1] There are tons of possible outcomes when the user loads the malicious file on the computer because malware creators can design the virus to steal information, spread additional malware, or gather other types of data.
This eFax spam campaign tricks users into opening the email and link or the directly attached file by stating that there is a number of unopened fax messages. To access them, people need to visit the site via the provided link and download the MS Office document that supposedly contains important files. Any random file name can be used on these documents or spreadsheets, so the user may not even expect anything suspicious, especially when these are many legitimate companies listed on the email, and the sender resembles the eFax platform.
| Name | eFax email virus |
|---|---|
| Type | Malware spreading campaign |
| Purpose | The misleading email notifications try to trick people into enabling additional content and loading malware on the machine, so the virus can run designed processes not he infected computer |
| Spreads | Trojans, password-stealing malware, banking malware,[2] spyware, and remote access trojans |
| Tactics | The notification supposedly informal people about pending pages from an unknown sender and encourages users to click on the link that should reveal the documents and fax pages with alleged messages and important files |
| Danger | There are tons of dangerous types of malware that email campaigns like this can spread around and features of stealthily intruders can differ from malware droppers to credential-stealers |
| Elimination | eFax email virus removal cannot be easy because you need to terminate all the programs that may end up on the computer and all the files that can possibly affect the performance. ANti-malware tools need to be used, so all the parts of the machine get checked for anything suspicious or malicious |
| Repair | System repair tools like FortectIntego or PC optimizing applications are needed for virus damage and any affected or possibly corrupted files that can significantly diminish your time on the computer in the future |
eFax email virus is the brandjacking scam that includes email fraud with the exploitation of a well-known brand name. The legitimate name and common type of notification help to convince people into opening files or links provided on the email. The recipient is informed that there are pages he or she forgot to check. Then the link leading to the phishing page is shown that encourages you to click on the button that should open the document directly.
Once the victim of the eFax email virus follows the suggested process, the page carries forged eFax branding as the email and other messages. The user is required to enter the login credentials that can be gathered this way, and people behind the scam can easily misuse data for identity theft or different campaigns.
eFax scams were noticed on different occasions, and none of them have the same email addresses, so those are formed randomly to resemble the company. In most cases, the eFax comes in from, and random characters or numbers follow. Even when the email includes a legitimate contact information window the only working part is the hyperlink leading to a phishing page and the initial email address.
eFax spam campaigns adopt several features to trick people:
- branding;
- logo;
- official contact spreadsheet;
- trademarked content;
- reference number;
- eFax website.
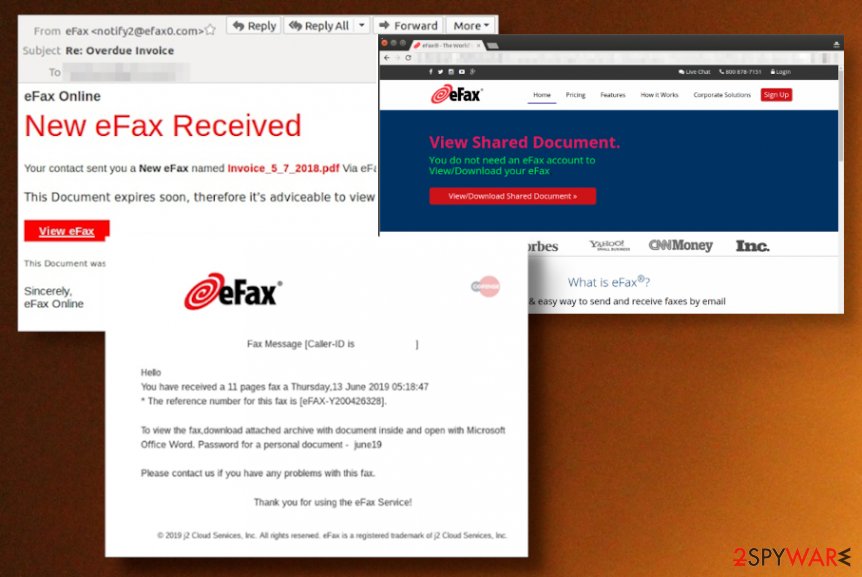
These malicious emails are always different, but experts[3] note that they may look like these examples:
Subject: eFax
You have an unread 4 page(s) fax.
Your fax can be viewed online, on our website, by visiting: hxxps://www.efax.com/
For additional assistance, please visit our help center at hxxps://www.efax.com/efax-help-center
Thank you for choosing eFax
Subject: efax
Fax Message[Caller-ID: 1-543-276-0865]
You have received a 1 page fax
*The reference number for this fax is at did-1400166434-31309133229-154.
Please download and view Microsoft Word attachment
Please visit www.eFax.com/en/efax/twa/page/help if you have any questions regarding this message or your service
Subject: You have a new fax from eFax!
Faxing Simplified
You have a new fax from eFax! Click attachment to view.
Thank you for choosing eFax!
Sincerely,
The eFax Team
P.S. Too busy to answer all your business calls? Let eVoice answer, manage and route your phone calls 24/7. Try a Free 30-Day Trial Today!
eFax spam focuses on companies that use the software and can get this scammy email. There are tons of possible innocent recipients who can get the email and fall for the malicious campaign without even noticing the red flags. This is the worst thing because there are many scenarios that can happen after the execution of a malicious file from the phishing site or a document.
You need to remove eFax email virus as soon as possible because criminals behind the scam can spread password-stealing malware, trojans or even ransomware, spyware, and banking credentials-targeting threats. Criminals continue to register email addresses and domains with napes of government departments and companies, so people receive backdoor trojans and other dangerous threats unsuspected.
eFax email virus can include chain infections that trigger one malicious script after the other and once you allow the malicious macros and execute data-stealing malware or a spying tool, you may at the same time receive the cryptocurrency mining virus or ransomware. Any intruder compromises the security of the machine and can lead to serious privacy issues and result in financial loss. 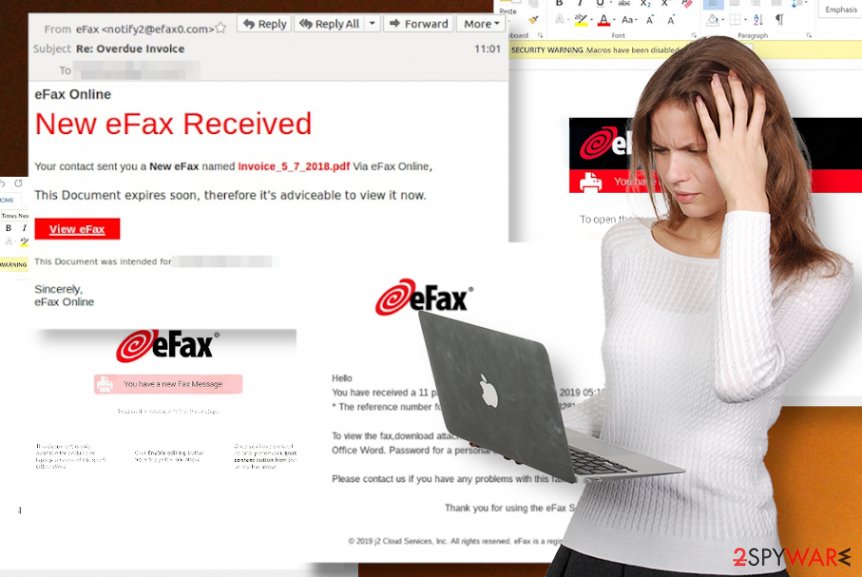
eFax spam can lead to huge businesses that enable employees to check their personal emails on work computers, suffer from cyber attacks. There is an important issue to have a multi-layered strategy to ensure the security of the company and personal data. Significantly reduced risks of malware infections can help protect the network.
Otherwise, you will face the difficulty of eFax email virus removal process. Even though this is an email campaign, the malware that is distributed can run in the background and affect various processes of the computer, so the full system scan is mandatory. You cannot get rid of all the malicious programs and files without employing a proper anti-malware tool. So rely on anti-malware application and run the software on your device, so all the parts of the virus can get terminated.
Unfortunately, you may not be sure when this eFax email virus ended up on your machine and for how long the malware may already be running. This fact also means that your device can get affected and significantly damaged behind your back and without you noticing. When the virus damage is left behind, infection may repeat itself, or your device may still work poorly even after the virus termination. Check the computer using FortectIntego or similar PC repair tools for affected files or system corruption and make sure to double-check to be sure. 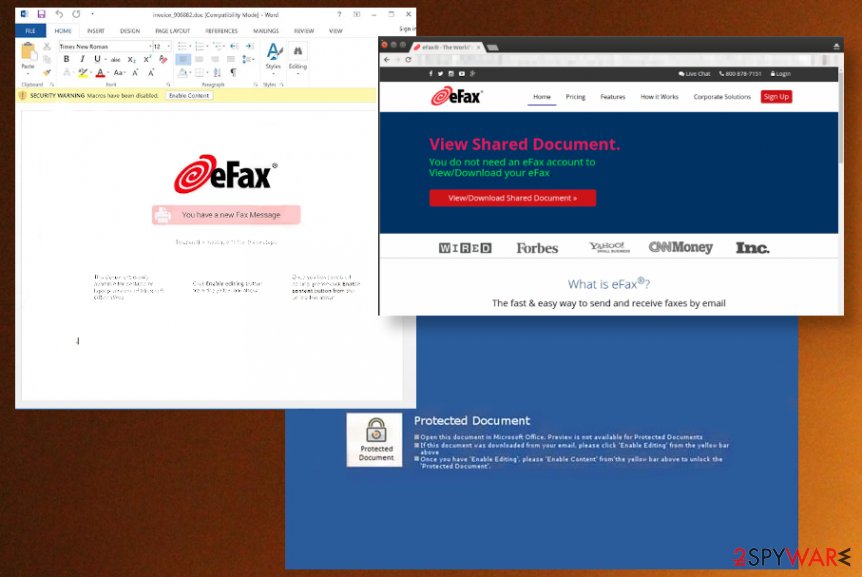
Do not click on any links or files when you are not sure about the email
There are tons of variants of such email campaigns and different scams that use decent logos, text, contact information, and other features that resemble legitimate companies and services. Scammers want you to click on zip files, Dropbox account links, open other websites, and download attachments. Some AV engines can detect suspicious files or links and indicate that the email is not safe, but you should run such applications on the machine more often and check particular notifications.
If you are familiar with the company or the service, you may not even consider the notification as a scam and open the message immediately. You need to pay attention to details all the time and consider any email a possible threat since these scams are more and more popular. Delete the email if it is suspicious in the first place, and you are not expecting to get any financial documents from the service.
Do not click on links or reply to any messages that are not expected. Try to look out for red flags and suspicious features like typos, grammar mistakes, and incorrect company emails. When receiving documents, look for a message that is specific – don't just open files shared with the generic message from the document sharing application or service.
Clean the machine from my traces of the eFax scam campaign
eFax email trojan can be one of the malware types that this scam distributes, so you need to find the intruder to get rid of it. There is no other way to delete a virus if you cannot see it as a program running on the computer. Trojans, spyware, and other malware are not PUPs or tools that can show up on the screen and indicate that there is something wrong.
To remove eFax email virus, you need a proper security tool like SpyHunter 5Combo Cleaner or Malwarebytes, an anti-malware application that can check various places of the machine and find malicious or even possibly dangerous programs, files, and scripts. You are left with a few options after the full system scan because AV engines show you the results and offer to delete or quarantine malware yourself.
When the process of eFax email virus removal becomes difficult, you can be sure that trojan is affecting particular processes and features of the system, so it is persistent. For that reason, you can reboot PC in Safe Mode and then run the anti-malware program. Also, for the damage that the virus leaves behind, try FortectIntego. Repair anything corrupted to a smooth working machine.
Getting rid of eFax email virus. Follow these steps
Manual removal using Safe Mode
Try Safe Mode reboot for eFax email virus removal
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove eFax email using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of eFax email. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from eFax email and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting malware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Charlie Osborne. Fake eFax emails are now spreading Dridex Trojan, RMS RAT. ZDNet. Technology and security news.
- ^ Corporate users at most hacking risk form banking malware attacks. Expresscomputer. IT news.
- ^ Bedynet. Bedynet. Spyware related news.







